File in Transaction: Htransactedfile = Createfiletransacted(“Svchost.Exe” , GENERIC WRITE | GENERIC READ, …, Htransaction, …) 3
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Windows 7 Operating Guide
Welcome to Windows 7 1 1 You told us what you wanted. We listened. This Windows® 7 Product Guide highlights the new and improved features that will help deliver the one thing you said you wanted the most: Your PC, simplified. 3 3 Contents INTRODUCTION TO WINDOWS 7 6 DESIGNING WINDOWS 7 8 Market Trends that Inspired Windows 7 9 WINDOWS 7 EDITIONS 10 Windows 7 Starter 11 Windows 7 Home Basic 11 Windows 7 Home Premium 12 Windows 7 Professional 12 Windows 7 Enterprise / Windows 7 Ultimate 13 Windows Anytime Upgrade 14 Microsoft Desktop Optimization Pack 14 Windows 7 Editions Comparison 15 GETTING STARTED WITH WINDOWS 7 16 Upgrading a PC to Windows 7 16 WHAT’S NEW IN WINDOWS 7 20 Top Features for You 20 Top Features for IT Professionals 22 Application and Device Compatibility 23 WINDOWS 7 FOR YOU 24 WINDOWS 7 FOR YOU: SIMPLIFIES EVERYDAY TASKS 28 Simple to Navigate 28 Easier to Find Things 35 Easy to Browse the Web 38 Easy to Connect PCs and Manage Devices 41 Easy to Communicate and Share 47 WINDOWS 7 FOR YOU: WORKS THE WAY YOU WANT 50 Speed, Reliability, and Responsiveness 50 More Secure 55 Compatible with You 62 Better Troubleshooting and Problem Solving 66 WINDOWS 7 FOR YOU: MAKES NEW THINGS POSSIBLE 70 Media the Way You Want It 70 Work Anywhere 81 New Ways to Engage 84 INTRODUCTION TO WINDOWS 7 6 WINDOWS 7 FOR IT PROFESSIONALS 88 DESIGNING WINDOWS 7 8 WINDOWS 7 FOR IT PROFESSIONALS: Market Trends that Inspired Windows 7 9 MAKE PEOPLE PRODUCTIVE ANYWHERE 92 WINDOWS 7 EDITIONS 10 Remove Barriers to Information 92 Windows 7 Starter 11 Access -

Diagnostics and Recovery Toolset Recovery Toolset
Para clientes de Software Assurance .. Microsoft Application Virtualization ® Microsoft .. Microsoft Asset Inventory Service Diagnostics and .. Microsoft Advanced Group Policy Management .. Microsoft Diagnostics and Recovery Toolset Recovery Toolset .. Microsoft System Center Desktop Error Monitoring .. Microsoft® Microsoft Enterprise Desktop Virtualization Paquete de Optimización de PC Para Software Assurance Microsoft® Diagnostics and Recovery Toolset ofrece herramientas intuitivas y poderosas que permiten a los administradores recuperar PCs que no se pueden utilizar y fácilmente, identifi car los problemas que causan los problemas del sistema y la red. Si ocurre una catástrofe en la PC, estas herramientas le permiten reparar los sistemas bloqueados o que no se pueden iniciar, recuperar los archivos eliminados en mucho menos tiempo que el que se requiere para realizar esto a partir de la copia de seguridad o la reinstalación de sistemas operativos, detectar o eliminar hardware que utiliza rootkits para evitar la detección, y mucho más. Microsoft Diagnostics and Recovery Toolset es un componente integral del Paquete de Optimización de PC de Microsoft para Software Assurance, una solución dinámica de PC disponible para clientes de Software Assurance que reduce los costos de implementación de aplicaciones, posibilita la entrega de aplicaciones como servicios ayuda a controlar y administrar mejor los entornos de PC de la empresa. Desafíos para la recuperación de las PCs de la empresa Proteger los datos corporativos y de los empleados es una de las funciones de TI más importantes. Si bien muchos departamentos de TI pueden realizar copias de seguridad de los datos de la red de manera proactiva, por lo general son reactivos en la planifi cación de fallas de los sistemas de las PCs. -

Operating System Transactions
Operating System Transactions Donald E. Porter, Owen S. Hofmann, Christopher J. Rossbach, Alexander Benn, and Emmett Witchel Department of Computer Sciences, The University of Texas at Austin {porterde,osh,rossbach,abenn1,witchel}@cs.utexas.edu ABSTRACT Programming; D.4.7 [Operating Systems]: Organization Applications must be able to synchronize accesses to oper- and Design ating system resources in order to ensure correctness in the face of concurrency and system failures. System transac- General Terms tions allow the programmer to specify updates to heteroge- Design, Performance, Security neous system resources with the OS guaranteeing atomicity, consistency, isolation, and durability (ACID). System trans- Keywords actions efficiently and cleanly solve persistent concurrency Transactions, Operating Systems, TxOS, Race Conditions, problems that are difficult to address with other techniques. Transactional Memory For example, system transactions eliminate security vulner- abilities in the file system that are caused by time-of-check- 1. INTRODUCTION to-time-of-use (TOCTTOU) race conditions. System trans- actions enable an unsuccessful software installation to roll Applications often need to group accesses to operating system resources (such as files and signals) into logical units, back without disturbing concurrent, independent updates to the file system. just as multithreaded applications must group accesses to This paper describes TxOS, a variant of Linux 2.6.22 that shared data structures into critical regions. For example, implements system transactions. TxOS uses new implemen- local user and group accounts on Linux and similar oper- tation techniques to provide fast, serializable transactions ating systems are stored across three files that need to be /etc/passwd /etc/shadow with strong isolation and fairness between system transac- mutually consistent: , , and /etc/group. -

Operating System Transactions
Operating System Transactions Donald E. Porter, Owen S. Hofmann, Christopher J. Rossbach, Alexander Benn, and Emmett Witchel Department of Computer Sciences, The University of Texas at Austin {porterde,osh,rossbach,abenn1,witchel}@cs.utexas.edu ABSTRACT 1. INTRODUCTION Applications must be able to synchronize accesses to operating sys- Applications often need to group accesses to operating system tem resources in order to ensure correctness in the face of concur- resources (such as files and signals) into logical units, just as mul- rency and system failures. System transactions allow the program- tithreaded applications must group accesses to shared data struc- mer to specify updates to heterogeneous system resources with the tures into critical regions. For example, local user and group ac- OS guaranteeing atomicity, consistency, isolation, and durability counts on Linux and similar operating systems are stored across (ACID). System transactions efficiently and cleanly solve persis- three files that need to be mutually consistent: /etc/passwd, tent concurrency problems that are difficult to address with other /etc/shadow, and /etc/group. techniques. For example, system transactions eliminate security Applications currently struggle to make consistent updates to vulnerabilities in the file system that are caused by time-of-check- system resources. In current operating systems, individual system to-time-of-use (TOCTTOU) race conditions. System transactions calls are generally atomic and isolated from the rest of the system, enable an unsuccessful software installation to roll back without but it is difficult, if not impossible, to condense complex opera- disturbing concurrent, independent updates to the file system. tions into a single system call. -
(MSCS) Computer Forensics
Master of Science(Cyber Security) (MSCS) Computer Forensics (CSP-18) Block 1 Introduction to Computer Forensics Unit – 1: INTRODUCTION TO DIGITAL FORENSIC Unit – 2: COMPUTER FORENSICS INVESTIGATION PROCESS Unit – 3: DIGITAL EVIDENCE AND FIRST RESPONDER PROCEDURE Unit – 4: UNDERSTANDING STORAGE MEDIA AND FILE SYSTEM Master of Science(Cyber Security) (MSCS) EXPERT COMMITTEE Dr. P.K Behera (Chairman) Reader in Computer Science Utkal University Bhubaneswar, Odisha Dr.J.RMohanty (Member) Professor and HOD KIIT University Bhubaneswar, Odisha Sri PabitranandaPattnaik (Member) Scientist-E, NIC Bhubaneswar, Odisha Sri Malaya Kumar Das (Member) Scientist-E, NIC Bhubaneswar, Odisha Dr. Bhagirathi Nayak (Member) Professor and Head (IT & System) Sri Sri University, Bhubaneswar,Odisha Dr.Manoranjan Pradhan (Member) Professor and Head (IT & System) G.I.T.A Bhubaneswar, Odisha Sri Chandrakant Mallick (Convener) Consultant (Academic) School of Computer and Information Science Odisha State Open University Sambalpur, Odisha Master of Science(Cyber Security) (MSCS) Course Writers Aseem Kumar Patel Academic Consultant Odisha State Open University,Sambalpur Material Production Dr. Manas Ranjan Pujari Registrar Odisha State Open University, Sambalpur © OSOU, 2019. Promoting Use and Contribution of Open Education Resources is made available under a Creative Commons Attribution- ShareAlike4.0http://creativecommons.org/licences/by-sa/4.0 Unit Structure 1.1 Learning Objectives 02 1.2 Introduction 02 1.3 Definition of Computer Forensics 02 1.4 Cybercrime 03 1.5 -

Microsoft Diagnostics and Recovery Toolset
For Software Assurance Customers Microsoft® .. Microsoft SoftGrid® Application Virtualization .. Microsoft Asset Inventory Service Diagnostics and .. Microsoft Advanced Group Policy Management Recovery Toolset .. Microsoft Diagnostics and Recovery Toolset .. Microsoft System Center Desktop Error Monitoring Microsoft® Desktop Optimization Pack for Software Assurance Microsoft® Diagnostics and Recovery Toolset provides powerful, intuitive tools that help administrators recover PCs that have become unusable and easily identify root causes of system and network issues. If a desktop catastrophe does occur, it helps you quickly repair unbootable or locked-out systems, restore lost files without the timely process of using backup or reinstalling the operating system, and much more. Microsoft Diagnostics and Recovery Toolset is an integral component in the Microsoft Desktop Optimization Pack for Software Assurance solution, a dynamic desktop solution available to Software Assurance customers that reduces application deployment costs, enables delivery of applications as services, and allows for better management and control of enterprise desktop environments. Challenges of Corporate Desktop Recovery A fundamental responsibility of enterprise IT departments is to protect corporate and employee data. Although many take a proactive approach to backing up network data, they tend to be Microsoft® reactive in planning for desktop system failures. Unfortunately, the cost of not having an effective Diagnostics and diagnostics and recovery plan in place can be devastating. Recovery Toolset Microsoft Diagnostics and Recovery Toolset can save significant time and reduce the headaches associated with repairing and troubleshooting common system failures. System administrators may Powerful tools to now run powerful recovery tools on unbootable systems and can quickly restore failed systems accelerate desktop repair with minimal manual effort—in much less time than is required when restoring PCs from backup or reinstalling operating systems. -

List of MS-DOS Commands - Wikipedia, the Free Encyclopedia Page 1 of 25
List of MS-DOS commands - Wikipedia, the free encyclopedia Page 1 of 25 List of MS-DOS commands From Wikipedia, the free encyclopedia In the personal computer operating systems MS -DOS and PC DOS, a number of standard system commands were provided for common Contents tasks such as listing files on a disk or moving files. Some commands were built-in to the command interpreter, others existed as transient ■ 1 Resident and transient commands commands loaded into memory when required. ■ 2 Command line arguments Over the several generations of MS-DOS, ■ 3 Windows command prompt commands were added for the additional ■ 4 Commands functions of the operating system. In the current ■ 4.1 @ Microsoft Windows operating system a text- ■ 4.2 : mode command prompt window can still be ■ 4.3 ; used. Some DOS commands carry out functions ■ 4.4 /* equivalent to those in a UNIX system but ■ 4.5 ( ) always with differences in details of the ■ 4.6 append function. ■ 4.7 assign ■ 4.8 attrib ■ 4.9 backup and restore Resident and transient ■ 4.10 BASIC and BASICA commands ■ 4.11 call ■ 4.12 cd or chdir ■ 4.13 chcp The command interpreter for MS-DOS runs ■ 4.14 chkdsk when no application programs are running. ■ 4.15 choice When an application exits, if the command ■ 4.16 cls interpreter in memory was overwritten, MS- ■ 4.17 copy DOS will re-load it from disk. The command ■ 4.18 ctty interpreter is usually stored in a file called ■ 4.19 defrag "COMMAND.COM". Some commands are ■ 4.20 del or erase internal and built-into COMMAND.COM, ■ 4.21 deltree others are stored on disk in the same way as ■ 4.22 dir application programs. -
Windows Internals, Sixth Edition, Part 2
spine = 1.2” Part 2 About the Authors Mark Russinovich is a Technical Fellow in ® the Windows Azure™ group at Microsoft. Windows Internals He is coauthor of Windows Sysinternals SIXTH EDITION Administrator’s Reference, co-creator of the Sysinternals tools available from Microsoft Windows ® The definitive guide—fully updated for Windows 7 TechNet, and coauthor of the Windows Internals and Windows Server 2008 R2 book series. Delve inside Windows architecture and internals—and see how core David A. Solomon is coauthor of the Windows Internals book series and has taught components work behind the scenes. Led by a team of internationally his Windows internals class to thousands of renowned internals experts, this classic guide has been fully updated Windows developers and IT professionals worldwide, SIXTH for Windows 7 and Windows Server® 2008 R2—and now presents its including Microsoft staff. He is a regular speaker 6EDITION coverage in two volumes. at Microsoft conferences, including TechNet As always, you get critical, insider perspectives on how Windows and PDC. operates. And through hands-on experiments, you’ll experience its Alex Ionescu is a chief software architect and internal behavior firsthand—knowledge you can apply to improve consultant expert in low-level system software, application design, debugging, system performance, and support. kernel development, security training, and Internals reverse engineering. He teaches Windows internals courses with David Solomon, and is ® In Part 2, you will: active in the security research community. -
Exploration of Windows Vista Advanced Forensic Topics – Day 1
Windows Vista and NTFS File System Internals Exploration of Windows Vista Advanced Forensic Topics – Day 1 LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Windows Client Forensics (Windows Vista Advanced Topics) Transactional NTFS and Registry Explained LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved New Features Important Changes of Interest LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Self-Healing File System • Vista includes a “self-healing” function which can correct certain errors in the system • Vista maintains a list of hashes of known files and checks the hashes periodically • On non-system files Vista will validate the file metadata • Files whose hashes do not match or metadata is not valid will be replaced the next time the system is rebooted LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Self-Healing File System • Equivalent to Chkdsk and defrag processes constantly running in the background • This has the potential to decrease the usefulness of the free space and slack space on the disk as well as limit the ability to recover deleted files LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Self-Healing File System • Healed files can be identified by an examination of the event -
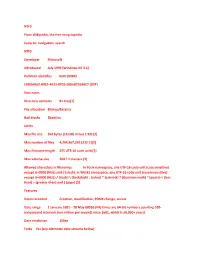
NTFS from Wikipedia, the Free Encyclopedia Jump To: Navigation, Search NTFS Developer Microsoft Introduced July 1993 (Windows
NTFS From Wikipedia, the free encyclopedia Jump to: navigation, search NTFS Developer Microsoft Introduced July 1993 (Windows NT 3.1) Partition identifier 0x07 (MBR) EBD0A0A2-B9E5-4433-87C0-68B6B72699C7 (GPT) Structures Directory contents B+ tree[1] File allocation Bitmap/Extents Bad blocks $badclus Limits Max file size 264 bytes (16 EiB) minus 1 KiB [2] Max number of files 4,294,967,295 (232-1)[2] Max filename length 255 UTF-16 code units[3] Max volume size 264 ? 1 clusters [2] Allowed characters in filenames In Posix namespace, any UTF-16 code unit (case sensitive) except U+0000 (NUL) and / (slash). In Win32 namespace, any UTF-16 code unit (case insensitive) except U+0000 (NUL) / (slash) \ (backslash) : (colon) * (asterisk) ? (Question mark) " (quote) < (less than) > (greater than) and | (pipe) [3] Features Dates recorded Creation, modification, POSIX change, access Date range 1 January 1601 ʹ 28 May 60056 (File times are 64-bit numbers counting 100- nanosecond intervals (ten million per second) since 1601, which is 58,000+ years) Date resolution 100ns Forks Yes (see Alternate data streams below) Attributes Read-only, hidden, system, archive, not content indexed, off-line, temporary File system permissions ACLs Transparent compression Per-file, LZ77 (Windows NT 3.51 onward) Transparent encryption Per-file, DESX (Windows 2000 onward), Triple DES (Windows XP onward), AES (Windows XP Service Pack 1, Windows Server 2003 onward) Single Instance Storage Yes Supported operating systems Windows NT family (Windows NT 3.1 to Windows NT 4.0, Windows 2000, Windows XP, Windows Server 2003, Windows Vista, Windows Server 2008) NTFS is the standard file system of Windows NT, including its later versions Windows 2000, Windows XP, Windows Server 2003, Windows Server 2008, and Windows Vista.[4] NTFS supersedes the FAT file system as the preferred file system for Microsoft͛s ͞Windows͟-branded operating systems. -

Computing at BSU User Guide Date: September 28, 1995
MEMO To: Faculty and Staff From: Shaun Loughney Subject: Computing at BSU User Guide Date: September 28, 1995 The following is the 1995-1996 updated inserts for your Computing at BSU User Guide. NOTE: CHAPTER 6 AND APPENDIXES B THRU E, G AND I, HAVE NO CBANGES. PLEASE RETAIN YOUR CURRENT REFERENCES. Take a look at what is new: The Center for Data Processing has added several new faces in the past year. See Chapter 1 for listing of current and new members of the Data Center. The not so new Student E-mail Server VARNEY is growing like wild fire. We have over 5000 users and are adding daily. See the Help Desk Documents BSU-01 and 02 for information on how to use the system. Several individuals on campus have pulled together and are designing a BSU Home Page for Internet access. The home page will eventually replace the Campus Wide Information System. See Chapters 2 and 5 for insight on what you will find at http://www.idbsu.edu. The Center for Data Processing has also started our own listserv, COMP-BSU. This is used to discuss campus computing issues, troubleshooting questions, and general topics of interest. See Help Desk Document Internet-05 to subscribe to listserv COMP-BSU. A couple of the Data Center's services have been improved to meet the campus needs: The dial-in access has received 16 new modems and authentication. To set up remote terminal access, see Help Desk Document COMM-05. The Faculty Computer Lab has upgraded their equipment. Several workstations are multi-media machines and have scanning ability. -

Copyrighted Material
Index Note to the Reader: Throughout this index boldfaced page numbers indicate primary discussions of a topic. Italicized page numbers indicate illustrations. socket identifiers, 756 A station addresses, 756 memory, 276–277, 884 AC adapters, 848 protocol, 239–240 Accelerated Graphics Port (AGP), 21, 21, SCSI, 144, 150–152 89–90, 90, 848 advanced attributes, 517–518, 517 access methods, media, 252–253 Advanced Micro Devices (AMD) processors, access points (APs), 259, 360, 385–386, 386, 848 103–104 access time, 122, 848 Advanced settings, System control panel for, Account Disabled option, 723 529–530 accounts, user advanced startup options, 566 in Windows 2000, 730–732, 730–732 in Windows 9x, 567 in Windows NT, 721–723, 722–724 in Windows 2000/XP, 567–568 in Windows XP, 736–737, 736 in Windows NT, 568–569 ACK (acknowledgment) packets, 748, 848 AGP (Accelerated Graphics Port), 21, 21, activation, Windows XP, 618–619, 896 89–90, 90, 848 Active Directory, 848 air, compressed, 282–283 active hubs, 254, 848 air cooling, 401 active-matrix screens, 47, 848 alignment, printhead, 200 active partitions, 590, 848 all-black printer pages, 203–204 active termination, 149, 849 allocation units, 591–592, 849 active windows, 502, 503 alpha releases, 434 actuator arms, 120, 120, 849 alternative operating systems, 468–469 adapter cards, 39, 849 Linux, 469–470 for building PCs, 289 Mac OS, 469 dislodged, 449 AMD (Advanced Micro Devices) processors, installing, 321–324, 322 103–104 modems, 41, 41 American Standard Code for Information networking, 704 Interchange