13 Years of Linux
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

SUCCESS STORY. Security Software Porting from Netware to Novell Linux
SUCCESS STORY. >_ >_ Security Software Porting From Netware To Novell >_ Linux About the The Client is a leader in the development of real-time monitoring, auditing and computer forensics Client technologies for Windows and Novell networks. Its ⧄agship product is used to secure the assets of the world’s largest corporations, banks, and government agencies, educational and healthcare institutions. Business The Client had a signi⣴cant install base for its ⧄agship software on Novell Netware OS. Novell’s Challenge adoption of Linux as the migration path for Netware OS created both an opportunity and a challenge for the Client. To continue supporting its Netware user base through Linux migration, the client wanted to port its monitoring and auditing solution to support SUSE Linux, Novell eDirectory and NSS (Novell Storage Services). The Client did not have in-house Linux Systems programming expertise, especially with ⣴le systems & security knowledge and approached Silicus. Silicus The software had two parts – the agent (client) and the server. The agent was a module that was Solution installed on the PC’s to be audited, and sends information on PC activities to a server installed at a centralized location. Termination of Netware required the agent to be re-developed/ported to Linux. Silicus commenced a feasibility study to address a few unknowns in the project: • Identify the auditing modules available on SuSE Linux • XML libraries that could be used • Multi-threading architecture to be used for agent development Silicus created a software architecture and design for the remote management agent. The agent was developed leveraging 3rd party tools to perform the auditing, monitoring of the Linux systems and communication with the remote server. -

Module Introduction
Module Introduction PURPOSE: The intent of this module is to provide an overview of the MPC5200. OBJECTIVES: - Identify the MPC5200 Block Diagram - Identify the MPC5200 Target Markets - Describe HiP7 Technology - Describe Core Features - Describe System Level Features CONTENT: - 28 pages - 5 questions LEARNING TIME: - 55 minutes The intent of this module is to provide you with an overview of the MPC5200 microcontroller. You will become familiar with the MPC5200 and its target markets. You will also learn about the composition of the MPC5200 by studying its block diagram. Finally, you will explore the core and system level features of the of the MPC5200. 1 MPC5200 Overview Designed with automotive/telematics applications in mind Runs at higher clock, bus, and CPU speeds Handles a tremendous range of applications Welcome to the MPC5200. This processor provides very high performance in automotive and other embedded environments. This device has been designed with automotive and telematics applications in mind. What is new about the MPC5200? Generally, automotive class processors have not run at the clock speeds seen in the MPC5200. The external bus speeds of this device are up to 132 MHz and the internal execution speed for the CPU is up to 400 MHz. This provides the horsepower to do voice recognition, graphics processing and wireless communications. The MPC5200 is not just for automotive applications. In fact, this device will handle a tremendous range of applications. This is mainly due to the wide range of communications peripherals and timers, as well as the processing power provided by the 603 G2_LE core that uses the PowerPCTM instruction set. -
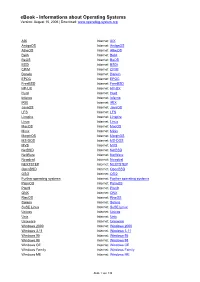
Ebook - Informations About Operating Systems Version: August 15, 2006 | Download
eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org AIX Internet: AIX AmigaOS Internet: AmigaOS AtheOS Internet: AtheOS BeIA Internet: BeIA BeOS Internet: BeOS BSDi Internet: BSDi CP/M Internet: CP/M Darwin Internet: Darwin EPOC Internet: EPOC FreeBSD Internet: FreeBSD HP-UX Internet: HP-UX Hurd Internet: Hurd Inferno Internet: Inferno IRIX Internet: IRIX JavaOS Internet: JavaOS LFS Internet: LFS Linspire Internet: Linspire Linux Internet: Linux MacOS Internet: MacOS Minix Internet: Minix MorphOS Internet: MorphOS MS-DOS Internet: MS-DOS MVS Internet: MVS NetBSD Internet: NetBSD NetWare Internet: NetWare Newdeal Internet: Newdeal NEXTSTEP Internet: NEXTSTEP OpenBSD Internet: OpenBSD OS/2 Internet: OS/2 Further operating systems Internet: Further operating systems PalmOS Internet: PalmOS Plan9 Internet: Plan9 QNX Internet: QNX RiscOS Internet: RiscOS Solaris Internet: Solaris SuSE Linux Internet: SuSE Linux Unicos Internet: Unicos Unix Internet: Unix Unixware Internet: Unixware Windows 2000 Internet: Windows 2000 Windows 3.11 Internet: Windows 3.11 Windows 95 Internet: Windows 95 Windows 98 Internet: Windows 98 Windows CE Internet: Windows CE Windows Family Internet: Windows Family Windows ME Internet: Windows ME Seite 1 von 138 eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org Windows NT 3.1 Internet: Windows NT 3.1 Windows NT 4.0 Internet: Windows NT 4.0 Windows Server 2003 Internet: Windows Server 2003 Windows Vista Internet: Windows Vista Windows XP Internet: Windows XP Apple - Company Internet: Apple - Company AT&T - Company Internet: AT&T - Company Be Inc. - Company Internet: Be Inc. - Company BSD Family Internet: BSD Family Cray Inc. -

Goodforkbadfork-Lineo.Pdf
Good Fork, Bad Fork Examining the Limits of Open Source Software in the Embedded Market Tim Bird Chief Technology Officer www.lineo.com Start with 2 Definitions Definition of open source What are it’s key attributes Definition of network effects Importance of network effects for open source software What is Open Source Software? Examples Linux Apache gcc (GNU compiler) Key Attributes of Open Source Software Access to the source code Freedom to make modifications AND distribute them (free = freedom : think free speech, not free beer) Licenses that provide these attributes Availability of source is NOT enough Source Availability != Open Source QNX now has source availability For lots of money, you can buy source code to VxWorks Microsoft may ship Windows CE source code But that's NOT Open Source Key Attributes of Open Source Software Communities develop The "Linux community" This generates "network effects" What are “Network Effects”? When the value of something increases with the number of items Classic example: the telephone Two phones have limited value Whole network of phones gives each one its value Other “Network Effect” Examples Classic example: VHS videocassette tapes Once a standard develops, it pushes other formats out Market for Applications Windows APIs OS More Popularity Applications Network Effects and Linux Every feature of Linux makes it more valuable to developers Every Linux developer makes Linux have more features Virtuous cycle Open Source Network Effects (Business Benefits) Popularity Availability of engineering resources Info Skilled manpower Engineer enthusiasm Commercial effects Multi-vendor OS Competition to produce rapid development Test organizations Linux is Not Just One Community Separate communities for networking, file systems, Web servers, graphic layers, desktops, etc. -

Novell Management Tools
04 0789729849_ch03.qxd 11/10/03 12:43 PM Page 91 CHAPTER 3 Novell Management Tools Using ConsoleOne ConsoleOne is a Java-based tool for managing your network and its resources. It can be launched by running CONSOLEONE.EXE from where it was installed (default: SYS:PUBLIC\MGMT\CONSOLEONE\1.2\BIN). By default, it lets you manage Novell eDirectory objects, schema, parti- tions, and replicas and NetWare server resources. If you install other Novell products, the appropriate management capabil- ities are automatically snapped into the version of ConsoleOne installed on that server. ConsoleOne is installed during the NetWare 6.5 installation, but can also be re-installed or installed locally from the Novell client’s CD. ConsoleOne also supports remote server console access through a Java applet called RConsoleJ. To access the NetWare 6.5 server console remotely, launch ConsoleOne and browse to the desired server. Select Tools, and then Remote Console. Accessing Web Manager Web Manager is a Web-based “home page” for accessing most of the NetWare 6.5 Web-based tools and services. To access Web Manager, open your Web browser and enter your Web server’s domain name or IP address, followed by a colon and the Web Manager port, which by default is 2200. For example: 04 0789729849_ch03.qxd 11/10/03 12:43 PM Page 92 92 PART I Getting Started https://www.quills.com:2200 or https://137.65.192.1:2200 Accessing iManager iManager provides role-based management of your NetWare network, together with a nearly comprehensive set of administrative tools. -

Novell Cluster Services,. for Linux. and Netware
Novell Cluster Services,. for Linux. and NetWare. ROB BASTIAANSEN SANDER VAN VUGT Novell PRESS. Novell. Published by Pearson Education, Inc. 800 East 96th Street, Indianapolis, Indiana 46240 USA Table of Contents Introduction 1 CHAPTER 1: Introduction to Clustering and High Availability 5 Novell Cluster Services Defined 5 Shared Disk Access 6 Secondary IP Addresses 7 Clustering Terminology 8 High-Availability Solutions Overview 12 Novell Cluster Services 12 Business Continuity Clustering 13 PolyServe Matrix Server 15 Heartbeat Subsystem for High-Availability Linux 16 When Not to Cluster Applications 16 Availability Defined 18 High Availability Defined 18 Calculating Average Downtime 21 Avoiding Downtime 22 Hardware 22 Environment 23 Software 23 Procedures 24 Novell Cluster Services Requirements 24 Hardware Requirements 24 Software Requirements 26 CHAPTER 2: Examining Novell Cluster Services Architecture 27 Novell Cluster Services Objects and Modules 27 Cluster eDirectory Objects 28 Cluster Modules 31 IH Novell Cluster Services for Linux and NetWare Heartbeats, Epoch Numbers, and the Split Brain Detector 35 Removing a Failing Slave Node 36 Removing a Failed Master Node 37 Summary 37 CHAPTER 3: Clustering Design 39 Cluster Design Guidelines 39 How Many Nodes to Choose 39 Using a Heartbeat LAN or Not 40 Use NIC Teaming 41 Choosing Storage Methods 42 Mirror the Split Brain Detector Partition 48 Selecting Applications to Run in a Cluster 48 eDirectory Cluster Guidelines 50 Creating a Failover Matrix 52 Application-Specific Design Guidelines -

Twenty Years of Berkeley Unix : from AT&T-Owned to Freely
Twenty Years of Berkeley Unix : From AT&T-Owned to Freely Redistributable Marshall Kirk McKusick Early History Ken Thompson and Dennis Ritchie presented the first Unix paper at the Symposium on Operating Systems Principles at Purdue University in November 1973. Professor Bob Fabry, of the University of California at Berkeley, was in attendance and immediately became interested in obtaining a copy of the system to experiment with at Berkeley. At the time, Berkeley had only large mainframe computer systems doing batch processing, so the first order of business was to get a PDP-11/45 suitable for running with the then-current Version 4 of Unix. The Computer Science Department at Berkeley, together with the Mathematics Department and the Statistics Department, were able to jointly purchase a PDP-11/45. In January 1974, a Version 4 tape was delivered and Unix was installed by graduate student Keith Standiford. Although Ken Thompson at Purdue was not involved in the installation at Berkeley as he had been for most systems up to that time, his expertise was soon needed to determine the cause of several strange system crashes. Because Berkeley had only a 300-baud acoustic-coupled modem without auto answer capability, Thompson would call Standiford in the machine room and have him insert the phone into the modem; in this way Thompson was able to remotely debug crash dumps from New Jersey. Many of the crashes were caused by the disk controller's inability to reliably do overlapped seeks, contrary to the documentation. Berkeley's 11/45 was among the first systems that Thompson had encountered that had two disks on the same controller! Thompson's remote debugging was the first example of the cooperation that sprang up between Berkeley and Bell Labs. -

How Free Become Open and Everything Else Under the Sun
This article was published as the featured article in the Journal Media/Culture here: http://journal.media-culture.org.au/0406/02_Coleman-Hill.php How Free Become Open and Everything Else Under the Sun Biella Coleman and Benjamin Mako Hill Abstract: Free and Open Source Software (FOSS) has been adopted as a political tool by leftist activists. At the same time, it has been embraced by large corporations to extend profits and has been criticized as an integral force in late capitalism. It has been adopted by members of the growing Commons movement as a model for limiting the power of capitalism. This essay attempts to confront the variability of these relationships through a cursory analysis of each field and through an look at FOSS philosophy and practice. It argues that Free Software exists as a politically agnostic field of practice--built on and through a broadly defined philosophy. It analyzes the way that this philosophy is well suited for the spread of FOSS technologies and its translation into the terms of radically different, even oppositional, social and political movements. Author Bios and Contact Information Benjamin "Mako" Hill is a Free and Open Source Software developer and advocate. He is a director of Software in the Public Interest and a member of the Debian project -- by most accounts the single largest Free Software project. In addition to volunteer and professional Free Software work, Hill writes and speaks extensively on issues of free software, intellectual property, collaboration, and technology. email: [email protected] Biella Coleman is a cultural anthropologist from the University of Chicago currently writing her dissertation on the ethical dynamics and political implications of the Free and Open Source movement. -

Operated by Triad National Security, LLC for the U.S. Department of Energy's NNSA Container Mythbusters
Operated by Triad National Security, LLC for the U.S. Department of Energy's NNSA Container Mythbusters Debunking the Nonsense, Dissecting the Misconceptions, and Distilling the Facts of High-Performance Containering Michael Jennings (@mej0) – [email protected] Platforms Team Lead, HPC Systems Group Los Alamos National Laboratory HPC/AI Advisory Council 2019 Swiss Conference HPCXXL 2019 Winter Meeting Lugano, Switzerland Wednesday, 3 April 2019 Operated by Triad National Security, LLC for the U.S. Department of Energy's NNSA UNCLASSIFIED LA-UR-19-XXXXX Los Alamos National Laboratory Introduction • Established in 1943 as “Site Y” of the Manhattan Project • Mission: To solve National Security challenges through Scientific Excellence • One of the largest science and technology institutes in the world, conducting multidisciplinary research in fields such as national security, space exploration, renewable energy, medicine, nanotechnology, and supercomputing. • Funded primarily by the Department of Energy, we also do extensive work for/with the Departments of Defense and Homeland Security, the Intelligence Community, et al. • Our strategy reflects US government priorities including nuclear security, intelligence, defense, emergency response, nonproliferation, counterterrorism, and more. • We help to ensure the safety, security, and effectiveness of the US nuclear stockpile. • Since 1992, the United States no longer performs full-scale testing of nuclear weapons. This has necessitated continuous, ongoing leadership in large-scale simulation capabilities -

United States Court of Appeals for the FOURTH CIRCUIT
Case: 10-1482 Document: 35 Date Filed: 09/17/2010 Page: 1 No. 10-1482 IN THE United States Court of Appeals FOR THE FOURTH CIRCUIT dNOVELL, INCORPORATED, Plaintiff-Appellant, —v.— MICROSOFT CORPORATION, Defendant-Appellee. ON APPEAL FROM THE UNITED STATES DISTRICT COURT FOR THE DISTRICT OF MARYLAND BRIEF OF APPELLEE MICROSOFT CORPORATION RICHARD J. WALLIS DAVID B.TULCHIN STEVEN J. AESCHBACHER Counsel of Record MICROSOFT CORPORATION STEVEN L. HOLLEY One Microsoft Way SULLIVAN & CROMWELL LLP Redmond, Washington 98052 125 Broad Street (425) 882-8080 New York, New York 10004 (212) 558-4000 G. S TEWART WEBB VENABLE LLP 750 East Pratt Street, Suite 900 Baltimore, Maryland 21202 (410) 244-7400 Attorneys for Microsoft Corporation September 17, 2010 Case: 10-1482 Document: 35 Date Filed: 09/17/2010 Page: 2 UNITED STATES COURT OF APPEALS FOR THE FOURTH CIRCUIT DISCLOSURE OF CORPORATE AFFILIATIONS AND OTHER INTERESTS Only one form needs to be completed for a party even if the party is represented by more than one attorney. Disclosures must be filed on behalf of all parties to a civil, agency, bankruptcy or mandamus case. Corporate defendants in a criminal or post-conviction case and corporate amici curiae are required to file disclosure statements. Counsel has a continuing duty to update this information. No. _______ Caption: __________________________________________________ Pursuant to FRAP 26.1 and Local Rule 26.1, ______________________ who is _______________________, makes the following disclosure: (name of party/amicus) (appellant/appellee/amicus) 1. Is party/amicus a publicly held corporation or other publicly held entity? YES NO 2. Does party/amicus have any parent corporations? YES NO If yes, identify all parent corporations, including grandparent and great-grandparent corporations: 3. -

Wikipedia: Design of the FAT File System
Design of the FAT file system A FAT file system is a specific type of computer file system architecture and FAT a family of industry-standard file systems utilizing it. Developer(s) Microsoft, SCP, IBM, [3] The FAT file system is a legacy file system which is simple and robust. It Compaq, Digital offers good performance even in very light-weight implementations, but Research, Novell, cannot deliver the same performance, reliability and scalability as some Caldera modern file systems. It is, however, supported for compatibility reasons by Full name File Allocation Table: nearly all currently developed operating systems for personal computers and FAT12 (12- many home computers, mobile devices and embedded systems, and thus is a bit version), well suited format for data exchange between computers and devices of almost FAT16 (16- any type and age from 1981 through the present. bit versions), Originally designed in 1977 for use on floppy disks, FAT was soon adapted and FAT32 (32-bit version used almost universally on hard disks throughout the DOS and Windows 9x with 28 bits used), eras for two decades. Today, FAT file systems are still commonly found on exFAT (64- floppy disks, USB sticks, flash and other solid-state memory cards and bit versions) modules, and many portable and embedded devices. DCF implements FAT as Introduced 1977 (Standalone the standard file system for digital cameras since 1998.[4] FAT is also utilized Disk BASIC-80) for the EFI system partition (partition type 0xEF) in the boot stage of EFI- FAT12: August 1980 compliant computers. (SCP QDOS) FAT16: August 1984 For floppy disks, FAT has been standardized as ECMA-107[5] and (IBM PC DOS 3.0) ISO/IEC 9293:1994[6] (superseding ISO 9293:1987[7]). -

DR DOS for the Zfx86
DR DOS for the ZFx86 Cost Effective, Reliable, Rapid Deployment of Embedded Systems w DR DOS on the ZFx86 gets products to market quickly at the lowest development and ownership cost. w Thousands of compatible applications, drivers and utilities available free or at minimal cost. w Full documentation available. DR DOS 7.03 Key Features of DR DOS Online Manual - DRDOS is supplied with a complete The ideal embedded DOS system, online manual that contains detailed information about all designed for out-of-the-box of the features of the operating system including the basic implementation into ROM or Flash commands, and the advanced utilities. It also has online ROM with tools and associated help available for all its commands. documents available in the DRDOS Memory Management - Memory management features OEM Documentation Kit. include a set of device drivers and commands that enable w 100% MS-DOS 6.22 compatible.. you to manage memory efficiently and make as much memory as possible available to your applications. w Comprehensive DOS utility set DOS Protected Mode Services - DOS Protected Mode w Multitasking, with API for developers Services (DPMS) interface allows specially-implemented w DPMS memory manager in addition to DPMI device drivers and TSRs to operate in extended memory. w Stacker disk compression This makes more memory within the first megabyte w NWCACHE - disk caching program available to applications and other conventionally-written drivers and TSRs. Both Stacker* (the disk compression w EMM386 memory manager program), and NWCACHE (the disk cache) use DPMS. w DOS Protected Mode Services (DPMS) Disk Compression - The disk compression component w Multitasking enables you to store more information by compressing the w DR-DOS provides a full multitasking environment data.