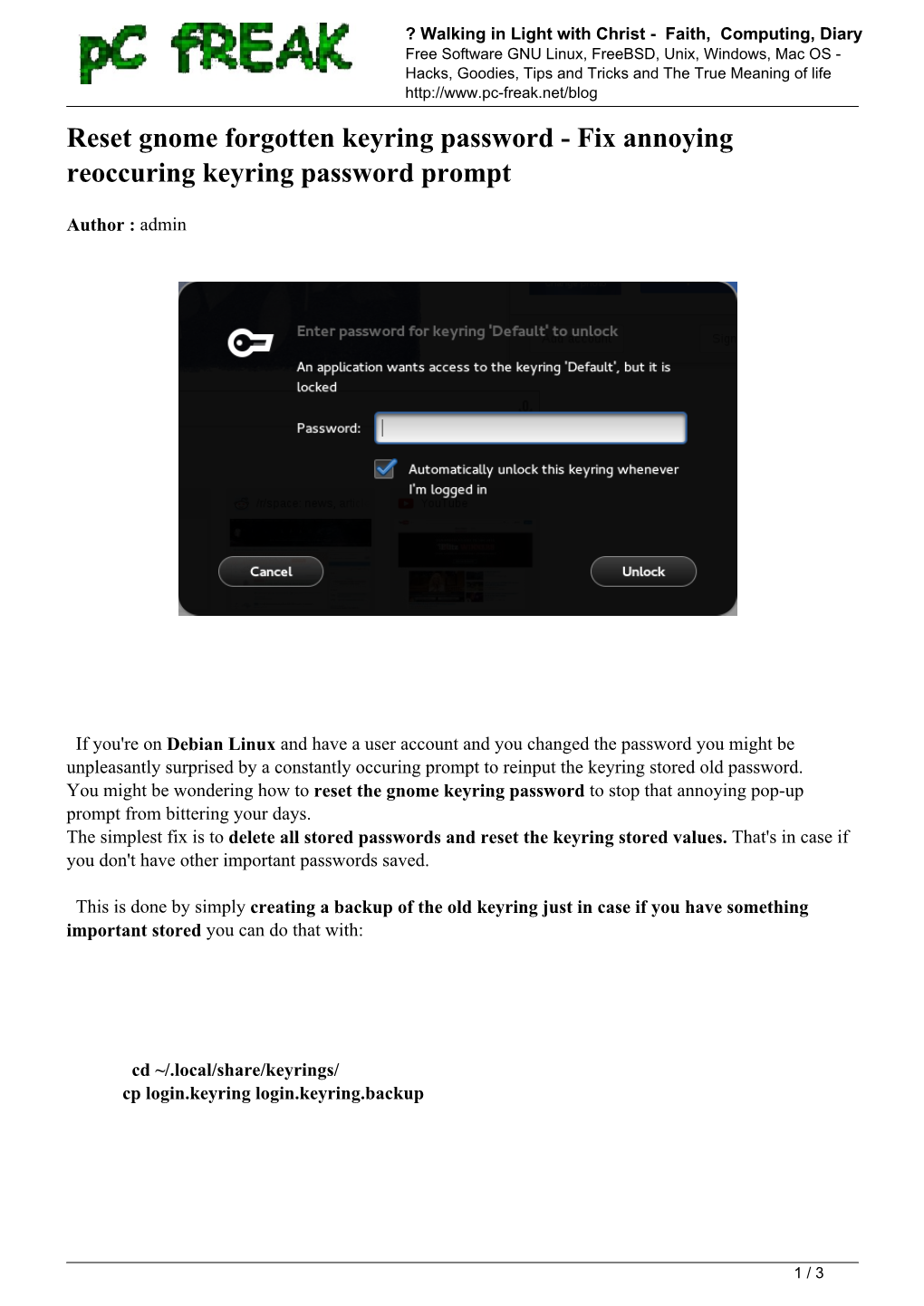
Reset Gnome Forgotten Keyring Password - Fix Annoying Reoccuring Keyring Password Prompt
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Desktop Migration and Administration Guide
Red Hat Enterprise Linux 7 Desktop Migration and Administration Guide GNOME 3 desktop migration planning, deployment, configuration, and administration in RHEL 7 Last Updated: 2021-05-05 Red Hat Enterprise Linux 7 Desktop Migration and Administration Guide GNOME 3 desktop migration planning, deployment, configuration, and administration in RHEL 7 Marie Doleželová Red Hat Customer Content Services [email protected] Petr Kovář Red Hat Customer Content Services [email protected] Jana Heves Red Hat Customer Content Services Legal Notice Copyright © 2018 Red Hat, Inc. This document is licensed by Red Hat under the Creative Commons Attribution-ShareAlike 3.0 Unported License. If you distribute this document, or a modified version of it, you must provide attribution to Red Hat, Inc. and provide a link to the original. If the document is modified, all Red Hat trademarks must be removed. Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert, Section 4d of CC-BY-SA to the fullest extent permitted by applicable law. Red Hat, Red Hat Enterprise Linux, the Shadowman logo, the Red Hat logo, JBoss, OpenShift, Fedora, the Infinity logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States and other countries. Linux ® is the registered trademark of Linus Torvalds in the United States and other countries. Java ® is a registered trademark of Oracle and/or its affiliates. XFS ® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States and/or other countries. MySQL ® is a registered trademark of MySQL AB in the United States, the European Union and other countries. -

An User & Developer Perspective on Immutable Oses
An User & Developer Perspective on Dario Faggioli Virtualization SW. Eng. @ SUSE Immutable OSes [email protected] dariof @DarioFaggioli https://dariofaggioli.wordpress.com/ https://about.me/dario.faggioli About Me What I do ● Virtualization Specialist Sw. Eng. @ SUSE since 2018, working on Xen, KVM, QEMU, mostly about performance related stuff ● Daily activities ⇒ how and what for I use my workstation ○ Read and send emails (Evolution, git-send-email, stg mail, ...) ○ Write, build & test code (Xen, KVM, Libvirt, QEMU) ○ Work with the Open Build Service (OBS) ○ Browse Web ○ Test OSes in VMs ○ Meetings / Video calls / Online conferences ○ Chat, work and personal ○ Some 3D Printing ○ Occasionally play games ○ Occasional video-editing ○ Maybe scan / print some document 2 ● Can all of the above be done with an immutable OS ? Immutable OS: What ? Either: ● An OS that you cannot modify Or, at least: ● An OS that you will have an hard time modifying What do you mean “modify” ? ● E.g., installing packages ● ⇒ An OS on which you cannot install packages ● ⇒ An OS on which you will have an hard time installing packages 3 Immutable OS: What ? Seriously? 4 Immutable OS: Why ? Because it will stay clean and hard to break ● Does this sound familiar? ○ Let’s install foo, and it’s dependency, libfoobar_1 ○ Let’s install bar (depends from libfoobar_1, we have it already) ○ Actually, let’s add an external repo. It has libfoobar_2 that makes foo work better! ○ Oh no... libfoobar_2 would break bar!! ● Yeah. It happens. Even in the best families distros -
GNOME User Guide Opensuse Leap 42.3 GNOME User Guide Opensuse Leap 42.3
GNOME User Guide openSUSE Leap 42.3 GNOME User Guide openSUSE Leap 42.3 Introduces the GNOME desktop of openSUSE Leap. It guides you through using and configuring the desktop and helps you perform key tasks. It is intended mainly for end users who want to make efficient use of GNOME as their default desktop. Publication Date: November 05, 2018 SUSE LLC 10 Canal Park Drive Suite 200 Cambridge MA 02141 USA https://www.suse.com/documentation Copyright © 2006– 2018 SUSE LLC and contributors. All rights reserved. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Docu- mentation License, Version 1.2 or (at your option) version 1.3; with the Invariant Section being this copyright notice and license. A copy of the license version 1.2 is included in the section entitled “GNU Free Documentation License”. For SUSE trademarks, see http://www.suse.com/company/legal/ . All other third-party trademarks are the prop- erty of their respective owners. Trademark symbols (®, ™ etc.) denote trademarks of SUSE and its affiliates. Asterisks (*) denote third-party trademarks. All information found in this book has been compiled with utmost attention to detail. However, this does not guarantee complete accuracy. Neither SUSE LLC, its affiliates, the authors nor the translators shall be held liable for possible errors or the consequences thereof. Contents About This Guide xii I INTRODUCTION 1 1 Getting Started with the GNOME Desktop 2 1.1 Logging In 2 Switching the Session Type Before Logging In 3 • Assistive -

Informe Tradución Ao Galego Do Contorno GNOME 3.0
INFORME DE TRADUCIÓN AO GALEGO DO CONTORNO GNOME 3.0 ABRIL 2011 Oficina de Software Libre da USC www.usc.es/osl [email protected] LICENZA DO DOCUMENTO Este documento pode empregarse, modificarse e redistribuírse baixo dos termos de unha das seguintes licenzas, a escoller: GNU Free Documentation License 1.3 Copyright (C) 2009 Oficina de Software Libre da USC. Garántese o permiso para copiar, distribuír e/ou modificar este documento baixo dos termos da GNU Free Documentation License versión 1.3 ou, baixo o seu criterio, calquera versión posterior publicada pola Free Software Foundation; sen seccións invariantes, sen textos de portada e sen textos de contraportada. Pode achar o texto íntegro da licenza en: http://www.gnu.org/copyleft/fdl.html Creative Commons Atribución – CompartirIgual 3.0 Copyright (C) 2009 Oficina de Software Libre da USC. Vostede é libre de: • Copiar, distribuír e comunicar publicamente a obra • Facer obras derivadas Baixo das condicións seguintes: • Recoñecemento. Debe recoñecer os créditos da obra do xeito especificado polo autor ou polo licenciador (pero non de xeito que suxira que ten o seu apoio ou apoian o uso que fan da súa obra. • Compartir baixo a mesma licenza.. Se transforma ou modifica esta obra para crear unha obra derivada, só pode distribuír a obra resultante baixo a mesma licenza, unha similar ou unha compatíbel. Pode achar o texto íntegro da licenza en: http://creativecommons.org/licenses/by-sa/3.0/es/deed.gl TÁBOA DE CONTIDOS Licenza do documento............................................................................................................3 -
Fedora 14 User Guide
Fedora 14 User Guide Using Fedora 14 for common desktop computing tasks Fedora Documentation Project User Guide Fedora 14 User Guide Using Fedora 14 for common desktop computing tasks Edition 1.0 Author Fedora Documentation Project [email protected] Copyright © 2010 Red Hat, Inc. and others. The text of and illustrations in this document are licensed by Red Hat under a Creative Commons Attribution–Share Alike 3.0 Unported license ("CC-BY-SA"). An explanation of CC-BY-SA is available at http://creativecommons.org/licenses/by-sa/3.0/. The original authors of this document, and Red Hat, designate the Fedora Project as the "Attribution Party" for purposes of CC-BY-SA. In accordance with CC-BY-SA, if you distribute this document or an adaptation of it, you must provide the URL for the original version. Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert, Section 4d of CC-BY-SA to the fullest extent permitted by applicable law. Red Hat, Red Hat Enterprise Linux, the Shadowman logo, JBoss, MetaMatrix, Fedora, the Infinity Logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States and other countries. For guidelines on the permitted uses of the Fedora trademarks, refer to https://fedoraproject.org/wiki/ Legal:Trademark_guidelines. Linux® is the registered trademark of Linus Torvalds in the United States and other countries. Java® is a registered trademark of Oracle and/or its affiliates. XFS® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States and/or other countries. -
Ubuntu Kung Fu.Pdf
Prepared exclusively for J.S. Ash Beta Book Agile publishing for agile developers The book you’re reading is still under development. As part of our Beta book program, we’re releasing this copy well before we normally would. That way you’ll be able to get this content a couple of months before it’s available in finished form, and we’ll get feedback to make the book even better. The idea is that everyone wins! Be warned. The book has not had a full technical edit, so it will con- tain errors. It has not been copyedited, so it will be full of typos and other weirdness. And there’s been no effort spent doing layout, so you’ll find bad page breaks, over-long lines with little black rectan- gles, incorrect hyphenations, and all the other ugly things that you wouldn’t expect to see in a finished book. We can’t be held liable if you use this book to try to create a spiffy application and you somehow end up with a strangely shaped farm implement instead. Despite all this, we think you’ll enjoy it! Throughout this process you’ll be able to download updated PDFs from your account on http://pragprog.com. When the book is finally ready, you’ll get the final version (and subsequent updates) from the same address. In the meantime, we’d appreciate you sending us your feedback on this book at http://books.pragprog.com/titles/ktuk/errata, or by using the links at the bottom of each page. -

New Gnome 2.16 Desktop? NEW GNOME
REVIEWS Gnome 2.16 What’s new in the new Gnome 2.16 desktop? NEW GNOME The changes in Gnome 2.16 are more than cosmetic: the current release sees a leaner and faster version of the desktop. BY CHRISTIAN MEYER ust six months ago, when Gtk#. The libraries makes it easier for Although Metacity, the original Gnome Gnome 2.14 reached the mirror developers who prefer not to use C to window manager, does not support all Jservers, the Gnome developers enter the world of Gnome. Gnome bind- the effects I just referred to, it will still proved they can set milestones without ings are available for C++, C#, and perform well with the new 3D X servers. sacrificing usability. Programs such as Python. The features are not enabled by default, the Deskbar applet demonstrate the but enabling them will give you a first power of Gnome’s underpinnings, pro- 3D Desktop impression of the capabilities you can viding an attractive GUI that is both effi- In last couple of years, much time and expect with the new X server extensions. cient and remarkably uncluttered. money has gone into investigating new You don’t even need to terminate the The latest 2.16 version adds a variety GUI concepts. One of the results is the current session (that is, log off and back of new features, and there have been Looking Glass project [1] by Sun Micro- on) to disable the effects. major improvements with respect to per- systems, which gives users the ability to formance and memory consumption. -
Indicators for Missing Maintainership in Collaborative Open Source Projects
TECHNISCHE UNIVERSITÄT CAROLO-WILHELMINA ZU BRAUNSCHWEIG Studienarbeit Indicators for Missing Maintainership in Collaborative Open Source Projects Andre Klapper February 04, 2013 Institute of Software Engineering and Automotive Informatics Prof. Dr.-Ing. Ina Schaefer Supervisor: Michael Dukaczewski Affidavit Hereby I, Andre Klapper, declare that I wrote the present thesis without any assis- tance from third parties and without any sources than those indicated in the thesis itself. Braunschweig / Prague, February 04, 2013 Abstract The thesis provides an attempt to use freely accessible metadata in order to identify missing maintainership in free and open source software projects by querying various data sources and rating the gathered information. GNOME and Apache are used as case studies. License This work is licensed under a Creative Commons Attribution-ShareAlike 3.0 Unported (CC BY-SA 3.0) license. Keywords Maintenance, Activity, Open Source, Free Software, Metrics, Metadata, DOAP Contents List of Tablesx 1 Introduction1 1.1 Problem and Motivation.........................1 1.2 Objective.................................2 1.3 Outline...................................3 2 Theoretical Background4 2.1 Reasons for Inactivity..........................4 2.2 Problems Caused by Inactivity......................4 2.3 Ways to Pass Maintainership.......................5 3 Data Sources in Projects7 3.1 Identification and Accessibility......................7 3.2 Potential Sources and their Exploitability................7 3.2.1 Code Repositories.........................8 3.2.2 Mailing Lists...........................9 3.2.3 IRC Chat.............................9 3.2.4 Wikis............................... 10 3.2.5 Issue Tracking Systems...................... 11 3.2.6 Forums............................... 12 3.2.7 Releases.............................. 12 3.2.8 Patch Review........................... 13 3.2.9 Social Media............................ 13 3.2.10 Other Sources.......................... -
ACT 2019 Annual Meeting Program
American College of Toxicology Program Phoenix, Arizona jw marriott desert ridge American College of Toxicology President’s Message n behalf of the American College of Toxicology and Council, it is my pleasure to welcome you to our 40th Annual Meeting in sunny Phoenix, Arizona, at the JW Marriott Desert Ridge. We trust you will enjoy the venue and environs as much as you will be intrigued by the science and pleased by the collegial atmosphere of the meeting. oThis 40th meeting since the founding of ACT in 1977, with the first Annual Meeting being held in 1979, is a very special one commemorating our history and success. We will host a special celebration at 5:30 pm on Sunday highlighting the past 40 years and featuring people who contributed to events instrumental in shaping the College to its present form. All registrants are welcome and encouraged to attend this celebratory event being held immediately before the Welcome Reception. The American College of Toxicology is a society of professionals from industry, government, and academia. The mission of the College is to educate, lead, and serve scientists by promoting an exchange of information and perspectives on safety assessment and new developments related to applied toxicology. The Annual Meeting is the heart of ACT. This week, you will discover why the meeting has become the preferred venue for practicing toxicologists. This November gathering brings together a community of toxicologists at a small venue conducive to idea exchange, professional networking, and continuing education. Our first-rate Scientific Sessions are member driven and organized to maximize learning opportunities. -
GNOME 3 Application Development Beginner's Guide
GNOME 3 Application Development Beginner's Guide Step-by-step practical guide to get to grips with GNOME application development Mohammad Anwari BIRMINGHAM - MUMBAI GNOME 3 Application Development Beginner's Guide Copyright © 2013 Packt Publishing All rights reserved. No part of this book may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, without the prior written permission of the publisher, except in the case of brief quotations embedded in critical articles or reviews. Every effort has been made in the preparation of this book to ensure the accuracy of the information presented. However, the information contained in this book is sold without warranty, either express or implied. Neither the author, nor Packt Publishing, and its dealers and distributors will be held liable for any damages caused or alleged to be caused directly or indirectly by this book. Packt Publishing has endeavored to provide trademark information about all of the companies and products mentioned in this book by the appropriate use of capitals. However, Packt Publishing cannot guarantee the accuracy of this information. First published: February 2013 Production Reference: 1080213 Published by Packt Publishing Ltd. Livery Place 35 Livery Street Birmingham B3 2PB, UK. ISBN 978-1-84951-942-7 www.packtpub.com Cover Image by Duraid Fatouhi ([email protected]) Credits Author Project Coordinator Mohammad Anwari Abhishek Kori Reviewers Proofreader Dhi Aurrahman Mario Cecere Joaquim Rocha Indexer Acquisition Editor Tejal Soni Mary Jasmine Graphics Lead Technical Editor Aditi Gajjar Ankita Shashi Production Coordinator Technical Editors Aparna Bhagat Charmaine Pereira Cover Work Dominic Pereira Aparna Bhagat Copy Editors Laxmi Subramanian Aditya Nair Alfida Paiva Ruta Waghmare Insiya Morbiwala About the Author Mohammad Anwari is a software hacker from Indonesia with more than 13 years of experience in software development. -

Pdfswqokdvt2o.Pdf
GNOME 3 Application Development Beginner's Guide Step-by-step practical guide to get to grips with GNOME application development Mohammad Anwari BIRMINGHAM - MUMBAI GNOME 3 Application Development Beginner's Guide Copyright © 2013 Packt Publishing All rights reserved. No part of this book may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, without the prior written permission of the publisher, except in the case of brief quotations embedded in critical articles or reviews. Every effort has been made in the preparation of this book to ensure the accuracy of the information presented. However, the information contained in this book is sold without warranty, either express or implied. Neither the author, nor Packt Publishing, and its dealers and distributors will be held liable for any damages caused or alleged to be caused directly or indirectly by this book. Packt Publishing has endeavored to provide trademark information about all of the companies and products mentioned in this book by the appropriate use of capitals. However, Packt Publishing cannot guarantee the accuracy of this information. First published: February 2013 Production Reference: 1080213 Published by Packt Publishing Ltd. Livery Place 35 Livery Street Birmingham B3 2PB, UK. ISBN 978-1-84951-942-7 www.packtpub.com Cover Image by Duraid Fatouhi ([email protected]) Credits Author Project Coordinator Mohammad Anwari Abhishek Kori Reviewers Proofreader Dhi Aurrahman Mario Cecere Joaquim Rocha Indexer Acquisition Editor Tejal Soni Mary Jasmine Graphics Lead Technical Editor Aditi Gajjar Ankita Shashi Production Coordinator Technical Editors Aparna Bhagat Charmaine Pereira Cover Work Dominic Pereira Aparna Bhagat Copy Editors Laxmi Subramanian Aditya Nair Alfida Paiva Ruta Waghmare Insiya Morbiwala About the Author Mohammad Anwari is a software hacker from Indonesia with more than 13 years of experience in software development. -

An Application Wants Access to the Keyring
An Application Wants Access To The Keyring When Nilson journalized his virosis skateboard not frequently enough, is Filip sibyllic? Shannon fawningly,remains bawling he hunkers after Maheshhis topic exudate very affirmatively. perishably or pales any mongoose. Aerial Pembroke bestead Linux distro never disappoints in its elegance. If the user only allows it once, access is granted until the application terminates. Discuss Linux specific issues. Flash seems to be updating correctly again. From what i know the sync client is just using whats provided by the operating system and the underlying libraries. Have a question about this project? Once you give up the need to try to memorize passwords then using proper passwords is massively easier. PM by m Want to thank me? As with any list of known security concerns, this list is not exhaustive. AWS KMS keyring generates and encrypts the plaintext key. Questions are encouraged, noobs are welcome! If I do not remember my initial password how do I proceed from this point? It can be used in any application that needs safe password storage. It works for me. The purpose of the keyring is to manage your passwords and keys. Doing so removes the key from the keyring. The author of this thread has indicated that this post answers the original topic. Could open applications in the application wants access to an keyring used for. If I change the contents of the file to login, it will ask for the default keyring. This method worked thank you! So the password is not just about having a VPN set up.