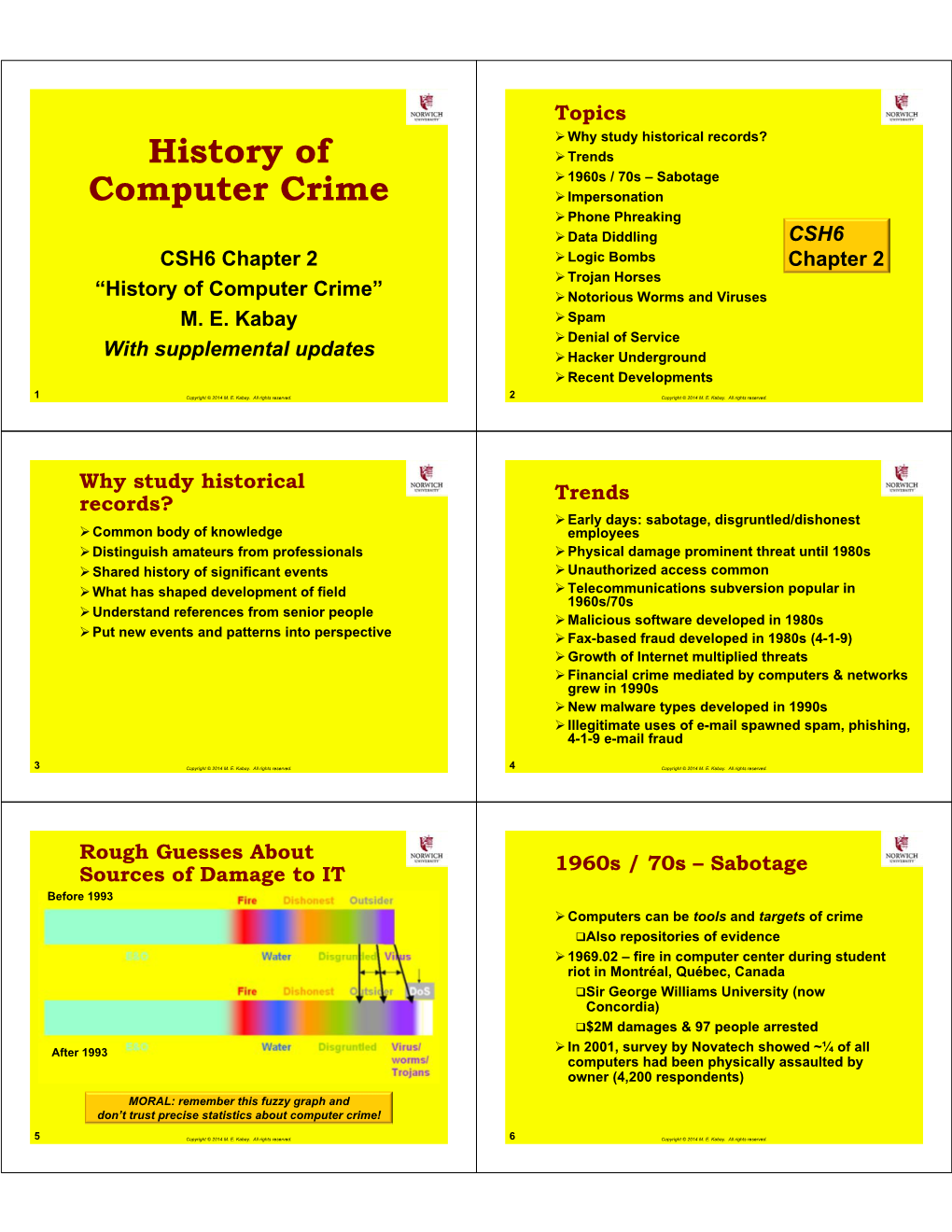
History of Computer Crime” Notorious Worms and Viruses M
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Ethical Hacking
International Journal of Scientific & Engineering Research, Volume 8, Issue 4, April-2017 ISSN 2229-5518 92 Ethical Hacking N.Vinodh Kumar, J.Arun Kumar ABSTRACT Ethical hacking and ethical hacker are terms used to describe hacking performed by a company or individual to help identify potential threats on a computer or network. An ethical hacker attempts to bypass system security and search for any weak points that could be exploited by malicious hackers. This information is then used by the organization to improve the system security, in an effort to minimize or eliminate any potential attacks. Types of hacking; Website Hacking, Network Hacking, Email Hacking, Ethical Hacking Password Hacking, Computer Hacking. Hackers type; White hat hackers, Black hat hackers, Grey hat hackers, miscellaneous hackers, Red hat hacker. Keywords- Ethical hacking, Website hacking, Network hacking —————————— —————————— Security Strategy for Predictive Systems' Global Integrity consulting practice, ethical hacking has continued to grow ETHICAL HACKING in an otherwise lackluster IT industry, and is becoming increasingly common outside the government and Ethical hacking is one of the certified any hacking to the technology sectors where it began. Many large companies, computer to important files to hacking. Hacking refers to an such as IBM, maintain employee teams of ethical hackers. array of activities which are done to intrude some one else’s personal information space so as to use it for malicious, FAMOUS HACKERS IN HISTORY unwanted purposes.Hacking is a term used to refer to activities aimed at exploiting security flaws to obtain IAN MURPHY critical information for gaining access to secured networks. KEVIN MITNICK JOHAN HELSINGUIS WEBSITE HACKING LINUS TORVALDS MARK ABENE Hacking a website means taking control from the website ROBERT MORRIES owner to a person who hackers the website. -
Lezione 2 Cenni Storici Sviluppo Di Software Sicuro (9 CFU), LM Informatica, A
Lezione 2 Cenni storici Sviluppo di software sicuro (9 CFU), LM Informatica, ! ! 2"2"#2"2$ Dipartimento di Scienze Fisic&e, Informatiche e Matematiche Universit' di Modena e Re))io *milia http+##we,la,!ing!unimore!it/people#andreolini#didattica#sviluppo-software-sicuro 1 Quote of t&e da/ (Meditate, )ente, meditate!!!) “If history repeats itself, and the unexpected always happens, how incapable must Man be of learning from experience.” 0eor)e Bernard S&aw (1234 – 193") Scrittore, drammatur)o, lin)uista, critico musicale utore de “Il Pigmalione8 2 Sir John mbrose Fleming (12:9-$9:3) (;he electrical en)ineer and ph/sicist) Inventore, in)e)nere, radiotecnico, elettrotecnico! Inventore del diodo e della valvola termoionica! Consulente (fra le altre) della Marconi <ireless ;ele)rap& Compan/! 3 Jo&n Nevil Mas>el/ne ($2?9-$9$@) (;he ma)ician) Mago. Inventore del ,agno pu,,lico 6a )ettone8! Fondatore del 6Comitato Occulto8 (antesi)nano dellBodierno CIC 7)! 1903: Mas>elyne rovina una dimostrazione pu,,lica del tele)rafo 6sicuro8 senza Cli (svolta da Flemin))! (iesce ad inviare insulti in codice Morse!.. 4 Eni)ma (1924) (;&e encr/ption#decr/ption machine) Macc&ina elettro-meccanica usata per cifrare e decifrare messa))i! Usata dalla <e&rmac&t durante la Seconda Guerra Mondiale! Considerata indecifrabile per lun)o tempo! 5 rthur Scher,ius (12@2-$929) (LBinventore di *nigma) In)e)nere tedesco! 1918: ,revetta Eni)ma (macc&ina cifrante ,asata su rotori)! 1926: la Marina Militare tedesca adotta una variante di Eni)ma per le sue comunicazioni cifrate! 6 LBEnigma militare (LBinventore di *nigma) Uso di un pannello di controllo ag)iuntivo (detto 6plu),oard”) per offuscare ulteriormente il processo di cifratura. -

PC Magazine Fighting Spyware Viruses And
01_577697 ffirs.qxd 12/7/04 11:49 PM Page i PC Magazine® Fighting Spyware, Viruses, and Malware Ed Tittel TEAM LinG - Live, Informative, Non-cost and Genuine ! 01_577697 ffirs.qxd 12/7/04 11:49 PM Page ii PC Magazine® Fighting Spyware, Viruses, and Malware Published by Wiley Publishing, Inc. 10475 Crosspoint Boulevard Indianapolis, IN 46256-5774 www.wiley.com Copyright © 2005 by Wiley Publishing Published simultaneously in Canada ISBN: 0-7645-7769-7 Manufactured in the United States of America 10 9 8 7 6 5 4 3 2 1 1B/RW/RS/QU/IN No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means, electronic, mechanical, photocopying, recording, scanning or otherwise, except as permitted under Sections 107 or 108 of the 1976 United States Copyright Act, without either the prior written permission of the Publisher, or authorization through payment of the appropriate per-copy fee to the Copyright Clearance Center, 222 Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 646-8600. Requests to the Publisher for permission should be addressed to the Legal Department, Wiley Publishing, Inc., 10475 Crosspoint Blvd., Indianapolis, IN 46256, (317) 572-3447, fax (317) 572-4355, e-mail: [email protected]. Limit of Liability/Disclaimer of Warranty: The publisher and the author make no representations or warranties with respect to the accuracy or completeness of the contents of this work and specifically disclaim all warranties, including without limitation warranties of fitness for a particular purpose. No warranty may be created or extended by sales or promotional materials. -

Hacks, Cracks, and Crime: an Examination of the Subculture and Social Organization of Computer Hackers Thomas Jeffrey Holt University of Missouri-St
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by University of Missouri, St. Louis University of Missouri, St. Louis IRL @ UMSL Dissertations UMSL Graduate Works 11-22-2005 Hacks, Cracks, and Crime: An Examination of the Subculture and Social Organization of Computer Hackers Thomas Jeffrey Holt University of Missouri-St. Louis, [email protected] Follow this and additional works at: https://irl.umsl.edu/dissertation Part of the Criminology and Criminal Justice Commons Recommended Citation Holt, Thomas Jeffrey, "Hacks, Cracks, and Crime: An Examination of the Subculture and Social Organization of Computer Hackers" (2005). Dissertations. 616. https://irl.umsl.edu/dissertation/616 This Dissertation is brought to you for free and open access by the UMSL Graduate Works at IRL @ UMSL. It has been accepted for inclusion in Dissertations by an authorized administrator of IRL @ UMSL. For more information, please contact [email protected]. Hacks, Cracks, and Crime: An Examination of the Subculture and Social Organization of Computer Hackers by THOMAS J. HOLT M.A., Criminology and Criminal Justice, University of Missouri- St. Louis, 2003 B.A., Criminology and Criminal Justice, University of Missouri- St. Louis, 2000 A DISSERTATION Submitted to the Graduate School of the UNIVERSITY OF MISSOURI- ST. LOUIS In partial Fulfillment of the Requirements for the Degree DOCTOR OF PHILOSOPHY in Criminology and Criminal Justice August, 2005 Advisory Committee Jody Miller, Ph. D. Chairperson Scott H. Decker, Ph. D. G. David Curry, Ph. D. Vicki Sauter, Ph. D. Copyright 2005 by Thomas Jeffrey Holt All Rights Reserved Holt, Thomas, 2005, UMSL, p. -

Ethical Hacking
International Journal of Scientific and Research Publications, Volume 5, Issue 6, June 2015 1 ISSN 2250-3153 Ethical Hacking Susidharthaka Satapathy , Dr.Rasmi Ranjan Patra CSA, CPGS, OUAT, Bhubaneswar, Odisha, India Abstract- In today's world where the information damaged the target system nor steal the information, they communication technique has brought the world together there is evaluate target system security and report back to the owner one of the increase growing areas is security of network ,which about the threats found. certainly generate discussion of ETHICAL HACKING . The main reason behind the discussion of ethical hacking is insecurity of the network i.e. hacking. The need of ethical hacking is to IV. FATHER OF HACKING protect the system from the damage caused by the hackers. The In 1971, John Draper , aka captain crunch, was one of the main reason behind the study of ethical hacking is to evaluate best known early phone hacker & one of the few who can be target system security & report back to owner. This paper helps called one of the father's of hacking. to generate a brief idea of ethical hacking & all its aspects. Index Terms- Hacker, security, firewall, automated, hacked, V. IS HACKING NECESSARY crackers Hacking is not what we think , It is an art of exploring the threats in a system . Today it sounds something with negative I. INTRODUCTION shade , but it is not exactly that many professionals hack system so as to learn the deficiencies in them and to overcome from it he increasingly growth of internet has given an entrance and try to improve the system security. -

Research Paper
Section 3 – Information Systems Security & Web Technologies and Security Social Engineering: A growing threat, with diverging directions J.V.Chelleth1, S.M.Furnell1, M.Papadaki2, G.Pinkney2 and P.S.Dowland1 1 Network Research Group, University of Plymouth, Plymouth, United Kingdom 2 Symantec, Hines Meadow, St Cloud Way, Maidenhead, Berkshire, United Kingdom e-mail: [email protected] Abstract The age old problem of social engineering is still a threat that does not receive due attention. Due to the advancements in information technology and the explosion of the Internet, attackers have many more avenues to pursue social engineering attacks. Inadequate efforts to educate employees and staff about social engineering and password management, inappropriate usage of messaging systems, poor implementation and awareness of security policies, all lead to people being exposed to potential incidents. This paper talks about social engineering and the new avenues that it has diverged into; and how social engineering plays a part in assisting other attack schemes. The paper first introduces the concept of social engineering. It then looks at different attack methods that have proliferated due to the help obtained by social engineering schemes. The paper establishes that, in addition to being a technique in its own right, social engineering can also be used to assist other types of attack, including viruses and worms, phishing, and identity theft. Keywords Social Engineering, Viruses, Worms, Identity theft, Phishing 1. Introduction Typically when security is spoken of in terms of information security, it is all about having secure systems and networks; anti-virus, firewalls, Intrusion Detection Systems (IDS), etc. -

Paradise Lost , Book III, Line 18
_Paradise Lost_, book III, line 18 %%%%%%%%%%%%%%%%%%%%%%%% ++++++++++Hacker's Encyclopedia++++++++ ===========by Logik Bomb (FOA)======== <http://www.xmission.com/~ryder/hack.html> ---------------(1997- Revised Second Edition)-------- ##################V2.5################## %%%%%%%%%%%%%%%%%%%%%%%% "[W]atch where you go once you have entered here, and to whom you turn! Do not be misled by that wide and easy passage!" And my Guide [said] to him: "That is not your concern; it is his fate to enter every door. This has been willed where what is willed must be, and is not yours to question. Say no more." -Dante Alighieri _The Inferno_, 1321 Translated by John Ciardi Acknowledgments ---------------------------- Dedicated to all those who disseminate information, forbidden or otherwise. Also, I should note that a few of these entries are taken from "A Complete List of Hacker Slang and Other Things," Version 1C, by Casual, Bloodwing and Crusader; this doc started out as an unofficial update. However, I've updated, altered, expanded, re-written and otherwise torn apart the original document, so I'd be surprised if you could find any vestiges of the original file left. I think the list is very informative; it came out in 1990, though, which makes it somewhat outdated. I also got a lot of information from the works listed in my bibliography, (it's at the end, after all the quotes) as well as many miscellaneous back issues of such e-zines as _Cheap Truth _, _40Hex_, the _LOD/H Technical Journals_ and _Phrack Magazine_; and print magazines such as _Internet Underground_, _Macworld_, _Mondo 2000_, _Newsweek_, _2600: The Hacker Quarterly_, _U.S. News & World Report_, _Time_, and _Wired_; in addition to various people I've consulted. -
Tangled Web : Tales of Digital Crime from the Shadows of Cyberspace
TANGLED WEB Tales of Digital Crime from the Shadows of Cyberspace RICHARD POWER A Division of Macmillan USA 201 West 103rd Street, Indianapolis, Indiana 46290 Tangled Web: Tales of Digital Crime Associate Publisher from the Shadows of Cyberspace Tracy Dunkelberger Copyright 2000 by Que Corporation Acquisitions Editor All rights reserved. No part of this book shall be reproduced, stored in a Kathryn Purdum retrieval system, or transmitted by any means, electronic, mechanical, pho- Development Editor tocopying, recording, or otherwise, without written permission from the Hugh Vandivier publisher. No patent liability is assumed with respect to the use of the infor- mation contained herein. Although every precaution has been taken in the Managing Editor preparation of this book, the publisher and author assume no responsibility Thomas Hayes for errors or omissions. Nor is any liability assumed for damages resulting from the use of the information contained herein. Project Editor International Standard Book Number: 0-7897-2443-x Tonya Simpson Library of Congress Catalog Card Number: 00-106209 Copy Editor Printed in the United States of America Michael Dietsch First Printing: September 2000 Indexer 02 01 00 4 3 2 Erika Millen Trademarks Proofreader Benjamin Berg All terms mentioned in this book that are known to be trademarks or ser- vice marks have been appropriately capitalized. Que Corporation cannot Team Coordinator attest to the accuracy of this information. Use of a term in this book should Vicki Harding not be regarded as affecting the validity of any trademark or service mark. Design Manager Warning and Disclaimer Sandra Schroeder Every effort has been made to make this book as complete and as accurate Cover Designer as possible, but no warranty or fitness is implied. -

Fdassiff Sports Or at the Office of the Town Clerk
c • Earth was moonstruck by Apollo 20 years ago ... page 1 f J fianrhpHtpr Mpralft u Wednesday, July 19, 1989 Manchester, Conn. — A City of Village Charm Newsstand Price: 35 Cents Consumer I- ^ price rise WARSAW, Poland (AP) - The National Assembly convened to day to choose a president, and Y Gen. Wojciech Jaruzelski was moderates expected to benefit from an opposition boycott to be elected to the powerful new post. By Martin Crutsinger Reserve Board, which has been Jaruzelski’s chances also de The Associated Press concerned that the country might sports pended in part on his ability to be on the verge of another command allegiance in the com WASHINGTON - Inflation inflationary spiral. munist coalition, where some slowed in June as consumer Today’s report on consumer prices rose a modest 0.2 percent, prices, coupled with news last legislators oppose him. week that wholesale prices actu As lawmakers gathered for the the smallest advance in 16 vote, about 50 anti-Jaruzelski months, the government reported ally fell in June, provided con today. crete evidence that the spurt in 991 Main St. Manchester, CT demonstrators from the Confed prices in the early part of 1989 was eration for an Independent Po The price mcdcration reflected land rallied outside. "Jaruzelski the biggest drop in energy prices finally beginning to moderate. in more than two years and the Patrick Jackman, a Labor Must Go,” read one of their Department analyst, said price 647-9126 banners. smallest increase in food costs this year. pressures over the next several Jaruzelski, the Communist The 0.2 percent June rise in the months should moderate enough Party chief, was expected to be to keep consumer inflation for all the sole candidate for the presid Consumer Price Index, the go "central connecticuts source for sports” vernment’s primary gauge of of 1989 down at around 5 percent. -

Flexible Infections: Computer Viruses, Human Bodies, Nation-States, Evolutionary Capitalism
Science,Helmreich Technology, / Flexible Infections& Human Values Flexible Infections: Computer Viruses, Human Bodies, Nation-States, Evolutionary Capitalism Stefan Helmreich New York University This article analyzes computer security rhetoric, particularly in the United States, argu- ing that dominant cultural understandings of immunology, sexuality, legality, citizen- ship, and capitalism powerfully shape the way computer viruses are construed and com- bated. Drawing on popular and technical handbooks, articles, and Web sites, as well as on e-mail interviews with security professionals, the author explores how discussions of computer viruses lean on analogies from immunology and in the process often encode popular anxieties about AIDS. Computer security rhetoric about compromised networks also uses language reminiscent of that used to describe the “bodies” of nation-states under military threat from without and within. Such language portrays viruses using images of foreignness, illegality, and otherness. The security response to viruses advo- cates the virtues of the flexible and adaptive response—a rhetoric that depends on evolu- tionary language but also on the ideological idiom of advanced capitalism. As networked computing becomes increasingly essential to the operations of corporations, banks, government, the military, and academia, worries about computer security and about computer viruses are intensifying among the people who manage and use these networks. The end of the 1990s saw the emergence of a small industry dedicated to antivirus protection software, and one can now find on the World Wide Web a great deal of information about how viruses work, how they can be combated, and how computer users might keep up with ever-changing inventories and taxonomies of the latest viruses. -

Hacks, Leaks and Disruptions | Russian Cyber Strategies
CHAILLOT PAPER Nº 148 — October 2018 Hacks, leaks and disruptions Russian cyber strategies EDITED BY Nicu Popescu and Stanislav Secrieru WITH CONTRIBUTIONS FROM Siim Alatalu, Irina Borogan, Elena Chernenko, Sven Herpig, Oscar Jonsson, Xymena Kurowska, Jarno Limnell, Patryk Pawlak, Piret Pernik, Thomas Reinhold, Anatoly Reshetnikov, Andrei Soldatov and Jean-Baptiste Jeangène Vilmer Chaillot Papers HACKS, LEAKS AND DISRUPTIONS RUSSIAN CYBER STRATEGIES Edited by Nicu Popescu and Stanislav Secrieru CHAILLOT PAPERS October 2018 148 Disclaimer The views expressed in this Chaillot Paper are solely those of the authors and do not necessarily reflect the views of the Institute or of the European Union. European Union Institute for Security Studies Paris Director: Gustav Lindstrom © EU Institute for Security Studies, 2018. Reproduction is authorised, provided prior permission is sought from the Institute and the source is acknowledged, save where otherwise stated. Contents Executive summary 5 Introduction: Russia’s cyber prowess – where, how and what for? 9 Nicu Popescu and Stanislav Secrieru Russia’s cyber posture Russia’s approach to cyber: the best defence is a good offence 15 1 Andrei Soldatov and Irina Borogan Russia’s trolling complex at home and abroad 25 2 Xymena Kurowska and Anatoly Reshetnikov Spotting the bear: credible attribution and Russian 3 operations in cyberspace 33 Sven Herpig and Thomas Reinhold Russia’s cyber diplomacy 43 4 Elena Chernenko Case studies of Russian cyberattacks The early days of cyberattacks: 5 the cases of Estonia, -

Editorial Sommaire
www.grasco.eu Parution trimestrielle www.larevuedugrasco.eu N°8— Février 2014 gratuite EDITORIAL SOMMAIRE EDITO1 Vers une directive « investigations fi- INTERVIEW : nancières » pour lutter contre le déve- EMILE PEREZ, DIRECTEUR DE LA COOPÉRATION INTER- NATIONALE4 loppement de l’économie criminelle ? . JACQUES BARROT, MEMBRE DU CONSEIL CONSTITU- TIONNEL, ANCIEN VICE-PRÉSIDENT DE LA COMMISSION EUROPÉENNE, CHARGÉ DE JUSTICE, LIBERTÉ ET SÉCU- RITÉ8 e CEIFAC accueillera, à Strasbourg, sa seconde promotion, RAPPORTS : DESSINER LE MINISTÈRE PUBLIC DE DEMAIN, À PROPOS du 17 mars au 4 avril 2013, formée de 30 représentants des DU RAPPORT NADAL, PAR MYRIAM QUÉMÉNER9 autorités de justice/police-gendarmerie/Douanes et Rensei- L CONSTATS ET PRÉCONISATIONS : gnement des Etats membres de l’Union européenne. DU RAPPORT NORA-MINC À LA LUTTE CONTRE LA CYBERCRIMINALITÉ, PAR ANNE SOUVIRA11 Créé eu sein de l’Université de Strasbourg dans le cadre d’un parte- PHÉNOMÉNOLOGIE DE LA CRIMINOLOGIE ORGANISÉE : nariat européen, le CEIFAC vise à promouvoir, au sein des Etats LES ESCROQUERIES AUX FAUX ORDRES DE VIREMENT, membres, le développement des investigations financières et de PAR PHILIPPE PETITPREZ16 FINANCE ET CRIME : PUISSANCES, HYBRIDATIONS, l’analyse financière dans le but de mieux lutter contre le dévelop- CONVERGENCES, PAR JEAN-FRANÇOIS GAYRAUD22 pement de l’infiltration de l’économie par des flux d’argent illicite. BLANCHIMENT D’ARGENT, UN NOUVEAU FLÉAU POUR Elles doivent également permettre de déjouer les fraudes finan- LES PARIS SPORTIFS, PAR CHRISTIAN KALB ET PIM VERSCHUUREN25 cières de grande envergure considérées comme étant en partie res- LA PRODUCTION ET LE TRAFIC DE CANNABIS DANS LE ponsables de la crise économique actuelle et qui menacent de dé- SUD DES BALKANS, PAR CYRILLE BAUMGARTNER31 stabiliser les systèmes financiers à l’échelle internationale.