Statistical Attack on RC4 Distinguishing WPA
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Middleware in Action 2007
Technology Assessment from Ken North Computing, LLC Middleware in Action Industrial Strength Data Access May 2007 Middleware in Action: Industrial Strength Data Access Table of Contents 1.0 Introduction ............................................................................................................. 2 Mature Technology .........................................................................................................3 Scalability, Interoperability, High Availability ...................................................................5 Components, XML and Services-Oriented Architecture..................................................6 Best-of-Breed Middleware...............................................................................................7 Pay Now or Pay Later .....................................................................................................7 2.0 Architectures for Distributed Computing.................................................................. 8 2.1 Leveraging Infrastructure ........................................................................................ 8 2.2 Multi-Tier, N-Tier Architecture ................................................................................. 9 2.3 Persistence, Client-Server Databases, Distributed Data ....................................... 10 Client-Server SQL Processing ......................................................................................10 Client Libraries .............................................................................................................. -

(SMC) MODULE of RC4 STREAM CIPHER ALGORITHM for Wi-Fi ENCRYPTION
InternationalINTERNATIONAL Journal of Electronics and JOURNAL Communication OF Engineering ELECTRONICS & Technology (IJECET),AND ISSN 0976 – 6464(Print), ISSN 0976 – 6472(Online), Volume 6, Issue 1, January (2015), pp. 79-85 © IAEME COMMUNICATION ENGINEERING & TECHNOLOGY (IJECET) ISSN 0976 – 6464(Print) IJECET ISSN 0976 – 6472(Online) Volume 6, Issue 1, January (2015), pp. 79-85 © IAEME: http://www.iaeme.com/IJECET.asp © I A E M E Journal Impact Factor (2015): 7.9817 (Calculated by GISI) www.jifactor.com VHDL MODELING OF THE SRAM MODULE AND STATE MACHINE CONTROLLER (SMC) MODULE OF RC4 STREAM CIPHER ALGORITHM FOR Wi-Fi ENCRYPTION Dr.A.M. Bhavikatti 1 Mallikarjun.Mugali 2 1,2Dept of CSE, BKIT, Bhalki, Karnataka State, India ABSTRACT In this paper, VHDL modeling of the SRAM module and State Machine Controller (SMC) module of RC4 stream cipher algorithm for Wi-Fi encryption is proposed. Various individual modules of Wi-Fi security have been designed, verified functionally using VHDL-simulator. In cryptography RC4 is the most widely used software stream cipher and is used in popular protocols such as Transport Layer Security (TLS) (to protect Internet traffic) and WEP (to secure wireless networks). While remarkable for its simplicity and speed in software, RC4 has weaknesses that argue against its use in new systems. It is especially vulnerable when the beginning of the output key stream is not discarded, or when nonrandom or related keys are used; some ways of using RC4 can lead to very insecure cryptosystems such as WEP . Many stream ciphers are based on linear feedback shift registers (LFSRs), which, while efficient in hardware, are less so in software. -

A Practical Attack on Broadcast RC4
A Practical Attack on Broadcast RC4 Itsik Mantin and Adi Shamir Computer Science Department, The Weizmann Institute, Rehovot 76100, Israel. {itsik,shamir}@wisdom.weizmann.ac.il Abstract. RC4is the most widely deployed stream cipher in software applications. In this paper we describe a major statistical weakness in RC4, which makes it trivial to distinguish between short outputs of RC4 and random strings by analyzing their second bytes. This weakness can be used to mount a practical ciphertext-only attack on RC4in some broadcast applications, in which the same plaintext is sent to multiple recipients under different keys. 1 Introduction A large number of stream ciphers were proposed and implemented over the last twenty years. Most of these ciphers were based on various combinations of linear feedback shift registers, which were easy to implement in hardware, but relatively slow in software. In 1987Ron Rivest designed the RC4 stream cipher, which was based on a different and more software friendly paradigm. It was integrated into Microsoft Windows, Lotus Notes, Apple AOCE, Oracle Secure SQL, and many other applications, and has thus become the most widely used software- based stream cipher. In addition, it was chosen to be part of the Cellular Digital Packet Data specification. Its design was kept a trade secret until 1994, when someone anonymously posted its source code to the Cypherpunks mailing list. The correctness of this unofficial description was confirmed by comparing its outputs to those produced by licensed implementations. RC4 has a secret internal state which is a permutation of all the N =2n possible n bits words. -

In the United States Bankruptcy Court for the District of Delaware
Case 21-10527-JTD Doc 285 Filed 04/14/21 Page 1 of 68 IN THE UNITED STATES BANKRUPTCY COURT FOR THE DISTRICT OF DELAWARE ) In re: ) Chapter 11 ) CARBONLITE HOLDINGS LLC, et al.,1 ) Case No. 21-10527 (JTD) ) Debtors. ) (Jointly Administered) ) AFFIDAVIT OF SERVICE I, Victoria X. Tran, depose and say that I am employed by Stretto, the claims and noticing agent for the Debtors in the above-captioned case. On April 10, 2021, at my direction and under my supervision, employees of Stretto caused the following documents to be served via first-class mail on the service list attached hereto as Exhibit A, and via electronic mail on the service list attached hereto as Exhibit B: Notice of Proposed Sale or Sales of Substantially All of the Debtors’ Assets, Free and Clear of All Encumbrances, Other Than Assumed Liabilities, and Scheduling Final Sale Hearing Related Thereto (Docket No. 268) Notice of Proposed Assumption and Assignment of Designated Executory Contracts and Unexpired Leases (Docket No. 269) Furthermore, on April 10, 2021, at my direction and under my supervision, employees of Stretto caused the following documents to be served via first-class mail on the service list attached hereto as Exhibit C, and via electronic mail on the service list attached hereto as Exhibit D: Notice of Proposed Sale or Sales of Substantially All of the Debtors’ Assets, Free and Clear of All Encumbrances, Other Than Assumed Liabilities, and Scheduling Final Sale Hearing Related Thereto (Docket No. 268, Pages 1-4) Notice of Proposed Assumption and Assignment of Designated Executory Contracts and Unexpired Leases (Docket No. -

Cryptanalysis of Stream Ciphers Based on Arrays and Modular Addition
KATHOLIEKE UNIVERSITEIT LEUVEN FACULTEIT INGENIEURSWETENSCHAPPEN DEPARTEMENT ELEKTROTECHNIEK{ESAT Kasteelpark Arenberg 10, 3001 Leuven-Heverlee Cryptanalysis of Stream Ciphers Based on Arrays and Modular Addition Promotor: Proefschrift voorgedragen tot Prof. Dr. ir. Bart Preneel het behalen van het doctoraat in de ingenieurswetenschappen door Souradyuti Paul November 2006 KATHOLIEKE UNIVERSITEIT LEUVEN FACULTEIT INGENIEURSWETENSCHAPPEN DEPARTEMENT ELEKTROTECHNIEK{ESAT Kasteelpark Arenberg 10, 3001 Leuven-Heverlee Cryptanalysis of Stream Ciphers Based on Arrays and Modular Addition Jury: Proefschrift voorgedragen tot Prof. Dr. ir. Etienne Aernoudt, voorzitter het behalen van het doctoraat Prof. Dr. ir. Bart Preneel, promotor in de ingenieurswetenschappen Prof. Dr. ir. Andr´eBarb´e door Prof. Dr. ir. Marc Van Barel Prof. Dr. ir. Joos Vandewalle Souradyuti Paul Prof. Dr. Lars Knudsen (Technical University, Denmark) U.D.C. 681.3*D46 November 2006 ⃝c Katholieke Universiteit Leuven { Faculteit Ingenieurswetenschappen Arenbergkasteel, B-3001 Heverlee (Belgium) Alle rechten voorbehouden. Niets uit deze uitgave mag vermenigvuldigd en/of openbaar gemaakt worden door middel van druk, fotocopie, microfilm, elektron- isch of op welke andere wijze ook zonder voorafgaande schriftelijke toestemming van de uitgever. All rights reserved. No part of the publication may be reproduced in any form by print, photoprint, microfilm or any other means without written permission from the publisher. D/2006/7515/88 ISBN 978-90-5682-754-0 To my parents for their unyielding ambition to see me educated and Prof. Bimal Roy for making cryptology possible in my life ... My Gratitude It feels awkward to claim the thesis to be singularly mine as a great number of people, directly or indirectly, participated in the process to make it see the light of day. -
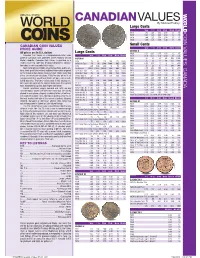
*UPDATED Canadian Values 07-04 201 7/26/2016 4:42:21 PM *UPDATED Canadian Values 07-04 202 COIN VALUES: CANADA 02 .0 .0 12
CANADIAN VALUES By Michael Findlay Large Cents VG-8 F-12 VF-20 EF-40 MS-60 MS-63R 1917 1.00 1.25 1.50 2.50 13. 45. CANADA COIN VALUES: 1918 1.00 1.25 1.50 2.50 13. 45. 1919 1.00 1.25 1.50 2.50 13. 45. 1920 1.00 1.25 1.50 3.00 18. 70. CANADIAN COIN VALUES Small Cents PRICE GUIDE VG-8 F-12 VF-20 EF-40 MS-60 MS-63R GEORGE V All prices are in U.S. dollars LargeL Cents C t 1920 0.20 0.35 0.75 1.50 12. 45. Canadian Coin Values is a comprehensive retail value VG-8 F-12 VF-20 EF-40 MS-60 MS-63R 1921 0.50 0.75 1.50 4.00 30. 250. guide of Canadian coins published online regularly at Coin VICTORIA 1922 20. 23. 28. 40. 200. 1200. World’s website. Canadian Coin Values is provided as a 1858 70. 90. 120. 200. 475. 1800. 1923 30. 33. 42. 55. 250. 2000. reader service to collectors desiring independent informa- 1858 Coin Turn NI NI 2500. 5000. BNE BNE 1924 6.00 8.00 11. 16. 120. 800. tion about a coin’s potential retail value. 1859 4.00 5.00 6.00 10. 50. 200. 1925 25. 28. 35. 45. 200. 900. Sources for pricing include actual transactions, public auc- 1859 Brass 16000. 22000. 30000. BNE BNE BNE 1926 3.50 4.50 7.00 12. 90. 650. tions, fi xed-price lists and any additional information acquired 1859 Dbl P 9 #1 225. -

An Archeology of Cryptography: Rewriting Plaintext, Encryption, and Ciphertext
An Archeology of Cryptography: Rewriting Plaintext, Encryption, and Ciphertext By Isaac Quinn DuPont A thesis submitted in conformity with the requirements for the degree of Doctor of Philosophy Faculty of Information University of Toronto © Copyright by Isaac Quinn DuPont 2017 ii An Archeology of Cryptography: Rewriting Plaintext, Encryption, and Ciphertext Isaac Quinn DuPont Doctor of Philosophy Faculty of Information University of Toronto 2017 Abstract Tis dissertation is an archeological study of cryptography. It questions the validity of thinking about cryptography in familiar, instrumentalist terms, and instead reveals the ways that cryptography can been understood as writing, media, and computation. In this dissertation, I ofer a critique of the prevailing views of cryptography by tracing a number of long overlooked themes in its history, including the development of artifcial languages, machine translation, media, code, notation, silence, and order. Using an archeological method, I detail historical conditions of possibility and the technical a priori of cryptography. Te conditions of possibility are explored in three parts, where I rhetorically rewrite the conventional terms of art, namely, plaintext, encryption, and ciphertext. I argue that plaintext has historically been understood as kind of inscription or form of writing, and has been associated with the development of artifcial languages, and used to analyze and investigate the natural world. I argue that the technical a priori of plaintext, encryption, and ciphertext is constitutive of the syntactic iii and semantic properties detailed in Nelson Goodman’s theory of notation, as described in his Languages of Art. I argue that encryption (and its reverse, decryption) are deterministic modes of transcription, which have historically been thought of as the medium between plaintext and ciphertext. -

RC4 Encryption
Ralph (Eddie) Rise Suk-Hyun Cho Devin Kaylor RC4 Encryption RC4 is an encryption algorithm that was created by Ronald Rivest of RSA Security. It is used in WEP and WPA, which are encryption protocols commonly used on wireless routers. The workings of RC4 used to be a secret, but its code was leaked onto the internet in 1994. RC4 was originally very widely used due to its simplicity and speed. Typically 16 byte keys are used for strong encryption, but shorter key lengths are also widely used due to export restrictions. Over time this code was shown to produce biased outputs towards certain sequences, mostly in first few bytes of the keystream generated. This led to a future version of the RC4 code that is more widely used today, called RC4-drop[n], in which the first n bytes of the keystream are dropped in order to get rid of this biased output. Some notable uses of RC4 are implemented in Microsoft Excel, Adobe's Acrobat 2.0 (1994), and BitTorrent clients. To begin the process of RC4 encryption, you need a key, which is often user-defined and between 40-bits and 256-bits. A 40-bit key represents a five character ASCII code that gets translated into its 40 character binary equivalent (for example, the ASCII key "pwd12" is equivalent to 0111000001110111011001000011000100110010 in binary). The next part of RC4 is the key-scheduling algorithm (KSA), listed below (from Wikipedia). for i from 0 to 255 S[i] := i endfor j := 0 for i from 0 to 255 j := (j + S[i] + key[i mod keylength]) mod 256 swap(S[i],S[j]) endfor KSA creates an array S that contains 256 entries with the digits 0 through 255, as in the table below. -

Data Extraction Tool
ANALYSIS OF COMMUNICATION PROTOCOLS FOR HOME AREA NETWORKS FOR SMART GRID Mayur Anand B.E, Visveswaraiah Technological University, Karnataka, India, 2007 PROJECT Submitted in partial satisfaction of the requirements for the degree of MASTER OF SCIENCE in COMPUTER SCIENCE at CALIFORNIA STATE UNIVERSITY, SACRAMENTO SPRING 2011 ANALYSIS OF COMMUNICATION PROTOCOLS FOR HOME AREA NETWORKS FOR SMART GRID A Project by Mayur Anand Approved by: __________________________________, Committee Chair Isaac Ghansah, Ph.D. __________________________________, Second Reader Chung-E-Wang, Ph.D. ____________________________ Date ii Student: Mayur Anand I certify that this student has met the requirements for format contained in the University format manual, and that this project is suitable for shelving in the Library and credit is to be awarded for the Project. __________________________, Graduate Coordinator ________________ Nikrouz Faroughi, Ph.D. Date Department of Computer Science iii Abstract of ANALYSIS OF COMMUNICATION PROTOCOLS FOR HOME AREA NETWORKS FOR SMART GRID by Mayur Anand This project discusses home area networks in Smart Grid. A Home Area Network plays a very important role in communication among various devices in a home. There are multiple technologies that are in contention to be used to implement home area networks. This project analyses various communication protocols in Home Area Networks and their corressponding underlying standards in detail. The protocols and standards covered in this project are ZigBee, Z-Wave, IEEE 802.15.4 and IEEE 802.11. Only wireless protocols have been discussed and evaluated. Various security threats present in the protocols mentioned above along with the counter measures to most of the threats have been discussed as well. -

RC4-2S: RC4 Stream Cipher with Two State Tables
RC4-2S: RC4 Stream Cipher with Two State Tables Maytham M. Hammood, Kenji Yoshigoe and Ali M. Sagheer Abstract One of the most important symmetric cryptographic algorithms is Rivest Cipher 4 (RC4) stream cipher which can be applied to many security applications in real time security. However, RC4 cipher shows some weaknesses including a correlation problem between the public known outputs of the internal state. We propose RC4 stream cipher with two state tables (RC4-2S) as an enhancement to RC4. RC4-2S stream cipher system solves the correlation problem between the public known outputs of the internal state using permutation between state 1 (S1) and state 2 (S2). Furthermore, key generation time of the RC4-2S is faster than that of the original RC4 due to less number of operations per a key generation required by the former. The experimental results confirm that the output streams generated by the RC4-2S are more random than that generated by RC4 while requiring less time than RC4. Moreover, RC4-2S’s high resistivity protects against many attacks vulnerable to RC4 and solves several weaknesses of RC4 such as distinguishing attack. Keywords Stream cipher Á RC4 Á Pseudo-random number generator This work is based in part, upon research supported by the National Science Foundation (under Grant Nos. CNS-0855248 and EPS-0918970). Any opinions, findings and conclusions or recommendations expressed in this material are those of the author (s) and do not necessarily reflect the views of the funding agencies or those of the employers. M. M. Hammood Applied Science, University of Arkansas at Little Rock, Little Rock, USA e-mail: [email protected] K. -

A Practical Attack on the Fixed RC4 in the WEP Mode
A Practical Attack on the Fixed RC4 in the WEP Mode Itsik Mantin NDS Technologies, Israel [email protected] Abstract. In this paper we revisit a known but ignored weakness of the RC4 keystream generator, where secret state info leaks to the gen- erated keystream, and show that this leakage, also known as Jenkins’ correlation or the RC4 glimpse, can be used to attack RC4 in several modes. Our main result is a practical key recovery attack on RC4 when an IV modifier is concatenated to the beginning of a secret root key to generate a session key. As opposed to the WEP attack from [FMS01] the new attack is applicable even in the case where the first 256 bytes of the keystream are thrown and its complexity grows only linearly with the length of the key. In an exemplifying parameter setting the attack recov- ersa16-bytekeyin248 steps using 217 short keystreams generated from different chosen IVs. A second attacked mode is when the IV succeeds the secret root key. We mount a key recovery attack that recovers the secret root key by analyzing a single word from 222 keystreams generated from different IVs, improving the attack from [FMS01] on this mode. A third result is an attack on RC4 that is applicable when the attacker can inject faults to the execution of RC4. The attacker derives the internal state and the secret key by analyzing 214 faulted keystreams generated from this key. Keywords: RC4, Stream ciphers, Cryptanalysis, Fault analysis, Side- channel attacks, Related IV attacks, Related key attacks. 1 Introduction RC4 is the most widely used stream cipher in software applications. -
The Rc4 Stream Encryption Algorithm
TTHEHE RC4RC4 SSTREAMTREAM EENCRYPTIONNCRYPTION AALGORITHMLGORITHM William Stallings Stream Cipher Structure.............................................................................................................2 The RC4 Algorithm ...................................................................................................................4 Initialization of S............................................................................................................4 Stream Generation..........................................................................................................5 Strength of RC4 .............................................................................................................6 References..................................................................................................................................6 Copyright 2005 William Stallings The paper describes what is perhaps the popular symmetric stream cipher, RC4. It is used in the two security schemes defined for IEEE 802.11 wireless LANs: Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). We begin with an overview of stream cipher structure, and then examine RC4. Stream Cipher Structure A typical stream cipher encrypts plaintext one byte at a time, although a stream cipher may be designed to operate on one bit at a time or on units larger than a byte at a time. Figure 1 is a representative diagram of stream cipher structure. In this structure a key is input to a pseudorandom bit generator that produces a stream