Operating Systems and Middleware: Supporting Controlled Interaction
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Operating System Transactions
Operating System Transactions Donald E. Porter, Owen S. Hofmann, Christopher J. Rossbach, Alexander Benn, and Emmett Witchel Department of Computer Sciences, The University of Texas at Austin {porterde,osh,rossbach,abenn1,witchel}@cs.utexas.edu ABSTRACT Programming; D.4.7 [Operating Systems]: Organization Applications must be able to synchronize accesses to oper- and Design ating system resources in order to ensure correctness in the face of concurrency and system failures. System transac- General Terms tions allow the programmer to specify updates to heteroge- Design, Performance, Security neous system resources with the OS guaranteeing atomicity, consistency, isolation, and durability (ACID). System trans- Keywords actions efficiently and cleanly solve persistent concurrency Transactions, Operating Systems, TxOS, Race Conditions, problems that are difficult to address with other techniques. Transactional Memory For example, system transactions eliminate security vulner- abilities in the file system that are caused by time-of-check- 1. INTRODUCTION to-time-of-use (TOCTTOU) race conditions. System trans- actions enable an unsuccessful software installation to roll Applications often need to group accesses to operating system resources (such as files and signals) into logical units, back without disturbing concurrent, independent updates to the file system. just as multithreaded applications must group accesses to This paper describes TxOS, a variant of Linux 2.6.22 that shared data structures into critical regions. For example, implements system transactions. TxOS uses new implemen- local user and group accounts on Linux and similar oper- tation techniques to provide fast, serializable transactions ating systems are stored across three files that need to be /etc/passwd /etc/shadow with strong isolation and fairness between system transac- mutually consistent: , , and /etc/group. -

Operating System Transactions
Operating System Transactions Donald E. Porter, Owen S. Hofmann, Christopher J. Rossbach, Alexander Benn, and Emmett Witchel Department of Computer Sciences, The University of Texas at Austin {porterde,osh,rossbach,abenn1,witchel}@cs.utexas.edu ABSTRACT 1. INTRODUCTION Applications must be able to synchronize accesses to operating sys- Applications often need to group accesses to operating system tem resources in order to ensure correctness in the face of concur- resources (such as files and signals) into logical units, just as mul- rency and system failures. System transactions allow the program- tithreaded applications must group accesses to shared data struc- mer to specify updates to heterogeneous system resources with the tures into critical regions. For example, local user and group ac- OS guaranteeing atomicity, consistency, isolation, and durability counts on Linux and similar operating systems are stored across (ACID). System transactions efficiently and cleanly solve persis- three files that need to be mutually consistent: /etc/passwd, tent concurrency problems that are difficult to address with other /etc/shadow, and /etc/group. techniques. For example, system transactions eliminate security Applications currently struggle to make consistent updates to vulnerabilities in the file system that are caused by time-of-check- system resources. In current operating systems, individual system to-time-of-use (TOCTTOU) race conditions. System transactions calls are generally atomic and isolated from the rest of the system, enable an unsuccessful software installation to roll back without but it is difficult, if not impossible, to condense complex opera- disturbing concurrent, independent updates to the file system. tions into a single system call. -
(MSCS) Computer Forensics
Master of Science(Cyber Security) (MSCS) Computer Forensics (CSP-18) Block 1 Introduction to Computer Forensics Unit – 1: INTRODUCTION TO DIGITAL FORENSIC Unit – 2: COMPUTER FORENSICS INVESTIGATION PROCESS Unit – 3: DIGITAL EVIDENCE AND FIRST RESPONDER PROCEDURE Unit – 4: UNDERSTANDING STORAGE MEDIA AND FILE SYSTEM Master of Science(Cyber Security) (MSCS) EXPERT COMMITTEE Dr. P.K Behera (Chairman) Reader in Computer Science Utkal University Bhubaneswar, Odisha Dr.J.RMohanty (Member) Professor and HOD KIIT University Bhubaneswar, Odisha Sri PabitranandaPattnaik (Member) Scientist-E, NIC Bhubaneswar, Odisha Sri Malaya Kumar Das (Member) Scientist-E, NIC Bhubaneswar, Odisha Dr. Bhagirathi Nayak (Member) Professor and Head (IT & System) Sri Sri University, Bhubaneswar,Odisha Dr.Manoranjan Pradhan (Member) Professor and Head (IT & System) G.I.T.A Bhubaneswar, Odisha Sri Chandrakant Mallick (Convener) Consultant (Academic) School of Computer and Information Science Odisha State Open University Sambalpur, Odisha Master of Science(Cyber Security) (MSCS) Course Writers Aseem Kumar Patel Academic Consultant Odisha State Open University,Sambalpur Material Production Dr. Manas Ranjan Pujari Registrar Odisha State Open University, Sambalpur © OSOU, 2019. Promoting Use and Contribution of Open Education Resources is made available under a Creative Commons Attribution- ShareAlike4.0http://creativecommons.org/licences/by-sa/4.0 Unit Structure 1.1 Learning Objectives 02 1.2 Introduction 02 1.3 Definition of Computer Forensics 02 1.4 Cybercrime 03 1.5 -
Windows Internals, Sixth Edition, Part 2
spine = 1.2” Part 2 About the Authors Mark Russinovich is a Technical Fellow in ® the Windows Azure™ group at Microsoft. Windows Internals He is coauthor of Windows Sysinternals SIXTH EDITION Administrator’s Reference, co-creator of the Sysinternals tools available from Microsoft Windows ® The definitive guide—fully updated for Windows 7 TechNet, and coauthor of the Windows Internals and Windows Server 2008 R2 book series. Delve inside Windows architecture and internals—and see how core David A. Solomon is coauthor of the Windows Internals book series and has taught components work behind the scenes. Led by a team of internationally his Windows internals class to thousands of renowned internals experts, this classic guide has been fully updated Windows developers and IT professionals worldwide, SIXTH for Windows 7 and Windows Server® 2008 R2—and now presents its including Microsoft staff. He is a regular speaker 6EDITION coverage in two volumes. at Microsoft conferences, including TechNet As always, you get critical, insider perspectives on how Windows and PDC. operates. And through hands-on experiments, you’ll experience its Alex Ionescu is a chief software architect and internal behavior firsthand—knowledge you can apply to improve consultant expert in low-level system software, application design, debugging, system performance, and support. kernel development, security training, and Internals reverse engineering. He teaches Windows internals courses with David Solomon, and is ® In Part 2, you will: active in the security research community. -
Exploration of Windows Vista Advanced Forensic Topics – Day 1
Windows Vista and NTFS File System Internals Exploration of Windows Vista Advanced Forensic Topics – Day 1 LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Windows Client Forensics (Windows Vista Advanced Topics) Transactional NTFS and Registry Explained LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved New Features Important Changes of Interest LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Self-Healing File System • Vista includes a “self-healing” function which can correct certain errors in the system • Vista maintains a list of hashes of known files and checks the hashes periodically • On non-system files Vista will validate the file metadata • Files whose hashes do not match or metadata is not valid will be replaced the next time the system is rebooted LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Self-Healing File System • Equivalent to Chkdsk and defrag processes constantly running in the background • This has the potential to decrease the usefulness of the free space and slack space on the disk as well as limit the ability to recover deleted files LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Self-Healing File System • Healed files can be identified by an examination of the event -
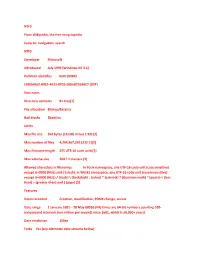
NTFS from Wikipedia, the Free Encyclopedia Jump To: Navigation, Search NTFS Developer Microsoft Introduced July 1993 (Windows
NTFS From Wikipedia, the free encyclopedia Jump to: navigation, search NTFS Developer Microsoft Introduced July 1993 (Windows NT 3.1) Partition identifier 0x07 (MBR) EBD0A0A2-B9E5-4433-87C0-68B6B72699C7 (GPT) Structures Directory contents B+ tree[1] File allocation Bitmap/Extents Bad blocks $badclus Limits Max file size 264 bytes (16 EiB) minus 1 KiB [2] Max number of files 4,294,967,295 (232-1)[2] Max filename length 255 UTF-16 code units[3] Max volume size 264 ? 1 clusters [2] Allowed characters in filenames In Posix namespace, any UTF-16 code unit (case sensitive) except U+0000 (NUL) and / (slash). In Win32 namespace, any UTF-16 code unit (case insensitive) except U+0000 (NUL) / (slash) \ (backslash) : (colon) * (asterisk) ? (Question mark) " (quote) < (less than) > (greater than) and | (pipe) [3] Features Dates recorded Creation, modification, POSIX change, access Date range 1 January 1601 ʹ 28 May 60056 (File times are 64-bit numbers counting 100- nanosecond intervals (ten million per second) since 1601, which is 58,000+ years) Date resolution 100ns Forks Yes (see Alternate data streams below) Attributes Read-only, hidden, system, archive, not content indexed, off-line, temporary File system permissions ACLs Transparent compression Per-file, LZ77 (Windows NT 3.51 onward) Transparent encryption Per-file, DESX (Windows 2000 onward), Triple DES (Windows XP onward), AES (Windows XP Service Pack 1, Windows Server 2003 onward) Single Instance Storage Yes Supported operating systems Windows NT family (Windows NT 3.1 to Windows NT 4.0, Windows 2000, Windows XP, Windows Server 2003, Windows Vista, Windows Server 2008) NTFS is the standard file system of Windows NT, including its later versions Windows 2000, Windows XP, Windows Server 2003, Windows Server 2008, and Windows Vista.[4] NTFS supersedes the FAT file system as the preferred file system for Microsoft͛s ͞Windows͟-branded operating systems. -

Exploiting CVE-2018-8611
Exploiting CVE-2018-8611 Windows Kernel Transaction Manager (KTM) Race Condition Cedric Halbronn - OffensiveCon 2020 1 / 137 2 / 137 About Exploit Development Group (EDG), NCC Group Write exploits to help consultants do their job Focus on patched vulnerabilities Cedric Halbronn Presenting @saidelike, [email protected] Aaron Adams Co-researcher, unable to attend @fidgetingbits, [email protected] 3 / 137 This talk Discuss an interesting race condition affecting Microsoft Kernel Transaction Manager (KTM) Found used in the wild by Kaspersky Boris Larin (@Oct0xor) and Igor Soumenkov (@2igosha) Exploited by us early 2019 Never got to see the original exploit or details Minimal details from Kaspersky at the time Race condition in KTM Exploitable from inside browser sandbox Works on Windows 10 A few hints for triggering the race Presented by Aaron at POC2019 in November 4 / 137 Notable KTM-related security findings 2010 - CVE-2010-1889 - Tavis Ormandy - invalid free 2015 - MS15-038 - James Forshaw - type confusion 2017 - CVE-2017-8481 - j00ru - stack memory disclosure 2018 - CVE-2018-8611 - Oct0xor/2igosha - Kaspersky blog 2019 - Proton Bot malware uses KTM Used transacted versions of common functions to evade API inspection 5 / 137 Oct0xor/2igosha - Kaspersky blog 6 / 137 Me when reading write-up 7 / 137 Tooling Virtualization: VMWare Workstation Binary analysis: IDA Pro, Hex-Rays Decompiler Binary diffing: Diaphora Collaboration: IDArling Debugging: WinDbg (ring0), virtualkd, x64dbg (ring3) Additional plugins/tools: ret-sync, -
Windows Persistent Memory Support
Windows Persistent Memory Support Neal Christiansen Microsoft © 2018 SNIA Persistent Memory Summit. All Rights Reserved. Agenda Review: Existing Windows PM Support What’s New New PM APIs Large & Huge Page Support Dax aware Write-ahead LOG Improved Driver Model Uncorrectable Error Handling Hyper-V & NVML Support © 2018 SNIA Persistent Memory Summit. All Rights Reserved. How DAX Works Block Mode DirectAccess Memory Mapped The Idea Application Application Region Application App has direct access to PM via Standard File API requests memory- Load/Store mapped file existing memory-mapping semantics User Mode Operations Updates directly modify PM Kernel Mode DirectAccess Storage Stack not involved Setup Path PM-Aware File System (NTFS - DAX) Characteristics True device performance (no DirectAccess software overhead) Data Path Byte-Addressable Enumerates Bus Driver NVDIMM Disk Driver Load/Store Operations Memory Mapped © 2018 SNIA Persistent Memory Summit. All Rights Reserved. PM Region Windows DAX Volume Support DAX mode is chosen at volume format time Why: compatibility issues with existing components, examples: File system filters Bitlocker (volume level software encryption) Volsnap (volume snapshot provider) Some existing functionality is lost DAX Volumes are only supported by the NTFS file system © 2018 SNIA Persistent Memory Summit. All Rights Reserved. IO on DAX Volumes Memory Mapped IO Memory mapped sections map directly to PM hardware Cached IO Cache Manager maps directly to persistent memory Copies directly between user’s buffer and -
![[MS-FSCC]: File System Control Codes](https://docslib.b-cdn.net/cover/6701/ms-fscc-file-system-control-codes-2706701.webp)
[MS-FSCC]: File System Control Codes
[MS-FSCC]: File System Control Codes Intellectual Property Rights Notice for Open Specifications Documentation . Technical Documentation. Microsoft publishes Open Specifications documentation for protocols, file formats, languages, standards as well as overviews of the interaction among each of these technologies. Copyrights. This documentation is covered by Microsoft copyrights. Regardless of any other terms that are contained in the terms of use for the Microsoft website that hosts this documentation, you may make copies of it in order to develop implementations of the technologies described in the Open Specifications and may distribute portions of it in your implementations using these technologies or your documentation as necessary to properly document the implementation. You may also distribute in your implementation, with or without modification, any schema, IDL's, or code samples that are included in the documentation. This permission also applies to any documents that are referenced in the Open Specifications. No Trade Secrets. Microsoft does not claim any trade secret rights in this documentation. Patents. Microsoft has patents that may cover your implementations of the technologies described in the Open Specifications. Neither this notice nor Microsoft's delivery of the documentation grants any licenses under those or any other Microsoft patents. However, a given Open Specification may be covered by Microsoft Open Specification Promise or the Community Promise. If you would prefer a written license, or if the technologies described in the Open Specifications are not covered by the Open Specifications Promise or Community Promise, as applicable, patent licenses are available by contacting [email protected]. Trademarks. The names of companies and products contained in this documentation may be covered by trademarks or similar intellectual property rights. -

Product Brief V10.95 November 2017
Product Brief v10.95 November 2017 © 2017 ICONICS, Inc. All rights reserved. Specifications are subject to change without notice. AnalytiX and its respective modules are registered trademarks of ICONICS, Inc. GENESIS64, GENESIS32, Hyper Historian, BizViz, PortalWorX, MobileHMI and their respective modules, OPC-To-The-Core, and Visualize Your Enterprise are trademarks of ICONICS, Inc. Other product and company names mentioned herein may be trademarks of their respective owners. Hyper Historian™ Product Brief Hyper Historian Introduction Companies today are faced with the need to perform better and to be more competitive with fewer resources. For plant-level operations, today’s systems need to connect to different infrastructures for data gathering and users need to analyze and visualize data in real time. Access to plant data is fundamental to staying competitive and efficient. The demand to produce products faster or streamline operations is increasing across the globe. ICONICS’ Hyper Historian™ enterprise-wide plant historian allows you to gain that competitive advantage, by organizing all your real-time information from across the enterprise. Hyper Historian is ICONICS’ high-speed, reliable and robust plant historian. In order to analyze and visualize data in real time, organizations must have access to plant data and reporting. Hyper Historian is designed to log large volumes of data, in excess of 100,000 updates per second, and connects to multiple data sources across the enterprise including OPC UA, OPC DA, OPC XML DA, BACnet, SNMP and many more. ICONICS Hyper Historian also provides full, web-based configuration. Optional redundant configurations are supported using redundant Hyper Historian Collectors and redundant Loggers, and Hyper Historian offers Store and Forward technology as part of its integrated redundancy solution. -

67594.Pdf (1510Mb)
Títol: Transactional FileSystem Volum: 1/1 Alumne: Juan Luis Pérez Rico Director/Ponente: Toni Cortés Rosselló Departament: Arquitectura de Computadors Data: 27 de setembre de 2010 DADES DEL PROJECTE Títol del projecte: Transactional FileSystem Nom de l’estudiant: Juan Luis Pérez Rico Titulació: Enginyeria Informàtica (Pla 2003) Crèdits: 37.5 Director/Ponent: Toni Cortés Rosselló Departament: Departament d’Arquitectura de Computadors MEMBRES DEL TRIBUNAL (nom i signatura) President: Yolanda Becerra Fontal Vocal: Raimon Elgueta Montó Secretari: Toni Cortés Rosselló QUALIFICACIÓ Qualificació numèrica: Qualificació descriptiva: Data: Índex 1 Introducció1 1.1 Motivació personal........................1 1.2 Objectius.............................3 1.3 Metodologia............................3 1.4 Organització de la memòria...................4 1.5 Agraïments............................6 2 Conceptes bàsics9 2.1 Sistemes Transaccionals.....................9 2.1.1 Sistemes de fitxers transaccionals............ 11 2.2 Entorn Windows......................... 12 2.2.1 Introducció........................ 12 2.2.2 Components clau..................... 14 2.3 Altres conceptes.......................... 19 2.3.1 Memory Mapped File Functions............. 19 2.3.2 Windows Streams..................... 20 2.3.3 NTFS Reparse Points................... 22 2.4 Installable File System Drivers.................. 23 vi ÍNDEX 2.4.1 File System Drivers.................... 24 2.4.2 File System Filter Drivers................ 26 2.4.3 File System Minifilter Drivers.............. 28 2.5 Desenvolupament de minifilters................. 33 2.5.1 Instal·lació, càrrega i descàrrega del minifilter..... 34 2.5.2 Processament d’operacions d’entrada/sortida...... 36 2.5.3 Modificació de paràmetres................ 38 2.5.4 Problemàtica: Complexitat de les interaccions..... 39 3 Aproximació i anàlisi del projecte 43 3.1 Aproximació inicial i antecedents................ 43 3.2 Marc de desenvolupament................... -

Download the Sample Pages
Microsoft® Windows® Vista™ Unleashed, Second Edition Publisher Copyright © 2008 by Sams Publishing Paul Boger All rights reserved. No part of this book shall be reproduced, stored in a retrieval Associate Publisher system, or transmitted by any means, electronic, mechanical, photocopying, recording, Greg Wiegand or otherwise, without written permission from the publisher. No patent liability is assumed with respect to the use of the information contained herein. Although every Acquisitions Editor precaution has been taken in the preparation of this book, the publisher and author Rick Kughen assume no responsibility for errors or omissions. Nor is any liability assumed for damages resulting from the use of the information contained herein. Development Editor ISBN-13: 978-0-672-33013-1 Rick Kughen ISBN-10: 0-672-33013-X Library of Congress Cataloging-in-Publication data Managing Editor McFedries, Paul. Patrick Kanouse Microsoft Windows Vista unleashed / Paul McFedries. -- 2nd ed. Project Editor p. cm. Seth Kerney Includes index. ISBN-10: 0-672-33013-X Copy Editor ISBN-13: 978-0-672-33013-1 Margo Catts 1. Microsoft Windows (Computer file) 2. Operating systems Proofreader (Computers) Paula Lowell I. Title. QA76.76.O63M398175 2008 Publishing 005.4'46--dc22 Coordinator Cindy Teeters 2008010864 Printed in the United States on America Book Designer First Printing March 2008 Gary Adair Trademarks Composition All terms mentioned in this book that are known to be trademarks or service marks Mark Shirar have been appropriately capitalized. Sams Publishing cannot attest to the accuracy of this information. Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark.