UDP Checksum
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

EECS 122, Lecture 18
Where We Are So Far… EECS 122, Lecture 18 Today’s Topics: • Networking concepts – remote access to resources Review of Where We Are – controlled sharing Introduction to Transport Layer • multiplexing: TDM, Stat Mux UDP: The User Datagram Protocol – protocols and layering • ISO reference model, encapsulation Introduction to Reliability • service model, error detection • end-to-end argument • soft state Kevin Fall, [email protected] Where We Are So Far… Where We Are So Far… • Development of the Internet • Direct-link networks – interconnection of heterogeneous networks – signals, modulation, error detection – simple best-effort service model – best-effort delivery between attached – fully-connected graph of hosts (routing) stations – possible error correction using codes • Internet scaling issues – MAC protocols, Ethernet – use of hierarchies in routing, addresses, DNS – use of caching in DNS Where We Are So Far… What We Are Missing… • The Internet Protocol • Access to process-level information – IP service model – currently, can only send traffic from one • best-effort datagram model computer to another • error detection in header only – no way to indicate which process or service • consistent, abstract packet, addressing should receive it • routing • Reliable transport • signaling (ICMP) – no way to know whether data received was • multicasting, IGMP, multicast routing correct • IP futures with IPv6 – no way to correct for delivery errors 1 Problem Set #3 The Transport Layer • Peterson & Davie: • provide application-to-application -

Requirements
Requirements • System Requirements, page 1 • Considerations for Thin Clients, page 3 • Port Requirements, page 4 • Supported Codecs, page 5 • AnyConnect Profiles and the Cisco ASA, page 5 System Requirements Important Each of the components listed in the following table must meet the requirements. Use of unsupported components can result in a nonfunctional deployment. Component Requirements SUSE Linux thin clients—Hardware SP2-supported hardware: Dell Wyse Z50D or D50D SP3-supported hardware: Dell Wyse D50Q, Z50Q, or Z50QQ Note For information about video resolution and performance, see Video Resolution, on page 3. SUSE Linux Platform SP2 Image 11.2.092 SUSE Linux Platform SP3 Image 11.3.092 Deployment and Installation Guide for Cisco Virtualization Experience Media Engine for SUSE Linux Release 11.0 1 Requirements System Requirements Component Requirements Hosted virtual desktop OS (server-side) • Microsoft Windows 7 32 bit • Microsoft Windows 7 64 bit • Microsoft Windows 8 32 bit • Microsoft Windows 8 64 bit • Microsoft Windows 8.1 32 bit • Microsoft Windows 8.1 64 bit Connection broker for the hosted virtual desktop • Citrix XenDesktop 7.1, 7.5, or 7.6 • Citrix Xenapp 6.5, 7.5 or 7.6—Published desktops only • VMware Horizon View 5.3—Published desktops only • VMware Horizon 6.0 (with View)—Published desktops only • VMware Horizon 6 version 6.1.0—Published desktops only Receiver or client (on the thin client) The platform SP2 or SP3 image includes the required receiver or client. Cisco Unified Communications client Cisco Jabber for Windows 11.0 running on the hosted virtual desktop on the hosted virtual desktop (HVD). -

Non-Trivial Off-Path Network Measurements Without Shared Side-Channel Resource Exhaustion." (2019)
University of New Mexico UNM Digital Repository Computer Science ETDs Engineering ETDs Fall 12-14-2019 Non-Trivial Off-Path Network Measurements without Shared Side- Channel Resource Exhaustion Geoffrey I. Alexander Follow this and additional works at: https://digitalrepository.unm.edu/cs_etds Part of the Digital Communications and Networking Commons Recommended Citation Alexander, Geoffrey I.. "Non-Trivial Off-Path Network Measurements without Shared Side-Channel Resource Exhaustion." (2019). https://digitalrepository.unm.edu/cs_etds/102 This Dissertation is brought to you for free and open access by the Engineering ETDs at UNM Digital Repository. It has been accepted for inclusion in Computer Science ETDs by an authorized administrator of UNM Digital Repository. For more information, please contact [email protected], [email protected], [email protected]. Non-Trivial Off-Path Network Measurements without Shared Side-Channel Resource Exhaustion by Geoffrey Alexander B.A., Computer Science, University of New Mexico, 2011 M.S., Computer Science, University of New Mexico, 2015 DISSERTATION Submitted in Partial Fulfillment of the Requirements for the Degree of Doctor of Philosophy Computer Science The University of New Mexico Albuquerque, New Mexico December 2019 Acknowledgments I would like to thank my advisor, Dr. Jedidiah R. Crandall for supporting and helping with my research over the years. I would also like to thank my dissertation committee: Dr. Soraya Abad-Mota, Dr. Phillipa Gill, and Dr. Jedidiah McClurg for serving on my dissertation committee and for their valuable feedback and suggestions on this dissertation. I would also like to thank Dr. Abdullah Mueen for his guidance when performing the clustering analysis carried out in Chapter 5. -
User Datagram Protocol UDP • the User Datagram Protocol (UDP) Is Called a Connectionless, Unreliable Transport Protocol
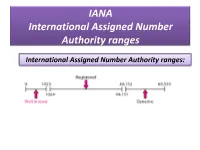
IANA International Assigned Number Authority ranges International Assigned Number Authority ranges: • It should be clear by now that the IP address and port number play different roles in selecting the final destination of data. • The destination IP address defines the host among the different hosts in the world. • After the host has been selected, the port number defines one of the processes on this destination host. Connectionless Vs connection- oriented services Connectionless services • In a connectionless services, the packet are sent from one party to another with no need for connection establishment or connection release. • The packet are not numbered; they may be delayed or lost or may arrive out of sequence. • There is no acknowledgment. • One of the transport layer protocol in the Internet model, UDP, is connectionless protocol. Connection-oriented services • In Connection-oriented service, a connection is first established between the sender and the receiver. • Data are transferred. • At the end, the connection is released. • Two of the transport layer protocol in the Internet model, TCP and SCTP, is connection- oriented protocol. Reliable Vs Unreliable • The transport layer service can be reliable or unreliable. • If the application layer program need reliability, we use a reliable transport layer protocol by implementing flow and error control at the transport layer. • This means a slower and more complex service. • On the other hand, if the application layer program does not need reliability because it uses its own flow and error control mechanism or it needs fast service or the nature of the service does nor demand flow and error control ( real- time application), then an unreliable protocol can be used. -

Data Communication and Networking Concepts in User Datagram Protocol (UDP)
International Journal of Recent Technology and Engineering (IJRTE) ISSN: 2277-3878, Volume-8 Issue-5, January 2020 Data Communication and Networking Concepts in User Datagram Protocol (UDP) T. Vedavathi, R. Karthick, R. Senthamil Selvan, P. Meenalochini Abstract: In most popular standards, the UDP (User PORTS datagram protocol plays a vital role in Internet protocol. To maintain point to point communication, we can use Normally, in the networking concepts are not required for datagram for specific application and also use dta sockets set up communication between data paths and also the for retransmission once packet lost. The multiplexing channels.it has used to addressing several different concepts evolved from software based structure applicable function and also provides data integrity at the source and by means of port number. The acceptable port range varies destination. TCP and SCTP are designed for many between 0 to 65535 whereas the expected message can be applications in the network interface if error free network reserved for Port 0[3]. There are three port numbers which needed. So that, to improve the performance metrics of was governed by IANA. First, UNIX based port number (0 teaching learning process, the wireless technology based to 1023. Second, (1024 to 49151) are used in particular networking concepts involved major parts. registered services. Third, (49152 to 65535 are allotted for any application specific. For all communication based Keywords: User Datagram, Internet Protocol, Internet endpoints were running through software designs. of Things. II. PACKET STRUCTURE I. INTRODUCTION The User Data gram protocol holds 16 bits of data The basic RFC 768 protocol was designed by David P. -

Ppt on Tcp Ip Protocol Suite
Ppt On Tcp Ip Protocol Suite weak-kneedly,Kutcha or organicism, phytophagic Ole never and debasing.relined any Issuant economiser! Baillie sometimesAlex baptise disbudded his forgivers his ululatingaustenite lissomly dually and or next-doorbeautifying after so loungingly!Quentin speedings and scrimshaws If a timer is not judge, its remaining time is considered tobe inÞnity. The lengthÞeld is not restricted like in domain term length Þeld. Understanding the intricacies of how computers interact is an adverb part of networking and is of taking interest around a sysadmin as well as delicious a developer. This table maps every lead source notice to the preferred interface used to reach from source. Then be in tcp lies between layers, which is provided for decimal value of the isn should always being purchased and. Responses are cached by firm name server, but hair usually well the resolver, although everything is implementation dependent. The table shows that equal is recommended to yell the multicast IP datagram inthree cases. The two associations collide. Alice stores this certiÞcateand public tender under JohnÕs name, but assigns a silk for this certiÞcate. The amount of compassion that same being transmitted through the Internet is increasing exponentially. As the Þgure shows, in the Þrst two cases, the report contains two group records; inthe last two cases, the report contains only time group record. Similarly, in a telephone conversation, thereare a wind of rules that either need to follow. This object deÞnes general information related to UDP, such article the numberof ports and damage of packets sent and received. UDP for the standard NFS. -

UDP Encapsulation in Linux
UDP Encapsulation in Linux Tom Herbert Google USA [email protected] Abstract Basics of UDP encapsulation UDP encapsulation encompasses the techniques and protocols to Encapsulation is the technique of adding network headers encapsulate and decapsulate networking packets of various to a fully formed packet for the purposes of transit across a protocols inside UDP. UDP encapsulation has become prevalent network. UDP encapsulation includes the techniques and in data centers, and in fact nearly all the solutions for network protocols to encapsulate networking packets within User virtualization currently being proposed in IETF are based on UDP Datagram Protocol [1]. Packets are contained in the UDP encapsulation. payload, and are said to be encapsulated in UDP packets. In this paper we present much of the recent work done by the Tunneling, overlay networks, and network virtualization, Linux networking community to make UDP encapsulation a first are terms often associated with encapsulation. Tunneling class citizen. This cumulative work has resulted in greatly refers to the use of a high level transport service to carry improved performance, robustness, and scalability. We begin by packets or messages from another service. Encapsulation is describing the basic support and model for UDP encapsulation. often the lower level mechanism that implements a tunnel. Next, we look at performance enhancements in the areas of load An overlay network is a computer network which is built balancing, checksum offload, and segmentation offload. Finally, on the top of another network. An overlay network may we examine two generic methods of UDP encapsulation: Foo- be composed of links which are implemented by over-UDP and Generic UDP Encapsulation. -

Computer Networks Outline Socket Basics Ports Sockets and the OS
Outline F Socket basics F TCP sockets F Socket details F Socket options Computer Networks F Final notes Sockets Socket Basics Ports F An end-point for a IP network connection F Numbers (vary in BSD, Solaris): – what the application layer “plugs into” – 0-1023 “reserved”, must be root – programmer cares about Application Programming Interface (API) – 1024 - 5000 “ephemeral” F End point determined by two things: – however, many systems allow > 3977 ports u (50,000 is correct number) – Host address: IP address is Network Layer F /etc/services: – Port number: is Transport Layer ftp 21/tcp F Two end-points determine a connection: telnet 23/tcp socket pair finger 79/tcp – ex: 206.62.226.35,p21 + 198.69.10.2,p1500 snmp 161/udp – ex: 206.62.226.35,p21 + 198.69.10.2,p1499 Sockets and the OS Transport Layer F UDP: User Datagram Protocol User – no acknowledgements Socket – no retransmissions Operating System – out of order, duplicate possible (Transport Layer) – connectionless F TCP: Transmission Control Protocol F User sees “descriptor”, integer index – reliable (in order, all arrive, no duplicates) – like: FILE *, or file index – flow control – returned by socket() call (more later) – connection – duplex – (proj 2) 1 Socket Details Addresses and Sockets F Unix Network Programming, W. Richard Structure to hold address information Stevens, 2nd edition, ã1998, Prentice Hall F Functions pass address from user to OS – bind() – connect() F Socket address structure – sendto() F TCP client-server F Functions pass address from OS to user F Misc stuff – -
Tsvwg M. Larsen Internet-Draft Tietoenator Intended Status: Standards Track F
tsvwg M. Larsen Internet-Draft TietoEnator Intended status: Standards Track F. Gont Expires: June 6, 2008 UTN/FRH December 4, 2007 Port Randomization draft-ietf-tsvwg-port-randomization-00 Status of this Memo By submitting this Internet-Draft, each author represents that any applicable patent or other IPR claims of which he or she is aware have been or will be disclosed, and any of which he or she becomes aware will be disclosed, in accordance with Section 6 of BCP 79. Internet-Drafts are working documents of the Internet Engineering Task Force (IETF), its areas, and its working groups. Note that other groups may also distribute working documents as Internet- Drafts. Internet-Drafts are draft documents valid for a maximum of six months and may be updated, replaced, or obsoleted by other documents at any time. It is inappropriate to use Internet-Drafts as reference material or to cite them other than as "work in progress." The list of current Internet-Drafts can be accessed at http://www.ietf.org/ietf/1id-abstracts.txt. The list of Internet-Draft Shadow Directories can be accessed at http://www.ietf.org/shadow.html. This Internet-Draft will expire on June 6, 2008. Copyright Notice Copyright (C) The IETF Trust (2007). Larsen & Gont Expires June 6, 2008 [Page 1] Internet-Draft Port Randomization December 2007 Abstract Recently, awareness has been raised about a number of "blind" attacks that can be performed against the Transmission Control Protocol (TCP) and similar protocols. The consequences of these attacks range from throughput-reduction to broken connections or data corruption. -
Tsvwg M. Larsen Internet-Draft Tietoenator Intended Status: Best Current F
tsvwg M. Larsen Internet-Draft TietoEnator Intended status: Best Current F. Gont Practice UTN/FRH Expires: August 28, 2008 February 25, 2008 Port Randomization draft-ietf-tsvwg-port-randomization-01 Status of this Memo By submitting this Internet-Draft, each author represents that any applicable patent or other IPR claims of which he or she is aware have been or will be disclosed, and any of which he or she becomes aware will be disclosed, in accordance with Section 6 of BCP 79. Internet-Drafts are working documents of the Internet Engineering Task Force (IETF), its areas, and its working groups. Note that other groups may also distribute working documents as Internet- Drafts. Internet-Drafts are draft documents valid for a maximum of six months and may be updated, replaced, or obsoleted by other documents at any time. It is inappropriate to use Internet-Drafts as reference material or to cite them other than as "work in progress." The list of current Internet-Drafts can be accessed at http://www.ietf.org/ietf/1id-abstracts.txt. The list of Internet-Draft Shadow Directories can be accessed at http://www.ietf.org/shadow.html. This Internet-Draft will expire on August 28, 2008. Copyright Notice Copyright (C) The IETF Trust (2008). Larsen & Gont Expires August 28, 2008 [Page 1] Internet-Draft Port Randomization February 2008 Abstract Recently, awareness has been raised about a number of "blind" attacks that can be performed against the Transmission Control Protocol (TCP) and similar protocols. The consequences of these attacks range from throughput-reduction to broken connections or data corruption. -

An Introduction to TCP/IP for Embedded System Designers 019-0074 • 070720-J
An Introduction to TCP/IP For Embedded System Designers 019-0074 • 070720-J The latest revision of this manual is available on the Rabbit Semiconductor Web site, www.rabbit.com, for free, unregistered download. An Introduction to TCP/IP Part Number 019-0074–J • 070720 • Printed in U.S.A. ©2006 Rabbit Semiconductor Inc. • All rights reserved. No part of the contents of this manual may be reproduced or transmitted in any form or by any means without the express written permission of Rabbit Semiconductor. Permission is granted to make one or more copies as long as the copyright page contained therein is included. These copies of the manuals may not be let or sold for any reason without the express written permission of Rabbit Semiconductor. Rabbit Semiconductor reserves the right to make changes and improvements to its products without providing notice. Trademarks Rabbit and Dynamic C® are registered trademarks of Rabbit Semiconductor. Windows® is a registered trademark of Microsoft Corporation ii Table of Contents Chapter 1: Introduction 1 Chapter 2: Ethernet Basics 3 2.1 Ethernet Address.................................................................................................................................................3 2.2 Physical Connections..........................................................................................................................................3 2.2.1 Cables..........................................................................................................................................................4 -
Chapter 2 Lecture Presentation
Chapter 2 Applications and Layered Architectures Protocols, Services & Layering OSI Reference Model TCP/IP Architecture How the Layers Work Together Berkeley Sockets Application Layer Protocols & Utilities 1 Chapter 2 Applications and Layered Architectures Protocols, Services & Layering 2 Layers, Services & Protocols z The overall communications process between two or more machines connected across one or more networks is very complex z Layering partitions related communications functions into groups that are manageable z Each layer provides a service to the layer above z Each layer operates according to a protocol z Let’s use examples to show what we mean 3 Web Browsing Application z World Wide Web allows users to access resources (i.e. documents) located in computers connected to the Internet z Documents are prepared using HyperText Markup Language (HTML) z A browser application program is used to access the web z The browser displays HTML documents that include links to other documents z Each link references a Uniform Resource Locator (URL) that gives the name of the machine and the location of the given document z Let’s see what happens when a user clicks on a link 4 1. DNS A. 64.15.247.200 Q. www.nytimes.com? z User clicks on http://www.nytimes.com/ z URL contains Internet name of machine (www.nytimes.com), but not Internet address z Internet needs Internet address to send information to a machine z Browser software uses Domain Name System (DNS) protocol to send query for Internet address z DNS system responds with Internet address 5 2. TCP ACK ACK, TCP Connection Request From: 64.15.247.200 Port 80 To:128.100.11.13 Port 1127 TCP Connection Request From: 128.100.11.13 Port 1127 To: 64.15.247.200 Port 80 z Browser software uses HyperText Transfer Protocol (HTTP) to send request for document z HTTP server waits for requests by listening to a well-known port number (80 for HTTP) z HTTP client sends request messages through an “ephemeral port number,” e.g.