Pyfilesystem Documentation Release 2.4.13
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

MOAT004 1 Eprint Cs.DC/0306067 Computing in High Energy and Nuclear Physics, 24-28 March 2003, La Jolla, California Resources
Computing in High Energy and Nuclear Physics, 24-28 March 2003, La Jolla, California The AliEn system, status and perspectives P. Buncic Institut für Kernphysik, August-Euler-Str. 6, D-60486 Frankfurt, Germany and CERN, 1211, Geneva 23, Switzerland A. J. Peters, P.Saiz CERN, 1211, Geneva 23, Switzerland In preparation of the experiment at CERN's Large Hadron Collider (LHC), the ALICE collaboration has developed AliEn, a production environment that implements several components of the Grid paradigm needed to simulate, reconstruct and analyse data in a distributed way. Thanks to AliEn, the computing resources of a Virtual Organization can be seen and used as a single entity – any available node can execute jobs and access distributed datasets in a fully transparent way, wherever in the world a file or node might be. The system is built aroun d Open Source components, uses the Web Services model and standard network protocols to implement the computing platform that is currently being used to produce and analyse Monte Carlo data at over 30 sites on four continents. Several other HEP experiments as well as medical projects (EU MammoGRID, INFN GP -CALMA) have expressed their interest in AliEn or some components of it. As progress is made in the definition of Grid standards and interoperability, our aim is to interface AliEn to emerging products from both Europe and the US. In particular, it is our intention to make AliEn services compatible with the Open Grid Services Architecture (OGSA). The aim of this paper is to present the current AliEn architecture and outline its future developments in the light of emerging standards. -

Release 0.5.0 Will Mcgugan
PyFilesystem Documentation Release 0.5.0 Will McGugan Aug 09, 2017 Contents 1 Guide 3 1.1 Introduction...............................................3 1.2 Getting Started..............................................4 1.3 Concepts.................................................5 1.4 Opening Filesystems...........................................7 1.5 Filesystem Interface...........................................7 1.6 Filesystems................................................9 1.7 3rd-Party Filesystems.......................................... 10 1.8 Exposing FS objects........................................... 10 1.9 Utility Modules.............................................. 11 1.10 Command Line Applications....................................... 11 1.11 A Guide For Filesystem Implementers.................................. 14 1.12 Release Notes.............................................. 16 2 Code Documentation 17 2.1 fs.appdirfs................................................ 17 2.2 fs.base.................................................. 18 2.3 fs.browsewin............................................... 30 2.4 fs.contrib................................................. 30 2.5 fs.errors.................................................. 32 2.6 fs.expose................................................. 34 2.7 fs.filelike................................................. 40 2.8 fs.ftpfs.................................................. 42 2.9 fs.httpfs.................................................. 43 2.10 fs.memoryfs.............................................. -
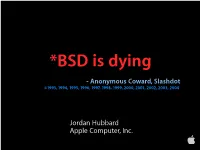
Jordan Hubbard Apple Computer, Inc. Oh Really?
*BSD is dying - Anonymous Coward, Slashdot ©1993, 1994, 1995, 1996, 1997, 1998, 1999, 2000, 2001, 2002, 2003, 2004 Jordan Hubbard Apple Computer, Inc. Oh really? Let’s look at some stats... FreeBSD Users: 2.5 Million Server Installations (Netcraft) 2,500,000 1,875,000 1,250,000 625,000 0 1993 1997 2001 2003 2004 12 Mac OS X Users: 9 6 3 0 12 Million Jul '01 Oct '01 Jan '02 Apr '02 Jul '02 Oct '02 Jan '03 Apr '03 Jun '03 Oct '03 Oct '04 Applications: FreeBSD ports 12,000 9,000 6,000 10,796 9,662 3,000 6,077 2,723 1,161 0 209 1995 1997 1999 2001 2003 2004 Applications: 12,000 Mac OS X Native 12,000 9,000 6,000 3,000 0 Apr '01 Jul '01 Oct '01 Jan '02 Apr '02 Jul '02 Oct '02 Jan '03 Apr '03 Jun '03 Oct '03 Oct '04 Since the arrival of Mac OS X, BSD has become the biggest desktop UNIX variant on the planet. Yes, even bigger than Linux Take that, Anonymous Coward! Selective overview of Mac OS X Mac OS X Architecture Applications User Interface Application Frameworks Graphics and Media System Services OS Foundation Apple Confidential OS Foundation Usermode BSD Commands and Usermode User FileSystem Libraries Drivers Kernel BSD Kernel IOKit Driver FileSystem Network Families Process Management Drivers Mach Kernel VM Scheduling IPC Open Source “Darwin” base OS Foundation Usermode BSD Commands and Usermode User FileSystem Libraries Drivers Kernel BSD Kernel IOKit Driver FileSystem Network Families Process Management Drivers Mach Kernel VM Scheduling IPC BSD Kernel • FreeBSD 5.1 based (networking, vfs, filesystems, etc) • Unified Buffer Cache (different -

Nextflow Documentation
Nextflow Documentation Release 0.30.2 Paolo Di Tommaso Jul 12, 2018 Contents 1 Get started 3 1.1 Requirements...............................................3 1.2 Installation................................................3 1.3 Your first script..............................................3 2 Basic concepts 7 2.1 Processes and channels..........................................7 2.2 Execution abstraction..........................................8 2.3 Scripting language............................................9 2.4 Configuration options..........................................9 3 Pipeline script 11 3.1 Language basics............................................. 11 3.2 Closures................................................. 14 3.3 Regular expressions........................................... 15 3.4 Files and I/O............................................... 17 4 Processes 27 4.1 Script................................................... 28 4.2 Inputs................................................... 32 4.3 Outputs.................................................. 39 4.4 When................................................... 44 4.5 Directives................................................. 44 5 Channels 63 5.1 Channel factory............................................. 63 5.2 Binding values.............................................. 67 5.3 Observing events............................................. 68 6 Operators 71 6.1 Filtering operators............................................ 71 6.2 Transforming operators........................................ -

How to Use BLM's External SFTA Temporary Account File Sharing
How to Use BLM’s External SFTA Temporary Account File Sharing The BLM’s External SFTA Temporary Account File Sharing allows BLM staff and external partners to share files through the Secure File Transfer Application (SFTA). The BLM staff member must request permissions, establish a folder, and sponsor their external partner’s account. Once an account is established, the external partner may upload, download and manage files in the specified temporary folder. After your BLM Partner has created a Temporary File Sharing Folder account associated with your email address, you will receive two emails. The first email will come from the SFTA Application with the Subject “SFTA External Temp Account Details: - PROD Env” and includes a link to the BLM Application Secure System (BASS) authentication system, your External UserId (User name) and the name of your external Get/Put file sharing folder: Subject: SFTA External Temp Account Details: - PROD Env The second email will come from the BLM Application Secure System (BASS) authentication system with the Subject “Your Temporary BASS Password”. This email will include your User name and temporary BASS password. Subject: Your Temporary BASS Password Updated December 16, 2020 To access SFTA, use these credentials to log into the BLM Application Secure System (BASS) located at: http://www.bass.blm.gov/bass2/ It is recommended that you cut & paste your temporary BASS password from the email message you received into the Password field in the login form. Click the Login button to login to BASS. On your first login, you will be asked to create a new strong password. -

Vmware Dynamic Environment Manager Administration Guide
VMware Dynamic Environment Manager Administration Guide VMware Dynamic Environment Manager 9.9 VMware Dynamic Environment Manager Administration Guide You can find the most up-to-date technical documentation on the VMware website at: https://docs.vmware.com/ If you have comments about this documentation, submit your feedback to [email protected] VMware, Inc. 3401 Hillview Ave. Palo Alto, CA 94304 www.vmware.com © Copyright 2019 VMware, Inc. All rights reserved. Copyright and trademark information. VMware, Inc. 2 Contents 1 About VMware Dynamic Environment Manager™ Administration Guide 7 2 Using Easy Start 8 3 Configuring Application and Windows Settings 9 Flex Configuration Files 10 Download Configuration Templates 10 Create a Flex Configuration File by Using Application Profiler 11 Create a Flex Configuration File by Using an Application Template 12 Create a Flex Configuration File by Using Windows Common Settings 13 Import a Flex Configuration File From Another Location or Environment 14 Export a Flex Configuration File to Another Location or Environment 15 Create a Custom Flex Configuration File 15 Configuring Settings for Storing and Retrieving Profile Information 15 Section Headers 16 Wildcard Support in Exclude Section Headers 17 Folder Tokens 17 Profile Browsing 18 Using the Advanced Tab 18 Using the User Environment Tab 19 Using the Information Tab 22 Manage Selected Windows Common Settings and Application Templates 22 Retiring, Deleting, and Disabling Flex Configuration Files 23 Retire a Flex Configuration File 23 Delete a Flex Configuration File 23 Disable a Flex Configuration File 24 Using the Profile Cleanup Editor 24 Create Profile Cleanup Content, Based on Import/Export Settings 25 Configuring Predefined Settings for Applications and Windows Settings 26 Create Predefined Settings 26 Import Predefined Settings 26 Use Multiple Predefined Settings 27 Working with Placeholders 27 Using DirectFlex 28 Configure Applications for Working with DirectFlex 29 Application Virtualization Support 29 Importing and Exporting DirectFlex Settings 29 VMware, Inc. -

Creating User-Mode Device Drivers with a Proxy Galen C
Creating User-Mode Device Drivers with a Proxy Galen C. Hunt [email protected] Department of Computer Science University of Rochester Rochester, NY 14627-0226 Abstract Writing device drivers is complicated because drivers operate as kernel-mode programs. Device drivers have Writing Windows NT device drivers can be a daunting limited access to other OS services and must be task. Device drivers must be fully re-entrant, must use conscious of kernel paging demands. Debugging only limited resources and must be created with special kernel-mode device drivers normally requires two development environments. Executing device drivers machines: one for the driver and another for the in user-mode offers significant coding advantages. debugger. User-mode device drivers have access to all user-mode libraries and applications. They can be developed using Device drivers run in kernel mode to optimize system standard development tools and debugged on a single performance. Kernel-mode device drivers have full machine. Using the Proxy Driver to retrieve I/O access to hardware resources and the data of user-mode requests from the kernel, user-mode drivers can export programs. From kernel mode, device drivers can full device services to the kernel and applications. exploit operations such as DMA and page sharing to User-mode device drivers offer enormous flexibility for transfer data directly into application address spaces. emulating devices and experimenting with new file Device drivers are placed in the kernel to minimize the systems. Experimental results show that in many number of times the CPU must cross the user/kernel cases, the overhead of moving to user-mode for boundary. -

File Organization and Management Com 214 Pdf
File organization and management com 214 pdf Continue 1 1 UNESCO-NIGERIA TECHNICAL - VOCATIONAL EDUCATION REVITALISATION PROJECT-PHASE II NATIONAL DIPLOMA IN COMPUTER TECHNOLOGY FILE Organization AND MANAGEMENT YEAR II- SE MESTER I THEORY Version 1: December 2 2 Content Table WEEK 1 File Concepts... 6 Bit:... 7 Binary figure... 8 Representation... 9 Transmission... 9 Storage... 9 Storage unit... 9 Abbreviation and symbol More than one bit, trit, dontcare, what? RfC on trivial bits Alternative Words WEEK 2 WEEK 3 Identification and File File System Aspects of File Systems File Names Metadata Hierarchical File Systems Means Secure Access WEEK 6 Types of File Systems Disk File Systems File Systems File Systems Transactional Systems File Systems Network File Systems Special Purpose File Systems 3 3 File Systems and Operating Systems Flat File Systems File Systems according to Unix-like Operating Systems File Systems according to Plan 9 from Bell Files under Microsoft Windows WEEK 7 File Storage Backup Files Purpose Storage Primary Storage Secondary Storage Third Storage Out Storage Features Storage Volatility Volatility UncertaintyAbility Availability Availability Performance Key Storage Technology Semiconductor Magnetic Paper Unusual Related Technology Connecting Network Connection Robotic Processing Robotic Processing File Processing Activity 4 4 Technology Execution Program interrupts secure mode and memory control mode Virtual Memory Operating Systems Linux and UNIX Microsoft Windows Mac OS X Special File Systems Journalized File Systems Graphic User Interfaces History Mainframes Microcomputers Microsoft Windows Plan Unix and Unix-like operating systems Mac OS X Real-time Operating Systems Built-in Core Development Hobby Systems Pre-Emptification 5 5 WEEK 1 THIS WEEK SPECIFIC LEARNING OUTCOMES To understand: The concept of the file in the computing concept, field, character, byte and bits in relation to File 5 6 6 Concept Files In this section, we will deal with the concepts of the file and their relationship. -
Oracle Applications Cloud
Oracle Applications Cloud Creating and Administering Analytics and Reports 21C Oracle Applications Cloud Creating and Administering Analytics and Reports 21C Part Number F42724-02 Copyright © 2011, 2021, Oracle and/or its affiliates. Authors: Dan Hilldale, Essan Ni Jirman This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. If this is software or related documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, then the following notice is applicable: U.S. GOVERNMENT END USERS: Oracle programs (including any operating system, integrated software, any programs embedded, installed or activated on delivered hardware, and modifications of such programs) and Oracle computer documentation or other Oracle data delivered to or accessed by U.S. Government end users are "commercial computer software" or "commercial computer software documentation" -

Pyfilesystem Documentation Release 2.0.21
PyFilesystem Documentation Release 2.0.21 Will McGugan May 12, 2018 Contents 1 Introduction 3 1.1 Installing.................................................3 2 Guide 5 2.1 Why use PyFilesystem?.........................................5 2.2 Opening Filesystems...........................................5 2.3 Tree Printing...............................................6 2.4 Closing..................................................7 2.5 Directory Information..........................................7 2.6 Sub Directories..............................................8 2.7 Working with Files............................................8 2.8 Walking..................................................9 2.9 Moving and Copying...........................................9 3 Concepts 11 3.1 Paths................................................... 11 3.2 System Paths............................................... 12 3.3 Sandboxing................................................ 12 3.4 Errors................................................... 13 4 Resource Info 15 4.1 Info Objects............................................... 15 4.2 Namespaces............................................... 15 4.3 Missing Namespaces........................................... 17 4.4 Raw Info................................................. 18 5 FS URLs 19 5.1 Format.................................................. 19 5.2 URL Parameters............................................. 20 5.3 Opening FS URLS............................................ 20 6 Walking 21 6.1 Walk -

Tinkertool System 6 Reference Manual Ii
Documentation 0632-1969/2 TinkerTool System 6 Reference Manual ii Version 6.99, July 21, 2021. US-English edition. MBS Documentation 0632-1969/2 © Copyright 2003 – 2021 by Marcel Bresink Software-Systeme Marcel Bresink Software-Systeme Ringstr. 21 56630 Kretz Germany All rights reserved. No part of this publication may be redistributed, translated in other languages, or transmitted, in any form or by any means, electronic, mechanical, recording, or otherwise, without the prior written permission of the publisher. This publication may contain examples of data used in daily business operations. To illustrate them as completely as possible, the examples include the names of individuals, companies, brands, and products. All of these names are fictitious and any similarity to the names and addresses used by an actual business enterprise is entirely coincidental. This publication could include technical inaccuracies or typographical errors. Changes are periodically made to the information herein; these changes will be incorporated in new editions of the publication. The publisher may make improvements and/or changes in the product(s) and/or the program(s) described in this publication at any time without notice. Make sure that you are using the correct edition of the publication for the level of the product. The version number can be found at the top of this page. Apple, macOS, iCloud, and FireWire are registered trademarks of Apple Inc. Intel is a registered trademark of Intel Corporation. UNIX is a registered trademark of The Open Group. Broadcom is a registered trademark of Broadcom, Inc. Trademarks or service marks are used for identification purposes only. -

Design and Implementation of a Distributed Back-Up System Thomas Mager
Design and implementation of a distributed back-up system Thomas Mager To cite this version: Thomas Mager. Design and implementation of a distributed back-up system. Cryptography and Security [cs.CR]. Télécom ParisTech, 2014. English. NNT : 2014ENST0036. tel-01413484 HAL Id: tel-01413484 https://pastel.archives-ouvertes.fr/tel-01413484 Submitted on 9 Dec 2016 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. 2014-ENST-0036 EDITE - ED 130 Doctorat ParisTech THÈSE pour obtenir le grade de docteur délivré par TELECOM ParisTech Spécialité « réseaux et sécurité » présentée et soutenue publiquement par Thomas MAGER le 30 juin 2014 Conception et implémentation d’un système de sauvegarde distribué Directeur de thèse : Prof. Ernst BIERSACK Jury M. Pietro MICHIARDI, EURECOM, Sophia-Antipolis - France Examinateur M. Guillaume URVOY-KELLER, Université Nice Sophia Antipolis - France Examinateur et Président M. Georg CARLE, TU Munich, Munich - Allemagne Rapporteur M. Pascal FELBER, Université de Neuchâtel, Neuchâtel - Suisse Rapporteur TELECOM ParisTech école de l’Institut Télécom - membre de ParisTech ii Abstract As computer users, we create increasing amounts of data, such as digital docu- ments, pictures, and videos. Because these data have high value in our daily life the need for back-ups arises.