Irc Software for Mac
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Lithium Hosting, Llc
Lithium Hosting, llc Acceptable Use Policy This Acceptable Use Policy ("AUP") governs your use of the Services and is incorporated by reference into Lithium Hosting, llc's Customer Master Agreement / Terms of Service. Unless otherwise stated, defined terms in this AUP have the meanings provided in the Terms of Service. Lithium Hosting, llc may modify this document at any time without notice. This document sets forth the principles, guidelines and requirements of the Acceptable Use Policy of Lithium Hosting, llc ("Company") governing the use by the Customer ("Customer") of the Company's products and services ("Products and Services"). The Purpose of the Lithium Hosting, llc Acceptable Use Policy, hereinafter referred to as the AUP, is to comply with all federal, state, and local laws coupled with protecting the network security, network availability, physical security, Customer privacy, and other factors affecting the services provided by Lithium Hosting, llc. Lithium Hosting, llc reserves the right to impose reasonable rules and regulations regarding the use of its services provided to all Customers and such rules and regulations are subject to change. Such rules and regulations are located on the Internet at https://lithiumhosting.com/acceptable-use-policy. The AUP is not an all inclusive exhaustive list and Lithium Hosting, llc reserves the right to modify the AUPs at any time as needed, effective upon either the posting of the modified AUPs to https://lithiumhosting.com/acceptable-use-policy or notification to the Customer via their client portal. Acceptance and execution of the Customer Master Agreement / Terms of Service binds all parties to Lithium Hosting, llc stated AUP at the time the contract is executed and as modified from time to time. -
A Short IRC Primer
A short IRC primer Nicolas Pioch Nap on IRC <Nicolas Pi och g ras p ins al yo nf r> Text conversion by Owe Rasmussen Sorg <drasmus d tek ch al mer s se> Edition b February Abstract Have you ever wanted to talk with other computer users in other parts of the world Well guess what::: You can The program is called IRC Internet Relay Chat and it is networked much over North America Asia Europ e and Oceania This program is a substitution for talk and many other multiple talk programs you might have read ab out When you are talking on IRC everything you type will instantly b e transmitted around the world to other users that might b e watching their terminals at the time they can then type something and respond to your messages and vice versa I should warn you that the program can b e very addictive once you b egin to make friends and contacts on IRC esp ecially when you learn how to discuss in languages::: Topics of discussion on IRC are varied just like the topics of Usenet newsgroups are varied Technical and p olitical discussions are p opular es p ecially when world events are in progress IRC is also a way to expand your horizons as p eople from many countries and cultures are on hours a day Most conversations are in English but there are always channels in German Japanese French Finnish and o ccasionally other languages IRC gained international fame during the late Persian Gulf War when up dates from around the world came across the wire and most p eople on IRC gathered on a single channel to hear these rep orts CONTENTS Contents -

Abstract Introduction Methodology
Kajetan Hinner (2000): Statistics of major IRC networks: methods and summary of user count. M/C: A Journal of Media and Culture 3(4). <originally: http://www.api-network.com/mc/0008/count.html> now: http://www.media-culture.org.au/0008/count.html - Actual figures and updates: www.hinner.com/ircstat/ Abstract The article explains a successful approach to monitor the major worldwide Internet Relay Chat (IRC) networks. It introduces a new research tool capable of producing detailed and accurate statistics of IRC network’s user count. Several obsolete methods are discussed before the still ongoing Socip.perl program is explained. Finally some IRC statistics are described, like development of user figures, their maximum count, IRC channel figures, etc. Introduction Internet Relay Chat (IRC) is a text-based service, where people can meet online and chat. All chat is organized in channels which a specific topic, like #usa or #linux. A user can be taking part in several channels when connected to an IRC network. For a long time the only IRC network has been EFnet (Eris-Free Network, named after its server eris.berkeley.edu), founded in 1990. The other three major IRC networks are Undernet (1993), DALnet (1994) and IRCnet, which split off EFnet in June 1996. All persons connecting to an IRC network at one time create that IRC network’s user space. People are constantly signing on and off, the total number of users ever been to a specific IRC network could be called social space of that IRC network. It is obvious, that the IRC network’s social space by far outnumbers its user space. -

There Are Two Dedicated Dspace IRC (Internet Relay Chat) Channels (I.E
IRC Code of Conduct All DSpace support channels, mailing lists and meetings follow the LYRASIS Code of Conduct. We ask you to remain respectful in all discussions. We also encourage you to report any violations of the code of conduct to LYRASIS (see the Code of Conduct for more details). DSpace chat has moved to Slack Our old IRC channels are essentially unmonitored these days. Instead, we recommend joining our DSpace.org Slack for any chat-based support. You are also welcome to email your question to the dspace-tech Mailing List as an alternative, or choose one of the other DSpace Sup port options. There are two dedicated DSpace IRC (internet relay chat) channels (i.e. "rooms") on the irc.freenode.net server: #dspace (irc://irc.freenode.net/dspace) - all DSpace discussions and live Q & A. This channel is unlogged. #duraspace (irc://irc.freenode.net/duraspace) - Old duraspace community channel (no longer used). As of July 2018, this channel is unlogged. Pri or years logs are still available/archived. If you do not have access to an IRC client, or are new to IRC, the following web interfaces are very easy way to get started: Login to #dspace IRC at: http://webchat.freenode.net?channels=dspace Enter in a nickname of your choice (e.g. firstName_lastName) & click "Connect" Login to #duraspace IRC at: http://webchat.freenode.net?channels=duraspace Enter in a nickname of your choice (e.g. firstName_lastName) & click "Connect" Or you can login to both IRC channels at the same time: http://webchat.freenode.net?channels=duraspace,dspace For a list of IRC client software, see: http://en.wikipedia.org/wiki/Comparison_of_Internet_Relay_Chat_clients Many current Instant Messaging (IM) clients also support IRC. -
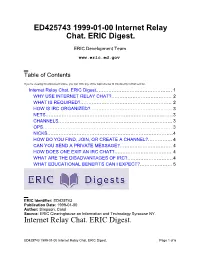
Internet Relay Chat. ERIC Digest
ED425743 1999-01-00 Internet Relay Chat. ERIC Digest. ERIC Development Team www.eric.ed.gov Table of Contents If you're viewing this document online, you can click any of the topics below to link directly to that section. Internet Relay Chat. ERIC Digest............................................... 1 WHY USE INTERNET RELAY CHAT?..................................... 2 WHAT IS REQUIRED?........................................................ 2 HOW IS IRC ORGANIZED?.................................................. 3 NETS..............................................................................3 CHANNELS......................................................................3 OPS............................................................................... 3 NICKS.............................................................................4 HOW DO YOU FIND, JOIN, OR CREATE A CHANNEL?............... 4 CAN YOU SEND A PRIVATE MESSAGE?................................ 4 HOW DOES ONE EXIT AN IRC CHAT?................................... 4 WHAT ARE THE DISADVANTAGES OF IRC?............................4 WHAT EDUCATIONAL BENEFITS CAN I EXPECT?....................5 ERIC Identifier: ED425743 Publication Date: 1999-01-00 Author: Simpson, Carol Source: ERIC Clearinghouse on Information and Technology Syracuse NY. Internet Relay Chat. ERIC Digest. ED425743 1999-01-00 Internet Relay Chat. ERIC Digest. Page 1 of 6 www.eric.ed.gov ERIC Custom Transformations Team THIS DIGEST WAS CREATED BY ERIC, THE EDUCATIONAL RESOURCES INFORMATION CENTER. FOR MORE -
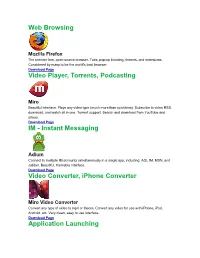
Instant Messaging Video Converter, Iphone Converter Application
Web Browsing Mozilla Firefox The premier free, open-source browser. Tabs, pop-up blocking, themes, and extensions. Considered by many to be the world's best browser. Download Page Video Player, Torrents, Podcasting Miro Beautiful interface. Plays any video type (much more than quicktime). Subscribe to video RSS, download, and watch all in one. Torrent support. Search and download from YouTube and others. Download Page IM - Instant Messaging Adium Connect to multiple IM accounts simultaneously in a single app, including: AOL IM, MSN, and Jabber. Beautiful, themable interface. Download Page Video Converter, iPhone Converter Miro Video Converter Convert any type of video to mp4 or theora. Convert any video for use with iPhone, iPod, Android, etc. Very clean, easy to use interface. Download Page Application Launching Quicksilver Quicksilver lets you start applications (and do just about everything) with a few quick taps of your fingers. Warning: start using Quicksilver and you won't be able to imagine using a Mac without it. Download Page Email Mozilla Thunderbird Powerful spam filtering, solid interface, and all the features you need. Download Page Utilities The Unarchiver Uncompress RAR, 7zip, tar, and bz2 files on your Mac. Many new Mac users will be puzzled the first time they download a RAR file. Do them a favor and download UnRarX for them! Download Page DVD Ripping Handbrake DVD ripper and MPEG-4 / H.264 encoding. Very simple to use. Download Page RSS Vienna Very nice, native RSS client. Download Page RSSOwl Solid cross-platform RSS client. Download Page Peer-to-Peer Filesharing Cabos A simple, easy to use filesharing program. -

Internet Evidence Finder Report
Patrick Leahy Center for Digital Investigation (LCDI) Internet Evidence Finder Report Written and Researched by Nick Murray 175 Lakeside Ave, Room 300A Phone: 802/865-5744 Fax: 802/865-6446 http://www.lcdi.champlin.edu July 2013 IEF Report 6/28/2013 Page 1 of 33 Patrick Leahy Center for Digital Investigation (LCDI) Disclaimer: This document contains information based on research that has been gathered by employee(s) of The Senator Patrick Leahy Center for Digital Investigation (LCDI). The data contained in this project is submitted voluntarily and is unaudited. Every effort has been made by LCDI to assure the accuracy and reliability of the data contained in this report. However, LCDI nor any of our employees make no representation, warranty or guarantee in connection with this report and hereby expressly disclaims any liability or responsibility for loss or damage resulting from use of this data. Information in this report can be downloaded and redistributed by any person or persons. Any redistribution must maintain the LCDI logo and any references from this report must be properly annotated. Contents Introduction ............................................................................................................................................................. 5 Prior Work: .......................................................................................................................................................... 7 Purpose and Scope: ............................................................................................................................................ -

Freiesmagazin 06/2011
freiesMagazin Juni 2011 Topthemen dieser Ausgabe Ubuntu 11.04 – Vorstellung des Natty Narwhal Seite 4 Am 28. April 2011 wurde Ubuntu 11.04 freigegeben. Der Artikel gibt einen Überblick über die Neuerungen der Distribution mit besonderem Augenmerk auf das neue Desktop-System „Unity“, welches im Vorfeld bereits für viel Furore sorgte. (weiterlesen) GNOME 3.0: Bruch mit Paradigmen Seite 15 Mit der Freigabe von GNOME 3 bricht der Entwicklerkreis rund um die Desktopumgebung mit vielen gängigen Paradigmen der Benutzerführung und präsentiert ein weitgehend überarbeite- tes Produkt, das zahlreiche Neuerungen mit sich bringt. Drei wesentliche Punkte sind in die neue Generation der Umgebung eingegangen: eine Erneuerung der Oberfläche, Entfernung von unnötigen Komponenten und eine bessere Außendarstellung. (weiterlesen) UnrealIRC – gestern „Flurfunk“, heute „Chat“ Seite 24 Ungern brüllt man Anweisungen von Büro zu Büro. Damit Angestellte miteinander kommunizie- ren können, wird vielerorts zum Telefon gegriffen. Wird bereits telefoniert, muss die dienstliche E-Mail herhalten, um Kommunikationsbedürfnisse zu befriedigen. Was aber, wenn die Leitung belegt und das Senden einer E-Mail derzeit nicht möglich ist? Ein Chat ist die Lösung für das Problem. (weiterlesen) © freiesMagazin CC-BY-SA 3.0 Ausgabe 06/2011 ISSN 1867-7991 MAGAZIN Editorial Traut Euch und macht mit Wer nicht wagt, der nicht gewinnt Dies gilt im Übrigen für fast alles im Leben: sei Inhalt Die Reaktionen auf unsere These im Editorial es die Frage nach einer Gehaltserhöhung, das des letzten Monats [1] waren recht gut. Zur Erin- erste zögerliche Gespräch mit seinem Schwarm Linux allgemein nerung: Wir fragten, ob – nach der bescheidenen oder der Umzug ins Ausland, um eines neues Le- Ubuntu 11.04 – Vorstellung von Natty S. -
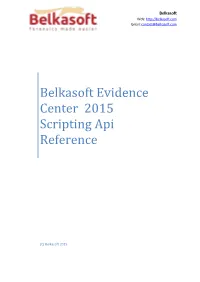
Belkasoft Evidence Center 2015 Scripting Api Reference
Belkasoft Web: http://belkasoft.com Email: [email protected] Belkasoft Evidence Center 2015 Scripting Api Reference (C) Belkasoft 2015 BELKASOFT EVIDENCE CENTER 2015 SCRIPTING API REFERENCE Table of Contents API Namespace .................................................................................................................................. 12 Browser Class................................................................................................................................. 12 Browser.CacheItems Property ................................................................................................... 13 Browser.Cookies Property ......................................................................................................... 14 Browser.DownloadedFiles Property .......................................................................................... 14 Browser.Favorites Property ....................................................................................................... 14 Browser.FormValues Property .................................................................................................. 14 Browser.Passwords Property .................................................................................................... 15 Browser.TypedUrls Property ..................................................................................................... 15 Browser.Urls Property ............................................................................................................... 15 -

Machine Learning and Cybersecurity: Studying Network Behaviour to Detect Anomalies
Machine Learning and Cybersecurity: Studying network behaviour to detect anomalies Jiawen Chen July 25, 2018 MSc in High Performance Computing with Data Science The University of Edinburgh Year of Presentation: 2018 Abstract Cybersecurity is an indispensable part of the Internet nowadays as almost everything can be connected by Internet. Individual privacy and property will face great danger if they are attacked by malware. This project aims to use the machine learning knowledge to build a classifier that can detect malware behaviour and avoid further damage to the network and its entity. The dataset used in this project is the CTU-13 dataset[1], which is NetFlow traffic from the normal, malware infected and background hosts. The classifier is built with the labelled normal and infected NetFlow, then applied to the unlabelled background NetFlow. This project follows the O’Neil & Schutt data science process[7] to process the data. The data is cleaned and processed, then aggregate based on time window to create a new dataset with the extracted features. This new dataset is the inputs of the following machine learning classification model: logistic regression, decision tree and random forest. Random forest model with an optimal threshold turns out to be the best model with an accuracy of 0.946 on the test dataset. Further application with this model is also implemented to the background traffic to detect potential malware. Keywords: Cybersecurity, NetFlow, Data science, Machine learning, Model building Contents Chapter 1 Introduction ....................................................................................................... -
Acl Zope-Plone3 Zope-Externaleditor 0. Poppler-Utils 0. Xtrans-Dev
libdevel-declare-perl libisc50 libparrot1.4.0 libgssrpc4 gcj-4.4-jre libbeecrypt7 0. python-logilab-astng libbind9-50 libcontext-preserve-perl 0. 2.43902439024 odbcinst1debian1 1.06382978723 0. 0. 0. 0. 0. 0. 2.40963855422 0. gnome-mime-data 0. 1.06382978723 0. libbeecrypt-dev 0. 0. libisccc50 0. libparrot-dev 0. parrot 0. pike7.6-gdbm pike7.6 libplasma-ruby1.8 gcj-4.4-jdk libgcj10-awt 0. 0. libasn1-8-heimdal libkdb5-4 libkadm5srv6 0. 0. 0. 0. libpoconet8-dbg 1.230228471 libcommons-net-java 0. kdegames-card-data pylint kbreakout odbcinst 0. 0. 4.42477876106 0. 0. libmono-system2.0-cil 0.0. libmono-security2.0-cil 0. 0. 0. 3.84615384615 libmoosex-declare-perl 0. 0. 0. sendmail-cf kbounce librpm-dev gcj-jdk 0. libdns50 libpococrypto8-dbg 1.22807017544 libgnomevfs2-0 libhx509-4-heimdal 3.84615384615 kdegames-mahjongg-data 2.66666666667 1.28205128205 0. 4.42477876106 0. 0. 0. 2.63157894737 2.66666666667 0. 0. libgcj10-dev libisccfg50 0. parrot-minimal libkrb5-dev kblocks unixodbc python-logilab-common 0. libplasma-ruby 0. 0. kamera gcj 0. kcron 2.7027027027 0. 0. 0. 0. 0. 0. 0. 0. libatk1-ruby1.8 0. 0. 0. libgnomevfs2-common sensible-mda sendmail sendmail-bin salliere libcsv-java 0. caudium 2.66666666667 pike7.6-image 0. libpoconetssl8-dbg 0. 0. 0. 0. libroken18-heimdal kdesnake 4. 2.66666666667 kblackbox 0. 0. 0. 0. 0. kcolorchooser 0. 0. knetworkconf 0. libaliased-perl 0. 0. 0. plasma-scriptengine-ruby 0. 0. gcj-jre libmalaga7 0.0. 1.33333333333 0. mono-2.0-gac 0. -

Introduction to Online Sexual Exploitation Curriculum 1 Safe Online Outreach Project Learning Objectives
Introduction To Online Sexual Exploitation: Curriculum February 2003 Safe OnLine Outreach Project © M. Horton 2003 Safe OnLine Outreach Project Acknowledgements This document is the result of many hours of hard work and dedication. I'd like to thank Renata Karrys, Jaynne Aster, Nikki O'Halloran, Charlaine Avery, Lisa Ingvallsen and Elizabeth Nethery for their support and assistance in producing this document. Additionally the SOLO Advisory Committee, the Canadian National Crime Prevention - Community Mobilization Program, the Vancouver Foundation, Athabasca University/MediaCan and Parents Against Sexual Abuse have all been instrumental in turning this idea into a Project. Lastly, David and Conor have been silent contributors to this project since it began. Their support is woven into each page. Merlyn Horton SOLO Project Coordinator February 2003 Safe OnLine Outreach Project February 3, 2003 Introduction to the Curriculum Dear Reader, The curriculum you hold in your hands was produced in a former pottery studio in the middle of a coastal rain forest in British Columbia, Canada; the physical launch pad for this examination of a virtual issue. It is the result of three years of research. This introduction is intended to outline a context for the curriculum and to give you an overview of how to use this curriculum, who should present this curriculum and how appropriate audiences might be chosen. Context The philosophical foundation for this curriculum, and indeed for the Safe OnLine Outreach Project, is the United Nations Convention on the Rights of the Child (CRC)1. The CRC is one of four Conventions created by the United Nations to further the goal of recognizing the inherent dignity and rights of all members of the human family2.