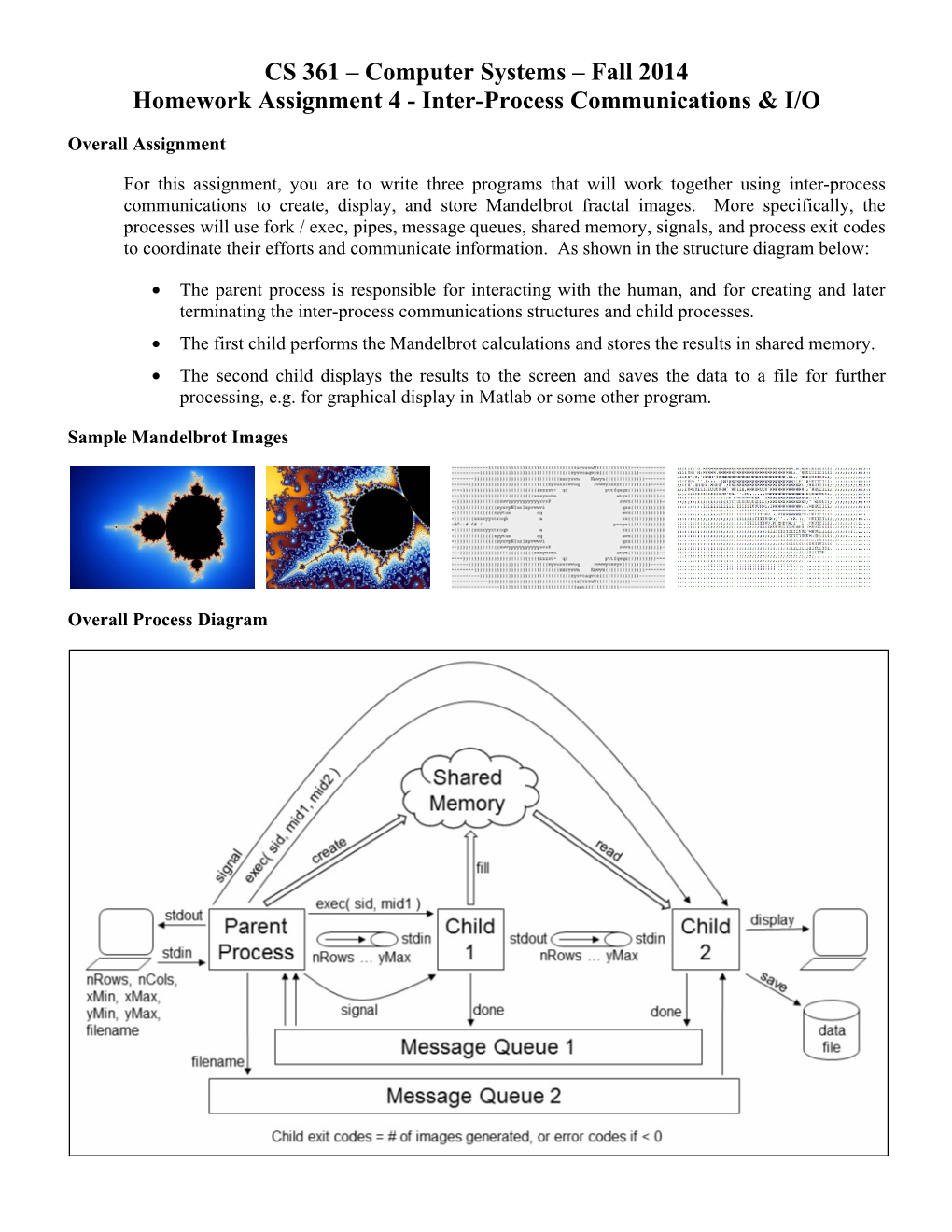
CS 361 – Computer Systems – Fall 2014 Homework Assignment 4 - Inter-Process Communications & I/O
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Administering Unidata on UNIX Platforms
C:\Program Files\Adobe\FrameMaker8\UniData 7.2\7.2rebranded\ADMINUNIX\ADMINUNIXTITLE.fm March 5, 2010 1:34 pm Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta UniData Administering UniData on UNIX Platforms UDT-720-ADMU-1 C:\Program Files\Adobe\FrameMaker8\UniData 7.2\7.2rebranded\ADMINUNIX\ADMINUNIXTITLE.fm March 5, 2010 1:34 pm Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Notices Edition Publication date: July, 2008 Book number: UDT-720-ADMU-1 Product version: UniData 7.2 Copyright © Rocket Software, Inc. 1988-2010. All Rights Reserved. Trademarks The following trademarks appear in this publication: Trademark Trademark Owner Rocket Software™ Rocket Software, Inc. Dynamic Connect® Rocket Software, Inc. RedBack® Rocket Software, Inc. SystemBuilder™ Rocket Software, Inc. UniData® Rocket Software, Inc. UniVerse™ Rocket Software, Inc. U2™ Rocket Software, Inc. U2.NET™ Rocket Software, Inc. U2 Web Development Environment™ Rocket Software, Inc. wIntegrate® Rocket Software, Inc. Microsoft® .NET Microsoft Corporation Microsoft® Office Excel®, Outlook®, Word Microsoft Corporation Windows® Microsoft Corporation Windows® 7 Microsoft Corporation Windows Vista® Microsoft Corporation Java™ and all Java-based trademarks and logos Sun Microsystems, Inc. UNIX® X/Open Company Limited ii SB/XA Getting Started The above trademarks are property of the specified companies in the United States, other countries, or both. All other products or services mentioned in this document may be covered by the trademarks, service marks, or product names as designated by the companies who own or market them. License agreement This software and the associated documentation are proprietary and confidential to Rocket Software, Inc., are furnished under license, and may be used and copied only in accordance with the terms of such license and with the inclusion of the copyright notice. -

Cygwin User's Guide
Cygwin User’s Guide Cygwin User’s Guide ii Copyright © Cygwin authors Permission is granted to make and distribute verbatim copies of this documentation provided the copyright notice and this per- mission notice are preserved on all copies. Permission is granted to copy and distribute modified versions of this documentation under the conditions for verbatim copying, provided that the entire resulting derived work is distributed under the terms of a permission notice identical to this one. Permission is granted to copy and distribute translations of this documentation into another language, under the above conditions for modified versions, except that this permission notice may be stated in a translation approved by the Free Software Foundation. Cygwin User’s Guide iii Contents 1 Cygwin Overview 1 1.1 What is it? . .1 1.2 Quick Start Guide for those more experienced with Windows . .1 1.3 Quick Start Guide for those more experienced with UNIX . .1 1.4 Are the Cygwin tools free software? . .2 1.5 A brief history of the Cygwin project . .2 1.6 Highlights of Cygwin Functionality . .3 1.6.1 Introduction . .3 1.6.2 Permissions and Security . .3 1.6.3 File Access . .3 1.6.4 Text Mode vs. Binary Mode . .4 1.6.5 ANSI C Library . .4 1.6.6 Process Creation . .5 1.6.6.1 Problems with process creation . .5 1.6.7 Signals . .6 1.6.8 Sockets . .6 1.6.9 Select . .7 1.7 What’s new and what changed in Cygwin . .7 1.7.1 What’s new and what changed in 3.2 . -

Linux from Scratch
Linux From Scratch Version 3.3 Gerard Beekmans Copyright © 1999−2002 by Gerard Beekmans This book describes the process of creating a Linux system from scratch from an already installed Linux distribution, using nothing but the sources of the software that we use. Copyright (c) 1999−2002, Gerard Beekmans All rights reserved. Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: • Redistributions in any form must retain the above copyright notice, this list of conditions and the following disclaimer. • Neither the name of "Linux From Scratch" nor the names of its contributors may be used to endorse or promote products derived from this material without specific prior written permission. • Any material derived from Linux From Scratch must contain a reference to the "Linux From Scratch" project. THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS ``AS IS'' AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE REGENTS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. Dedication This book is dedicated to my loving and supportive wife Beverly Beekmans. -
![[Linux] - Unix/Linix Commands](https://docslib.b-cdn.net/cover/5564/linux-unix-linix-commands-595564.webp)
[Linux] - Unix/Linix Commands
[Linux] - Unix/Linix Commands 1. $ ssh username@servername command used to login to server 2$ pwd it prints present working directory 3$ ls -l listing the files in present directory 4$ cd..takes you to previous Dir 5$ mkdir <directory>will create directory 6$ mkdir -p /home/user1/d1/d2/d3will create all the non-existing Dir’s 7$ vi <file_name>opens file for reading/editing 8$ cat <file_name>display contents of file 9$ more <file_name>displays page by page contents of file 10$ grep <pattern> file_namechecks pattern/word in file name specified 11$ head <file_name>shows first 10 lines of file_name 12$ touch <file_name>creates a zero/dummy file 13$ ln file1 file2 creates link of file1 to file2 14$ cp <file1> <file2>Copy a file 15$ mv <file1> <file2>Move/rename a file or folder 16$ clearclears the scree 17$ whoDisplays logged in user to the system. 18$ file <file_name>shows what type of file it is like 19$wwill display more info abt the users logged in 20$ ps -efshows process 21$ which <file_name>shows if the file_name/command exists and if exists display the path 22$ rm <file_name>will delete file specified$ rm * Delete all the files in the present directory (BE CAREFUL WHILE GIVING THIS COMMAND) 23$ find . -type f -print -exec grep -i <type_ur_text_here> {} \;this is recursive grep$ find / - name <file_name> -print 24$ tail <file_name>shows last 10 lines of fileuse tail -f for continous update of file_name 25$ chmod 777 <file_name>changes file_name/directory permissions use –R switch for recursive 26$ chown owner:group <file_name>changes -

CICS and IPCS
CICS and IPCS Andre Clark Staff CICS L2 Support Agenda § Dump types § Some basic IPCS commands § CICS Verbexit DFHPDxxx § Common System Area (CSA) § Storage Manager (SM) § Transaction Manager (XM) § Dispatcher (DS) § Kernel (KE) § Loader domain (LD) § Program domain (PG) § Lock Manager (LM) § Enqueue domain (NQ) § Application domain (AP) § Task Summary (TK) § Trace (TR) 3 IPCS Primary Menu ------------------- IPCS PRIMARY OPTION MENU --------------------------------- OPTION ===> ******************** 0 DEFAULTS - Specify default dump and options * USERID - USASSC1 1 BROWSE - Browse dump data set * 2 ANALYSIS - Analyze dump contents * 3 UTILITY - Perform utility functions * TIME - 16:46 4 INVENTORY - Inventory of problem data * PREFIX - USASSC1 5 SUBMIT - Submit problem analysis job to batch * TERMINAL- 3278 6 COMMAND - Enter subcommand, CLIST or REXX exec * PF KEYS - 24 T TUTORIAL - Learn how to use the IPCS dialog ******************** X EXIT - Terminate using log and list defaults Enter END command to terminate IPCS dialog F1=HELP F2=SPLIT F3=END F4=RETURN F5=RFIND F6=MORE F7=UP F8=DOWN F9=SWAP F10=LEFT F11=RIGHT F12=CURSOR 4 IPCS Default Menu ------------------------- IPCS Default Values --------------------------------- Command ===> You may change any of the defaults listed below. The defaults shown before any changes are LOCAL. Change scope to GLOBAL to display global defaults. Scope ==> BOTH (LOCAL, GLOBAL, or BOTH) If you change the Source default, IPCS will display the current default Address Space for the new source and will ignore any data entered in the Address Space field. Source ==> DSNAME('USASSC1.SHAREFC.DUMP') Address Space ==> ASID(X'0044') Message Routing ==> NOPRINT TERMINAL Message Control ==> FLAG(WARNING) NOCONFIRM VERIFY Display Content ==> MACHINE REMARK REQUEST NOSTORAGE SYMBOL Press ENTER to update defaults. -

Using IPCS with MVS/ESA Version 5
SYSTEM BY TOM BRYANT STRATEGIES MVS/XA/ESA Problem Solving: Part I — Using IPCS With MVS/ESA Version 5 PCS for MVS/ESA Version 5 has come a long way since I first used it in 1983 at the prompting of an exuberant IBM customer engineer. IPCS IPCS for MVS/ESA continues to move toward a fully panel-driven environment, although in Version 5 offers many Isome situations, I find using IPCS commands easier. capabilities, including the ability to scan for unformatted storage dumps. This article Future articles will examine the environ- easily in batch mode as well as in an ISPF mental record editing and printing program foreground session. I also wanted a CLIST examines the many (EREP), one-page MVS/XA/ESA abend that was well-documented with easy-to-use facilities of IPCS, analysis, advanced SVCDUMP analysis, parameters. Finally, I wanted a CLIST that slip traps and GTF tracing, and standalone does not hang onto dump directory and IPCS and includes some dump analysis. print dataset allocations when completed, as of the author’s favorite IPCS stands for Interactive Problem the IBM BLSCDDIR CLIST does. Control System, although most people IPCS commands. (myself included) use it just for looking at IPCS CLISTS FOR MVS/ESA unformatted storage dumps. IPCS will process VERSION 4.3 AND ABOVE SVCDUMPs which are dumps usually pro- The #IPCSTJB CLIST is the mainline duced with the abend (SVC 13) issued by your CLIST that you execute to establish an IPCS program or the system. Other unformatted session (see Figure 1). If you are invoking dumps that IPCS will produce include an #IPCSTJB for the first time, the NEW CLIST application unformatted dump allocated keyword parameter indicates that you will through the SYSMDUMP DD statement and dynamically create a VSAM dump directory the standalone dump produced by the stand- using the value of the VOL CLIST keyword alone dump program. -

Operating System Lab Manual
OPERATING SYSTEM LAB MANUAL BASICS OF UNIX COMMANDS Ex.No:1.a INTRODUCTION TO UNIX AIM: To study about the basics of UNIX UNIX: It is a multi-user operating system. Developed at AT & T Bell Industries, USA in 1969. Ken Thomson along with Dennis Ritchie developed it from MULTICS (Multiplexed Information and Computing Service) OS. By1980, UNIX had been completely rewritten using C langua ge. LINUX: It is similar to UNIX, which is created by Linus Torualds. All UNIX commands works in Linux. Linux is a open source software. The main feature of Linux is coexisting with other OS such as windows and UNIX. STRUCTURE OF A LINUXSYSTEM: It consists of three parts. a)UNIX kernel b) Shells c) Tools and Applications UNIX KERNEL: Kernel is the core of the UNIX OS. It controls all tasks, schedule all Processes and carries out all the functions of OS. Decides when one programs tops and another starts. SHELL: Shell is the command interpreter in the UNIX OS. It accepts command from the user and analyses and interprets them 1 | P a g e BASICS OF UNIX COMMANDS Ex.No:1.b BASIC UNIX COMMANDS AIM: To study of Basic UNIX Commands and various UNIX editors such as vi, ed, ex and EMACS. CONTENT: Note: Syn->Syntax a) date –used to check the date and time Syn:$date Format Purpose Example Result +%m To display only month $date+%m 06 +%h To display month name $date+%h June +%d To display day of month $date+%d O1 +%y To display last two digits of years $date+%y 09 +%H To display hours $date+%H 10 +%M To display minutes $date+%M 45 +%S To display seconds $date+%S 55 b) cal –used to display the calendar Syn:$cal 2 2009 c)echo –used to print the message on the screen. -
17555: Lab: Z/OS Debugging IPCS Hands-On
1177555555:: LLaabb:: zz//OOSS DDeebbuuggggiinngg IIPPCCSS HHaannddss--oonn LLaabb WWeeddnneessddaayy,, AAuugguusstt 1122 1122::3300 PPMM JJoohhnn CC.. SShheebbeeyy IIIIII IIBBMM PPoouugghhkkeeeeppssiiee jjsshheebbeeyy@@uuss..iibbmm..ccoomm PPaattrriicciiaa LLiittttllee IIBBMM PPoouugghhkkeeeeppssiiee pplliittttllee@@uuss..iibbmm..ccoomm © 2015 IBM Corporation Lab Agenda Introduction o How the Lab is Presented …………………… 2 o Downloading Dumps via FTP ……………….. 3 o Related Sessions …………………………….. 3 o Lab Setup Instructions ……………………….. 4 Lab Exercises o Dump of Hung Job ………………………….. 5-6 o Dump of Looping Job…..…………………….. 7-8 o ABEND0C1 Dump …………………................9-11 o ABEND0C4 Dump .........................................12-14 Answers to Lab Exercises .......................... 15-25 Appendix o IPCS Option 1 - BROWSE Mode ………..…. 27 o IP ST REGS …………………………………... 28 o IP SYSTRACE ………………………………... 29 How the Lab is Presented Self-Paced o Be warned there is a lot of material in this lab. You may not finish in the time allotted. o '**' on page title indicates exercises on that page. Each exercise details commands to be entered. This lab session lets you experiment with some of the IPCS commands and displays discussed in lecture session 17907. Please refer to lecture session 17907 for sample command display output. SHARE Session 17555 2 © 2015 IBM Corporation Downloading Dumps via FTP ALL 4 data sets used in today's lab are available for FTP download. Download from TESTCASE.BOULDER.IBM.COM, login as ANONYMOUS, and use your complete E-MAIL address as the password. Files are in BINARY format in the ‘fromibm/mvs’ directory. Filenames are ‘share.s17555.dumpN.trs.bin’ (N is 1 - 4; filenames are lower case). All files are in tersed format, so will need to be untersed after download. -

Harmonization Project Document No. 4
This report contains the collective views of an international group of experts and does not necessarily represent the decisions or the stated policy of the World Health Organization, the International Labour Organization, or the United Nations Environment Programme. Harmonization Project Document No. 4 PART 1: IPCS FRAMEWORK FOR ANALYSING THE RELEVANCE OF A CANCER MODE OF ACTION FOR HUMANS AND CASE-STUDIES PART 2: IPCS FRAMEWORK FOR ANALYSING THE RELEVANCE OF A NON-CANCER MODE OF ACTION FOR HUMANS This project was conducted within the IPCS project on the Harmonization of Approaches to the Assessment of Risk from Exposure to Chemicals. Published under the joint sponsorship of the World Health Organization, the International Labour Organization, and the United Nations Environment Programme, and produced within the framework of the Inter-Organization Programme for the Sound Management of Chemicals. The International Programme on Chemical Safety (IPCS), established in 1980, is a joint venture of the United Nations Environment Programme (UNEP), the International Labour Organization (ILO), and the World Health Organization (WHO). The overall objectives of the IPCS are to establish the scientific basis for assessment of the risk to human health and the environment from exposure to chemicals, through international peer review processes, as a prerequisite for the promotion of chemical safety, and to provide technical assistance in strengthening national capacities for the sound management of chemicals. The Inter-Organization Programme for the Sound Management of Chemicals (IOMC) was established in 1995 by UNEP, ILO, the Food and Agriculture Organization of the United Nations, WHO, the United Nations Industrial Development Organization, the United Nations Institute for Training and Research, and the Organisation for Economic Co-operation and Development (Participating Organizations), following recommendations made by the 1992 UN Conference on Environment and Development to strengthen cooperation and increase coordination in the field of chemical safety. -

Session 12C3 a Simplified Interface for Concurrent Processing
Session 12c3 A Simplified Interface for Concurrent Processing Janet D. Hartman Applied Computer Science Department Illinois State University Normal, IL 61704 Abstract - Teaching the concepts of concurrency is a task library of C functions, the Parallel Library, that can be used requiring an understanding of how the operating system to introduce the concepts of shared memory multiprocessing allocates resources for the processes and how concurrent and message passing, but hide the details of the actual processes may share data. The difficulty of trying to system calls used to implement them. These functions can understand the asynchronous execution behavior of be used to introduce students to the ideas associated with processes is compounded by the need to understand the concurrent processing in many courses, even at the syntax and required parameters for making the system introductory level. The functions are based on the System calls. Providing wrappers for system calls that make more V UNIX system calls for generating processes and intuitive function calls to allocate and manage resources allocating and managing interprocess communication, but can help students understand the issues involved with could easily be modified for similar POSIX functions. shared memory multiprocessing and message passing systems without having to understand the details of the The Parallel Library syntax associated with making the system calls. This paper describes a library of C functions, the Parallel Library, that The Parallel Library contains functions for creating and can be used to introduce the concepts of shared memory terminating processes along with functions for allocating multiprocessing, message passing, and related and managing interprocess communication structures synchronization issues, but hide the details of the actual (shared memory and message queues) along with functions system calls used to implement them. -

(Ipcs) User Guide Submitting Professional Medical Claims on the Medi-Cal Provider Website
INTERNET PROFESSIONAL CLAIM SUBMISSION (IPCS) USER GUIDE SUBMITTING PROFESSIONAL MEDICAL CLAIMS ON THE MEDI-CAL PROVIDER WEBSITE July 2020 INTERNET PROFESSIONAL CLAIM SUBMISSION (IPCS) USER GUIDE Contents ABOUT THIS GUIDE .......................................................................................................................................... 1 ABOUT IPCS ................................................................................................................................................... 1 Questions................................................................................................................................................... 1 Minimum System Requirements ............................................................................................................... 2 Before You Start – IPCS Access Requirements ....................................................................................... 2 CONNECTING TO THE MEDI-CAL PROVIDER WEBSITE TO ACCESS THE IPCS APPLICATION .................................. 3 ENTERING A NEW CLAIM .................................................................................................................................. 5 IPCS Application Tips ................................................................................................................................ 5 Required Fields ......................................................................................................................................... 6 Removing Data from a Tab ...................................................................................................................... -

The Unix/Linux Library for Semaphore and Shared Memory Manipulation Programmed by B
The Unix/Linux Library for Semaphore and Shared Memory Manipulation Programmed by B. Chandrasekara (February 2002) and updated by E. Talagrand and J. Brinkmeier (January 2004) 1. Introduction This library provides a set of functional calls (based on Unix/Linux system calls) for semaphore definitions and operations on semaphores and for a shared memory definition and shared memory access. Download from Carmen Cse2431 at Files into your directory the following files: ssem.h, ssem.c, sshm.h and sshm.c. Then obtain ssem.o and sshm.o using the following compilation commands: gcc –o ssem.o –c ssem.c gcc –o sshm.o –c sshm.c For a program that uses semaphores and a shared memory, the header files ssem.h and sshm.h have to be included into the source code as follows: #include "ssem.h" #include "sshm.h" and the following compilation commands is to be used: gcc –o program program.c ssem.o sshm.o When semaphores or sheared memories are not used in the given program, sem.o or sshm.o, respectively, may be omitted from the above commands. 2. Semaphore Definition and Operations a. int sem_create(int key, int initial_value) This function creates a new semaphore and returns a positive integer (but only if successful). The positive integer is a semaphore identifier to be used in other semaphore functions. The parameter key has to contain a unique value, and a six digit integer is recommended. The parameter initial_value should contain the initial value for the semaphore. b. int sem_open(int key) This function opens an existing semaphore and it returns a positive integer (but only if successful).