Secret Language Use of Criminals: Their Implications to Legislative Institutions, Police, and Public Social Practices
Total Page:16
File Type:pdf, Size:1020Kb

Load more
Recommended publications
-

Individualism, Structuralism, and Climate Change
1 2 3 Individualism, Structuralism, and Climate Change 4 5 Michael Brownstein 6 Alex Madva 7 Daniel Kelly 8 9 10 Abstract 11 12 Scholars and activists working on climate change often distinguish between “individual” and 13 “structural” approaches to decarbonization. The former concern behaviors and consumption 14 choices individual citizens can make to reduce their “personal carbon footprint” (e.g., eating less 15 meat). The latter concern institutions that shape collective action, focusing instead on state and 16 national laws, industrial policies, and international treaties. While the distinction between 17 individualism and structuralism—the latter of which we take to include “institutional”, “systemic”, 18 and “collectivist” approaches—is intuitive and ubiquitous, the two approaches are often portrayed 19 as oppositional, as if one or the other is the superior route to decarbonization. We argue instead for 20 a more symbiotic conception of structural and individual reform. 21 22 23 1. Introduction 24 Scholars and activists working on climate change often distinguish between “individual” and 25 “structural” approaches to decarbonization. The former concern behaviors and consumption 26 choices individual citizens can make to reduce their “personal carbon footprint” (e.g., eating less 27 meat). The latter concern institutions that shape collective action, focusing instead on state and 28 national laws, industrial policies, and international treaties. While the distinction between 29 individualism and structuralism—the latter of which we take to include “institutional”, “systemic”, 30 and “collectivist” approaches—is intuitive and ubiquitous, the two approaches are often portrayed 31 as oppositional, as if one or the other is the superior route to decarbonization. -

Limits on Bilingualism Revisited: Stress 'Deafness' in Simultaneous French
Cognition 114 (2010) 266–275 Contents lists available at ScienceDirect Cognition journal homepage: www.elsevier.com/locate/COGNIT Limits on bilingualism revisited: Stress ‘deafness’ in simultaneous French–Spanish bilinguals Emmanuel Dupoux a,*, Sharon Peperkamp a,b, Núria Sebastián-Gallés c a Laboratoire de Sciences Cognitives et Psycholinguistique, Ecole des Hautes Etudes en Sciences Sociales, Département d’Etudes Cognitives, Ecole Normale Supérieure, Centre National de la Recherche Scientifique, 29 Rue d’Ulm, 75005 Paris, France b Département des Sciences du Langage, Université de Paris VIII, Saint-Denis, France c Brain and Cognition Unit, Universitat Pompeu Fabra, Barcelona, Spain article info abstract Article history: We probed simultaneous French–Spanish bilinguals for the perception of Spanish lexical Received 29 September 2008 stress using three tasks, two short-term memory encoding tasks and a speeded lexical deci- Revised 30 September 2009 sion. In all three tasks, the performance of the group of simultaneous bilinguals was inter- Accepted 1 October 2009 mediate between that of native speakers of Spanish on the one hand and French late learners of Spanish on the other hand. Using a composite stress ‘deafness’ index measure computed over the results of the three tasks, we found that the performance of the simul- Keywords: taneous bilinguals is best fitted by a bimodal distribution that corresponds to a mixture of Speech perception the performance distributions of the two control groups. Correlation analyses showed that Simultaneous bilingualism Phonology the variables explaining language dominance are linked to early language exposure. These Stress findings are discussed in light of theories of language processing in bilinguals. Ó 2009 Elsevier B.V. -

Language Development Language Development
Language Development rom their very first cries, human beings communicate with the world around them. Infants communicate through sounds (crying and cooing) and through body lan- guage (pointing and other gestures). However, sometime between 8 and 18 months Fof age, a major developmental milestone occurs when infants begin to use words to speak. Words are symbolic representations; that is, when a child says “table,” we understand that the word represents the object. Language can be defined as a system of symbols that is used to communicate. Although language is used to communicate with others, we may also talk to ourselves and use words in our thinking. The words we use can influence the way we think about and understand our experiences. After defining some basic aspects of language that we use throughout the chapter, we describe some of the theories that are used to explain the amazing process by which we Language9 A system of understand and produce language. We then look at the brain’s role in processing and pro- symbols that is used to ducing language. After a description of the stages of language development—from a baby’s communicate with others or first cries through the slang used by teenagers—we look at the topic of bilingualism. We in our thinking. examine how learning to speak more than one language affects a child’s language develop- ment and how our educational system is trying to accommodate the increasing number of bilingual children in the classroom. Finally, we end the chapter with information about disorders that can interfere with children’s language development. -

Similarities and Differences Between Simultaneous and Successive Bilingual Children: Acquisition of Japanese Morphology
International Journal of Applied Linguistics & English Literature E-ISSN: 2200-3452 & P-ISSN: 2200-3592 www.ijalel.aiac.org.au Similarities and Differences between Simultaneous and Successive Bilingual Children: Acquisition of Japanese Morphology Yuki Itani-Adams1, Junko Iwasaki2, Satomi Kawaguchi3* 1ANU College of Asia & the Pacific, The Australian National University, Canberra, ACT, 2601, Australia 2School of Arts and Humanities, Edith Cowan University, 2 Bradford Street, Mt Lawley WA 6050, Australia 3School of Humanities and Communication Arts, Western Sydney University, Bullecourt Ave, Milperra NSW 2214, Australia Corresponding Author: Satomi Kawaguchi , E-mail: [email protected] ARTICLE INFO ABSTRACT Article history This paper compares the acquisition of Japanese morphology of two bilingual children who had Received: June 14, 2017 different types of exposure to Japanese language in Australia: a simultaneous bilingual child Accepted: August 14, 2017 who had exposure to both Japanese and English from birth, and a successive bilingual child Published: December 01, 2017 who did not have regular exposure to Japanese until he was six years and three months old. The comparison is carried out using Processability Theory (PT) (Pienemann 1998, 2005) as a Volume: 6 Issue: 7 common framework, and the corpus for this study consists of the naturally spoken production Special Issue on Language & Literature of these two Australian children. The results show that both children went through the same Advance access: September 2017 developmental path in their acquisition of the Japanese morphological structures, indicating that the same processing mechanisms are at work for both types of language acquisition. However, Conflicts of interest: None the results indicate that there are some differences between the two children, including the rate Funding: None of acquisition, and the kinds of verbal morphemes acquired. -
Normative Labels in Two Lexicographic Traditions
http://lexikos.journals.ac.za; https://doi.org/10.5788/30-1-1604 Normative Labels in Two Lexicographic Traditions: A Slovene–English Case Study Marjeta Vrbinc, Faculty of Arts, University of Ljubljana, Slovenia ([email protected]) Danko Šipka, School for International Letters and Cultures, Arizona State University, Tempe Campus, USA ([email protected]) and Alenka Vrbinc, School of Economics and Business, University of Ljubljana, Slovenia ([email protected]) Abstract: This article presents and discusses the findings of a study conducted with the users of Slovene and American monolingual dictionaries. The aim was to investigate how native speakers of Slovene and American English interpret select normative labels in monolingual dictionaries. The data were obtained by questionnaires developed to elicit monolingual dictionary users' attitudes toward normative labels and the effects the labels have on dictionary users. The results show that a higher level of prescriptivism in the Slovene linguistic culture is reflected in the Slovene respon- dents' perception of the labels (for example, a stronger effect of the normative labels, a higher approval for the claim about usefulness of the labels, a considerably lower general level of accep- tance for the standard language) when compared with the American respondents' perception, since the American linguistic culture tends to be more descriptive. However, users often seek answers to their linguistic questions in dictionaries, which means that they expect at least a certain degree of normativity. Therefore, a balance between descriptive and prescriptive approaches should be found, since both of them affect the users. Keywords: GENERAL MONOLINGUAL DICTIONARY, PRESCRIPTIVISM, NORMATIVITY, DESCRIPTIVISM, NORMATIVE LABELS, PRIMARY EXCLUSION LABELS, SECONDARY EXCLUSION LABELS, USE OF LABELS, USEFULNESS OF LABELS, (UN)LABELED ENTRIES Opsomming: Normatiewe etikette in twee leksikografiese tradisies: 'n Sloweens–Engelse gevallestudie. -

Part 1: Introduction to The
PREVIEW OF THE IPA HANDBOOK Handbook of the International Phonetic Association: A guide to the use of the International Phonetic Alphabet PARTI Introduction to the IPA 1. What is the International Phonetic Alphabet? The aim of the International Phonetic Association is to promote the scientific study of phonetics and the various practical applications of that science. For both these it is necessary to have a consistent way of representing the sounds of language in written form. From its foundation in 1886 the Association has been concerned to develop a system of notation which would be convenient to use, but comprehensive enough to cope with the wide variety of sounds found in the languages of the world; and to encourage the use of thjs notation as widely as possible among those concerned with language. The system is generally known as the International Phonetic Alphabet. Both the Association and its Alphabet are widely referred to by the abbreviation IPA, but here 'IPA' will be used only for the Alphabet. The IPA is based on the Roman alphabet, which has the advantage of being widely familiar, but also includes letters and additional symbols from a variety of other sources. These additions are necessary because the variety of sounds in languages is much greater than the number of letters in the Roman alphabet. The use of sequences of phonetic symbols to represent speech is known as transcription. The IPA can be used for many different purposes. For instance, it can be used as a way to show pronunciation in a dictionary, to record a language in linguistic fieldwork, to form the basis of a writing system for a language, or to annotate acoustic and other displays in the analysis of speech. -

Constructing Kallipolis: the Political Argument of Plato's Socratic Dialogues
Constructing Kallipolis: The Political Argument of Plato's Socratic Dialogues The Harvard community has made this article openly available. Please share how this access benefits you. Your story matters Citation Muller, Joe Pahl Williams. 2016. Constructing Kallipolis: The Political Argument of Plato's Socratic Dialogues. Doctoral dissertation, Harvard University, Graduate School of Arts & Sciences. Citable link http://nrs.harvard.edu/urn-3:HUL.InstRepos:33493293 Terms of Use This article was downloaded from Harvard University’s DASH repository, and is made available under the terms and conditions applicable to Other Posted Material, as set forth at http:// nrs.harvard.edu/urn-3:HUL.InstRepos:dash.current.terms-of- use#LAA Constructing Kallipolis: The Political Argument of Plato’s Socratic Dialogues A dissertation presented by Joe Pahl Williams Muller to The Department of Government in partial fulfillment of the requirements for the degree of Doctor of Philosophy in the subject of Political Science Harvard University Cambridge, Massachusetts April 2016 © 2016 Joe Pahl Williams Muller All rights reserved. Dissertation Advisors: Joe Pahl Williams Muller Professor Eric Nelson Professor Rusty Jones Constructing Kallipolis: The Political Argument of Plato’s Socratic Dialogues Abstract This dissertation examines the political argument of Plato’s Socratic dialogues. Common interpretations of these texts suggest, variously: (1) that Socrates does not offer much in the way of a political theory; (2) that Socrates does reflect on politics but ultimately rejects political in- stitutions as irrelevant to his ethical concerns; (3) that Socrates arrives at a political theory that either accepts or even celebrates free and demo- cratic political arrangements. -

Whole Language Instruction Vs. Phonics Instruction: Effect on Reading Fluency and Spelling Accuracy of First Grade Students
Whole Language Instruction vs. Phonics Instruction: Effect on Reading Fluency and Spelling Accuracy of First Grade Students Krissy Maddox Jay Feng Presentation at Georgia Educational Research Association Annual Conference, October 18, 2013. Savannah, Georgia 1 Abstract The purpose of this study is to investigate the efficacy of whole language instruction versus phonics instruction for improving reading fluency and spelling accuracy. The participants were the first grade students in the researcher’s general education classroom of a non-Title I school. Stratified sampling was used to randomly divide twenty-two participants into two instructional groups. One group was instructed using whole language principles, where the children only read words in the context of a story, without any phonics instruction. The other group was instructed using explicit phonics instruction, without a story or any contextual influence. After four weeks of treatment, results indicate that there were no statistical differences between the two literacy approaches in the effect on students’ reading fluency or spelling accuracy; however, there were notable changes in the post test results that are worth further investigation. In reading fluency, both groups improved, but the phonics group made greater gains. In spelling accuracy, the phonics group showed slight growth, while the whole language scores decreased. Overall, the phonics group demonstrated greater growth in both reading fluency and spelling accuracy. It is recommended that a literacy approach should combine phonics and whole language into one curriculum, but place greater emphasis on phonics development. 2 Introduction Literacy is the fundamental cornerstone of a student’s academic success. Without the skill of reading, children will almost certainly have limited academic, economic, social, and even emotional success in school and in later life (Pikulski, 2002). -
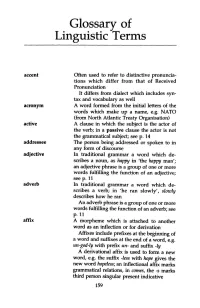
Glossary of Linguistic Terms
Glossary of Linguistic Terms accent Often used to refer to distinctive pronuncia tions which differ from that of Received Pronunciation It differs from dialect which includes syn tax and vocabulary as well acronym A word formed from the initial letters of the words which make up a name, e.g. NATO (from North Atlantic Treaty Organisation) active A clause in which the subject is the actor of the verb; in a passive clause the actor is not the grammatical subject; seep. 14 addressee The person being addressed or spoken to in any form of discourse adjective In traditional grammar a word which de scribes a noun, as happy in 'the happy man'; an adjective phrase is a group of one or more words fulfilling the function of an adjective; seep. 11 adverb In t:r:aditional grammar a word which de scribes a verb; in 'he ran slowly', slowly describes how he ran An adverb phrase is a group of one or more words fulfilling the function of an adverb; see p. 11 affix A morpheme which is attached to another word as an inflection or for derivation Affixes include prefixes at the beginning of a word and suffixes at the end of a word, e.g. un-god-ly with prefix un- and suffix -ly A derivational affix is used to form a new word, e.g. the suffix -less with hope gives the new word hopeless; an inflectional affix marks grammatical relations, in comes, the -s marks third person singular present indicative 159 160 Glossary alliteration The repetition of the same sound at the beginning of two or more words in close proximity, e.g. -
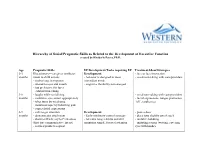
Hierarchy of Social/Pragmatic Skills As Related to the Development of Executive Function Created by Kimberly Peters, Ph.D
Hierarchy of Social/Pragmatic Skills as Related to the Development of Executive Function created by Kimberly Peters, Ph.D. Age Pragmatic Skills EF Development/Tasks requiring EF Treatment Ideas/Strategies 0-3 Illocutionary—caregiver attributes Development: - face to face interaction months intent to child actions - behavior is designed to meet - vocal-turn-taking with care-providers - smiles/coos in response immediate needs - attends to eyes and mouth - cognitive flexibility not emerged - has preference for faces - exhibits turn-taking 3-6 - laughs while socializing - vocal turn-taking with care-providers months - maintains eye contact appropriately - facial expressions: tongue protrusion, - takes turns by vocalizing “oh”, raspberries. - maintains topic by following gaze - copies facial expressions 6-9 - calls to get attention Development: - peek-a-boo months - demonstrates attachment - Early inhibitory control emerges - place toys slightly out of reach - shows self/acts coy to Peek-a-boo - tolerates longer delays and still - imitative babbling (first true communicative intent) maintains simple, focused attention - imitating actions (waving, covering - reaches/points to request eyes with hands). 9-12 - begins directing others Development: - singing/finger plays/nursery rhymes months - participates in verbal routines - Early inhibitory control emerges - routines (so big! where is baby?), - repeats actions that are laughed at - tolerates longer delays and still peek-a-boo, patta-cake, this little piggy - tries to restart play maintain simple, -

Zerohack Zer0pwn Youranonnews Yevgeniy Anikin Yes Men
Zerohack Zer0Pwn YourAnonNews Yevgeniy Anikin Yes Men YamaTough Xtreme x-Leader xenu xen0nymous www.oem.com.mx www.nytimes.com/pages/world/asia/index.html www.informador.com.mx www.futuregov.asia www.cronica.com.mx www.asiapacificsecuritymagazine.com Worm Wolfy Withdrawal* WillyFoReal Wikileaks IRC 88.80.16.13/9999 IRC Channel WikiLeaks WiiSpellWhy whitekidney Wells Fargo weed WallRoad w0rmware Vulnerability Vladislav Khorokhorin Visa Inc. Virus Virgin Islands "Viewpointe Archive Services, LLC" Versability Verizon Venezuela Vegas Vatican City USB US Trust US Bankcorp Uruguay Uran0n unusedcrayon United Kingdom UnicormCr3w unfittoprint unelected.org UndisclosedAnon Ukraine UGNazi ua_musti_1905 U.S. Bankcorp TYLER Turkey trosec113 Trojan Horse Trojan Trivette TriCk Tribalzer0 Transnistria transaction Traitor traffic court Tradecraft Trade Secrets "Total System Services, Inc." Topiary Top Secret Tom Stracener TibitXimer Thumb Drive Thomson Reuters TheWikiBoat thepeoplescause the_infecti0n The Unknowns The UnderTaker The Syrian electronic army The Jokerhack Thailand ThaCosmo th3j35t3r testeux1 TEST Telecomix TehWongZ Teddy Bigglesworth TeaMp0isoN TeamHav0k Team Ghost Shell Team Digi7al tdl4 taxes TARP tango down Tampa Tammy Shapiro Taiwan Tabu T0x1c t0wN T.A.R.P. Syrian Electronic Army syndiv Symantec Corporation Switzerland Swingers Club SWIFT Sweden Swan SwaggSec Swagg Security "SunGard Data Systems, Inc." Stuxnet Stringer Streamroller Stole* Sterlok SteelAnne st0rm SQLi Spyware Spying Spydevilz Spy Camera Sposed Spook Spoofing Splendide -

Yaron Matras
THE ROLE OF LANGUAGE IN MYSTIFYING AND DE-MYSTIFYING GYPSY IDENTITY Yaron Matras ‘Gypsy’: A double signifier No discovery has been as significant to the understanding of the history of the Gyp- sies as the illumination of their linguistic connection with India. Having said this, there arises immediately a need to clarify. For the connection between the Romani language and the languages of India has no bearing at all on the history and origin of the Irish Travellers, and probably little and only indirect significance for an under- standing of the culture of the German or Swiss Jenische, to name but two examples out of many. At the same time it is impossible to understand the Rom, Romacel, Romanichel, Sinte, Manush, or Kaale without knowing something about the origins of their language – romani chib, or romanes, or, as it is referred to in modern lin- guistics: Romani. How might we resolve this contradiction? The answer is very triv- ial: two separate signified entities are captured by the term ‘Gypsy’. GYPSY 1 denotes the social phenomenon of communities of peripatetics or com- mercial nomads, irrespective of origin or language. Whether or not the diverse communities that fall under GYPSY 1 have much in common, is the subject of occa- sional discussions among members of these groups, and of intense research among social scientists describing their cultures. Let us accept both the fact that members of these distinct groups often show interest in one another and may at times feel a sense of common destiny, while at the scientific level comparative research into diverse peripatetic communities is now an established discipline.