Blockchain Certification: Bitcoin & Opentimestamps
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Markets in Crypto Assets: Mica Regulation
February 5 2021 Digital Gold Institute: Vision R&D center of excellence focused on teaching, training, consulting, and advising about scarcity in digital domain (bitcoin and crypto-assets) and the underlying blockchain technology Bitcoin: Digital Gold Blockchain: Hype or Reality? The most successful attempt at creating scarcity Blockchain requires an intrinsic native digital in the digital realm without a trusted third party. asset to provide the economic incentives for the Bitcoin is the digital equivalent of gold, blockchain maintainers to be honest. Without disruptive for our current digital civilization and the seigniorage revenues associated to its native the future of money and finance. More a crypto- asset, a blockchain system would need to select commodity than a crypto-currency, Bitcoin aims and appoint its maintainers, ultimately resorting to be world reserve asset. to central governance. Beyond Bitcoin: Timestamping Financial Services for Crypto A timestamp demonstrates that a document The most promising field, instead of existed in a specific status prior to a given point technological applications of blockchain, is the in time. Digital data can be securely development of financial services for crypto timestamped though the attestation of its hash assets: those tools, practices, and facilities value in a blockchain transaction. What jewellery needed by institutional investors and high net is for gold, Timestamping could be for bitcoin: worth individuals. Finance might not need not essential but effective at leveraging its blockchain, -

October 29 2020 Digital Gold Institute: Vision
October 29 2020 Digital Gold Institute: Vision R&D center of excellence focused on teaching, training, consulting, and advising about scarcity in digital domain (bitcoin and crypto-assets) and the underlying blockchain technology Bitcoin: Digital Gold Blockchain: Hype or Reality? The most successful attempt at creating scarcity Blockchain requires an intrinsic native digital in the digital realm without a trusted third party. asset to provide the economic incentives for the Bitcoin is the digital equivalent of gold, blockchain maintainers to be honest. Without disruptive for our current digital civilization and the seigniorage revenues associated to its native the future of money and finance. More a crypto- asset, a blockchain system would need to select commodity than a crypto-currency, Bitcoin aims and appoint its maintainers, ultimately resorting to be world reserve asset. to central governance. Beyond Bitcoin: Timestamping Financial Services for Crypto A timestamp demonstrates that a document The most promising field, instead of existed in a specific status prior to a given point technological applications of blockchain, is the in time. Digital data can be securely development of financial services for crypto timestamped though the attestation of its hash assets: those tools, practices, and facilities value in a blockchain transaction. What jewellery needed by institutional investors and high net is for gold, Timestamping could be for bitcoin: worth individuals. Finance might not need not essential but effective at leveraging its blockchain, -

TRUST, but VERIFY: WHY the BLOCKCHAIN NEEDS the LAW Kevin Werbach†
TRUST, BUT VERIFY: WHY THE BLOCKCHAIN NEEDS THE LAW Kevin Werbach† ABSTRACT The blockchain could be the most consequential development in information technology since the Internet. Created to support the Bitcoin digital currency, the blockchain is actually something deeper: a novel solution to the age-old human problem of trust. Its potential is extraordinary. Yet, this approach may not promote trust at all without effective governance. Wholly divorced from legal enforcement, blockchain-based systems may be counterproductive or even dangerous. And they are less insulated from the law’s reach than it seems. The central question is not how to regulate blockchains but how blockchains regulate. They may supplement, complement, or substitute for legal enforcement. Excessive or premature application of rigid legal obligations will stymie innovation and forego opportunities to leverage technology to achieve public policy objectives. Blockchain developers and legal institutions can work together. Each must recognize the unique affordances of the other system. DOI: https://doi.org/10.15779/Z38H41JM9N © 2018 Kevin Werbach. † Associate Professor of Legal Studies and Business Ethics, The Wharton School, University of Pennsylvania. Email: [email protected]. Thanks to Dan Hunter for collaborating to develop the ideas that gave rise to this Article, and to Sarah Light, Patrick Murck, and participants in the 2017 Lastowka Cyberlaw Colloquium and 2016 TPRC Conference for comments on earlier drafts. 488 BERKELEY TECHNOLOGY LAW JOURNAL [Vol. 33:487 -

Il Modello Predittivo Degli Eventi Futuri Del CRNE - Centro Ricerche Nuove Energie
Il Modello Predittivo degli Eventi Futuri del CRNE - Centro Ricerche Nuove Energie: Analisi GeoPolitiche, Tecnologiche & Smart City Solution - Advice Service CRNE Science & Business Vision Il CRNE Centro Ricerche Nuove Energie nasce nel 1998, e nel 2015 la “Divisione Ricerca e Sviluppo” ha sviluppato “un modello predittivo degli eventi futuri basato sul censimento delle minacce ponderate”. Si tratta di “un servizio di consulenza sulle aspettative future” unico nel suo genere sul panorama nazionale e internazionale, in cui viene esposto in maniera chiara una visuale precisa degli eventi futuri, che noi riteniamo altamente probabili, sia sul breve, che nel medio, che nel lungo periodo. Il Modello Predittivo degli eventi futuri del CRNE è uno strumento prezioso per quanti vogliono avere una visione moderna e all’avanguardia dell’evoluzione degli eventi, per proteggersi nell’immediato futuro dalle minacce ponderate che abbiamo censito, che sono esposte in forma cronologica nel modello predittivo. Sta alla sensibilità del lettore tenere in considerazione per il proprio futuro quanto riportato in questa relazione. CRNE Science & Business Vision is an Advice Service to Avoid Future’s Systemic Crisis These Are Our Areas of Expertise: Geopolitical Analysis and Solutions - Investment in Work & Residential CRNE Concept Outside Italy, called “Smart City Project”, named “Backup Italy” Advice Service for Human Resources & Capital Money Protection - Scientific and Technological Research - Development Service for Start Up, Patent and Prototype for CRNE’s Smart City - International Financial Analysis & Development Performance’s Strategy for Stock Market CRNE leads the way to the future to the best Italians, Serenity is our goal, Choose to live under CRNE wings&vision. -

The Lightning Network - Deconstructed and Evaluated
The Lightning Network - Deconstructed and Evaluated Anti-Money Laundering (AML) and Anti-Terrorist Financing (ATF) professionals, especially those working in the blockchain and cryptocurrency environment, may have heard of the second layer evolution of Bitcoin's blockchain - the Lightning Network, (LN). This exciting new and rapidly deploying technology offers innovative solutions to solve issues around the speed of transaction times using bitcoin currently, but expandable to other tokens. Potentially however, this technology raises regulatory concerns as it arguably makes, (based on current technical limitations), bitcoin transactions truly anonymous and untraceable, as opposed to its current status, where every single bitcoin can be traced all the way back to its coinbase transaction1 on the public blockchain. This article will break down the Lightning Network - analyzing how it works and how it compares to Bitcoin’s current system, the need for the technology, its money laundering (ML) and terrorist financing (TF) risks, and some thoughts on potential regulatory applications. Refresher on Blockchain Before diving into the Lightning Network, a brief refresher on how the blockchain works - specifically the Bitcoin blockchain (referred to as just “Bitcoin” with a capital “B” herein) - is required. For readers with no knowledge or those wishing to learn more about Bitcoin, Mastering Bitcoin by Andreas Antonopoulos2 is a must read, and for those wishing to make their knowledge official, the Cryptocurrency Certification Consortium, (C4) offers the Certified Bitcoin Professional (CBP) designation.3 Put simply, the blockchain is a growing list of records that can be visualized as a series of blocks linked by chains. Each block contains specific information - in Bitcoin’s case, a list of transactions and their data, which includes the time, date, amount, and the counterparties4 of each transaction. -

Flyclient: Super-Light Clients for Cryptocurrencies
FlyClient: Super-Light Clients for Cryptocurrencies Benedikt B¨unz1∗y, Lucianna Kiffer2∗y, Loi Luu3∗, and Mahdi Zamani4 1Stanford University, 2Northeastern University, 3Kyber Network, 4Visa Research August 20, 2020 Abstract To validate transactions, cryptocurrencies such as Bitcoin and Ethereum require nodes to verify that a blockchain is valid. This entails downloading and verifying all blocks, taking hours and requiring gigabytes of bandwidth and storage. Hence, clients with limited resources cannot verify transactions independently without trusting full nodes. Bitcoin and Ethereum offer light clients known as simplified payment verification (SPV) clients, that can verify the chain by downloading only the block headers. Unfortunately, the storage and bandwidth requirements of SPV clients still increase linearly with the chain length. For example, as of July 2019, an SPV client in Ethereum needs to download and store about 4 GB of data. Recently, Kiayias et al. proposed a solution known as non-interactive proofs of proof-of-work (NIPoPoW) that allows a light client to download and store only a polylogarithmic number of block headers in expectation. Unfortunately, NIPoPoWs are succinct only as long as no adversary influences the honest chain, and can only be used in chains with fixed block difficulty, contrary to most cryptocur- rencies which adjust block difficulty frequently according to the network hashrate. We introduce FlyClient, a novel transaction verification light client for chains of variable difficulty. FlyClient is efficient both asymptotically and practically and requires downloading only a logarithmic number of block headers while storing only a single block header between executions. Using an opti- mal probabilistic block sampling protocol and Merkle Mountain Range (MMR) commitments, FlyClient overcomes the limitations of NIPoPoWs and generates shorter proofs over all measured parameters. -

Bitcoin 2.0 – New Technologies and New Legal Impacts
October 16, 16, 2018 October RamdeRakesh – ProteumLLC Capital, –MinneJacob Lewis Bockius& Morgan, LLP ANDNEWIMPACTS LEGAL NEWTECHNOLOGIES BITCOIN2.0– © 2018 Morgan, Lewis & Bockius LLP Agenda • Introduction - A Brief Refresher on Bitcoin • Second Layer Solutions: – Lightning Network – Applicability of AML Laws – Extraterritoriality – Taxation – Potential Strategies • Digital Governance Strategies – Dash – Taxing and Spending – Ethereum and the DAO – EOS – On-Chain Dispute Ressolution • Business Assets on the Blockchain – Rakesh Ramde, Proteum Capital, LLC 2 INTRODUCTION AND REFRESHER ON BLOCKCHAIN A Blockchain Is: 1. A database, 2. that is distributed (not centralized), 3. whose data elements are immutable (unalterable), and 4. that is encrypted “At its simplest level, a blockchain is nothing much more than a fancy kind of database” - Blythe Masters, Digital Assets 4 Bitcoin Distributed Payment System • All participants (A-I) have sight of all transactions on A B the blockchain (and their C entire history) • Payments pass directly I between users, here A to F, D but are verified by other users (here, D, G, and I) • New transactions are H E broadcast to “miners” • When verified, the G F transaction is added to the (Bank of England Quarterly Bulletin 2014 Q3) blockchain history 5 Advantages and Disadvantages Advantages: Disadvantages: • Accessibility • Slow transaction rate / (potentially) high cost • Redundancy • High Energy Cost • Passive access • Lack of Privacy 6 SECOND LAYER SOLUTIONS – A DISCUSSION OF LIGHTNING NETWORK Second Layer Solutions • Developers need a way to scale if Bitcoin is to have widespread adoption. One so-called “second layer” solution is “Lightning Network.” 8 Lightning Network • In Lightning, two peers make a single transaction on the blockchain, each locking some amount of bitcoin in a “channel.” • The two parties can then trade back and forth so long as the net balance never exceeds the channel balance. -
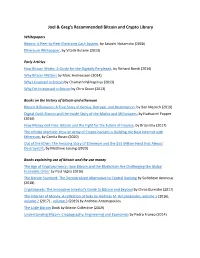
Joel & Greg's Recommended Bitcoin and Crypto Library
Joel & Greg’s Recommended Bitcoin and Crypto Library Whitepapers Bitcoin: A Peer‐to‐Peer Electronic Cash System, by Satoshi Nakamoto (2008) Ethereum Whitepaper, by Vitalik Buterin (2013) Early Articles How Bitcoin Works: A Guide for the Digitally Perplexed, by Richard Bondi (2014) Why Bitcoin Matters by Marc Andreessen (2014) Why I Invested in Bitcoin by Chamath Palihapitiya (2013) Why I’m Interested in Bitcoin by Chris Dixon (2013) Books on the history of bitcoin and ethereum Bitcoin Billionaires: A True Story of Genius, Betrayal, and Redemption, by Ben Mezrich (2019) Digital Gold: Bitcoin and the Inside Story of the Misfits and Millionaires, by Nathaniel Popper (2016) How Money Got Free: Bitcoin and the Fight for the Future of Finance, by Brian Eha (2017) The Infinite Machine: How an Army of Crypto‐hackers is Building the Next Internet with Ethereum, by Camila Russo (2020) Out of the Ether: The Amazing Story of Ethereum and the $55 Million Heist that Almost Destroyed It, by Matthew Leising (2020) Books explaining use of bitcoin and the use money The Age of Cryptocurrency: How Bitcoin and the Blockchain Are Challenging the Global Economic Order by Paul Vigna (2016) The Bitcoin Standard: The Decentralized Alternative to Central Banking by Saifedean Ammous (2018) Cryptoassets: The Innovative Investor's Guide to Bitcoin and Beyond by Chros Burniske (2017) The Internet of Money: A collection of talks by Andreas M. Antonopoulos, volume 1 (2016), volume 2 (2017) , volume 3 (2019) by Andreas Antonopoulos The Little Bitcoin Book by Bitcoin Collective -

Decentralized Attestation of Conceptual Models Using the Ethereum Blockchain
Decentralized Attestation of Conceptual Models Using the Ethereum Blockchain Felix Harer¨ Hans-Georg Fill Digitalization and Information Systems Group Digitalization and Information Systems Group University of Fribourg University of Fribourg Fribourg, Switzerland Fribourg, Switzerland [email protected] hans-georg.fi[email protected] Abstract—Decentralized attestation methods for blockchains When implementing the idea of decentralized identification are currently being discussed and standardized for use cases such together with verifiable attestations about the identity and ex- as certification, identity and existence proofs. In a blockchain- istence of information [11], decentralized applications beyond based attestation, a claim made about the existence of information can be cryptographically verified publicly and transparently. the ones built into distributed ledger systems can be realized. In this paper we explore the attestation of models through Many applications can be designed in such a way that infor- globally unique identifiers as a first step towards decentralized mation does not need to be held available in cases where an applications based on models. As a proof-of-concept we describe assertion about the existence of the information can be made a prototypical implementation of a software connector for the instead. For the attestation of the existence of documents, ADOxx metamodeling platform. The connector allows for (a.) the creation of claims bound to the identity of an Ethereum the concept has been implemented in the form of attestation account and (b.) their verification on the blockchain by anyone services based on blockchains [11]–[14]. In this realization, at a later point in time. For evaluating the practical applicability, the representation used for attestation by these services is we demonstrate the application on the Ethereum network and on the level of data. -
Blockchain and Freedom of Expression
Blockchain and freedom of expression 2019 Blockchain and freedom of expression 1 ARTICLE 19 Free Word Centre 60 Farringdon Road London EC1R 3GA United Kingdom T: +44 20 7324 2500 F: +44 20 7490 0566 E: [email protected] W: www.article19.org Tw: @article19org Fb: facebook.com/article19org © ARTICLE 19, 2019 This work is provided under the Creative Commons Attribution-Non-Commercial-ShareAlike 2.5 licence. You are free to copy, distribute and display this work and to make derivative works, provided you: 1) give credit to ARTICLE 19; 2) do not use this work for commercial purposes; 3) distribute any works derived from this publication under a licence identical to this one. To access the full legal text of this licence, please visit: http://creativecommons.org/licenses/ by-nc-sa/2.5/legalcode. ARTICLE 19 would appreciate receiving a copy of any materials in which information from this report is used. Contents Executive summary 4 Summary of recommendations 6 Introduction 9 Background to blockchains 12 Key terminology 12 Key characteristics of blockchains 14 International human rights standards and blockchains 16 Right to freedom of expression 16 Right to privacy 17 Internet governance 18 Intermediary liability 18 Blockchains and freedom of expression 20 Decentralisation, disintermediation and freedom of expression 20 Digital access and literacy 21 Security and vulnerability of access points 22 Governance 23 Use case: content dissemination 25 Dissemination of text 25 Dissemination of multimedia and the ‘permanent web’ 27 Blockchain-based social networks 29 Use case: authentication 32 Authentication of individuals 32 Authentication of content (digital notarisation) 37 Use case: personal data and storage of identity-linked information 39 Use case: cryptocurrencies 41 Conclusions and recommendations 43 Recommendations 44 About ARTICLE 19 48 Endnotes 49 Executive summary In this report, ARTICLE 19 examines the impact and implications of blockchain technology for the right to freedom of expression. -

Interview CEO of the Largest Bitcoin Cloud Pit World Answers the Most Important Questions About Bitcoin Mining - Moneycontrol.Com 1 Bitcoin Berapa Rupiah 2017
Interview CEO of the largest bitcoin Cloud Pit World answers the most important questions about bitcoin mining - Moneycontrol.com 1 bitcoin berapa Rupiah 2017 October 11, 2017 Bitcoin news The world's first decentralized crypto is to serve as peer-to-peer electronic cash so that transactions are possible directly between users, eliminating the need for trustworthy third parties such as central banks. For this reason, Bitcoin mining has become increasingly difficult to purchase Bitcoin Bergmann. Those who do not want to invest in expensive hardware that for bitcoin or cryptography mining in general can earn a few coins through cloud mining. (This activity refers to mining bitcoins using modern hardware from companies that are specifically set up to provide this service, instead of a fee.) In a detailed conversation with Moneycontrol, Marco Streng, CEO of Genesis Mining, the largest cloud mining company in the world, casts a light on the cloud mining industry, his challenges and the future path cryptocurrencies. Crypto, which is a paragon for Bitcoin and Altcoins such as Astraleum, Dash, Monero etc, is bound to change the way we look at money. Industry leaders such as Bill Gates and Richard Branson have expressed their support for Bitcoin and Blockchain technology and Bitcoin experts like Andreas Antonopoulos believe, "It is the Internet of Money". The co-founder of Genesis Mining, Marco Krohn, Jakov Dolic and I met around 4 years ago through the Munich (Germany) localBitcoins website - at that time no Bitcoin exchange was. We discovered we had a common passion for Bitcoin and home mining. We decided to set up a large GPU farm in Eastern Europe to mine Litecoins and in the process of doing this, we decided to create fairly quickly a cloud-mining platform bitcoins com. -

Understanding the Blockchain Oracle Problem: a Call for Action
information Review Understanding the Blockchain Oracle Problem: A Call for Action Giulio Caldarelli Department of Business Administration, University of Verona, 37129 Verona, Italy; [email protected] Received: 12 September 2020; Accepted: 28 October 2020; Published: 29 October 2020 Abstract: Scarce and niche in the literature just a few years ago, the blockchain topic is now the main subject in conference papers and books. However, the hype generated by the technology and its potential implications for real-world applications is flawed by many misconceptions about how it works and how it is implemented, creating faulty thinking or overly optimistic expectations. Too often, characteristics such as immutability, transparency, and censorship resistance, which mainly belong to the bitcoin blockchain, are sought in regular blockchains, whose potential is barely comparable. Furthermore, critical aspects such as oracles and their role in smart contracts receive few literature contributions, leaving results and theoretical implications highly questionable. This literature review of the latest papers in the field aims to give clarity to the blockchain oracle problem by discussing its effects in some of the most promising real-world applications. The analysis supports the view that the more trusted a system is, the less the oracle problem impacts. Keywords: blockchain; smart contracts; oracles 1. Introduction “Is the blockchain the greatest technological innovation since the internet ::: or the greatest load of hype ever raged around the history of technology? ::: Both” (Andreas Antonopoulos). Blockchain’s primary innovation is that it allows business partners to transfer digital assets without the need for a centralized third party [1]. However, as blockchain can execute only simple transactions, “smart contracts” are necessary to settle the terms of an agreement [2,3].