Suse Linux / User Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Herramientas En GNU/Linux Para Estudiantes Universitarios
Herramientas en GNU/Linux para estudiantes universitarios El Escritorio KDE David Vaquero Santiago Herramientas en GNU/Linux para estudiantes universitarios: El Escritorio KDE por David Vaquero Santiago Copyright (c) 2.003 David Vaquero Santiago Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with no Invariant Sections, no Front-Cover Texts, and no Back-Cover Texts. A copy of the license is included in the section entitled "GNU Free Documentation License". Tabla de contenidos 1. El Escritorio KDE..............................................................................................................................................1 1.1. La Historia de KDE.................................................................................................................................1 1.2. .................................................................................................................................................................1 2. ..............................................................................................................................................................................3 2.1. El escritorio KDE....................................................................................................................................3 3. Konqueror: La herramienta polivalente..........................................................................................................8 -
Comodo System Cleaner Version 3.0
Comodo System Cleaner Version 3.0 User Guide Version 3.0.122010 Versi Comodo Security Solutions 525 Washington Blvd. Jersey City, NJ 07310 Comodo System Cleaner - User Guide Table of Contents 1.Comodo System-Cleaner - Introduction ............................................................................................................ 3 1.1.System Requirements...........................................................................................................................................5 1.2.Installing Comodo System-Cleaner........................................................................................................................5 1.3.Starting Comodo System-Cleaner..........................................................................................................................9 1.4.The Main Interface...............................................................................................................................................9 1.5.The Summary Area.............................................................................................................................................11 1.6.Understanding Profiles.......................................................................................................................................12 2.Registry Cleaner............................................................................................................................................. 15 2.1.Clean.................................................................................................................................................................16 -

110% Gaming 220 Triathlon Magazine 3D World Adviser
110% Gaming 220 Triathlon Magazine 3D World Adviser Evolution Air Gunner Airgun World Android Advisor Angling Times (UK) Argyllshire Advertiser Asian Art Newspaper Auto Car (UK) Auto Express Aviation Classics BBC Good Food BBC History Magazine BBC Wildlife Magazine BIKE (UK) Belfast Telegraph Berkshire Life Bikes Etc Bird Watching (UK) Blackpool Gazette Bloomberg Businessweek (Europe) Buckinghamshire Life Business Traveller CAR (UK) Campbeltown Courier Canal Boat Car Mechanics (UK) Cardmaking and Papercraft Cheshire Life China Daily European Weekly Classic Bike (UK) Classic Car Weekly (UK) Classic Cars (UK) Classic Dirtbike Classic Ford Classic Motorcycle Mechanics Classic Racer Classic Trial Classics Monthly Closer (UK) Comic Heroes Commando Commando Commando Commando Computer Active (UK) Computer Arts Computer Arts Collection Computer Music Computer Shopper Cornwall Life Corporate Adviser Cotswold Life Country Smallholding Country Walking Magazine (UK) Countryfile Magazine Craftseller Crime Scene Cross Stitch Card Shop Cross Stitch Collection Cross Stitch Crazy Cross Stitch Gold Cross Stitcher Custom PC Cycling Plus Cyclist Daily Express Daily Mail Daily Star Daily Star Sunday Dennis the Menace & Gnasher's Epic Magazine Derbyshire Life Devon Life Digital Camera World Digital Photo (UK) Digital SLR Photography Diva (UK) Doctor Who Adventures Dorset EADT Suffolk EDGE EDP Norfolk Easy Cook Edinburgh Evening News Education in Brazil Empire (UK) Employee -

Pressreader Magazine Titles
PRESSREADER: UK MAGAZINE TITLES www.edinburgh.gov.uk/pressreader Computers & Technology Sport & Fitness Arts & Crafts Motoring Android Advisor 220 Triathlon Magazine Amateur Photographer Autocar 110% Gaming Athletics Weekly Cardmaking & Papercraft Auto Express 3D World Bike Cross Stitch Crazy Autosport Computer Active Bikes etc Cross Stitch Gold BBC Top Gear Magazine Computer Arts Bow International Cross Stitcher Car Computer Music Boxing News Digital Camera World Car Mechanics Computer Shopper Carve Digital SLR Photography Classic & Sports Car Custom PC Classic Dirt Bike Digital Photographer Classic Bike Edge Classic Trial Love Knitting for Baby Classic Car weekly iCreate Cycling Plus Love Patchwork & Quilting Classic Cars Imagine FX Cycling Weekly Mollie Makes Classic Ford iPad & Phone User Cyclist N-Photo Classics Monthly Linux Format Four Four Two Papercraft Inspirations Classic Trial Mac Format Golf Monthly Photo Plus Classic Motorcycle Mechanics Mac Life Golf World Practical Photography Classic Racer Macworld Health & Fitness Simply Crochet Evo Maximum PC Horse & Hound Simply Knitting F1 Racing Net Magazine Late Tackle Football Magazine Simply Sewing Fast Bikes PC Advisor Match of the Day The Knitter Fast Car PC Gamer Men’s Health The Simple Things Fast Ford PC Pro Motorcycle Sport & Leisure Today’s Quilter Japanese Performance PlayStation Official Magazine Motor Sport News Wallpaper Land Rover Monthly Retro Gamer Mountain Biking UK World of Cross Stitching MCN Stuff ProCycling Mini Magazine T3 Rugby World More Bikes Tech Advisor -

Techniques for Authoring Complex XML Documents Vincent Quint, Irène Vatton
Techniques for Authoring Complex XML Documents Vincent Quint, Irène Vatton To cite this version: Vincent Quint, Irène Vatton. Techniques for Authoring Complex XML Documents. Proceedings of the 2004 ACM symposium on Document Engineering, DocEng 2004, Oct 2004, MilWaukee, WI, United States. pp.115-123, 10.1145/1030397.1030422. inria-00423365 HAL Id: inria-00423365 https://hal.inria.fr/inria-00423365 Submitted on 9 Oct 2009 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. Techniques for Authoring Complex XML Documents Vincent Quint Irene` Vatton INRIA Rhone-Alpesˆ INRIA Rhone-Alpesˆ 655 avenue de l’Europe 655 avenue de l’Europe 38334 Saint Ismier Cedex, France 38334 Saint Ismier Cedex, France [email protected] [email protected] ABSTRACT 1. INTRODUCTION This paper reviews the main innovations of XML and con- Authoring techniques for structured documents consti- siders their impact on the editing techniques for structured tuted an active research area during the second half of the documents. Namespaces open the way to compound docu- 80’s and the early 90’s [10]. Several experimental systems ments; well-formedness brings more freedom in the editing such as Grif [7] and Rita [6] were developed and a few pro- task; CSS allows style to be associated easily with structured duction tools resulted from that work. -
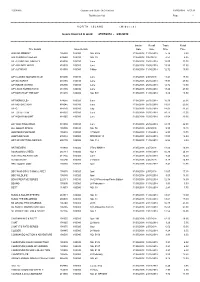
Distribution List Page - 1
R56891A Gordon and Gotch (NZ) Limited 29/05/2018 8:57:12 Distribution List Page - 1 =========================================================================================================================================================== N O R T H I S L A N D ( M i d w e e k ) Issues invoiced in week 27/05/2018 - 2/06/2018 =========================================================================================================================================================== Invoice Recall Trade Retail Title Details Issue Details Date Date Price Price 2000 AD WEEKLY 105030 100080 NO. 2075 31/05/2018 11/06/2018 5.74 8.80 500 SUDOKU PUZZLES 239580 100010 NO. 39 31/05/2018 9/07/2018 4.53 6.95 A/F AEROPLANE MNTHLY 818005 100010 June 31/05/2018 25/06/2018 15.00 23.00 A/F AIRLINER WRLD 818020 100020 June 31/05/2018 25/06/2018 15.59 23.90 A/F AUTOCAR 818030 100080 9 May 31/05/2018 11/06/2018 12.72 19.50 A/F CLASSIC MOTORCYCLE 915600 100010 June 31/05/2018 2/07/2018 11.41 17.50 A/F GUITARIST 818155 100010 June 31/05/2018 25/06/2018 17.93 27.50 A/F INSIDE UNITED 896390 100010 June 31/05/2018 25/06/2018 12.72 19.50 A/F LINUX FORMAT DVD 818185 100010 June 31/05/2018 25/06/2018 18.20 27.90 A/F MATCH OF THE DAY 818215 100080 NO. 504 31/05/2018 11/06/2018 8.80 13.50 A/F MONOCLE> 874655 100020 June 31/05/2018 25/06/2018 16.30 25.00 A/F MOTORSPORT 818245 100010 June 31/05/2018 25/06/2018 13.63 20.90 A/F Q 818270 100010 July 31/05/2018 25/06/2018 14.02 21.50 A/F TOTAL FILM 818335 100010 June 31/05/2018 25/06/2018 10.11 15.50 A/F WOMAN&HOME 818365 100010 June 31/05/2018 25/06/2018 13.04 20.00 A/F YACHTING WRLD 818380 100010 June 31/05/2018 25/06/2018 14.35 22.00 ALL ABOUT SPACE 105505 100010 NO. -
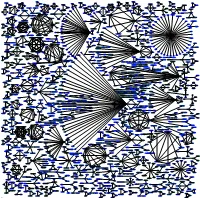
Apg Zope-Plone3 Zope-Externaleditor 0. Poppler-Utils 0. Apache2.2
deluge-core libmagickcore2 libecpg6 libcvaux-dev libcairo-perl 0.655021834061 0. 0. libisc50 libfindlib-ocaml-dev 0. libparrot1.4.0 libjaxp1.3-java-gcj 0. 0. libgssrpc4 peercast 0. gcj-4.4-jre 0. libxfconf-0-2 0. 0. 0. libbind9-50 deluge-common 0. 0. liblqr-1-0 libecpg-compat3 0. libcv-dev libavahi-common-data libgtk2-perl 0. 1.03092783505 1.5873015873 0. 0. libasm0 2.94117647059 2.40963855422 libacl1 coreutils 0.0842023447114 0. 0.655021834061 0. 0. libplasma-ruby1.8 0. 0. 0. 0. 2.38095238095 libxalan2-java-gcj 0. 0. 0. 0. libfindlib-ocaml 0. librevm0 python-poker-engine 0. peercast-geekast 1.03092783505 0. libxfcegui4-4 0.1941370607650.278515447892 0. libisccc50 0. 0.0971754340503 libparrot-dev parrot 0.0226346763241 0. 0. geoip-database 0. libhighgui-dev 0. libmagickwand2 libpango-perl libpgtypes3 0. gcj-4.4-jdk libgcj10-awt 2.94117647059 libkdb5-4 libkadm5srv6 0. 0. 0. 0. 0.01295672454 libasn1-8-heimdal 0.340676811265 kamera python 1.61290322581 libpoconet8-dbg python-alsaaudio 0. 0. libedfmt0 0. 0. step 1.3314094576 0. 0. libxerces2-java-gcj 0. 0. xfconf ocaml-findlib 3.79746835443 dpkg libattr1 0. peercast-servent 3.75283079909 0. libplasma-ruby gnustep-base-runtime 0.2915263021511.24614678297 libdns50 0. 0. 3.79746835443 apg python-poker-network 0. libdigest-bubblebabble-perl 0. libloader-java-openoffice.org libhx509-4-heimdal libavahi-client3 libavahi-common3 0. libdb4.5 0. libcrypt-openssl-dsa-perl libpococrypto8-dbg 0.3179650238473.05646290247 0. 0. 0. 0. 1.23302944842 2.63157894737 0. kcolorchooser libisccfg50 0. libetrace0 libgcj10-dev 0. marble libkrb5-dev 1.52816947596 parrot-minimal 0. -

Oracle Solaris 10 910 Release Notes
Oracle® Solaris 10 9/10 Release Notes Part No: 821–1839–11 September 2010 Copyright © 2010, Oracle and/or its affiliates. All rights reserved. This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. If this is software or related software documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, the following notice is applicable: U.S. GOVERNMENT RIGHTS Programs, software, databases, and related documentation and technical data delivered to U.S. Government customers are “commercial computer software” or “commercial technical data” pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, the use, duplication, disclosure, modification, and adaptation shall be subject to the restrictions and license terms setforth in the applicable Government contract, and, to the extent applicable by the terms of the Government contract, the additional rights set forth in FAR 52.227-19, Commercial Computer Software License (December 2007). Oracle America, Inc., 500 Oracle Parkway, Redwood City, CA 94065. -
Linux for Biologists
Linux for Beginners – Part 2 3CPG Workshop Robert Bukowski Computational Biology Service Unit http://cbsu.tc.cornell.edu/lab/doc/Linux_workshop_Part2_Nov_2011.pdf Topics CBSU/3CPG Lab Part 1: (March Nov. 7, 2011) cbsuwrkst2,3,4 (Linux) Reserving time on 3CPG Lab workstations 3 “interactive” Logging in to a Linux workstation machines with nice consoles (also Terminal window and tricks accessible remotely) Linux directory structure cbsum1c1b00n (Linux) Working with files cbsum1c2b00n (Linux) Working with text files 31 “remote” machines Part 2: (today) cbsulm01,cbsulm02 (Linux, 64 and 500 GB Transferring files to/from workstations RAM) Running applications Note: this will only cover the Linux aspect of running applications; the functionality and the biological aspect will be covered in workshop Using BioHPC Lab Software on Nov. 28, 2011. Basics of scripting (shell and Perl) Note: this will not teach you scripting – just get you started. We are planning a series of workshops on Perl in the fall – stay tuned. In the meantime - use multiple resources online (google “Perl tutorial”, for example). Disk usage guidelines: Local vs. network directories (3CPG LAB – specific) cbsuwrkst2 Network directories / /home, /programs, /shared_data ……… |-- home/bukowski (with all subdirectories) |-- programs/ |-- shared_data/ • Physically located on the file `-- workdir/bukowski server • Visible from all workstations Cbsuwrkstfsrv1 cbsuwrkst3 (file server) • Relatively SLOW access – DO NOT / / run any calculations there, avoid ……… ……… |-- home/bukowski -
How to Make a Simple Web Page Using HTML
How to make a simple web page using HTML Introduction to HTML HTML For this class, you will have to create a web page using HTML Joke: (from http://www.w3schools.com/html/html_layout.asp): Student: How do you spell HTML? HTML stands for Hyper Text Markup Language Used to create web pages Made up of Tags - commands enclosed in < and >, example <HTML> Opening tag: <HTML> Closing tag: </HTML> HTML page “skeleton” <HTML> - opening HTML tag <HEAD> <TITLE>Page Title</TITLE> </HEAD> <BODY> Page Body </BODY> </HTML> - closing HTML TAG Not all tags need a closing tag, but its always safer to include it An html document should end with the extension “.html” or “.htm” As I will demonstrate, an html document can be written using notepad; no special software is needed HTML Tags First tag: <HTML> First tag in document Tag tells the Internet browser that it is reading an HTML document Without it, the browser would think it was viewing a text document Closed at end of document with </HTML> tag All content of web page is between <HTML> and </HTML> Can think of the <HTML> tag as being a container, since it “holds” the entire content of the web page between the <HTML> and </HTML> tags HTML Tags Next tag: <HEAD> Think of it as a container for aspects of the page that aren't part of the “meat” of the page For the purposes of this intro, will look at the <TITLE> tag and <META name=“description” content=”...”> tag that go within the <HEAD> container; that is, between the <HEAD> and </HEAD> tags Closed with </HEAD> tag <TITLE> Tag Belongs inside the <HEAD> container; -

Annex I: List of Internet Robots, Crawlers, Spiders, Etc. This Is A
Annex I: List of internet robots, crawlers, spiders, etc. This is a revised list published on 15/04/2016. Please note it is rationalised, removing some previously redundant entries (e.g. the text ‘bot’ – msnbot, awbot, bbot, turnitinbot, etc. – which is now collapsed down to a single entry ‘bot’). COUNTER welcomes updates and suggestions for this list from our community of users. bot spider crawl ^.?$ [^a]fish ^IDA$ ^ruby$ ^voyager\/ ^@ozilla\/\d ^ÆƽâºóµÄ$ ^ÆƽâºóµÄ$ alexa Alexandria(\s|\+)prototype(\s|\+)project AllenTrack almaden appie Arachmo architext aria2\/\d arks ^Array$ asterias atomz BDFetch Betsie biadu biglotron BingPreview bjaaland Blackboard[\+\s]Safeassign blaiz\-bee bloglines blogpulse boitho\.com\-dc bookmark\-manager Brutus\/AET bwh3_user_agent CakePHP celestial cfnetwork checkprivacy China\sLocal\sBrowse\s2\.6 cloakDetect coccoc\/1\.0 Code\sSample\sWeb\sClient ColdFusion combine contentmatch ContentSmartz core CoverScout curl\/7 cursor custo DataCha0s\/2\.0 daumoa ^\%?default\%?$ Dispatch\/\d docomo Download\+Master DSurf easydl EBSCO\sEJS\sContent\sServer ELinks\/ EmailSiphon EmailWolf EndNote EThOS\+\(British\+Library\) facebookexternalhit\/ favorg FDM(\s|\+)\d feedburner FeedFetcher feedreader ferret Fetch(\s|\+)API(\s|\+)Request findlinks ^FileDown$ ^Filter$ ^firefox$ ^FOCA Fulltext Funnelback GetRight geturl GLMSLinkAnalysis Goldfire(\s|\+)Server google grub gulliver gvfs\/ harvest heritrix holmes htdig htmlparser HttpComponents\/1.1 HTTPFetcher http.?client httpget httrack ia_archiver ichiro iktomi ilse -

Transforming Library Service Through Information Commons Case Studies for the Digital Age
TRANSFORMING LIBRARY SERVICE THROUGH INFORMATION COMMONS Case Studies for the Digital Age D. Russell Bailey and Barbara Gunter Tierney TRANSFORMING LIBRARY SERVICE THROUGH INFORMATION COMMONS Case Studies for the Digital Age D. Russell Bailey and Barbara Gunter Tierney AMERICAN LIBRARY ASSOCIATION Chicago 2008 While extensive effort has gone into ensuring the reliability of information appearing in this book, the publisher makes no warranty, express or implied, on the accuracy or reliability of the information, and does not assume and hereby disclaims any liability to any person for any loss or damage caused by errors or omissions in this publication. Composition in Berkeley and Antique Olive typefaces using InDesign on a PC platform. The paper used in this publication meets the minimum requirements of American National Standard for Information Sciences—Permanence of Paper for Printed Library Materials, ANSI Z39.48-1992. Library of Congress Cataloging-in-Publication Data Bailey, D. Russell. Transforming library service through information commons : case studies for the digital age / D. Russell Bailey and Barbara Gunter Tierney. p. cm. Includes bibliographical references and index. ISBN-13: 978-0-8389-0958-4 (alk. paper) ISBN-10: 0-8389-0958-2 (alk. paper) 1. Information commons. I. Tierney, Barbara. II. Title. ZA3270.B35 2008 025.5'23—dc22 2007040040 Copyright © 2008 by the American Library Associ ation. All rights reserved except those which may be granted by Sections 107 and 108 of the Copyright Revision Act of 1976. ISBN-13: 978-0-8389-0958-4