Half-Double”: Next-Row-Over Assisted Rowhammer Abstract 2
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Microkernel Mechanisms for Improving the Trustworthiness of Commodity Hardware
Microkernel Mechanisms for Improving the Trustworthiness of Commodity Hardware Yanyan Shen Submitted in fulfilment of the requirements for the degree of Doctor of Philosophy School of Computer Science and Engineering Faculty of Engineering March 2019 Thesis/Dissertation Sheet Surname/Family Name : Shen Given Name/s : Yanyan Abbreviation for degree as give in the University calendar : PhD Faculty : Faculty of Engineering School : School of Computer Science and Engineering Microkernel Mechanisms for Improving the Trustworthiness of Commodity Thesis Title : Hardware Abstract 350 words maximum: (PLEASE TYPE) The thesis presents microkernel-based software-implemented mechanisms for improving the trustworthiness of computer systems based on commercial off-the-shelf (COTS) hardware that can malfunction when the hardware is impacted by transient hardware faults. The hardware anomalies, if undetected, can cause data corruptions, system crashes, and security vulnerabilities, significantly undermining system dependability. Specifically, we adopt the single event upset (SEU) fault model and address transient CPU or memory faults. We take advantage of the functional correctness and isolation guarantee provided by the formally verified seL4 microkernel and hardware redundancy provided by multicore processors, design the redundant co-execution (RCoE) architecture that replicates a whole software system (including the microkernel) onto different CPU cores, and implement two variants, loosely-coupled redundant co-execution (LC-RCoE) and closely-coupled redundant co-execution (CC-RCoE), for the ARM and x86 architectures. RCoE treats each replica of the software system as a state machine and ensures that the replicas start from the same initial state, observe consistent inputs, perform equivalent state transitions, and thus produce consistent outputs during error-free executions. -

SMASH: Synchronized Many-Sided Rowhammer Attacks from Javascript
SMASH: Synchronized Many-sided Rowhammer Attacks from JavaScript Finn de Ridder Pietro Frigo Emanuele Vannacci Herbert Bos ETH Zurich VU Amsterdam VU Amsterdam VU Amsterdam VU Amsterdam Cristiano Giuffrida Kaveh Razavi VU Amsterdam ETH Zurich Abstract has instead been lagging behind. In particular, rather than Despite their in-DRAM Target Row Refresh (TRR) mitiga- addressing the root cause of the Rowhammer bug, DDR4 in- tions, some of the most recent DDR4 modules are still vul- troduced a mitigation known as Target Row Refresh (TRR). nerable to many-sided Rowhammer bit flips. While these TRR, however, has already been shown to be ineffective bit flips are exploitable from native code, triggering them against many-sided Rowhammer attacks from native code, in the browser from JavaScript faces three nontrivial chal- at least in its current in-DRAM form [12]. However, it is lenges. First, given the lack of cache flushing instructions in unclear whether TRR’s failing also re-exposes end users to JavaScript, existing eviction-based Rowhammer attacks are TRR-aware, JavaScript-based Rowhammer attacks from the already slow for the older single- or double-sided variants browser. In fact, existing many-sided Rowhammer attacks and thus not always effective. With many-sided Rowhammer, require frequent cache flushes, large physically-contiguous mounting effective attacks is even more challenging, as it re- regions, and certain access patterns to bypass in-DRAM TRR, quires the eviction of many different aggressor addresses from all challenging in JavaScript. the CPU caches. Second, the most effective many-sided vari- In this paper, we show that under realistic assumptions, it ants, known as n-sided, require large physically-contiguous is indeed possible to bypass TRR directly from JavaScript, memory regions which are not available in JavaScript. -

Drammer: Deterministic Rowhammer Attacks on Mobile Platforms
Drammer: Deterministic Rowhammer Attacks on Mobile Platforms Victor van der Veen Yanick Fratantonio Martina Lindorfer Vrije Universiteit Amsterdam UC Santa Barbara UC Santa Barbara [email protected] [email protected] [email protected] Daniel Gruss Clémentine Maurice Giovanni Vigna Graz University of Technology Graz University of Technology UC Santa Barbara [email protected] [email protected] [email protected] Herbert Bos Kaveh Razavi Cristiano Giuffrida Vrije Universiteit Amsterdam Vrije Universiteit Amsterdam Vrije Universiteit Amsterdam [email protected] [email protected] [email protected] ABSTRACT 1. INTRODUCTION Recent work shows that the Rowhammer hardware bug can The Rowhammer hardware bug allows an attacker to mod- be used to craft powerful attacks and completely subvert a ify memory without accessing it, simply by repeatedly ac- system. However, existing efforts either describe probabilis- cessing, i.e., \hammering", a given physical memory loca- tic (and thus unreliable) attacks or rely on special (and often tion until a bit in an adjacent location flips. Rowhammer unavailable) memory management features to place victim has been used to craft powerful attacks that bypass all cur- objects in vulnerable physical memory locations. Moreover, rent defenses and completely subvert a system [16,32,35,47]. prior work only targets x86 and researchers have openly won- Until now, the proposed exploitation techniques are either dered whether Rowhammer attacks on other architectures, probabilistic [16,35] or rely on special memory management such as ARM, are even possible. features such as memory deduplication [32], MMU paravir- We show that deterministic Rowhammer attacks are feasi- tualization [47], or the pagemap interface [35]. -

Throwhammer: Rowhammer Attacks Over the Network and Defenses
Throwhammer: Rowhammer Attacks over the Network and Defenses Andrei Tatar Radhesh Krishnan Konoth Elias Athanasopoulos VU Amsterdam VU Amsterdam University of Cyprus Cristiano Giuffrida Herbert Bos Kaveh Razavi VU Amsterdam VU Amsterdam VU Amsterdam Abstract never progressed beyond local privilege escalations or sandbox escapes. The attacker needs the ability to run Increasingly sophisticated Rowhammer exploits allow an code on the victim machine in order to flip bits in sen- attacker that can execute code on a vulnerable system sitive data. Hence, Rowhammer posed little threat from to escalate privileges and compromise browsers, clouds, attackers without code execution on the victim machines. and mobile systems. In all these attacks, the common In this paper, we show that this is no longer true and at- assumption is that attackers first need to obtain code tackers can flip bits by only sending network packets to execution on the victim machine to be able to exploit a victim machine connected to RDMA-enabled networks Rowhammer either by having (unprivileged) code exe- commonly used in clouds and data centers [1, 20, 45, 62]. cution on the victim machine or by luring the victim to a website that employs a malicious JavaScript applica- Rowhammer exploits today Rowhammer allows at- tion. In this paper, we revisit this assumption and show tackers to flip a bit in one physical memory location that an attacker can trigger and exploit Rowhammer bit by aggressively reading (or writing) other locations (i.e., flips directly from a remote machine by only sending hammering). As bit flips occur at the physical level, they network packets. -

Can Microkernels Mitigate Microarchitectural Attacks?⋆
Can Microkernels Mitigate Microarchitectural Attacks?? Gunnar Grimsdal1, Patrik Lundgren2, Christian Vestlund3, Felipe Boeira1, and Mikael Asplund1[0000−0003−1916−3398] 1 Department of Computer and Information Science, Link¨oping University, Sweden ffelipe.boeira,[email protected] 2 Westermo Network Technologies [email protected] 3 Sectra AB, Link¨oping,Sweden Abstract. Microarchitectural attacks such as Meltdown and Spectre have attracted much attention recently. In this paper we study how effec- tive these attacks are on the Genode microkernel framework using three different kernels, Okl4, Nova, and Linux. We try to answer the question whether the strict process separation provided by Genode combined with security-oriented kernels such as Okl4 and Nova can mitigate microar- chitectural attacks. We evaluate the attack effectiveness by measuring the throughput of data transfer that violates the security properties of the system. Our results show that the underlying side-channel attack Flush+Reload used in both Meltdown and Spectre, is effective on all in- vestigated platforms. We were also able to achieve high throughput using the Spectre attack, but we were not able to show any effective Meltdown attack on Okl4 or Nova. Keywords: Genode, Meltdown, Spectre, Flush+Reload, Okl4, Nova 1 Introduction It used to be the case that general-purpose operating systems were mostly found in desktop computers and servers. However, as IoT devices are becoming in- creasingly more sophisticated, they tend more and more to require a powerful operating system such as Linux, since otherwise all basic services must be im- plemented and maintained by the device developers. At the same time, security has become a prime concern both in IoT and in the cloud domain. -
Throwhammer: Rowhammer Attacks Over the Network and Defenses
Throwhammer: Rowhammer Attacks over the Network and Defenses Andrei Tatar and Radhesh Krishnan Konoth, Vrije Universiteit Amsterdam; Elias Athanasopoulos, University of Cyprus; Cristiano Giuffrida, Herbert Bos, and Kaveh Razavi, Vrije Universiteit Amsterdam https://www.usenix.org/conference/atc18/presentation/tatar This paper is included in the Proceedings of the 2018 USENIX Annual Technical Conference (USENIX ATC ’18). July 11–13, 2018 • Boston, MA, USA ISBN 978-1-939133-02-1 Open access to the Proceedings of the 2018 USENIX Annual Technical Conference is sponsored by USENIX. Throwhammer: Rowhammer Attacks over the Network and Defenses Andrei Tatar Radhesh Krishnan Konoth Elias Athanasopoulos VU Amsterdam VU Amsterdam University of Cyprus Cristiano Giuffrida Herbert Bos Kaveh Razavi VU Amsterdam VU Amsterdam VU Amsterdam Abstract never progressed beyond local privilege escalations or sandbox escapes. The attacker needs the ability to run Increasingly sophisticated Rowhammer exploits allow an code on the victim machine in order to flip bits in sen- attacker that can execute code on a vulnerable system sitive data. Hence, Rowhammer posed little threat from to escalate privileges and compromise browsers, clouds, attackers without code execution on the victim machines. and mobile systems. In all these attacks, the common In this paper, we show that this is no longer true and at- assumption is that attackers first need to obtain code tackers can flip bits by only sending network packets to execution on the victim machine to be able to exploit a victim machine connected to RDMA-enabled networks Rowhammer either by having (unprivileged) code exe- commonly used in clouds and data centers [1, 20, 45, 62]. -

Row Hammer Exploit in Cloud Environment
Iowa State University Capstones, Theses and Creative Components Dissertations Fall 2018 Row hammer exploit in cloud environment Adithya Venkataraman Iowa State University Follow this and additional works at: https://lib.dr.iastate.edu/creativecomponents Part of the Computer and Systems Architecture Commons Recommended Citation Venkataraman, Adithya, "Row hammer exploit in cloud environment" (2018). Creative Components. 113. https://lib.dr.iastate.edu/creativecomponents/113 This Creative Component is brought to you for free and open access by the Iowa State University Capstones, Theses and Dissertations at Iowa State University Digital Repository. It has been accepted for inclusion in Creative Components by an authorized administrator of Iowa State University Digital Repository. For more information, please contact [email protected]. Row hammer exploit in c loud environment by Adithya Venkataraman A report submitted to the graduate faculty in partial fulfillment of the requirements for the degree of MASTER OF SCIENCE Major: Electrical and Computer Engineering Program of Study Committee: Akhilesh Tyagi, Major Professor The student author, whose presentation of the scholarship herein was approved by the program of study committee, is solely responsible for the content of this thesis. The Graduate College will ensure this dissertation is globally accessible and will not permit alterations after a degree is conferred. Iowa State University Ames, Iowa 2018 Copyright © Adithya Venkataraman, 2018. All rights reserved. ii TABLE OF CONTENTS Page -

Quantifying Rowhammer Vulnerability for DRAM Security
Quantifying Rowhammer Vulnerability for DRAM Security Yichen Jiang∗x, Huifeng Zhuyx, Dean Sullivan∗, Xiaolong Guoz, Xuan Zhangy and Yier Jin∗ ∗University of Florida, yWashington University in St. Louis, zKansas State University yichen.jiang@ufl.edu, [email protected], deanms@ufl.edu, [email protected], [email protected], [email protected]fl.edu Abstract—Rowhammer is a memory-based attack that leverages attack and evaluate cells’ susceptibility of being leaked during such capacitive-coupling to induce faults in modern dynamic random-access an attack. In our model, the equivalent resistance of intrinsic leakage memory (DRAM). Over the last decade, a significant number of Rowham- (denoted as R ) describes the retention time of the DRAM cells mer attacks have been presented to reveal that it is a severe security issue L capable of causing privilege escalations, launching distributed denial- storage capacitor. The equivalent resistance of capacitive coupling of-service (DDoS) attacks, and even runtime attack such as control leakage (denoted as RSW ) represents the DRAM cells resistance flow hijacking. Moreover, the Rowhammer vulnerability has also been to repeated aggressor row activations. We experimentally determine identified and validated in both cloud computing and data center these model parameters and how they can be used to characterize a environments, threatening data security and privacy at a large scale. Various solutions have been proposed to counter Rowhammer attacks DRAM’s resilience against Rowhammer attacks. To the best of our but existing methods lack a circuit-level explanation of the capacitive- knowledge, this is the first work to quantify the relationship between coupling phenomenon in modern DRAMs, the key cause of Rowhammer DRAM data retention and counts of aggressor row activations. -

OS-Level Attacks and Defenses: from Software to Hardware-Based Exploits © December 2018 by David Gens Phd Referees: Prof
OS-LEVELATTACKSANDDEFENSES: FROMSOFTWARETOHARDWARE-BASEDEXPLOITS Dissertation zur Erlangung des akademischen Grades Doktor der Ingenieurswissenschaften (Dr.-Ing.) genehmigt durch den Fachbereich Informatik (FB 20) der Technischen Universtität Darmstadt von D AV I D G E N S aus Wiesbaden, Deutschland Gutachter: Prof. Dr.-Ing. Ahmad-Reza Sadeghi (Erstreferent) Prof. Dr. Thorsten Holz (Zweitreferent) Tag der Einreichung: 14. Dezember 2018 Tag der Disputation: 13. Februar 2019 CYSEC/System Security Lab Intel Collaborative Research Institute (ICRI-CARS) Fachbereich für Informatik Technische Universität Darmstadt Hochschulkennziffer: D17 OS-level Attacks and Defenses: from Software to Hardware-based Exploits © December 2018 by David Gens phd referees: Prof. Dr.-Ing. Ahmad-Reza Sadeghi (1st PhD Referee) Prof. Dr. Thorsten Holz (2nd PhD Referee) further phd commission members: Prof. Dr. Sebastian Faust Prof. Dr. Guido Salvaneschi Prof. Dr.-Ing. Thomas Schneider Darmstadt, Germany December 2018 Veröffentlichung unter CC-BY-SA 4.0 International https://creativecommons.org/licenses/ ABSTRACT Run-time attacks have plagued computer systems for more than three decades, with control-flow hijacking attacks such as return-oriented programming repre- senting the long-standing state-of-the-art in memory-corruption based exploits. These attacks exploit memory-corruption vulnerabilities in widely deployed soft- ware, e.g., through malicious inputs, to gain full control over the platform remotely at run time, and many defenses have been proposed and thoroughly studied in the past. Among those defenses, control-flow integrity emerged as a powerful and ef- fective protection against code-reuse attacks in practice. As a result, we now start to see attackers shifting their focus towards novel techniques through a number of increasingly sophisticated attacks that combine software and hardware vulnerabil- ities to construct successful exploits. -

Mithril: Cooperative Row Hammer Protection on Commodity DRAM Leveraging Managed Refresh
Mithril: Cooperative Row Hammer Protection on Commodity DRAM Leveraging Managed Refresh Michael Jaemin Kim, Jaehyun Park, Yeonhong Park, Wanju Doh, Namhoon Kim, Tae Jun Ham, Jae W. Lee, and Jung Ho Ahn Seoul National University [email protected] Abstract—Since its public introduction in the mid-2010s, the computer system. RH-induced bit-flip can be abused in various Row Hammer (RH) phenomenon has drawn significant attention attack scenarios. For example, the RH can be utilized to from the research community due to its security implications. modify an unauthorized memory location or enable other Although many RH-protection schemes have been proposed by processor vendors, DRAM manufacturers, and academia, they attack techniques such as privilege escalation and cross-VM still have shortcomings. Solutions implemented in the memory attacks [1], [11], [12], [17], [41], [49], [53]. controller (MC) pay an increasingly higher cost due to their The criticality of this problem motivated many RH protec- conservative design for the worst case in terms of the number tion solutions. There exist several software-based solutions [5], of DRAM banks and RH threshold to support. Meanwhile, the [9], [19], [30], [49], but such solutions often incur a high- DRAM-side implementation has a limited time margin for RH protection measures or requires extensive modifications to the performance cost and have limited coverage (i.e., only ef- standard DRAM interface. fective against a specific attack scenario). For these reasons, Recently, a new command for RH protection has been intro- architectural solutions have emerged as promising alternatives. duced in the DDR5/LPDDR5 standards, called refresh manage- By providing the RH mitigation at the DRAM device level, ment (RFM). -

Rowhammer Attacks: a Walkthrough Guide
Rowhammer Attacks: A Walkthrough Guide Daniel Gruss & Clementine´ Maurice, Graz University of Technology May 4, 2017 — RuhrSec 2017 www.tugraz.at Who are we Daniel Gruss PhD student @ Graz University Of Technology 7 @lavados R [email protected] Daniel Gruss & Clementine´ Maurice, Graz University of Technology 2 May 4, 2017 — RuhrSec 2017 www.tugraz.at Who are we Clementine´ Maurice PhD in computer science, Postdoc @ Graz University Of Technology 7 @BloodyTangerine R [email protected] Daniel Gruss & Clementine´ Maurice, Graz University of Technology 3 May 4, 2017 — RuhrSec 2017 www.tugraz.at Goals of this talk you get a comprehensive overview of Rowhammer attacks you can run the tools on your machine you understand what’s happening and why ! nothing here is black magic! Daniel Gruss & Clementine´ Maurice, Graz University of Technology 4 May 4, 2017 — RuhrSec 2017 www.tugraz.at Outline Background How to flip bits? How to exploit them? How to mitigate them? Conclusion Daniel Gruss & Clementine´ Maurice, Graz University of Technology 5 May 4, 2017 — RuhrSec 2017 www.tugraz.at 1. Background Daniel Gruss & Clementine´ Maurice, Graz University of Technology 6 May 4, 2017 — RuhrSec 2017 back of DIMM: rank1 channel0 front of DIMM: rank0 chip channel1 www.tugraz.at DRAM organization Daniel Gruss & Clementine´ Maurice, Graz University of Technology 7 May 4, 2017 — RuhrSec 2017 back of DIMM: rank1 front of DIMM: rank0 chip www.tugraz.at DRAM organization channel0 channel1 Daniel Gruss & Clementine´ Maurice, Graz University -
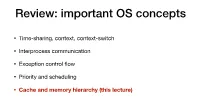
Cache & Memory Hierarchy
Review: important OS concepts • Time-sharing, context, context-switch • Interprocess communication • Exception control flow • Priority and scheduling • Cache and memory hierarchy (this lecture) Cache & Memory Hierarchy Recall our abstraction: CPU + memory CPU Address Content #ffffffff 8bits Register1 CPU has a number of registers. … Memory is a two-column table. … Register2 #00000002 8bits #00000001 8bits (More registers) #00000000 8bits Recall our abstraction: CPU + memory CPU Address Content load instruction #ffffffff 8bits Register1 … store instruction … Register2 #00000002 8bits Load and store cost constant time. #00000001 8bits (More registers) #00000000 8bits Why cache in the middle? CPU Address Content Cache #ffffffff byte Register1 … Cache is faster than memory. … Register2 Memory has larger capacity #00000002 byte than cache. #00000001 byte (More registers) Memory is cheaper than cache in terms of $/byte. #00000000 byte What to learn about cache? CPU Address Content Cache #ffffffff 8bits Register1 … What is the interface of a cache? … Register2 What is the structure of a cache? #00000002 8bits #00000001 8bits (More registers) #00000000 8bits Write-through and Write-back cache • Write-through and write-back are two types of cache. • You are going to implement both in P3. • The general structure is a 3-columnCache table. Cache Address Content In use? Addr1 8bits Yes a cache line or cache entry ???? ???? NO … Read in Write-back and Write-through CPU Cache Address Content Address Content In use? #ffffffff 8bits Register1 read load … … Register2 #00000002