Wiretapping End-To-End Encrypted Voip Calls: Real-World Attacks on ZRTP
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Course 5 Lesson 2
This material is based on work supported by the National Science Foundation under Grant No. 0802551 Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author (s) and do not necessarily reflect the views of the National Science Foundation C5L3S1 With the advent of the Internet, social networking, and open communication, a vast amount of information is readily available on the Internet for anyone to access. Despite this trend, computer users need to ensure private or personal communications remain confidential and are viewed only by the intended party. Private information such as a social security numbers, school transcripts, medical histories, tax records, banking, and legal documents should be secure when transmitted online or stored locally. One way to keep data confidential is to encrypt it. Militaries,U the governments, industries, and any organization having a desire to maintain privacy have used encryption techniques to secure information. Encryption helps to boost confidence in the security of online commerce and is necessary for secure transactions. In this lesson, you will review encryption and examine several tools used to encrypt data. You will also learn to encrypt and decrypt data. Anyone who desires to administer computer networks and work with private data must have some familiarity with basic encryption protocols and techniques. C5L3S2 You should know what will be expected of you when you complete this lesson. These expectations are presented as objectives. Objectives are short statements of expectations that tell you what you must be able to do, perform, learn, or adjust after reviewing the lesson. -

Lesson Plans and Resources for There There by Tommy Orange
Lesson Plans and Resources for There There by Tommy Orange Table of Contents 1. Overview and Essential Questions 2. In-Class Introduction 3. Common Core Standards Alignment 4. Reader Response Questions 5. Literary Log Prompts + Worksheets 6. Suggested Analytical Assessments 7. Suggested Creative Assessments 8. Online Resources 9. Print Resources - “How to Talk to Each Other When There’s So Little Common Ground” by Tommy Orange - Book Review from The New York Times - Book Review from Tribes.org - Interview with Tommy Orange from Powell’s Book Blog These resources are all available, both separately and together, at www.freelibrary.org/onebook Please send any comments or feedback about these resources to [email protected]. OVERVIEW AND ESSENTIAL QUESTIONS The materials in this unit plan are meant to be flexible and easy to adapt to your own classroom. Each chapter has discussion questions provided in a later section. Through reading the book and completing any of the suggested activities, students can achieve any number of the following understandings: - A person’s identity does not form automatically – it must be cultivated. - Trauma is intergenerational -- hardship is often passed down through families. - A physical place can both define and destroy an individual. Students should be introduced to the following key questions as they begin reading. They can be discussed both in universal terms and in relation to specific characters in the book: Universal - How has your family cultivated your identity? How have you cultivated it yourself? -
Copyrighted Material
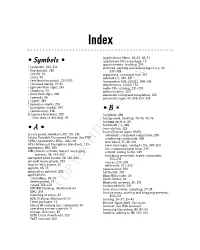
33_754935 bindex.qxp 11/7/05 10:09 PM Page 345 Index Applications Menu, 42–43, 68–71 • Symbols • Applixware Office package, 15 appointments, tracking, 210 * (asterisk), 249, 251 archives, packing and unpacking (tar), 20, \ (backslash), 248 337–338 - (dash), 94 arguments, command line, 247 . (dot), 92 asterisk (*), 249, 251 ! (exclamation point), 252–253 Asymmetric DSL (ADSL), 108–109 / (forward slash), 79, 81 attachments, e-mail, 154 > (greater-than sign), 249 audio CDs, playing, 221–223 - (hyphen), 95 authentication, 292 < (less-than sign), 249 automatic command completion, 250 . (period), 96 automatic login, 40, 318–319, 325 | (pipe), 248 ? (question mark), 251 " (quotation marks), 247 ; (semicolon), 248 • B • [] (square brackets), 252 backdoor, 292 .. (two dots or dot-dot), 92 background, desktop, 73–74, 75–76 backing up files, 20 backslash (\), 248 • A • base station, 129 bash (Bourne Again Shell) access point, wireless LAN, 129, 131 automatic command completion, 250 Adobe Portable Document Format. See PDF combining commands, 248 ADSL (Asymmetric DSL), 108–109 described, 47–48, 246 AES (Advanced Encryption Standard), 129 error messages, saving to file, 249–250 aggregator, RSS, 185 file, command input from, 249 AIM (America Online instant messaging output, saving to file, 249 service), 54, 161–162 repeating previously typed commands, Akregator news reader, 54, 185–186 252–253 amaroK music player, 224 syntax, 247–248 Apache Web server, 16 wildcards, 251–252 applets, 68, 75 bastion host, 293 application gateway, 292 bit bucket, 250 applications Blam RSS reader, 54 controlling, 18–19 block device, 94 development, 17 Bluetooth wireless, 20, 271 e-mail, 152–153 bookmark field, 200 GNOME Desktop, illustrated,COPYRIGHTED 64 boot menu MATERIAL items, installing, 27–28 GNU, 343 boot process, starting and stopping services, installing at setup, 32 263–264 KDE Desktop, illustrated, 64 booting, 26–27, 39–40 Linux packages, 11 Bourne Again Shell. -

Uila Supported Apps
Uila Supported Applications and Protocols updated Oct 2020 Application/Protocol Name Full Description 01net.com 01net website, a French high-tech news site. 050 plus is a Japanese embedded smartphone application dedicated to 050 plus audio-conferencing. 0zz0.com 0zz0 is an online solution to store, send and share files 10050.net China Railcom group web portal. This protocol plug-in classifies the http traffic to the host 10086.cn. It also 10086.cn classifies the ssl traffic to the Common Name 10086.cn. 104.com Web site dedicated to job research. 1111.com.tw Website dedicated to job research in Taiwan. 114la.com Chinese web portal operated by YLMF Computer Technology Co. Chinese cloud storing system of the 115 website. It is operated by YLMF 115.com Computer Technology Co. 118114.cn Chinese booking and reservation portal. 11st.co.kr Korean shopping website 11st. It is operated by SK Planet Co. 1337x.org Bittorrent tracker search engine 139mail 139mail is a chinese webmail powered by China Mobile. 15min.lt Lithuanian news portal Chinese web portal 163. It is operated by NetEase, a company which 163.com pioneered the development of Internet in China. 17173.com Website distributing Chinese games. 17u.com Chinese online travel booking website. 20 minutes is a free, daily newspaper available in France, Spain and 20minutes Switzerland. This plugin classifies websites. 24h.com.vn Vietnamese news portal 24ora.com Aruban news portal 24sata.hr Croatian news portal 24SevenOffice 24SevenOffice is a web-based Enterprise resource planning (ERP) systems. 24ur.com Slovenian news portal 2ch.net Japanese adult videos web site 2Shared 2shared is an online space for sharing and storage. -

Cisco SCA BB Protocol Reference Guide
Cisco Service Control Application for Broadband Protocol Reference Guide Protocol Pack #60 August 02, 2018 Cisco Systems, Inc. www.cisco.com Cisco has more than 200 offices worldwide. Addresses, phone numbers, and fax numbers are listed on the Cisco website at www.cisco.com/go/offices. THE SPECIFICATIONS AND INFORMATION REGARDING THE PRODUCTS IN THIS MANUAL ARE SUBJECT TO CHANGE WITHOUT NOTICE. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL RESPONSIBILITY FOR THEIR APPLICATION OF ANY PRODUCTS. THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR CISCO REPRESENTATIVE FOR A COPY. The Cisco implementation of TCP header compression is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB’s public domain version of the UNIX operating system. All rights reserved. Copyright © 1981, Regents of the University of California. NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ARE PROVIDED “AS IS” WITH ALL FAULTS. CISCO AND THE ABOVE-NAMED SUPPLIERS DISCLAIM ALL WARRANTIES, EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, THOSE OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE. IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. -

The Handshake - Establishing Secure Connections Over Insecure Channels
Lecture 13: The handshake - establishing secure connections over insecure channels Boaz Barak We’ve now compiled all the tools that are needed for the basic goal of cryptography (which is still being subverted quite often) allowing Alice and Bob to exchange messages assuring their integrity and confidentiality over a channel that is observed or controlled by an adversary. Our tools for achieving this goal are: • Public key (aka assymetric) encryption schemes. • Public key (aka assymetric) digital signatures schemes. • Private key (aka symmetric) encryption schemes - block ciphers and stream ciphers. • Private key (aka symmetric) message authentication codes and psedoran- dom functions. • Hash functions that are used both as ways to compress messages for authentication as well as key derivation and other tasks. The notions of security we require from these building blocks can vary as well. For encryption schemes we talk about CPA (chosen plaintext attack) and CCA (chosen ciphertext attacks), for hash functions we talk about collision-resistance, being used (combined with keys) as pseudorandom functions, and then sometimes we simply model those as random oracles. Also, all of those tools require access to a source of randomness, and here we use hash functions as well for entropy extraction. Cryptography’s obsession with adjectives. As we learn more and more cryptography we see more and more adjectives, every notion seems to have modifiers such as “non malleable”, “leakage-resilient”, “identity based”, “concurrently secure”, “adaptive”, “non-interactive”, etc.. etc. Indeed, this motivated a parody web page of an automatic crypto paper title generator. Unlike algorithms, where typically there are straightforward quantitative tradeoffs (e.g., faster is better), in cryptography there are many qualitative ways protocols can vary based on the assumptions they operate under and the notions of security they provide. -

Unit 5: Understanding and Resolving Guest Problems
Unit 5: Understanding and Resolving Guest Problems Project Hotel T.E.A.C.H Curriculum Center for Immigrant Education and Training (ACE) LaGuardia Community College Hotel TEACH Lesson Plan Unit 5, Lesson 1 Career Counseling: Listening with Empathy Objectives Sts will learn to resolve problems and listen empathetically for improved customer service. EFF Skill Sets addressed Cooperate with Others: Try to adjust one’s actions to take into the account the needs of others and/or the task to be accomplished. Industry Skill Sets addressed Resolve Guest Problems Exceed Customer Expectations Activity 1: Empathy Skills T introduces another important component of active listening: empathy. T asks the Sts to define “empathy.” As Sts call out answers, T leads responses towards the following definition and writes it on the board. Empathy is the ability to recognize and understand the emotions, beliefs, moods and desires of another person. Empathy is often characterized as the ability to “put oneself into another’s shoes.” T elicits from Sts the reasons why it would be important for hotel workers to have empathy. Some examples might be as follows: 1. Listening empathetically makes people feel as if they are truly being heard and that their needs will be taken care of. 2. Listening with empathy gives guests a positive experience of the hotel and of you as a worker. Guests will always remember the worker who truly listened and cared about their problem, as opposed to the worker who offers a quick solution. 3. When you acknowledge how people are feeling, you reassure them that they are understood. -

Universidad Pol Facultad D Trabajo
UNIVERSIDAD POLITÉCNICA DE MADRID FACULTAD DE INFORMÁTICA TRABAJO FINAL DE CARRERA ESTUDIO DEL PROTOCOLO XMPP DE MESAJERÍA ISTATÁEA, DE SUS ATECEDETES, Y DE SUS APLICACIOES CIVILES Y MILITARES Autor: José Carlos Díaz García Tutor: Rafael Martínez Olalla Madrid, Septiembre de 2008 2 A mis padres, Francisco y Pilar, que me empujaron siempre a terminar esta licenciatura y que tanto me han enseñado sobre la vida A mis abuelos (q.e.p.d.) A mi hijo icolás, que me ha dejado terminar este trabajo a pesar de robarle su tiempo de juego conmigo Y muy en especial, a Susana, mi fiel y leal compañera, y la luz que ilumina mi camino Agradecimientos En primer lugar, me gustaría agradecer a toda mi familia la comprensión y confianza que me han dado, una vez más, para poder concluir definitivamente esta etapa de mi vida. Sin su apoyo, no lo hubiera hecho. En segundo lugar, quiero agradecer a mis amigos Rafa y Carmen, su interés e insistencia para que llegara este momento. Por sus consejos y por su amistad, les debo mi gratitud. Por otra parte, quiero agradecer a mis compañeros asesores militares de Nextel Engineering sus explicaciones y sabios consejos, que sin duda han sido muy oportunos para escribir el capítulo cuarto de este trabajo. Del mismo modo, agradecer a Pepe Hevia, arquitecto de software de Alhambra Eidos, los buenos ratos compartidos alrrededor de nuestros viejos proyectos sobre XMPP y que encendieron prodigiosamente la mecha de este proyecto. A Jaime y a Bernardo, del Ministerio de Defensa, por haberme hecho descubrir las bondades de XMPP. -

ULTIMA X Series 3 EC Declaration of Conformity MSA
Operating Manual ULTIMAX-Series Gas Monitors Order No. 10046690/09 MSA AUER GmbH Thiemannstrasse 1 D-12059 Berlin Germany © MSA AUER GmbH. All rights reserved MSA EC Declaration of Conformity EC Declaration of Conformity Manufactured by: Mine Safety Appliances Company 1000 Cranberry Woods Drive Cranberry Township, PA 16066 USA The manufacturer or the European Authorized Representative: MSA AUER GmbH, Thiemannstrasse 1, D-12059 Berlin declares that the ULTIMA XE Main product ULTIMA XE Main with HART Module based on the EC-Type Examination Certificate: DMT 02 ATEX E 202 X complies with the ATEX directive 94/9/EC, Annex III. Quality Assurance Notification complying with Annex IV of the ATEX Directive 94/9/EC has been issued by Ineris of France, Notified Body number: 0080. The product is in conformance with the EMC directive 2004 / 108/ EC, EN 50270 :2006 Type 2 *, EN 61000 - 6 - 4 : 2007 * EN 61000-4-6 : Ultima XE MAIN HART MODULE : occasional transmission error can appear at the 2-wire version. A fault check has to be used at the receiver unit. The product complies with the directive 96/98 / EC (MarED), based on the EC-Type Examination Certificate : SEE BG 213.038 The quality survaillance is under the control of SEE BG, Notified Body number: 0736 We further declare that the product complies with the provisions of LVD Directive 2006 / 95/ EC, with the following harmonised standard: EN 61010-1 :2002 MSA AUER GmbH Berlin, October 2008 Dr. Axel Schubert R&D Instruments ® GB ULTIMA X Series 3 EC Declaration of Conformity MSA EC Declaration of Conformity Manufactured by: Mine Safety Appliances Company 1000 Cranberry Woods Drive Cranberry Township, PA 16066 USA The manufacturer or the European Authorized Representative: MSA AUER GmbH, Thiemannstrasse 1, D-12059 Berlin declares that the product ULTIMA SENSOR XE based on the EC-Type Examination Certificate: DMT 02 ATEX E 202 X complies with the ATEX directive 94/9/EC, Annex III. -

Download Windows Live Messenger for Linux Ubuntu
Download windows live messenger for linux ubuntu But installing applications in Ubuntu that were originally made for I found emescene to be the best Msn Messenger for Ubuntu Linux so far. It really gives you the feel as if you are using Windows Live Messenger. Its builds are available for Archlinux, Debian, Ubuntu, Fedora, Mandriva and Windows. At first I found it quite difficult to use Pidgin Internet Messenger on Ubuntu Linux. Even though it allows signing into MSN, Yahoo! Messenger and Google Talk. While finding MSN Messenger for Linux / Ubuntu, I found different emesene is also available and could be downloaded and installed for. At first I found it quite difficult to use Pidgin Internet Messenger on Ubuntu Linux. Even though it allows signing into MSN, Yahoo! Messenger. A simple & beautiful app for Facebook Messenger. OS X, Windows & Linux By downloading Messenger for Desktop, you acknowledge that it is not an. An alternative MSN Messenger chat client for Linux. It allows Linux users to chat with friends who use MSN Messenger in Windows or Mac OS. The strength of. Windows Live Messenger is an instant messenger application that For more information on installing applications, see InstallingSoftware. sudo apt-get install chromium-browser. 2. After the installation is Windows Live Messenger running in LinuxMint / Ubuntu. You can close the. Linux / X LAN Messenger for Debian/Ubuntu LAN Messenger for Fedora/openSUSE Download LAN Messenger for Windows. Windows installer A MSN Messenger / Live Messenger client for Linux, aiming at integration with the KDE desktop Ubuntu: Ubuntu has KMess in its default repositories. -

Wiretapping End-To-End Encrypted Voip Calls Real-World Attacks on ZRTP
Institute of Operating Systems and Computer Networks Wiretapping End-to-End Encrypted VoIP Calls Real-World Attacks on ZRTP Dominik Schürmann, Fabian Kabus, Gregor Hildermeier, Lars Wolf, 2017-07-18 wiretapping difficulty End-to-End Encryption SIP + DTLS-SRTP (SIP + Datagram Transport Layer Security-SRTP) End-to-End Encryption & Authentication SIP + SRTP + ZRTP Introduction Man-in-the-Middle ZRTP Attacks Conclusion End-to-End Security for Voice Calls Institute of Operating Systems and Computer Networks No End-to-End Security PSTN (Public Switched Telephone Network) SIP + (S)RTP (Session Initiation Protocol + Secure Real-Time Transport Protocol) 2017-07-18 Dominik Schürmann Wiretapping End-to-End Encrypted VoIP Calls Page 2 of 13 wiretapping difficulty End-to-End Encryption & Authentication SIP + SRTP + ZRTP Introduction Man-in-the-Middle ZRTP Attacks Conclusion End-to-End Security for Voice Calls Institute of Operating Systems and Computer Networks No End-to-End Security PSTN (Public Switched Telephone Network) SIP + (S)RTP (Session Initiation Protocol + Secure Real-Time Transport Protocol) End-to-End Encryption SIP + DTLS-SRTP (SIP + Datagram Transport Layer Security-SRTP) 2017-07-18 Dominik Schürmann Wiretapping End-to-End Encrypted VoIP Calls Page 2 of 13 wiretapping difficulty Introduction Man-in-the-Middle ZRTP Attacks Conclusion End-to-End Security for Voice Calls Institute of Operating Systems and Computer Networks No End-to-End Security PSTN (Public Switched Telephone Network) SIP + (S)RTP (Session Initiation Protocol + Secure Real-Time -

AUTHENTICATION TECHNIQUES for HETEROGENEOUS TELEPHONE NETWORKS by BRADLEY GALLOWAY REAVES a DISSERTATION PRESENTED to the GRADUA
AUTHENTICATION TECHNIQUES FOR HETEROGENEOUS TELEPHONE NETWORKS By BRADLEY GALLOWAY REAVES A DISSERTATION PRESENTED TO THE GRADUATE SCHOOL OF THE UNIVERSITY OF FLORIDA IN PARTIAL FULFILLMENT OF THE REQUIREMENTS FOR THE DEGREE OF DOCTOR OF PHILOSOPHY UNIVERSITY OF FLORIDA 2017 © 2017 Bradley Galloway Reaves For Sarah ACKNOWLEDGMENTS Iamonlywritingthistodaybecauseofthemultitudeoffamily,friends,teachers,and colleagues who helped get me here. This journey began in high school, when Mrs. Reid, my English teacher, suggested that I would make a good college professor. I wasn’t sure about the idea until my second programming class in college. I loved programming, so I would do the lab assignments at home, then show up in the lab to demonstrate the project to the TA. My work for the week was done, but I didn’t leave the lab. Instead, I stayed for the next few hours helping other students when they needed help with the programming assignments. It became the best part of my week, and I realized that there was no career I wanted more than to be a professor of computing. Having a goal and knowing what it takes to achieve it are two very di↵erent things. At the time I knew I needed a PhD, but nothing of what it took to get one. Luckily, I had wonderfully supportive professors and advisors who told me what it took, and one in particular helped me take the first steps toward a research career. Tommy Morris was a new professor at Mississippi State, and after teaching my digital design class o↵ered me a (paid!) position in his research lab.