Windows 98 Beta 3 Release
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Optimizing and Protecting Hard Drives ‐ Chapter # 9
Optimizing and Protecting Hard Drives ‐ Chapter # 9 Amy Hissom Key Terms antivirus (AV) software — Utility programs that prevent infection or scan a system to detect and remove viruses. McAfee Associates’ VirusScan and Norton AntiVirus are two popular AV packages. backup — An extra copy of a file, used in the event that the original becomes damaged or destroyed. boot sector virus — An infectious program that can replace the boot program with a modified, infected version of the boot command utilities, often causing boot and data retrieval problems. buffer — A temporary memory area where data is kept before being written to a hard drive or sent to a printer, thus reducing the number of writes to the devices. chain — A group of clusters used to hold a single file. child, parent, grandparent backup method — A plan for backing up and reusing tapes or removable disks by rotating them each day (child), week (parent), and month (grandparent). cross-linked clusters — Errors caused when more than one file points to a cluster, and the files appear to share the same disk space, according to the file allocation table. defragment — To “optimize” or rewrite a file to a disk in one contiguous chain of clusters, thus speeding up data retrieval. differential backup — Backup method that backs up only files that have changed or have been created since the last full backup. When recovering data, only two backups are needed: the full backup and the last differential backup. disk cache — A method whereby recently retrieved data and adjacent data are read into memory in advance, anticipating the next CPU request. -

Softwindows™ 95 for UNIX Administrator's Guide (Version 5 of Softwindows
SoftWindows™ 95 for UNIX Administrator’s Guide (Version 5 of SoftWindows 95) Document Number 007-3221-006 CONTRIBUTORS Edited by Karin Borda and Douglas B. O’Morain Production by Carlos Miqueo © 1998, Silicon Graphics, Inc.— All Rights Reserved The contents of this document may not be copied or duplicated in any form, in whole or in part, without the prior written permission of Silicon Graphics, Inc. RESTRICTED RIGHTS LEGEND Use, duplication, or disclosure of the technical data contained in this document by the Government is subject to restrictions as set forth in subdivision (c) (1) (ii) of the Rights in Technical Data and Computer Software clause at DFARS 52.227-7013 and/or in similar or successor clauses in the FAR, or in the DOD or NASA FAR Supplement. Unpublished rights reserved under the Copyright Laws of the United States. Contractor/manufacturer is Silicon Graphics, Inc., 2011 N. Shoreline Blvd., Mountain View, CA 94043-1389. TurboStart and SoftNode are registered trademarks of Insignia Solutions. SoftWindows is a trademark used under license. Silicon Graphics, the Silicon Graphics logo and IRIX are registered trademarks, and Indy, O2, and IRIS InSight are trademarks of Silicon Graphics, Inc. R5000 and R10000 are registered trademarks of MIPS Technologies, Inc. Apple and Macintosh are registered trademarks of Apple Computer, Inc. DEC is a trademark of Digital Equipment Corporation. WinPost is a trademark of Eastern Mountain Software. FLEXlm is a trademark of Globetrotter Software Inc. IBM is a registered trademark and IBM PC and IBM PC/AT are trademarks of International Business Machines Corp. Intel and Pentium are registered trademarks of Intel Corporation. -

MX2 Reference Guide, Rev A
MX2 Reference Guide MX2A137REFGD October 2000 E-EQ-MX2RG-A-ARC Copyright © 2000 by LXE Inc. An EMS Technologies Company All Rights Reserved MX2A1 3 7REFGD REV I S I ON A REGULATORY NOTICES Notice: LXE Inc. reserves the right to make improvements or changes in the products described in this manual at any time without notice. While reasonable efforts have been made in the preparation of this document to assure its accuracy, LXE assumes no liability resulting from any errors or omissions in this document, or from the use of the information contained herein. Copyright Notice: This manual is copyrighted. All rights are reserved. This document may not, in whole or in part, be copied, photocopied, reproduced, translated or reduced to any electronic medium or machine-readable form without prior consent, in writing, from LXE Inc. Copyright © 2000 by LXE Inc., An EMS Technologies Company 125 Technology Parkway, Norcross, GA 30092, U.S.A. (770) 447-4224 LXE is a registered trademark of LXE Inc. All other brand or product names are trademarks or registered trademarks of their respective companies or organizations. Note: The original equipment’s Reference Manual is copyrighted by PSC® Inc. This manual has been amended by LXE® Inc., for the MX2 and Docking Stations with PSC’s express permission. Notice: The long term characteristics or the possible physiological effects of radio frequency electromagnetic fields have not been investigated by UL. FCC Information: This device complies with FCC Rules, part 15. Operation is subject to the following conditions: 1. This device may not cause harmful interference and 2. -

Scala Infochannel Player Setup Guide
SETUP GUIDE P/N: D40E04-01 Copyright © 1993-2002 Scala, Inc. All rights reserved. No part of this publication, nor any parts of this package, may be copied or distributed, transmitted, transcribed, recorded, photocopied, stored in a retrieval system, or translated into any human or computer language, in any form or by any means, electronic, mechanical, magnetic, manual, or otherwise, or disclosed to third parties without the prior written permission of Scala Incorporated. TRADEMARKS Scala, the exclamation point logo, and InfoChannel are registered trademarks of Scala, Inc. All other trademarks or registered trademarks are the sole property of their respective companies. The following are trademarks or registered trademarks of the companies listed, in the United States and other countries: Microsoft, MS-DOS, Windows, Windows 95, Windows 98, Windows NT, Windows 2000, Windows XP, DirectX, DirectDraw, DirectSound, ActiveX, ActiveMovie, Internet Explorer, Outlook Express: Microsoft Corporation IBM, IBM-PC: International Business Machines Corporation Intel, Pentium, Indeo: Intel Corporation Adobe, the Adobe logo, Adobe Type Manager, Acrobat, ATM, PostScript: Adobe Systems Incorporated TrueType, QuickTime, Macintosh: Apple Computer, Incorporated Agfa: Agfa-Gevaert AG, Agfa Division, Bayer Corporation “Segoe” is a trademark of Agfa Monotype Corporation. “Flash” and “Folio” are trademarks of Bauer Types S.A. Some parts are derived from the RSA Data Security, Inc. MD5 Message-Digest Algorithm. JPEG file handling is based in part on the work of the Independent JPEG Group. Lexsaurus Speller Technology Copyright © 1992, 1997 by Lexsaurus Software Inc. All rights reserved. TIFF-LZW and/or GIF-LZW: Licensed under Unisys Corporation US Patent No. 4,558,302; End-User use restricted to use on only a single personal computer or workstation which is not used as a server. -
Install Guide
THIS BOX CONTAINS: • (1) CD (your game!) • Install Guide (16 pp.) with quick installation instructions, directions for creating a floppy boot disk, configurations for a variety of memory management systems and Troubleshooting answers to possible problems. • Playguide (24 pp.) covering movement, fighting, interaction and so on. • Reference Card lists keyboard commands for a single-glance reminder. • Top Line — news brief, courtesy of the World Economic Consortium. • Anti-Terrorist Site Security — guide to keeping your WEC installation safe from armored, gun-toting turncoats and other menaces, annotated by General Maxis. • Resistance Handbook — written briefing for new rebel recruits. • Registration Card — please tell us who you are! CRUSADER: NO REMORSE ™ INSTALL GUIDE Welcome to Crusader: No Remorse. This guide includes quick installation instructions for users more familiar with the process, and a detailed, step-by- step guide to installing the game. If you experience any difficulty, consult Troubleshooting (page 9). To avoid compatibility or memory problems, please take a moment to confirm that your machine matches the System Require- ments described on page 2. Remember, you may safely stop at any time during installation and return to DOS with q, except when files are being copied. QUICK INSTALLATION Note: If you are running a disk cache such as SMARTDrive, you need to disable it to ensure a clean installation. (This only affects the installation of the game. SMARTDrive will work normally during gameplay.) Refer to your SMARTDrive documentation or make a system boot disk as described in Boot Disks (page 4) to disable this cache. 1. Turn on your computer and wait for the DOS prompt. -
Internet Explorer 9 Features
m National Institute of Information Technologies NIIT White Paper On “What is New in Internet Explorer 9” Submitted by: Md. Yusuf Hasan Student ID: S093022200027 Year: 1st Quarter: 2nd Program: M.M.S Date - 08 June 2010 Dhaka - Bangladesh Internet Explorer History Abstract: In the early 90s—the dawn of history as far as the World Wide Web is concerned—relatively few users were communicating across this Internet Explorer 9 (abbreviated as IE9) is the upcoming global network. They used an assortment of shareware and other version of the Internet Explorer web browser from software for Microsoft Windows operating system. In 1995, Microsoft Microsoft. It is currently in development, but developer hosted an Internet Strategy Day and announced its commitment to adding Internet capabilities to all its products. In fulfillment of that previews have been released. announcement, Microsoft Internet Explorer arrived as both a graphical Web browser and the name for a set of technologies. IE9 will have complete or nearly complete support for all 1995: Internet Explorer 1.0: In July 1995, Microsoft released the CSS 3 selectors, border-radius CSS 3 property, faster Windows 95 operating system, which included built-in support for JavaScript and embedded ICC v2 or v4 color profiles dial-up networking and TCP/IP (Transmission Control support via Windows Color System. IE9 will feature Protocol/Internet Protocol), key technologies for connecting to the hardware accelerated graphics rendering using Direct2D, Internet. In response to the growing public interest in the Internet, Microsoft created an add-on to the operating system called Internet hardware accelerated text rendering using Direct Write, Explorer 1.0. -
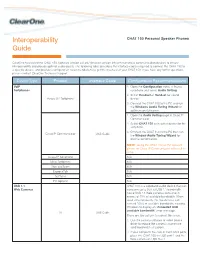
CHAT Firmware Release Notes
Interoperability CHAT 150 Personal Speaker Phones Guide ClearOne has tested the CHAT 150 (software version 2.0.28 / firmware version 39) with numerous communication devices to ensure interoperability and provide optimal audio quality. The following table describes the interface cables required to connect the CHAT 150 to a specific device, and provides configuration recommendations to get the most out of your CHAT 150. If you have any further questions, please contact ClearOne Technical Support. Device Type Product Interface Cable Configuration Recommendations VoIP 1. Open the Configuration menu in Avaya Softphones softphone and select Audio Setting. 2. Select Headset or Handset for sound Avaya SIP Softphone device. 3. Connect the CHAT 150 to the PC and run the Windows Audio Tuning Wizard for optimum performance. 1. Open the Audio Setting page in Cisco IP Communicator. 2. Select CHAT 150 as headset device for the softphone. 3. Connect the CHAT 150 to the PC then run Cisco IP Communicator USB Cable the Window Audio Tuning Wizard for optimal performance. NOTE: Using the CHAT 150 as the speaker phone for Cisco IP Communicator will result in echo. Avaya IP Softphone N/A Mirial Softphone N/A Xten eyeBeam N/A ExpressTalk N/A SJPhone N/A PC Gphone N/A USB 1.1 CHAT 150 is a wideband audio device that can Web Cameras consume up to 35% of USB 1.1 bandwidth. Some USB 1.1 Web cameras consume in excess of 75% of available bandwidth. When used simultaneously, the two devices can exceed 100% of available bandwidth, causing Windows to display an “Exceeded USB available bandwidth” error message. -

How to Cheat at Windows System Administration Using Command Line Scripts
www.dbebooks.com - Free Books & magazines 405_Script_FM.qxd 9/5/06 11:37 AM Page i How to Cheat at Windows System Administration Using Command Line Scripts Pawan K. Bhardwaj 405_Script_FM.qxd 9/5/06 11:37 AM Page ii Syngress Publishing, Inc., the author(s), and any person or firm involved in the writing, editing, or produc- tion (collectively “Makers”) of this book (“the Work”) do not guarantee or warrant the results to be obtained from the Work. There is no guarantee of any kind, expressed or implied, regarding the Work or its contents.The Work is sold AS IS and WITHOUT WARRANTY.You may have other legal rights, which vary from state to state. In no event will Makers be liable to you for damages, including any loss of profits, lost savings, or other incidental or consequential damages arising out from the Work or its contents. Because some states do not allow the exclusion or limitation of liability for consequential or incidental damages, the above limitation may not apply to you. You should always use reasonable care, including backup and other appropriate precautions, when working with computers, networks, data, and files. Syngress Media®, Syngress®,“Career Advancement Through Skill Enhancement®,”“Ask the Author UPDATE®,” and “Hack Proofing®,” are registered trademarks of Syngress Publishing, Inc.“Syngress:The Definition of a Serious Security Library”™,“Mission Critical™,” and “The Only Way to Stop a Hacker is to Think Like One™” are trademarks of Syngress Publishing, Inc. Brands and product names mentioned in this book are trademarks or service marks of their respective companies. -

Hard Configurator - Manual Version 4.1.1.1 (July 2019)
Hard_Configurator - Manual Version 4.1.1.1 (July 2019) Copyright: Andrzej Pluta, @Andy Ful Developer Web Page: https://github.com/AndyFul/Hard_Configurator/ @askalan website about Hard_Configurator: https://hard-configurator.com/ Malwaretips forum thread: https://malwaretips.com/threads/hard_configurator-windows-hardening-con- figurator.66416/ Distribution This software may be freely distributed as long as no modification is made to it. Disclaimer of Warranty THIS SOFTWARE IS DISTRIBUTED "AS IS". NO WARRANTY OF ANY KIND IS EXPRESSED OR IMPLIED. YOU USE IT AT YOUR OWN RISK. THE AUTHOR WILL NOT BE LIABLE FOR DATA LOSS, DAMAGES, LOSS OF PROFITS OR ANY OTHER KIND OF LOSS WHILE USING THIS SOFTWARE. TABLE OF CONTENTS INTRODUCTION ...................................................................... 3 INSTALLATION / DEINSTALLATION ................................... 6 SOFTWARE RESTRICTION POLICIES (SRP) ..................... 8 HOW SRP CAN CONTROL FILE EXECUTION/OPENING.. 10 WHITELISTING BY HASH ................................................... 15 WHITELISTING BY PATH .................................................... 16 WHITELIST PROFILES .......................................................... 17 DESIGNATED FILE TYPES .................................................... 19 DEFAULT SECURITY LEVELS ............................................ 20 ENFORCEMENT ...................................................................... 21 BLOCKING SPONSORS ......................................................... 23 PROTECTING ‘WINDOWS’ FOLDER ................................ -

Case Study: Internet Explorer 1994..1997
Case Study: Internet Explorer 1994..1997 Ben Slivka General Manager Windows UI [email protected] Internet Explorer Chronology 8/94 IE effort begins 12/94 License Spyglass Mosaic source code 7/95 IE 1.0 ships as Windows 95 feature 11/95 IE 2.0 ships 3/96 MS Professional Developer’s Conference AOL deal, Java license announced 8/96 IE 3.0 ships, wins all but PC Mag review 9/97 IE 4.0 ships, wins all the reviews IE Feature Chronology IE 1.0 (7/14/95) IE 2.0 (11/17/95) HTML 2.0 HTML Tables, other NS enhancements HTML <font face=> Cell background colors & images Progressive Rendering HTTP cookies (arthurbi) Windows Integration SSL Start.Run HTML (MS enhancements) Internet Shortcuts <marquee> Password Caching background sounds Auto Connect, in-line AVIs Disconnect Active VRML 1.0 Navigator parity MS innovation Feature Chronology - continued IE 3.0 (8/12/96) IE 3.0 - continued... IE 4.0 (9/12/97) Java Accessibility Dynamic HTML (W3C) HTML Frames PICS (W3C) Data Binding Floating frames HTML CSS (W3C) 2D positioning Componentized HTML <object> (W3C) Java JDK 1.1 ActiveX Scripting ActiveX Controls Explorer Bars JavaScript Code Download Active Setup VBScript Code Signing Active Channels MSHTML, SHDOCVW IEAK (corporations) CDF (XML) WININET, URLMON Internet Setup Wizard Security Zones DocObj hosting Referral Server Windows Integration Single Explorer ActiveDesktop™ Navigator parity MS innovation Quick Launch, … Wins for IE • Quality • CoolBar, Explorer Bars • Componetization • Great Mail/News Client • ActiveX Controls – Outlook Express – vs. Nav plug-ins -

United States Patent (19) 11 Patent Number: 5,987,611 Freund (45) Date of Patent: Nov
USOO5987611A United States Patent (19) 11 Patent Number: 5,987,611 Freund (45) Date of Patent: Nov. 16, 1999 54 SYSTEM AND METHODOLOGY FOR Postel, J., “RFC 821-Simple Mail Transfer Protocol.” MANAGING INTERNET ACCESS ON A PER Information Science Institute, University of Southern Cali APPLICATION BASIS FOR CLIENT fornia, Aug. 1982, pp. 1-68. COMPUTERS CONNECTED TO THE INTERNET (List continued on next page.) 75 Inventor: Gregor Freund, San Francisco, Calif. Primary Examiner Robert W. BeauSoliel, Jr. Assistant Examiner Stephen C. Elmore 73 Assignee: Zone Labs, Inc., San Francisco, Calif. Attorney, Agent, or Firm John A. Smart 21 Appl. No.: 08/851,777 57 ABSTRACT 22 Filed: May 6, 1997 A computing environment with methods for monitoring access to an open network, Such as a WAN or the Internet, Related U.S. Application Data is described. The System includes one or more clients, each 60 Provisional application No. 60/033,975, Dec. 31, 1996. operating applications or processes (e.g., Netscape Naviga torTM or Microsoft Internet ExplorerTM browser software) (51) Int. Cl." ...................................................... G06F 13/00 requiring Internet (or other open network) access (e.g., an 52 U.S. Cl. .............................................................. 713/201 Internet connection to one or more Web servers). Client 58 Field of Search ............................... 395/18701, 186; based monitoring and filtering of access is provided in 364/222.5, 286.4, 286.5; 711/163; 707/9, conjunction with a centralized enforcement Supervisor. The 10, 203; 713/200, 201 Supervisor maintains access rules for the client-based filter ing and verifies the existence and proper operation of the 56) References Cited client-based filter application. -

Planning for Internet Explorer and the IEAK
02_Inst.fm Page 15 Monday, October 16, 2000 9:40 AM TWO 2Chapter 2 Planning for Internet Explorer and the IEAK LChapter Syllabus In this chapter, we will look at material covered in the Planning section of Microsoft’s Implementing MCSE 2.1 Addressing Technical Needs, Rules, and Policies and Supporting Microsoft Internet Explorer 5 by using the Internet Explorer Administration Kit exam MCSE 2.2 Planning for Custom (70-080). After reading this chapter, you should be Installations and Settings able to: MCSE 2.3 Providing Multiple • Identify and evaluate the technical needs of business Language Support units, such as Internet Service Providers (ISPs), con- tent providers, and corporate administrators. MCSE 2.4 Providing Multiple Platform Support • Design solutions based on organizational rules and policies for ISPs, content providers, and corporate MCSE 2.5 Developing Security Strategies administrators. • Evaluate which components to include in a custom- MCSE 2.6 Configuring for Offline ized Internet Explorer installation package for a given Viewing deployment scenario. MCSE 2.7 Replacing Other Browsers • Develop appropriate security strategies for using Internet Explorer at various sites, including public MCSE 2.8 Developing CMAK kiosks, general business sites, single-task-based sites, Strategies and intranet-only sites. 15 02_Inst.fm Page 16 Monday, October 16, 2000 9:40 AM 16 Chapter 2 • Planning for Internet Explorer and the IEAK • Configure offline viewing for various types of users, including gen- eral business users, single-task users, and mobile users. • Develop strategies for replacing other Internet browsers, such as Netscape Navigator and previous versions of Internet Explorer. • Decide which custom settings to configure for Microsoft Outlook Express for a given scenario.