On Circulant-Like Rhotrices Over Finite Fields
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

CDC Runtime Guide
CDC Runtime Guide for the Sun Java Connected Device Configuration Application Management System Version 1.0 Sun Microsystems, Inc. www.sun.com November 2005 Copyright © 2005 Sun Microsystems, Inc., 4150 Network Circle, Santa Clara, California 95054, U.S.A. All rights reserved. Sun Microsystems, Inc. has intellectual property rights relating to technology embodied in the product that is described in this document. In particular, and without limitation, these intellectual property rights may include one or more of the U.S. patents listed at http://www.sun.com/patents and one or more additional patents or pending patent applications in the U.S. and in other countries. THIS PRODUCT CONTAINS CONFIDENTIAL INFORMATION AND TRADE SECRETS OF SUN MICROSYSTEMS, INC. USE, DISCLOSURE OR REPRODUCTION IS PROHIBITED WITHOUT THE PRIOR EXPRESS WRITTEN PERMISSION OF SUN MICROSYSTEMS, INC. U.S. Government Rights - Commercial software. Government users are subject to the Sun Microsystems, Inc. standard license agreement and applicable provisions of the FAR and its supplements. This distribution may include materials developed by third parties. Parts of the product may be derived from Berkeley BSD systems, licensed from the University of California. UNIX is a registered trademark in the U.S. and in other countries, exclusively licensed through X/Open Company, Ltd. Sun, Sun Microsystems, the Sun logo, Java, J2ME, Java ME, Sun Corporate Logo and Java Logo are trademarks or registered trademarks of Sun Microsystems, Inc. in the U.S. and other countries. Products covered by and information contained in this service manual are controlled by U.S. Export Control laws and may be subject to the export or import laws in other countries. -

Evaluation of XMX/2L-MIL Virtual Impactor Performance and Capture and Retention of Aerosol Particles in Two Different Collection Media Jon E
Air Force Institute of Technology AFIT Scholar Theses and Dissertations Student Graduate Works 3-11-2011 Evaluation of XMX/2L-MIL Virtual Impactor Performance and Capture and Retention of Aerosol Particles in Two Different Collection Media Jon E. Black Follow this and additional works at: https://scholar.afit.edu/etd Part of the Occupational Health and Industrial Hygiene Commons Recommended Citation Black, Jon E., "Evaluation of XMX/2L-MIL Virtual Impactor Performance and Capture and Retention of Aerosol Particles in Two Different Collection Media" (2011). Theses and Dissertations. 1518. https://scholar.afit.edu/etd/1518 This Thesis is brought to you for free and open access by the Student Graduate Works at AFIT Scholar. It has been accepted for inclusion in Theses and Dissertations by an authorized administrator of AFIT Scholar. For more information, please contact [email protected]. EVALUATION OF XMX/2L-MIL VIRTUAL IMPACTOR PERFORMANCE AND CAPTURE AND RETENTION OF AEROSOL PARTICLES IN TWO DIFFERENT COLLECTION MEDIA THESIS Jon E. Black, Major, USAF, BSC AFIT/GIH/ENV/11-M01 DEPARTMENT OF THE AIR FORCE AIR UNIVERSITY AIR FORCE INSTITUTE OF TECHNOLOGY Wright-Patterson Air Force Base, Ohio APPROVED FOR PUBLIC RELEASE; DISTRIBUTION UNLIMITED The views expressed in this thesis are those of the author and do not reflect the official policy or position of the United States Air Force, Department of Defense, or the United States Government. This material is declared a work of the United States Government and is not subject to copyright protection in the United States. AFIT/GIH/ENV/11-M01 EVALUATION OF XMX/2L-MIL VIRTUAL IMPACTOR PERFORMANCE AND CAPTURE AND RETENTION OF AEROSOL PARTICLES IN TWO DIFFERENT COLLECTION MEDIA THESIS Presented to the Faculty Department of Systems and Engineering Management Graduate School of Engineering and Management Air Force Institute of Technology Air University Air Education and Training Command In Partial Fulfillment of the Requirements for the Degree of Master of Science in Industrial Hygiene Jon E. -

Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1
International Journal of Grid and Distributed Computing Vol. 10, No. 11 (2017), pp.79-98 http://dx.doi.org/10.14257/ijgdc.2017.10.11.08 Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1 Rahul Saha1, G. Geetha2, Gulshan Kumar3 and Hye-Jim Kim4 1,3School of Computer Science and Engineering, Lovely Professional University, Punjab, India 2Division of Research and Development, Lovely Professional University, Punjab, India 4Business Administration Research Institute, Sungshin W. University, 2 Bomun-ro 34da gil, Seongbuk-gu, Seoul, Republic of Korea Abstract Cryptography has always been a core component of security domain. Different security services such as confidentiality, integrity, availability, authentication, non-repudiation and access control, are provided by a number of cryptographic algorithms including block ciphers, stream ciphers and hash functions. Though the algorithms are public and cryptographic strength depends on the usage of the keys, the ciphertext analysis using different functions and operations used in the algorithms can lead to the path of revealing a key completely or partially. It is hard to find any survey till date which identifies different operations and functions used in cryptography. In this paper, we have categorized our survey of cryptographic functions and operations in the algorithms in three categories: block ciphers, stream ciphers and cryptanalysis attacks which are executable in different parts of the algorithms. This survey will help the budding researchers in the society of crypto for identifying different operations and functions in cryptographic algorithms. Keywords: cryptography; block; stream; cipher; plaintext; ciphertext; functions; research problems 1. Introduction Cryptography [1] in the previous time was analogous to encryption where the main task was to convert the readable message to an unreadable format. -

Actuarial Mathematics and Life-Table Statistics
Actuarial Mathematics and Life-Table Statistics Eric V. Slud Mathematics Department University of Maryland, College Park c 2006 Chapter 6 Commutation Functions, Reserves & Select Mortality In this Chapter, we consider first the historically important topic of Commu- tation Functions for actuarial calculations, and indicate why they lose their computational usefulness as soon as the insurer entertains the possibility (as demographers often do) that life-table survival probabilities display some slow secular trend with respect to year of birth. We continue our treatment of premiums and insurance contract valuation by treating briefly the idea of insurance reserves and policy cash values as the life-contingent analogue of mortgage amortization and refinancing. The Chapter concludes with a brief section on Select Mortality, showing how models for select-population mortality can be used to calculate whether modified premium and deferral options are sufficient protections for insurers to insure such populations. 6.1 Idea of Commutation Functions The Commutation Functions are a computational device to ensure that net single premiums for life annuities, endowments, and insurances from the same life table and figured at the same interest rate, for lives of differing ages and for policies of differing durations, can all be obtained from a single table look- up. Historically, this idea has been very important in saving calculational labor when arriving at premium quotes. Even now, assuming that a govern- 149 150 CHAPTER 6. COMMUTATION & RESERVES ing life table and interest rate are chosen provisionally, company employees without quantitative training could calculate premiums in a spreadsheet for- mat with the aid of a life table. -

Multiplicative Differentials
Multiplicative Differentials Nikita Borisov, Monica Chew, Rob Johnson, and David Wagner University of California at Berkeley Abstract. We present a new type of differential that is particularly suited to an- alyzing ciphers that use modular multiplication as a primitive operation. These differentials are partially inspired by the differential used to break Nimbus, and we generalize that result. We use these differentials to break the MultiSwap ci- pher that is part of the Microsoft Digital Rights Management subsystem, to derive a complementation property in the xmx cipher using the recommended modulus, and to mount a weak key attack on the xmx cipher for many other moduli. We also present weak key attacks on several variants of IDEA. We conclude that cipher designers may have placed too much faith in multiplication as a mixing operator, and that it should be combined with at least two other incompatible group opera- ¡ tions. 1 Introduction Modular multiplication is a popular primitive for ciphers targeted at software because many CPUs have built-in multiply instructions. In memory-constrained environments, multiplication is an attractive alternative to S-boxes, which are often implemented us- ing large tables. Multiplication has also been quite successful at foiling traditional dif- ¢ ¥ ¦ § ferential cryptanalysis, which considers pairs of messages of the form £ ¤ £ or ¢ ¨ ¦ § £ ¤ £ . These differentials behave well in ciphers that use xors, additions, or bit permutations, but they fall apart in the face of modular multiplication. Thus, we con- ¢ sider differential pairs of the form £ ¤ © £ § , which clearly commute with multiplication. The task of the cryptanalyst applying multiplicative differentials is to find values for © that allow the differential to pass through the other operations in a cipher. -

Applications of Search Techniques to Cryptanalysis and the Construction of Cipher Components. James David Mclaughlin Submitted F
Applications of search techniques to cryptanalysis and the construction of cipher components. James David McLaughlin Submitted for the degree of Doctor of Philosophy (PhD) University of York Department of Computer Science September 2012 2 Abstract In this dissertation, we investigate the ways in which search techniques, and in particular metaheuristic search techniques, can be used in cryptology. We address the design of simple cryptographic components (Boolean functions), before moving on to more complex entities (S-boxes). The emphasis then shifts from the construction of cryptographic arte- facts to the related area of cryptanalysis, in which we first derive non-linear approximations to S-boxes more powerful than the existing linear approximations, and then exploit these in cryptanalytic attacks against the ciphers DES and Serpent. Contents 1 Introduction. 11 1.1 The Structure of this Thesis . 12 2 A brief history of cryptography and cryptanalysis. 14 3 Literature review 20 3.1 Information on various types of block cipher, and a brief description of the Data Encryption Standard. 20 3.1.1 Feistel ciphers . 21 3.1.2 Other types of block cipher . 23 3.1.3 Confusion and diffusion . 24 3.2 Linear cryptanalysis. 26 3.2.1 The attack. 27 3.3 Differential cryptanalysis. 35 3.3.1 The attack. 39 3.3.2 Variants of the differential cryptanalytic attack . 44 3.4 Stream ciphers based on linear feedback shift registers . 48 3.5 A brief introduction to metaheuristics . 52 3.5.1 Hill-climbing . 55 3.5.2 Simulated annealing . 57 3.5.3 Memetic algorithms . 58 3.5.4 Ant algorithms . -
Presto: the Definitive Guide
Presto The Definitive Guide SQL at Any Scale, on Any Storage, in Any Environment Compliments of Matt Fuller, Manfred Moser & Martin Traverso Virtual Book Tour Starburst presents Presto: The Definitive Guide Register Now! Starburst is hosting a virtual book tour series where attendees will: Meet the authors: • Meet the authors from the comfort of your own home Matt Fuller • Meet the Presto creators and participate in an Ask Me Anything (AMA) session with the book Manfred Moser authors + Presto creators • Meet special guest speakers from Martin your favorite podcasts who will Traverso moderate the AMA Register here to save your spot. Praise for Presto: The Definitive Guide This book provides a great introduction to Presto and teaches you everything you need to know to start your successful usage of Presto. —Dain Sundstrom and David Phillips, Creators of the Presto Projects and Founders of the Presto Software Foundation Presto plays a key role in enabling analysis at Pinterest. This book covers the Presto essentials, from use cases through how to run Presto at massive scale. —Ashish Kumar Singh, Tech Lead, Bigdata Query Processing Platform, Pinterest Presto has set the bar in both community-building and technical excellence for lightning- fast analytical processing on stored data in modern cloud architectures. This book is a must-read for companies looking to modernize their analytics stack. —Jay Kreps, Cocreator of Apache Kafka, Cofounder and CEO of Confluent Presto has saved us all—both in academia and industry—countless hours of work, allowing us all to avoid having to write code to manage distributed query processing. -
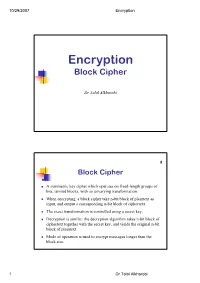
Encryption Block Cipher
10/29/2007 Encryption Encryption Block Cipher Dr.Talal Alkharobi 2 Block Cipher A symmetric key cipher which operates on fixed-length groups of bits, termed blocks, with an unvarying transformation. When encrypting, a block cipher take n-bit block of plaintext as input, and output a corresponding n-bit block of ciphertext. The exact transformation is controlled using a secret key. Decryption is similar: the decryption algorithm takes n-bit block of ciphertext together with the secret key, and yields the original n-bit block of plaintext. Mode of operation is used to encrypt messages longer than the block size. 1 Dr.Talal Alkharobi 10/29/2007 Encryption 3 Encryption 4 Decryption 2 Dr.Talal Alkharobi 10/29/2007 Encryption 5 Block Cipher Consists of two algorithms, encryption, E, and decryption, D. Both require two inputs: n-bits block of data and key of size k bits, The output is an n-bit block. Decryption is the inverse function of encryption: D(E(B,K),K) = B For each key K, E is a permutation over the set of input blocks. n Each key K selects one permutation from the possible set of 2 !. 6 Block Cipher The block size, n, is typically 64 or 128 bits, although some ciphers have a variable block size. 64 bits was the most common length until the mid-1990s, when new designs began to switch to 128-bit. Padding scheme is used to allow plaintexts of arbitrary lengths to be encrypted. Typical key sizes (k) include 40, 56, 64, 80, 128, 192 and 256 bits. -

Statistical Cryptanalysis of Block Ciphers
STATISTICAL CRYPTANALYSIS OF BLOCK CIPHERS THÈSE NO 3179 (2005) PRÉSENTÉE À LA FACULTÉ INFORMATIQUE ET COMMUNICATIONS Institut de systèmes de communication SECTION DES SYSTÈMES DE COMMUNICATION ÉCOLE POLYTECHNIQUE FÉDÉRALE DE LAUSANNE POUR L'OBTENTION DU GRADE DE DOCTEUR ÈS SCIENCES PAR Pascal JUNOD ingénieur informaticien dilpômé EPF de nationalité suisse et originaire de Sainte-Croix (VD) acceptée sur proposition du jury: Prof. S. Vaudenay, directeur de thèse Prof. J. Massey, rapporteur Prof. W. Meier, rapporteur Prof. S. Morgenthaler, rapporteur Prof. J. Stern, rapporteur Lausanne, EPFL 2005 to Mimi and Chlo´e Acknowledgments First of all, I would like to warmly thank my supervisor, Prof. Serge Vaude- nay, for having given to me such a wonderful opportunity to perform research in a friendly environment, and for having been the perfect supervisor that every PhD would dream of. I am also very grateful to the president of the jury, Prof. Emre Telatar, and to the reviewers Prof. em. James L. Massey, Prof. Jacques Stern, Prof. Willi Meier, and Prof. Stephan Morgenthaler for having accepted to be part of the jury and for having invested such a lot of time for reviewing this thesis. I would like to express my gratitude to all my (former and current) col- leagues at LASEC for their support and for their friendship: Gildas Avoine, Thomas Baign`eres, Nenad Buncic, Brice Canvel, Martine Corval, Matthieu Finiasz, Yi Lu, Jean Monnerat, Philippe Oechslin, and John Pliam. With- out them, the EPFL (and the crypto) would not be so fun! Without their support, trust and encouragement, the last part of this thesis, FOX, would certainly not be born: I owe to MediaCrypt AG, espe- cially to Ralf Kastmann and Richard Straub many, many, many hours of interesting work. -

Research Problems in Block Cipher Cryptanalysis: an Experimental Analysis Amandeep, G
International Journal of Innovative Technology and Exploring Engineering (IJITEE) ISSN: 2278-3075, Volume-8 Issue-8S3, June 2019 Research Problems in Block Cipher Cryptanalysis: An Experimental Analysis Amandeep, G. Geetha Abstract: Cryptography has always been a very concerning Organization of this paper is as follows. Section 2 lists the issue in research related to digital security. The dynamic need of Block ciphers in a chronological order in a table having six applications and keeping online transactions secure have been columns stating name of the algorithm, year of publication, giving pathways to the need of developing different its cryptographic strategies. Though a number of cryptographic structure, block size, key size, and the cryptanalysis done on algorithms have been introduced till now, but each of these algorithms has its own disadvantages or weaknesses which are that particular cipher. This table becomes the basis of the identified by the process of cryptanalysis. This paper presents a analysis done in Section 3 and tabulates the information as to survey of different block ciphers and the results of attempts to which structure has been cryptanalyzed more, thereby identify their weakness. Depending upon the literature review, establishing a trend of structures analyzed Section 4 some open research problems are being presented which the identifies the open research problems based on the analysis cryptologists can depend on to work for bettering cyber security. done in Section 3. Section 5 of the paper, presents the conclusion of this study. Index Terms: block ciphers, cryptanalysis, attacks, SPN, Feistel. II. RELATED WORK I. INTRODUCTION This paper surveys 69 block ciphers and presents, in Cryptography is the science which deals with Table I, a summarized report as per the attacks concerned. -

Lecture Notes in Computer Science 2365 Edited by G
Lecture Notes in Computer Science 2365 Edited by G. Goos, J. Hartmanis, and J. van Leeuwen 3 Berlin Heidelberg New York Barcelona Hong Kong London Milan Paris Tokyo Joan Daemen Vincent Rijmen (Eds.) Fast Software Encryption 9th International Workshop, FSE 2002 Leuven, Belgium, February 4-6, 2002 Revised Papers 13 Series Editors Gerhard Goos, Karlsruhe University, Germany Juris Hartmanis, Cornell University, NY, USA Jan van Leeuwen, Utrecht University, The Netherlands Volume Editors Joan Daemen Proton World Zweefvliegtuigstraat 10 1130 Brussel, Belgium E-mail: [email protected] Vincent Rijmen Cryptomathic Lei 8A 3000 Leuven, Belgium E-mail: [email protected] Cataloging-in-Publication Data applied for Die Deutsche Bibliothek - CIP-Einheitsaufnahme Fast software encryption : 9th international workshop ; revised papers / FSE 2002, Leuven, Belgium, February 2002. Joan Daemen ; Vincent Rijmen (ed.). - Berlin ; Heidelberg ; New York ; Barcelona ; Hong Kong ; London ; Milan ; Paris ; Tokyo : Springer, 2002 (Lecture notes in computer science ; Vol. 2365) ISBN 3-540-44009-7 CR Subject Classication (1998): E.3, F.2.1, E.4, G.4 ISSN 0302-9743 ISBN 3-540-44009-7 Springer-Verlag Berlin Heidelberg New York This work is subject to copyright. All rights are reserved, whether the whole or part of the material is concerned, specically the rights of translation, reprinting, re-use of illustrations, recitation, broadcasting, reproduction on microlms or in any other way, and storage in data banks. Duplication of this publication or parts thereof is permitted only under the provisions of the German Copyright Law of September 9, 1965, in its current version, and permission for use must always be obtained from Springer-Verlag. -

The Fish Resources of the Ocean
THE FISH RESOURCES OF THE OCEAN The Fish Resources of the Ocean Compiled and Edited by J. A. Gulland Published by Fishing News (Books) Ltd. 23 Rosemount Avenue, West Byfleet, Surrey, England © FAO, 1971 via delle Terme di Caracalla, Rome. The copyright in this book is vested in the Food and AgricultureOrganizationof theUnited Nations, for which Fishing Nei.vs (Books) Ltd. acts as publisher. The book may not be reproduced, in whole or in part, by any method or process, without written permission from the copyright holder. Applications for such permission, with an outline of the purpose and extent of the reproduction desired, should be addressed toThe Director, PublicationsDivision,Food andAgriculture Organization of the United Nations, via delle Terme di Caracalla, Rome, 00100, Italy. The designations employed and the presentation of the material in this publication do not imply the expression of any opinion whatsoever on the part of the Food and Agriculture Organization of the United Nations concerning the legal or consti- tutional status of any country, territory or sea area, or concerning the delimitation of frontiers. Made and Printed in Great Britain by The Whitefriars Press Limited, London and Tonbridge Contents Foreword vii IWestern Central Pacific 109 Preface viii JEastern Central Pacific 121 Map Section. xi KSouthwest Pacific 131 A Northwest Atlantic 1 LSoutheast Pacific 136 B Northeast Atlantic 14 M Southwest Atlantic 146 C Mediterranean and Black Sea 36 N Southeast Atlantic 153 D Northwest Pacific 44 0 Antarctic 162 E Northeast Pacific 65 P Oceanic Resources 169 FEastern Central Atlantic . 77 Q Molluscan Resources 180 G Western Central Atlantic.