Zypper Cheat Sheet Or Type M an Zypper on a Terminal
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Getting to Grips with Unix and the Linux Family
Getting to grips with Unix and the Linux family David Chiappini, Giulio Pasqualetti, Tommaso Redaelli Torino, International Conference of Physics Students August 10, 2017 According to the booklet At this end of this session, you can expect: • To have an overview of the history of computer science • To understand the general functioning and similarities of Unix-like systems • To be able to distinguish the features of different Linux distributions • To be able to use basic Linux commands • To know how to build your own operating system • To hack the NSA • To produce the worst software bug EVER According to the booklet update At this end of this session, you can expect: • To have an overview of the history of computer science • To understand the general functioning and similarities of Unix-like systems • To be able to distinguish the features of different Linux distributions • To be able to use basic Linux commands • To know how to build your own operating system • To hack the NSA • To produce the worst software bug EVER A first data analysis with the shell, sed & awk an interactive workshop 1 at the beginning, there was UNIX... 2 ...then there was GNU 3 getting hands dirty common commands wait till you see piping 4 regular expressions 5 sed 6 awk 7 challenge time What's UNIX • Bell Labs was a really cool place to be in the 60s-70s • UNIX was a OS developed by Bell labs • they used C, which was also developed there • UNIX became the de facto standard on how to make an OS UNIX Philosophy • Write programs that do one thing and do it well. -
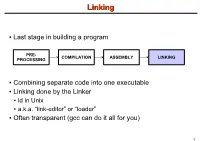
Linking + Libraries
LinkingLinking ● Last stage in building a program PRE- COMPILATION ASSEMBLY LINKING PROCESSING ● Combining separate code into one executable ● Linking done by the Linker ● ld in Unix ● a.k.a. “link-editor” or “loader” ● Often transparent (gcc can do it all for you) 1 LinkingLinking involves...involves... ● Combining several object modules (the .o files corresponding to .c files) into one file ● Resolving external references to variables and functions ● Producing an executable file (if no errors) file1.c file1.o file2.c gcc file2.o Linker Executable fileN.c fileN.o Header files External references 2 LinkingLinking withwith ExternalExternal ReferencesReferences file1.c file2.c int count; #include <stdio.h> void display(void); Compiler extern int count; int main(void) void display(void) { file1.o file2.o { count = 10; with placeholders printf(“%d”,count); display(); } return 0; Linker } ● file1.o has placeholder for display() ● file2.o has placeholder for count ● object modules are relocatable ● addresses are relative offsets from top of file 3 LibrariesLibraries ● Definition: ● a file containing functions that can be referenced externally by a C program ● Purpose: ● easy access to functions used repeatedly ● promote code modularity and re-use ● reduce source and executable file size 4 LibrariesLibraries ● Static (Archive) ● libname.a on Unix; name.lib on DOS/Windows ● Only modules with referenced code linked when compiling ● unlike .o files ● Linker copies function from library into executable file ● Update to library requires recompiling program 5 LibrariesLibraries ● Dynamic (Shared Object or Dynamic Link Library) ● libname.so on Unix; name.dll on DOS/Windows ● Referenced code not copied into executable ● Loaded in memory at run time ● Smaller executable size ● Can update library without recompiling program ● Drawback: slightly slower program startup 6 LibrariesLibraries ● Linking a static library libpepsi.a /* crave source file */ … gcc .. -

AR400 User Guide 2.7.1
AR400 SERIES User Guide Software Release 2.7.1 AR410 AR440S AR441S AR450S AR400 Series Router User Guide for Software Release 2.7.1 Document Number C613-02021-00 REV F. Copyright © 2004 Allied Telesyn International Corp. 19800 North Creek Parkway, Suite 200, Bothell, WA 98011, USA. All rights reserved. No part of this publication may be reproduced without prior written permission from Allied Telesyn. Allied Telesyn International Corp. reserves the right to make changes in specifications and other information contained in this document without prior written notice. The information provided herein is subject to change without notice. In no event shall Allied Telesyn be liable for any incidental, special, indirect, or consequential damages whatsoever, including but not limited to lost profits, arising out of or related to this manual or the information contained herein, even if Allied Telesyn has been advised of, known, or should have known, the possibility of such damages. All trademarks are the property of their respective owner. Contents CHAPTER 1 Introduction Why Read this User Guide? ............................................................................... 7 Where To Find More Information ...................................................................... 8 The Documentation Set .............................................................................. 8 Technical support .............................................................................................. 9 Features of the Router ..................................................................................... -

An User & Developer Perspective on Immutable Oses
An User & Developer Perspective on Dario Faggioli Virtualization SW. Eng. @ SUSE Immutable OSes [email protected] dariof @DarioFaggioli https://dariofaggioli.wordpress.com/ https://about.me/dario.faggioli About Me What I do ● Virtualization Specialist Sw. Eng. @ SUSE since 2018, working on Xen, KVM, QEMU, mostly about performance related stuff ● Daily activities ⇒ how and what for I use my workstation ○ Read and send emails (Evolution, git-send-email, stg mail, ...) ○ Write, build & test code (Xen, KVM, Libvirt, QEMU) ○ Work with the Open Build Service (OBS) ○ Browse Web ○ Test OSes in VMs ○ Meetings / Video calls / Online conferences ○ Chat, work and personal ○ Some 3D Printing ○ Occasionally play games ○ Occasional video-editing ○ Maybe scan / print some document 2 ● Can all of the above be done with an immutable OS ? Immutable OS: What ? Either: ● An OS that you cannot modify Or, at least: ● An OS that you will have an hard time modifying What do you mean “modify” ? ● E.g., installing packages ● ⇒ An OS on which you cannot install packages ● ⇒ An OS on which you will have an hard time installing packages 3 Immutable OS: What ? Seriously? 4 Immutable OS: Why ? Because it will stay clean and hard to break ● Does this sound familiar? ○ Let’s install foo, and it’s dependency, libfoobar_1 ○ Let’s install bar (depends from libfoobar_1, we have it already) ○ Actually, let’s add an external repo. It has libfoobar_2 that makes foo work better! ○ Oh no... libfoobar_2 would break bar!! ● Yeah. It happens. Even in the best families distros -

The Linux Command Line
The Linux Command Line Fifth Internet Edition William Shotts A LinuxCommand.org Book Copyright ©2008-2019, William E. Shotts, Jr. This work is licensed under the Creative Commons Attribution-Noncommercial-No De- rivative Works 3.0 United States License. To view a copy of this license, visit the link above or send a letter to Creative Commons, PO Box 1866, Mountain View, CA 94042. A version of this book is also available in printed form, published by No Starch Press. Copies may be purchased wherever fine books are sold. No Starch Press also offers elec- tronic formats for popular e-readers. They can be reached at: https://www.nostarch.com. Linux® is the registered trademark of Linus Torvalds. All other trademarks belong to their respective owners. This book is part of the LinuxCommand.org project, a site for Linux education and advo- cacy devoted to helping users of legacy operating systems migrate into the future. You may contact the LinuxCommand.org project at http://linuxcommand.org. Release History Version Date Description 19.01A January 28, 2019 Fifth Internet Edition (Corrected TOC) 19.01 January 17, 2019 Fifth Internet Edition. 17.10 October 19, 2017 Fourth Internet Edition. 16.07 July 28, 2016 Third Internet Edition. 13.07 July 6, 2013 Second Internet Edition. 09.12 December 14, 2009 First Internet Edition. Table of Contents Introduction....................................................................................................xvi Why Use the Command Line?......................................................................................xvi -

The BIG Change for Opensuse Leap 15.3 About Me
The BIG Change for openSUSE Leap 15.3 About Me openSUSE Manager Hobbies ● Marketing/PR ● Fantasy Sports ● Event Organizer ● Mining ● Coordinate Event ● Series Binge Watcher Sponsorship Interesting Fact Education Christopher Reeve was ● MBA - Business to blame for me breaking my arm ● BA - Education Douglas DeMaio (Superman 1978) V International GNU Health Conference - Nov. 20 - 21, online event - #GHCon2020 The Way to openSUSE Leap 15.3 bout Me !losing the Leap Gap What is it & why does it matter. Jump 15.&.1 Leap 15.3 The efforts to change What to expect with in how a distribution is coming releases of this built openSUSE distribution What is openSUSE Leap Leap is trying to bridge “Community and Enterprise” the distribution is based on the latest version of SUSE Linux Enterprise available to the date, typically with a 12 months release cycle. Leap 15.2 Retrospective told us that users value most the installer, stability, seamless migrations, and YaST. These would be then our strengths according to users! The distribution is often profiled as the more stable one and easy to use as there should be no radical or disruptive changes in between minor updates. Some users say It’s the KDE distribution. Box says “The Linux Distribution for Beginners and Pros” !"osing the Leap Gap ● CtLG is a SUSE driven effort to bring Leap closer to SUSE Linux Enterprise than ever before. This brings quite some challenges but also open some new opportunities. ● Unification of openSUSE Leap and SUSE Linux Enterprise 15 code streams and feature set. ● Concept of building a community distribution by combining rpms from openSUSE Backports (community part) and SUSE signed SLE rpms (Enterprise part). -

BASIC UNIX COMMANDS FILES and DIRECTORIES All Information Is Stored in files
BASIC UNIX COMMANDS FILES AND DIRECTORIES All information is stored in files. File names and COMMANDS commands are case sensitive. Case matters. Files Commands are what you type at the prompt. Com- are contained in directories. You start out in your mands have arguments on which they operate. For own home directory, and your prompt usually tells example, in rm temp, the command is rm and the ar- its name. At any given time, one of these directories gument is temp; this command removes the file called is your working directory, the one you are in. temp. Here I put arguments in UPPER CASE. Thus, You can refer to files in your working directory by words such as FILE are taken to stand for some other just their names. You can refer to a file that is in a word, such as temp. In the following list, I use [ ] for subdirectory by giving a subdirectory name, a slash, optional arguments that are not typicaly used. and the file name, e.g., Mail/baron. You can refer to Commands have options that are controlled with any file on the computer by giving its full name, start- switches, which are usually letters following a single ing with a slash, such as /home7/b/baron/mbox. dash. Usually you can write several letters after one dash. For example ls -l lists files in a long format, If the file is a program, typing its name will run it. with more information. ls -a lists all the files, in- (That is what commands do.) If the program is some- cluding those that begin with ., which are usually thing you have just written and is in the director you files used by various programs. -
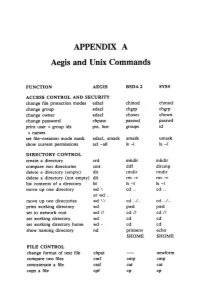
APPENDIX a Aegis and Unix Commands
APPENDIX A Aegis and Unix Commands FUNCTION AEGIS BSD4.2 SYSS ACCESS CONTROL AND SECURITY change file protection modes edacl chmod chmod change group edacl chgrp chgrp change owner edacl chown chown change password chpass passwd passwd print user + group ids pst, lusr groups id +names set file-creation mode mask edacl, umask umask umask show current permissions acl -all Is -I Is -I DIRECTORY CONTROL create a directory crd mkdir mkdir compare two directories cmt diff dircmp delete a directory (empty) dlt rmdir rmdir delete a directory (not empty) dlt rm -r rm -r list contents of a directory ld Is -I Is -I move up one directory wd \ cd .. cd .. or wd .. move up two directories wd \\ cd . ./ .. cd . ./ .. print working directory wd pwd pwd set to network root wd II cd II cd II set working directory wd cd cd set working directory home wd- cd cd show naming directory nd printenv echo $HOME $HOME FILE CONTROL change format of text file chpat newform compare two files emf cmp cmp concatenate a file catf cat cat copy a file cpf cp cp Using and Administering an Apollo Network 265 copy std input to std output tee tee tee + files create a (symbolic) link crl In -s In -s delete a file dlf rm rm maintain an archive a ref ar ar move a file mvf mv mv dump a file dmpf od od print checksum and block- salvol -a sum sum -count of file rename a file chn mv mv search a file for a pattern fpat grep grep search or reject lines cmsrf comm comm common to 2 sorted files translate characters tic tr tr SHELL SCRIPT TOOLS condition evaluation tools existf test test -

Snort 2.9.9.X on Opensuse Leap 42.2
Snort Installation on openSUSE Leap 42.2 64 bits Boris A. Gómez Universidad Tecnológica de Panamá July 2017 About This Guide This guide has been tested on openSUSE Leap 42.2, 64 bits, using DAQ 2.0.6 and Snort 2.9.9.0. Software was installed in a virtual machine: Virtual Machine Manager: VirtualBox 5.1.22 or KVM 1.4.0 HOST operating system: Windows 7 or openSUSE Leap 42.2 GUEST operating system: openSUSE Leap 42.2 (Snort will be installed here) For clarity, the following color code was used: Orange – commands that the user types at the shell prompt. Blue – text inside of configuration files. Purple – text to focus your attention on. This guide is based on the document "Snort 2.9.8.x on OpenSuSE 13x" by William Parker. Network Card Configuration Run VirtualBox | KVM manager and configure the network section of the guest machine to bridge mode. KVM Manager: VirtualBox Manager: Guest Machine Start your guest machine and set its network interface card to a static IP, for example 192.168.99.10, then check settings: ifconfig eth0 Link encap:Ethernet HWaddr 08:00:27:50:CA:99 inet addr: 192.168.99.10 Bcast:192.168.99.255 Mask:255.255.255.0 Verify that you can access Internet by accessing a web page, for example: https://snort.org Before proceeding, it is advisable to update the system. Required Packages Use YAST to install the following packages: gcc version 4.8.x (including libraries: libgcc_s1 (5.3.1), libgcc_s1-32bit(5.3.1)) flex (2.5.37) bison (2.7) php5-zlib (5.5.14 including zlib-devel 1.2.8) libpcap1 (1.8.1 including libpcap-devel 1.8.1) (versions must match) libpcre1 (8.39 including pcre-devel 8.39 and libpcre1-32bit 8.39) (versions must match) libdnet1 (1.12 including libdnet-devel 1.12) (versions must match) tcpdump (4.5.1). -

Integrating New Major Components on Fast and Slow Moving Distributions
IntegratingIntegrating newnew majormajor componentscomponents onon fastfast andand slowslow movingmoving distributionsdistributions How latest GNOME desktop was integrated into latest SUSE / openSUSE releases Frédéric Crozat <[email protected]> SUSE Linux Enterprise Release Manager What we don’t do What we do DistributionDistribution deliverydelivery stylesstyles 4 Three distributions styles ● Rolling: – Bleeding edge – Release as soon as possible – Example: openSUSE Tumbleweed, ArchLinux, Gentoo ● Regular: – Release one to twice a year – Update their entire stack for each release – Example: Ubuntu, Fedora, Debian ● LTS / Enterprise: – Slow cadence (yearly or even less than that) – Very few things move between sub-releases – Example: openSUSE Leap, Ubuntu LTS, SLES/SLED, RHEL 5 openSUSE/SUSE terminology ● OBS = OpenBuildService ● SLE = SUSE Linux Enterprise (Server / Desktop) – Enterprise distribution, developed by SUSE ● openSUSE Tumbleweed: – openSUSE Rolling release, by openSUSE, using only Factory packages, tested by openQA ● openSUSE Factory: – Development repository for Tumbleweed ● openSUSE Leap: – openSUSE Stable release, based on SLE common code + Packages from Factory (or specific repository) 6 IntegrationIntegration processprocess 7 OBS and Devel project ● On OBS, every source package is handled in a project which can build several packages together ● openSUSE Tumbleweed uses devel project per “topic” (KDE, GNOME, X11, …) ● Changes (patch, version update) are done in Devel projects and then, pushed to “main” distribution for -

Configuration Challenges in Linux and Ecos: a Survey
GSDLAB TECHNICAL REPORT Configuration Challenges in Linux and eCos: A Survey Arnaud Hubaux, Yingfei Xiong, Krzysztof Czarnecki GSDLAB{TR 2011{09{29 September 2011 Generative Software Development Laboratory University of Waterloo 200 University Avenue West, Waterloo, Ontario, Canada N2L 3G1 WWW page: http://gsd.uwaterloo.ca/ The GSDLAB technical reports are published as a means to ensure timely dissemination of scholarly and technical work on a non-commercial basis. Copyright and all rights therein are maintained by the authors or by other copyright holders, notwithstanding that they have offered their works here electronically. It is understood that all persons copying this information will adhere to the terms and constraints invoked by each author's copyright. These works may not be reposted without the explicit permission of the copyright holder. Configuration Challenges in Linux and eCos: A Survey Arnaud Hubaux, Yingfei Xiong, Krzysztof Czarnecki September 29, 2011 Abstract Operating systems expose sophisticated configurability to handle vari- ations in hardware platforms like desktops, servers, and mobile devices. The configuration of an operating system like Linux contains thousands of options guarded by hundreds of complex constraints. To guide users throughout the configuration activity, configurators implement various mechanisms to produce correct configurations. However, configuration still remains a difficult and challenging process. To better understand the challenges faced by users during configuration, we conducted surveys among Linux and eCos users to answer the two following questions: • What challenges do users most frequently face? • How significant is the conflict resolution problem? In this paper, we report on the results of these two surveys. 1 Linux This section focuses on the configuration tools used for the Linux kernel. -
Differential Response: a Primer for Child Welfare Professionals
FACTSHEETS | OCTOBER 2020 Differential Response: A Primer for Child Welfare Professionals Recognizing that a one-size-fits-all approach WHAT'S INSIDE does not serve children and families well, many agencies have implemented differential response Overview (DR), a system reform that establishes multiple pathways to respond to child maltreatment reports. DR routes families with a screened- Approaches to implementing differential response in report of child maltreatment through a traditional investigation pathway or an alternative assessment response pathway, depending on Differential response in the field other State policies and program requirements. Rather than initiating an investigation every time a family has a screened-in report, DR practice Conclusion seeks to assess a family's needs and connect them with services that will help them keep their References children safe. By linking families with services that will strengthen their ability to safely care for their children, DR can reduce the number of children entering foster care and decrease future involvement with the child welfare system. This factsheet provides child welfare professionals with an overview of DR and considerations for practice. Children's Bureau/ACYF/ACF/HHS | 800.394.3366 | Email: [email protected] | https://www.childwelfare.gov 1 OVERVIEW Both pathways share underlying principles and goals, including a focus on child safety, DR—also called alternative response, family permanency, and well-being, and include assessment response, multiple response, child safety and/or risk assessments. The or dual track—is a way of structuring child pathway assignment for a family could change protective services (CPS) to allow for more based on new information, such as potential flexibility in how it responds to low- and criminal behavior or imminent danger of moderate-risk cases and better meet the maltreatment.