Architecting Next-Generation Networks
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

~DRAFT~ CHAPTER 5: Link Layer
~DRAFT~ CHAPTER 5: Link layer Contents Network notes – Link layer ..................................................................................................................... 1 1 Context of Chapter .................................................................................................................. 2 2 Introduction ............................................................................................................................. 2 3 Objectives of Chapter/module ................................................................................................ 3 4 Services of the link layer ......................................................................................................... 4 5 Error detection ........................................................................................................................ 4 a. Parity check ............................................................................................................................. 4 b. Cyclic Redundancy Check ...................................................................................................... 5 6 Error Correction ...................................................................................................................... 5 7 MAC ....................................................................................................................................... 6 a. Fixed assigned MAC .............................................................................................................. -

Networking Packet Broadcast Storms
Lesson Learned Networking Packet Broadcast Storms Primary Interest Groups Balancing Authorities (BAs) Generator Operators (GOPs) Reliability Coordinators (RCs) Transmission Operators (TOPs) Transmission Owners (TOs) that own and operate an Energy Management System (EMS) Problem Statement When a second network cable was connected from a voice over internet protocol (VOIP) phone to a network switch lacking proper settings, a packet broadcast storm prevented network communications from functioning, and supervisory control and data acquisition (SCADA) was lost for several hours. Broadcast storm events have also arisen from substation local area network (LAN) issues. Details A conference room was set up for a training class that needed to accommodate multiple PCs. The bridge protocol data unit (BPDU) packet propagation prevention setting was disabled on a port in the conference room in order to place a network switch off of that port. Upon completion of the training, the network switch was removed; however, the BPDU packet propagation setting was inadvertently not restored. As part of a telephone upgrade project, the traditional phone in this conference room was recently replaced by a VOIP phone. Later, an additional network cable was connected to the output port of this VOIP phone into a secondary network jack within the conference room. When the second network cable was connected from a VOIP phone to a network switch lacking proper settings, a switching loop resulted. Spanning tree protocol is normally used to prevent switching loops from propagating broadcast packets continuously until the network capacity is overwhelmed. A broadcast packet storm from the switching loop prevented network communications from functioning and SCADA was lost for several hours. -
Frequently Asked Questions
User Guide E-Series Routers Linksys E-Series Table of Contents Table of Contents Product overview Wireless Security E900/E1200/E1500/E2500/E3200 1 Wireless > Wireless Security 8 Back view 1 Personal options 8 Bottom view 1 Office options 8 E4200 2 Option settings 8 Top view 2 Back view 2 Troubleshooting Setting Up Your E-Series Router How to run Linksys Connect after setup 11 Your router was not successfully set up 12 Where to find more help 3 Get Windows XP Service Pack 3 message 12 How to set up your router 3 Your Internet cable is not plugged in message 13 How to start Linksys Connect 3 Use Linksys Connect to manage your router 3 Cannot access your router message 14 How to manually set up your router 3 Device not found message 15 Advanced Configuration Specifications How to open the browser-based utility 4 Linksys E900 17 Setup > Basic Setup 5 Linksys E1200 18 Language 5 Linksys E1500 19 Internet Setup 5 Linksys E2500 20 Wireless > Basic Wireless Settings 6 Wireless Settings 6 Linksys E3200 21 Linksys E4200 22 i Linksys E-Series Product overview • Power indicator—Stays on steadily while power is connected and Product overview following a successful Wi-Fi Protected Setup connection Flashes slowly during bootup, during firmware upgrades, and during a Wi-Fi Protected Setup connection Flashes quickly when there is a Wi-Fi Protected Setup error • Power—Connect the included AC power adapter to this port E900/E1200/E1500/E2500/E3200 CAUTION Use only the adapter that came with your router Back view • Power button—Press | (on) to turn on the -

Network PC Card
Instant WirelessTM Series Network PC Card Use this Guide to install the following: WPC11 V2.5 User Guide COPYRIGHT & TRADEMARKS Copyright © 2001 Linksys, All Rights Reserved. Instant Wireless™ is a registered trade- mark of Linksys. Microsoft, Windows, and the Windows logo are registered trademarks of Microsoft Corporation. All other trademarks and brand names are the property of their respective proprietors. LIMITED WARRANTY Linksys guarantees that every Instant Wireless™ Network PC Card V2.5 is free from phys- ical defects in material and workmanship under normal use for one year from the date of purchase. If these products prove defective during this warranty period, call Linksys Customer Support in order to obtain a Return Authorization Number. BE SURE TO HAVE YOUR PROOF OF PURCHASE AND A BARCODE FROM THE PRODUCT’S PACKAGING ON HAND WHEN CALLING. RETURN REQUESTS CANNOT BE PROCESSED WITHOUT PROOF OF PURCHASE. When returning a product, mark the Return Authorization Number clearly on the outside of the package and include your original proof of pur- chase. All customers located outside of the United States of America and Canada shall be held responsible for shipping and handling charges. IN NO EVENT SHALL LINKSYS’ LIABILITY EXCEED THE PRICE PAID FOR THE PROD- UCT FROM DIRECT, INDIRECT, SPECIAL, INCIDENTAL, OR CONSEQUENTIAL DAM- AGES RESULTING FROM THE USE OF THE PRODUCT, ITS ACCOMPANYING SOFT- WARE, OR ITS DOCUMENTATION. LINKSYS DOES NOT OFFER REFUNDS FOR ANY PRODUCT. Linksys makes no warranty or representation, expressed, implied, or statuto- ry, with respect to its products or the contents or use of this documentation and all accompanying software, and specifically disclaims its quality, performance, mer- chantability, or fitness for any particular purpose. -
Application of Ethernet Networking Devices Used for Protection and Control Applications in Electric Power Substations
Application of Ethernet Networking Devices Used for Protection and Control Applications in Electric Power Substations Report of Working Group P6 of the Power System Communications and Cybersecurity Committee of the Power and Energy Society of IEEE September 12, 2017 1 IEEE PES Power System Communications and Cybersecurity Committee (PSCCC) Working Group P6, Configuring Ethernet Communications Equipment for Substation Protection and Control Applications, has existed during the course of report development as Working Group H12 of the IEEE PES Power System Relaying Committee (PSRC). The WG designation changed as a result of a recent IEEE PES Technical Committee reorganization. The membership of H12 and P6 at time of approval voting is as follows: Eric A. Udren, Chair Benton Vandiver, Vice Chair Jay Anderson Galina Antonova Alex Apostolov Philip Beaumont Robert Beresh Christoph Brunner Fernando Calero Christopher Chelmecki Thomas Dahlin Bill Dickerson Michael Dood Herbert Falk Didier Giarratano Roman Graf Christopher Huntley Anthony Johnson Marc LaCroix Deepak Maragal Aaron Martin Roger E. Ray Veselin Skendzic Charles Sufana John T. Tengdin 2 IEEE PES PSCCC P6 Report, September 2017 Application of Ethernet Networking Devices Used for Protection and Control Applications in Electric Power Substations Table of Contents 1. Introduction ...................................................................................... 10 2. Ethernet for protection and control .................................................. 10 3. Overview of Ethernet message -

USER GUIDE R75 Model EA7500/EA7500S Contents
USER GUIDE R75 Model EA7500/EA7500S Contents Product Overview .........................................................................................................3 Top ....................................................................................................................................................................... 3 Back ..................................................................................................................................................................... 4 Setting Up: Basics ........................................................................................................5 Where to find more help ............................................................................................................................... 5 How to install your router ............................................................................................................................ 6 www.LinksysSmartWiFi.com ....................................................................................9 How to log in to www.LinksysSmartWiFi.com ...................................................................................... 9 Network Map ................................................................................................................................................. 11 Guest Access ................................................................................................................................................ 11 Parental Controls........................................................................................................................................ -
Wireless-G Broadband Router WIRELESS User Guide
GHz 2,4802.11g Wireless-G Broadband Router WIRELESS User Guide Model No. WRT54G (EU/LA) Wireless-G Broadband Router Copyright and Trademarks Specifications are subject to change without notice. Linksys is a registered trademark or trademark of Cisco Systems, Inc. and/or its affiliates in the U.S. and certain other countries. Copyright © 2006 Cisco Systems, Inc. All rights reserved. Other brands and product names are trademarks or registered trademarks of their respective holders. How to Use This User Guide This User Guide has been designed to make understanding networking with the Wireless-G Broadband Router easier than ever. Look for the following items when reading this User Guide: This checkmark means there is a note of interest and is something you should pay special attention to while using the Wireless-G Broadband Router. This exclamation point means there is a caution or warning and is something that could damage your property or the Wireless-G Broadband Router. This question mark provides you with a reminder about something you might need to do while using the Wireless-G Broadband Router. In addition to these symbols, there are definitions for technical terms that are presented like this: word: definition. Also, each figure (diagram, screenshot, or other image) is provided with a figure number and description, like this: Figure 0-1: Sample Figure Description Figure numbers and descriptions can also be found in the “List of Figures” section in the “Table of Contents”. WRT54GV7-EU-UG-60307 BW Wireless-G Broadband Router Table of -
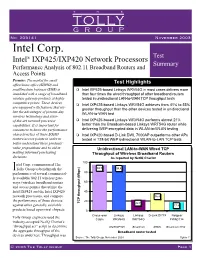
Intel Corp IXP425/IXP420 Network Processors
TH E TOLLY GROUP No. 203141 November 2003 Intel Corp. Test Intel® IXP425/IXP420 Network Processors Summary Performance Analysis of 802.11 Broadband Routers and Access Points Premise: The market for small Test Highlights office/home office (SOHO) and small/medium business (SMB) is Intel IXP425-based Linksys WRV54G in most cases delivers more inundated with a range of broadband than four times the wired throughput of other broadband routers wireless gateway products at highly tested in unidirectional LAN-to-WAN TCP throughput tests competitive prices. These devices Intel IXP425-based Linksys WRV54G achieves from 41% to 55% are equipped with features that uti- greater throughput than the other devices tested in unidirectional lize the advantages of present-day WLAN-to-WAN test wireless technology and state- of-the-art network processor Intel IXP425-based Linksys WRV54G performs almost 21% capabilities. It is important for better than the Broadcom-based Linksys WRT54G router while consumers to know the performance delivering WEP-encrypted data in WLAN-to-WLAN testing characteristics of these SOHO Intel IXP420-based D-Link DWL 7000AP outperforms other APs routers/access points in order to tested in 128-bit WEP bidirectional WLAN-to-LAN TCP tests better understand these products’ value propositions and to aid in Unidirectional LAN-to-WAN Wired TCP making informed purchasing Throughput of Wireless Broadband Routers decisions. As reported by NetIQ Chariot 100 ntel Corp. commissioned The ITolly Group to benchmark the 94.7 94.4 performance of several commercial- 80 ly available 802.11 wireless gate- ways (wireless broadband routers 60 and access points) that utilize the Intel IXP425 and the Intel IXP420 40 network processors, and compare 36.4 the performance of those devices 20 TCP throughput (Mbps) 22.7 against other generally available 17.8 products based upon rival chipsets. -

Wireless LAN (WLAN) Switching
TECHNICAL WHITEPAPER Wireless LAN (WLAN) Switching An examination of a long range wireless switching technology to enable large and secure Wi-Fi Deployments TECHNICAL WHITEPAPER Wireless LAN (WLAN) Switching This whitepaper provides a detailed explanation of a new wireless switching technology that will allow for large and secure deployments of WLANS. The explosion of wireless networking on the scene in the past few years has been unprecedented. Many compare the market acceptance of this technology to the advent of the early days of Ethernet. When Ethernet was adopted as a standard, it was quickly embraced by the users of PCs, and the acceptance of wireless LANs has followed a similar path. Comparatively, the adoption of the wireless standard, IEEE 802.11, (also known as Wi-Fi) and use of mobile computing platforms is the basis of the wireless revolution. While this is a very good comparative analysis, in the real sense the adoption rate of wireless LANs has been much higher. The worker of today has morphed into a mobile worker that has grown accustomed to information on the fly, and will demand information inside and outside of the workplace. These factors have converged and are providing the impetus for the hyper acceptance of wireless technologies where by IT professionals are faced with the choice of embracing the technology or having it implemented by their users. Wireless Adoption at Warp Speed The next logical evolution of the technology was to make it ubiquitous to the mobile wireless worker. Intel is helping this technology “cross the chasm” into the mainstream by spending $300 million to market their introduction of the Centrino™ mobile technology, which provides built-in Wi-Fi for the mobile computing platform. -

Wireless Network Bridge Lmbc-650
DIGITAL LIGHTING MANAGEMENT WIRELESS DLM WATTSTOPPER® WIRELESS NETWORK BRIDGE LMBC-650 • Connects any DLM wired devices to a wireless IPv6 Mesh secure self-forming network • Built-in IPv6 Mesh and Bluetooth® low energy technology antenna provides robust signal strength and reliable communication • Two RJ-45 ports for DLM Cat 5e communication and class 2 power • Includes trusted hardware chips for device validation and secure out-of-box wireless AES 128-bit encryption • Tri-color LED indicator displays wireless network health, DLM Cat 5e communication, and ability to identify during commissioning • Plenum rated with mounting hardware for fast installation • In conjunction with an LMBR-650, supports third party integration with BAS through BACnet/IP over IPv6 Wireless Mesh network • Commissioning using LMCS-100 software ® IPv6 MESH Description Operation The LMBC-650 Wireless Network Bridge provides room The wireless network bridge operates using Class 2 power to room network connectivity for rooms with Wattstopper supplied by a DLM local network from one or more DLM room Digital Lighting Management (DLM) devices. The wireless controllers. It connects to the free-topology local network at DLM platform simplifies room to room communication and any convenient location using a standard LMRJ cable. It then installation, and eliminates potential start-up delays caused by securely communicates via encrypted wireless protocol over wiring issues. a mesh network to an LMBR-650 Border Router on the same The DLM local room network must include at least one wired floor of the building. controller. Once the LMBC-650 is connected to LMBR-650 The LMBC-650 monitors the DLM local network and network and then either using LMCS-100 or DLM Dashboard automatically exposes all room devices, settings and software, the system can expose BACnet protocol to revel the calibrations to the LMBR-650 Border Router. -
Gigabit Ethernet Switch User's Guide
Gigabit Ethernet Switch User’s Guide Version 1.0 P/N: ATNSGD8082503 Rev.1 This User's Guide contains important information regarding the installation of your switch. Please read it completely before beginning installation. For future reference, record the serial number of your network switch in the space below: SERIAL number The serial number is located on the bottom of the switch. Amer.com 7259 Bryan Dairy Road, Largo, FL 33777 USA © Amer.com Corp., 1997-2002 All rights reserved. No part of this publication may be reproduced in any form or by any means or used to make any derivative such as translation, transformation, or adaptation without permission from Amer.com, as stipulated by the United States Copyright Act of 1976. Amer.com reserves the right to make changes to this document and the products which it describes without notice. Amer.com shall not be liable for technical or editorial errors or omissions made herein; nor for incidental or consequential damages resulting from the furnishing, performance, or use of this material. Amer.com is a registered trademark of Amer.com. All other trademarks and trade names are properties of their owners. FCC Class A Certification Statement Model SGD8 FCC Class A This device complies with Part 15 of the FCC rules. Operation is subject to the following two conditions: (1)This device may not cause harmful interference, and (2)This device must accept any interference received, including interference that may cause undesired operation. This equipment has been tested and found to comply with the limits for a Class A digital device, pursuant to Part 15 of the FCC Rules. -

216155 October 2016 Commissioned by Linksys, Inc
#216155 October 2016 Commissioned by Linksys, Inc. Linksys EA7300 Max-Stream AC1750 MU-MIMO Gigabit Router Comparative Wireless LAN Performance EXECUTIVE SUMMARY Busy home networks are now the rule rather than the exception with multiple THE BOTTOM LINE clients demanding multiple high-bandwidth services - like video streaming - Linksys EA7300 Max-Stream AC1750 MU-MIMO simultaneously. Multi-user MIMO (MU-MIMO) technology can deliver Gigabit Router provides: significantly more throughput to multiple users than the prior generation single-user MIMO (SU-MIMO). The Linksys EA7300 Max-Stream AC1750 MU- Up to 3.5X greater aggregate throughput in line-of- MIMO Gigabit Router is a home entertainment Wi-Fi router optimized for online 1 sight tests gaming and streaming. Linksys, Inc. commissioned Tolly to benchmark the throughput of the Linksys Up to 3.5X greater per client average throughput in 2 EA7300 and compare that to the aggregate throughput of several competing line-of-sight tests dual-band, AC1750 wireless LAN (WLAN) solutions. The Linksys solution can deliver up to 3.5X the multi-client, aggregate throughput of competing Up to 4.4X greater individual client average 3 solutions. See Figure 1. ...<continued on next page> throughput in long distance tests Wireless LAN MU-MIMO Multi-Client Downstream Performance Four Clients, Line-of-Sight Aggregate Throughput, (as reported by Ixia IxChariot v7.10 SP3) 600 500 Linksys MU-MIMO delivers up to 3.5X greater aggregate throughput. 400 300 200 Throughput (Mbps) 100 0 Solution Under Test Linksys EA7300 ASUS RT-AC66U NETGEAR R6400 TP-LINK Archer C7 TP-LINK Archer C8 Notes: Dual-band devices provide a 2.4GHz radio and a 5GHz radio.