Balancing Privacy and Accountability in Digital Payment Methods Using Zk-Snarks
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

T U M a Digital Wallet Implementation for Anonymous Cash
Technische Universität München Department of Informatics Bachelor’s Thesis in Information Systems A Digital Wallet Implementation for Anonymous Cash Oliver R. Broome Technische Universität München Department of Informatics Bachelor’s Thesis in Information Systems A Digital Wallet Implementation for Anonymous Cash Implementierung eines digitalen Wallets for anonyme Währungen Author Oliver R. Broome Supervisor Prof. Dr.-Ing. Georg Carle Advisor Sree Harsha Totakura, M. Sc. Date October 15, 2015 Informatik VIII Chair for Network Architectures and Services I conrm that this thesis is my own work and I have documented all sources and material used. Garching b. München, October 15, 2015 Signature Abstract GNU Taler is a novel approach to digital payments with which payments are performed with cryptographically generated representations of actual currencies. The main goal of GNU Taler is to allow taxable anonymous payments to non-anonymous merchants. This thesis documents the implementation of the Android version of the GNU Taler wallet, which allows users to create new Taler-based funds and perform payments with them. Zusammenfassung GNU Taler ist ein neuartiger Ansatz für digitales Bezahlen, bei dem Zahlungen mit kryptographischen Repräsentationen von echten Währungen getätigt werden. Das Hauptziel von GNU Taler ist es, versteuerbare, anonyme Zahlungen an nicht-anonyme Händler zu ermöglichen. Diese Arbeit dokumentiert die Implementation der Android-Version des Taler-Portemonnaies, der es Benutzern erlaubt, neues Taler-Guthaben zu erzeugen und mit ihnen Zahlungen zu tätigen. I Contents 1 Introduction 1 1.1 GNU Taler . .2 1.2 Goals of the thesis . .2 1.3 Outline . .3 2 Implementation prerequisites 5 2.1 Native libraries . .5 2.1.1 Libgcrypt . -
The Bitcoin Trading Ecosystem
ArcaneReport(PrintReady).qxp 21/07/2021 14:43 Page 1 THE INSTITUTIONAL CRYPTO CURRENCY EXCHANGE INSIDE FRONT COVER: BLANK ArcaneReport(PrintReady).qxp 21/07/2021 14:43 Page 3 The Bitcoin Trading Ecosystem Arcane Research LMAX Digital Arcane Research is a part of Arcane Crypto, bringing LMAX Digital is the leading institutional spot data-driven analysis and research to the cryptocurrency exchange, run by the LMAX Group, cryptocurrency space. After launch in August 2019, which also operates several leading FCA regulated Arcane Research has become a trusted brand, trading venues for FX, metals and indices. Based on helping clients strengthen their credibility and proven, proprietary technology from LMAX Group, visibility through research reports and analysis. In LMAX Digital allows global institutions to acquire, addition, we regularly publish reports, weekly market trade and hold the most liquid digital assets, Bitcoin, updates and articles to educate and share insights. Ethereum, Litecoin, Bitcoin Cash and XRP, safely and securely. Arcane Crypto develops and invests in projects, focusing on bitcoin and digital assets. Arcane Trading with all the largest institutions globally, operates a portfolio of businesses, spanning the LMAX Digital is a primary price discovery venue, value chain for digital nance. As a group, Arcane streaming real-time market data to the industry’s deliver services targeting payments, investment, and leading indices and analytics platforms, enhancing trading, in addition to a media and research leg. the quality of market information available to investors and enabling a credible overview of the Arcane has the ambition to become a leading player spot crypto currency market. in the digital assets space by growing the existing businesses, invest in cutting edge projects, and LMAX Digital is regulated by the Gibraltar Financial through acquisitions and consolidation. -
3Rd Global Cryptoasset Benchmarking Study
3RD GLOBAL CRYPTOASSET BENCHMARKING STUDY Apolline Blandin, Dr. Gina Pieters, Yue Wu, Thomas Eisermann, Anton Dek, Sean Taylor, Damaris Njoki September 2020 supported by Disclaimer: Data for this report has been gathered primarily from online surveys. While every reasonable effort has been made to verify the accuracy of the data collected, the research team cannot exclude potential errors and omissions. This report should not be considered to provide legal or investment advice. Opinions expressed in this report reflect those of the authors and not necessarily those of their respective institutions. TABLE OF CONTENTS FOREWORDS ..................................................................................................................................................4 RESEARCH TEAM ..........................................................................................................................................6 ACKNOWLEDGEMENTS ............................................................................................................................7 EXECUTIVE SUMMARY ........................................................................................................................... 11 METHODOLOGY ........................................................................................................................................ 14 SECTION 1: INDUSTRY GROWTH INDICATORS .........................................................................17 Employment figures ..............................................................................................................................................................................................................17 -

Digital Trade Coin: Towards a More Stable Digital Currency Rsos.Royalsocietypublishing.Org Alex Lipton, Thomas Hardjono and Alex Pentland
Digital trade coin: towards a more stable digital currency rsos.royalsocietypublishing.org Alex Lipton, Thomas Hardjono and Alex Pentland MIT Connection Science, Massachusetts Institute of Technology, Cambridge, MA, USA Research TH, """"-"""#-('&)-()*" Cite this article: Lipton A, Hardjono T, We study the evolution of ideas related to creation of asset- Pentland A. !"#$ Digital trade coin: towards a backed currencies over the last 200 years and argue that recent more stable digital currency. R. Soc. open sci. developments related to distributed ledger technologies and !: #$"#%%. blockchains give asset-backed currencies a new lease of life. We http://dx.doi.org/#".#"&$/rsos.#$"#%% propose a practical mechanism combining novel technological breakthroughs with well-established hedging techniques for building an asset-backed transactional oriented cryptocurrency, which we call the digital trade coin (DTC). We show that in its Received: '# January !"#$ mature state, the DTC can serve as a much-needed counterpoint Accepted: #$ June !"#$ to fiat reserve currencies of today. #. Introduction Subject Category: This paper describes the concept of the asset-backed digital Computer science trade coins (DTCs), currently under development at MIT [1]. It outlines an approach to building a consortium of sponsors, Subject Areas: who contribute real assets, a narrow bank handling financial cryptography/human-computer transactions involving fiat currencies, and an administrator, who interaction/software issues the corresponding digital token in exchange for fiat payments and makes fiat payments in exchange for digital tokens. Keywords: In short, our proposal is to apply distributed ledger technology to blockchain technology, digital currency, give a new lease of life to the old notion of a sound asset-backed currency, and to use this currency as a transactional tool for a large electronic cash pool of potential users, including small and medium enterprises and individuals. -

Escaping the Ossification Trap with Gnunet
Escaping the Ossification Trap with GNUnet Christian Grothoff BFH & The GNU Project 25.1.2018 \We shape our tools, and thereafter our tools shape us". {John Culkin What can be done? I Democracies are slow ) Effective regulation of mega-corporations exists only under dictatorships Dictatorship or Corpocracy? Regulation? I Charles Stross (@34c4) warns: Companies are AIs that develop faster than the law I Julia Reda (@IGF) warns: Regulation of platforms paradoxically can give them more power Regulation? I Charles Stross (@34c4) warns: Companies are AIs that develop faster than the law I Julia Reda (@IGF) warns: Regulation of platforms paradoxically can give them more power I Democracies are slow ) Effective regulation of mega-corporations exists only under dictatorships Dictatorship or Corpocracy? Better Technology! Data protection! Decentralization! Self-Organization! Technological impact assessment!1 1Difficult, but better than design-by-buzzword! Technological impact assessment case-study: Name systems DNS/DNSSEC DNS Server Root Zone a.root-servers.net. www.example.com? a.gtld-servers.net.test E2D3C9.... DNSSEC Trust Anchor NS . S4LXnQiBS... 49AAC1... DS RRSIG www.example.com? Recursive DNS Server Stub www.example.com? Name .com Resolver Server NS a.gtld-servers.net.test a.gtld-servers.net. A 93.184.216.119 DS 3490A6.... RRSIG example.com. K0rp9n... RRSIG com. U/ZW6P3c... AD www.example.com? RRSIG A 93.184.216.119 example.com. K0rp9n... DNS Server example.com a.iana-servers.net. RAINS Authority Server Root Zone 44 ) com ZK ; :registry www.example.com? -
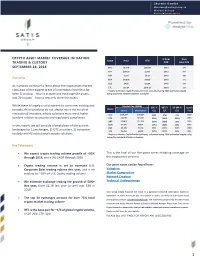
Crypto Asset Market Coverage Initiation: Trading
Sherwin Dowlat [email protected] Michael Hodapp [email protected] CRYPTO ASSET MARKET COVERAGE INITIATION: % from Days Name Price ATH TRADING & CUSTODY ATH Since ATH SEPTEMBER 18, 2018 BTC $6,270 $20,089 (69%) 274 ETH $197.86 $1,432 (86%) 247 XRP $.273 $3.84 (93%) 256 Overview BCH $420.06 $4,330 (90%) 271 EOS $4.90 $22.89 (79%) 141 As investors continue to learn about the cryptoasset market LTC $52.34 $375.29 (86%) 272 class, two of the biggest areas of uncertainty have thus far * Refers to Market Capitalization estimate, calculated using 2050 estimated supply using respective network inflation schedules been 1) trading – how to acquire and exchange the assets, and 2) custody – how to securely store the assets. While there is largely a solid market for consumer trading and Market Cap ($MM) 30D % 90D % 52-Wk % Launch Name custody, these products do not always meet the needs of Current 2050 Implied* G/L G/L G/L Year institutional investors, whose solutions must meet higher BTC $108,304 $131,567 (3%) (7%) 45% 2009 burdens relative to security and regulatory compliance. ETH $20,186 $29,081 (35%) (62%) (30%) 2015 XRP $10,874 $27,316 (19%) (50%) 38% 2013 In this report, we will provide a breakdown of the current BCH $7,290 $8,814 (27%) (53%) (2%) 2017 $4,438 $7,150 (6%) (54%) 643% 2018 landscape for 1) exchanges, 2) OTC providers, 3) consumer EOS LTC $3,053 $4,390 (10%) (47%) (4%) 2011 custody and 4) institutional custody solutions. * Refers to Market Capitalization estimate, calculated using 2050 estimated supply using respective network inflation schedules. -

Bitwise Asset Management, Inc., NYSE Arca, Inc., and Vedder Price P.C
MEMORANDUM TO: File No. SR-NYSEArca-2019-01 FROM: Lauren Yates Office of Market Supervision, Division of Trading and Markets DATE: March 20, 2019 SUBJECT: Meeting with Bitwise Asset Management, Inc., NYSE Arca, Inc., and Vedder Price P.C. __________________________________________________________________________ On March 19, 2019, Elizabeth Baird, Christian Sabella, Natasha Greiner, Michael Coe, Edward Cho, Neel Maitra, David Remus (by phone), and Lauren Yates from the Division of Trading and Markets; Charles Garrison, Johnathan Ingram, Cindy Oh, Andrew Schoeffler (by phone), Amy Starr (by phone), Sara Von Althann, and David Walz (by phone) from the Division of Corporation Finance; and David Lisitza (by phone) from the Office of General Counsel, met with the following individuals: Teddy Fusaro, Bitwise Asset Management, Inc. Matt Hougan, Bitwise Asset Management, Inc. Hope Jarkowski, NYSE Arca, Inc. Jamie Patturelli, NYSE Arca, Inc. David DeGregorio, NYSE Arca, Inc. (by phone) Tom Conner, Vedder Price P.C. John Sanders, Vedder Price P.C. The discussion concerned NYSE Arca, Inc.’s proposed rule change to list and trade, pursuant to NYSE Arca Rule 8.201-E, shares of the Bitwise Bitcoin ETF Trust. Bitwise Asset Management, Inc. also provided the attached presentation to the Commission Staff. Bitwise Asset Management Presentation to the U.S. Securities and Exchange Commission March 19, 2019 About Bitwise 01 VENTURE INVESTORS Pioneer: Created the world’s first crypto index fund. 02 TEAM BACKGROUNDS Specialist: The only asset we invest in is crypto. 03 Experienced: Deep expertise in crypto, asset management and ETFs. 2 Today’s Speakers Teddy Fusaro Matt Hougan Chief Operating Officer Global Head of Research Previously Senior Vice President and Senior Previously CEO of Inside ETFs. -
(DISSENS) Open Identity Summit 2021
Decentralized Identities for Self-sovereign End-users (DISSENS) Open Identity Summit 2021 Martin Schanzenbach 1.6.2021 • Unique benefits over existing solutions: • No gatekeepers; no vendor lock-in. • Support for non-interactive business processes. • Scalability and sustainability. • Integration in a popular e-commerce framework (WooCommerce) as pilot • Use of OpenID Connect standard for interoperability. • GNU Taler plugin for usable one-click account-less payments. • Academic institutions as credential issuers highlighting federation capabilities. Objectives • Combination of user-centric, privacy-friendly personal data sharing and payments: • Self-sovereign identity system re:claimID eliminates need for Web accounts. • Privacy-friendly payment system GNU Taler suitable for Digital Euro.1 1David Chaum et al, \How to Issue a CBDC", Swiss National Bank, 2021; https://www.snb.ch/en/mmr/papers/id/working_paper_2021_03 1 • Integration in a popular e-commerce framework (WooCommerce) as pilot • Use of OpenID Connect standard for interoperability. • GNU Taler plugin for usable one-click account-less payments. • Academic institutions as credential issuers highlighting federation capabilities. Objectives • Combination of user-centric, privacy-friendly personal data sharing and payments: • Self-sovereign identity system re:claimID eliminates need for Web accounts. • Privacy-friendly payment system GNU Taler suitable for Digital Euro.1 • Unique benefits over existing solutions: • No gatekeepers; no vendor lock-in. • Support for non-interactive business processes. • Scalability and sustainability. 1David Chaum et al, \How to Issue a CBDC", Swiss National Bank, 2021; https://www.snb.ch/en/mmr/papers/id/working_paper_2021_03 1 Objectives • Combination of user-centric, privacy-friendly personal data sharing and payments: • Self-sovereign identity system re:claimID eliminates need for Web accounts. -

Bulletin Issue 37
Issue 37 Bulletin Fall 2020 Contents I've had the good fortune of being at the FSF for over seventeen years – page 1: FSF at 35: Why free software nearly half of the thirty-five years matters more than ever we’re celebrating today. I'm so page 3: Celebrating the FSF's tireless thankful for all of you – the members, commitment volunteers, and supporters – who page 4: How Tor improves usability have stuck with us through the ups without compromising user privacy and downs. page 7: Free software payment I miss seeing so many of you in system launches at Swiss university person, hearing your stories, and page 9: Why providing source code getting updates on your projects and organizing efforts. This work that we for unmodified works is important do together, standing up to some of page 10: Updates from the FSF Tech the most powerful and wealthy Team corporations and governments on the FSF at 35: Why free software matters more than ever By John Sullivan Executive Director These are excerpts from John’s talk at the FSF35 anniversary celebration, edited for length and clarity. You can watch the full event videos at u.fsf.org/35vid. hope you have been enjoying our I small celebration of the thirty- five years that the FSF and our supporters have been hacking, The FSF thirty-fifth anniversary artwork campaigning, organizing, and was inspired by the interdependence of educating for user freedom. organisms in a coral reef. 1 planet, can be exhausting. This problem as companies having grown pandemic has been hell on people in too large, rather than companies so many ways, and I've wondered at being based on fundamentally unjust several points whether we should power. -

Bitcoin's Investment Thesis
Edison Explains Bitcoin’s investment thesis Part three: Durability and transferability Negative Positive X Cryptocurrencies – irrational recourse. The story of a German programmer who forgot hype or financial revolution? the password to his hard drive containing more than US$200m worth of BTC made the headlines earlier this Bitcoin (BTC) and other digital year. assets have been making the headlines in recent months, Multiple solutions to protect private keys are polarising the investment community with an equal number available of strong advocates and fierce critics (even within the same However, we note that the storage solutions currently financial institution or research house). Moreover, valid available for digital assets eliminate this risk (the analysis, backed by in-depth research, is mixed up with programmer received his BTC back in 2011, according to ideological, poorly researched conclusions both for and The New York Times, when these solutions were not widely against the theme. We have decided to look at both sides available). Retail investors who decide to use self-custody of the same (Bit)coin to extract the investment thesis for their digital assets can choose from a range of dedicated behind this new asset class. Each part of this Edison online and software wallets which, on set-up, ask the user Explains series looks at one feature of BTC and the to create a so-called 'recovery seed' or 'recovery phrase'. broader cryptocurrency landscape (broadly referred to as This is basically a list of 12, 18 or 24 words (preferably kept ‘altcoins’). We conclude by summarising our subjective offline, eg written down and stored in multiple physical view on how positive or negative we believe the feature is locations) that contain all the information required to for BTC’s investment thesis. -

List of Bitcoin Companies
List of bitcoin companies This is a list of Wikipedia articles about for-profit companies with notable commercial activities related to bitcoin. Common services are cryptocurrency wallet providers, bitcoin exchanges, payment service providers[a] and venture capital. Other services include mining pools, cloud mining, peer-to-peer lending, exchange-traded funds, over-the-counter trading, gambling, micropayments, affiliates and prediction markets. Headquarters Company Founded Service Notes Refs Country City bitcoin exchange, wallet Binance 2017 Japan Tokyo [1] provider bitcoin exchange, wallet Bitcoin.com [data unknown/missing] Japan Tokyo provider bitcoin exchange, digital Hong currency exchange, Bitfinex 2012 Kong electronic trading platform United San multisignature security BitGo 2013 States Francisco platform for bitcoin ASIC-based bitcoin BitMain 2013 China Beijing miners cryptocurrency BitMEX 2014 derivatives trading Seychelles platform United payment service BitPay 2011 Atlanta States provider Bitstamp 2011 bitcoin exchange Luxembourg bitcoin debit card, Bitwala 2015 Berlin international transfers, [2] Germany bitcoin wallet Blockchain.com 2011 wallet provider Luxembourg United San Blockstream 2014 software States Francisco shut down by the United BTC-e 2011 Russia bitcoin exchange States government in July 2017 Canaan ASIC-based bitcoin 2013 China Beijing Creative miners United Circle 2013 Boston wallet provider States United San wallet provider, bitcoin Coinbase 2012 States Francisco exchange bitcoin/ether exchange, wallet provider, -

Asia's Crypto Landscape
A MESSARI REPORT Asia’s Crypto Landscape The key exchanges, funds, and market makers that define crypto in China, Japan, Korea, Hong Kong, Singapore, and Southeast Asia, with commentary on regulatory and investment trends. SPONSORED BY Author Mira Christanto RESEARCH ANALYST AT MESSARI Mira is a Research Analyst at Messari. Previously, she was a Senior Portfolio Manager at APG Asset Management, managing a US $7 billion fund focused on Real Estate equity investments across Asia Pacific. Prior to APG, Mira worked at $15 billion hedge fund TPG-Axon Capital Management, an affiliate of Texas Pacific Group, where she was a private and public market investor across multiple sectors and geographies. Before that, Mira was in Credit Suisse’s Investment Banking Division in the Leveraged Finance and Restructuring group in New York and worked on a variety of mergers & acquisitions, leveraged buyouts and restructuring deals. She received a BA in Economics and Mathematical Methods in the Social Sciences from Northwestern University. Never miss an update Real-time monitoring and alerts for all the assets you support Built for: • Funds • Exchanges • Custodians • Infrastructure Providers Learn More Asia’s Crypto Landscape 2 © 2021 Messari Table of Contents Introduction 5 SBI Group 67 SBI Virtual Currencies Trade 68 1.0 The Countries 8 TaoTao 69 GMO Coin 69 China 8 Bitpoint 69 Hong Kong 13 DMM Bitcoin 69 Japan 15 Rakuten Wallet 70 LVC (BITMAX) 70 South Korea 20 B Dash Ventures & B Cryptos 71 Singapore 23 Rest of Southeast Asia 25 South Korea 72 Philippines