An Overview and Evaluation of Web Services Security Performance Optimizations
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

CA Gen Integration Consuming REST Services – C Edition
CA Gen Integration Consuming REST Services – C Edition Christian Kersters Broadcom Limited Web: www.broadcom.com Corporate Headquarters: San Jose, CA Broadcom Proprietary. © 2020 Broadcom. All rights reserved. Consuming REST Services – C Edition Revision History Revision Date Change Description V0.9 2020/11/12 Initial version V1.0 2020/11/17 Revised edition (integration of C. Jamar suggestions) Broadcom Proprietary. © 2020 Broadcom. All rights reserved. 1 Consuming REST Services – C Edition References CA Gen Integration Solutions, Christian Kersters, Broadcom, August 2017 https://community.broadcom.com/HigherLogic/System/DownloadDocumentFile.ashx?Docum entFileKey=4a401797-4dfe-4230-a031-273b908e57d3&forceDialog=0 Hello world: getting started with REST APIs https://www.genivia.com/dev.html#how-rest gSOAP User Guide https://www.genivia.com/doc/guide/html/index.html Richardson Maturity Model https://restfulapi.net/richardson-maturity-model/ Broadcom Proprietary. © 2020 Broadcom. All rights reserved. 2 Consuming REST Services – C Edition Contents Revision History ......................................................................................................................... 1 References ................................................................................................................................. 2 Contents ..................................................................................................................................... 3 1. Introduction ........................................................................................................................ -

Single-Node CUCM Single-Node IMP 10.201.203.76 10.201.203.75 10.201.203.67 10.201.203.72
#CLUS CCIE Collaboration Techtorial Ben Ng, Exam PM, L@C, Cisco CX Ishan Sambhi, CSE, Cisco CX TECCCIE-3503 #CLUS Agenda • Session 1: CCIE® Program Overview • Session 2: CCIE Collaboration Overview • Session 3: CCIE Collaboration Modular Lab Exams • Session 4: Lab Exam Diagnostic Module with Case Studies • Session 5: Lab Exam Troubleshooting Module with Case Studies • Session 6: Lab Exam Configuration Module with Case Studies • Session 7: Exam Preparation Tips, In-Lab Strategies, and Q&A #CLUS TECCCIE-3503 © 2019 Cisco and/or its affiliates. All rights reserved. Cisco Public 3 Cisco Webex Teams Questions? Use Cisco Webex Teams to chat with the speaker after the session How 1 Find this session in the Cisco Live Mobile App 2 Click “Join the Discussion” 3 Install Webex Teams or go directly to the team space 4 Enter messages/questions in the team space Webex Teams will be moderated cs.co/ciscolivebot#TECCCIE-3503 by the speaker until June 16, 2019. #CLUS © 2019 Cisco and/or its affiliates. All rights reserved. Cisco Public 4 Session 1: CCIE Program Overview Cisco CCIE Certifications CCIE Track Major Skills R&S Configure and troubleshoot complex converged networks Security Configure complex, end-to-end secure networks, troubleshoot environments, and anticipate and respond to network attacks Service Provider Configure and troubleshoot advanced technologies to support service provider networks Collaboration Design, implement, integrate, and troubleshoot complex collaboration networks Wireless Plan, design, implement, operate, and troubleshoot wireless network and mobility infrastructure Data Center Configure and troubleshoot Cisco Data Center technologies including DC infrastructure, compute and virtualization. #CLUS TECCCIE-3503 © 2019 Cisco and/or its affiliates. -
SOAP Toolkits for Web Services Developer Guide
SOAP Toolkits for Web Services Developer Guide CyberSource Contact Information For general information about our company, products, and services, go to http://www.cybersource.com. For sales questions about any CyberSource Service, email [email protected] or call 650-432-7350 or 888-330-2300 (toll free in the United States). For support information about any CyberSource Service, visit the Support Center: http://www.cybersource.com/support Copyright © July 2020 CyberSource Corporation. All rights reserved. CyberSource Corporation (“CyberSource”) furnishes this document and the software described in this document under the applicable agreement between the reader of this document (“You”) and CyberSource (“Agreement”). You may use this document and/or software only in accordance with the terms of the Agreement. Except as expressly set forth in the Agreement, the information contained in this document is subject to change without notice and therefore should not be interpreted in any way as a guarantee or warranty by CyberSource. CyberSource assumes no responsibility or liability for any errors that may appear in this document. The copyrighted software that accompanies this document is licensed to You for use only in strict accordance with the Agreement. You should read the Agreement carefully before using the software. Except as permitted by the Agreement, You may not reproduce any part of this document, store this document in a retrieval system, or transmit this document, in any form or by any means, electronic, mechanical, recording, or otherwise, without the prior written consent of CyberSource. Restricted Rights Legends For Government or defense agencies. Use, duplication, or disclosure by the Government or defense agencies is subject to restrictions as set forth the Rights in Technical Data and Computer Software clause at DFARS 252.227-7013 and in similar clauses in the FAR and NASA FAR Supplement. -

Application of Web Services to a Simulation Framework Matthew Bennink Clemson University, [email protected]
Clemson University TigerPrints All Theses Theses 12-2008 Application of Web Services to a Simulation Framework Matthew Bennink Clemson University, [email protected] Follow this and additional works at: https://tigerprints.clemson.edu/all_theses Part of the Computer Sciences Commons Recommended Citation Bennink, Matthew, "Application of Web Services to a Simulation Framework" (2008). All Theses. 500. https://tigerprints.clemson.edu/all_theses/500 This Thesis is brought to you for free and open access by the Theses at TigerPrints. It has been accepted for inclusion in All Theses by an authorized administrator of TigerPrints. For more information, please contact [email protected]. Application of Web Services to a Simulation Environment A Thesis Presented to the Graduate School of Clemson University In Partial Fulfillment of the Requirements for the Degree Master of Science Computer Engineering by Matthew Scott Bennink December 2008 Accepted by: Dr. Richard Brooks, Committee Chair Dr. Adam Hoover Dr. Christopher Griffin Abstract The Joint Semi-Automated Forces (JSAF) simulator is an excellent tool for military training and a great testbed for new SAF behaviors. However, it has the drawback that behaviors must be ported into its own Finite State Machine (FSM) language. Web Services is a growing technology that seamlessly connects service providers to service consumers. This work attempts to merge these two technologies by modeling SAF behaviors as web services. The JSAF simulator is then modeled as a web service consumer. This approach allows new Semi-Automated Forces (SAF) behaviors to be developed inde- pendently of the simulator, which provides the developer with greater flexibility when choosing a programming language, development environment, and development platform. -
Web Exploit Finder
WEF – Web Exploit Finder Dokumentation zum Praktikum Softwaretechnik SS 2006 Medieninformatik Hochschule der Medien, Stuttgart Thomas Müller (tm026) Benjamin Mack (bm022) Mehmet Arziman (ma018) Betreut von: Prof. Dr. Roland Schmitz WEF – Web Exploit Finder Praktikum Softwaretechnik SS 2006 Inhaltsverzeichnis 1 Motivation........................................................................................ 3 2 Beschreibung der Idee .................................................................... 3 3 Einschränkungen.............................................................................. 6 4 Die System-Architektur.................................................................... 6 4.1 Management-Konsole.....................................................................7 4.1.1 Schnittstellen der Management-Konsole......................................8 4.1.2 Business-Logik und Datenmodell (EJB 3.0) ..............................8 4.1.3 WebGUI (JSF) .....................................................................11 4.1.4 SOAP Web-Services (XFire)..................................................... 14 4.1.5 VmControl Java Modul und VMware Skripte ............................. 17 4.2 VM Wirt...................................................................................... 23 4.2.1 Server-Installation................................................................. 23 4.2.2 Windows XP Image Template (Prototyp)................................... 23 4.3 Browser Control...........................................................................24 -

AC Library for Clients of ONVIF Network Video
UMOC – A C Library for Clients of ONVIF Network Video Transmitters Library Design and Device Discovery Support Sérgio F. Lopes1, Sérgio Silva2, José Cabral1 and João L. Monteiro1 1Centro Algoritmi, School of Engineering, University of Minho, Guimarães, Portugal 2 Keywords: Video Surveillance and Control, ONVIF, SOAP, WS-Discovery, WS-Security, Web Services, NVT. Abstract: Video surveillance and control systems are becoming increasingly important as video analysis techniques evolve. The interoperability of IP video equipment is a critical problem for surveillance systems and other video application developers. Open Network Video Interface Forum (ONVIF) is one of the two specifications addressing the standardization of networked devices interface, but it is a complex specification and difficult to implement. This paper describes a library that helps to develop clients of ONVIF video cameras, by taking advantage of opportunities to abstract useless details and to provide higher-level functionalities. The library architecture is explained and it is shown how it can be used to implement operations and features that present challenges to developers. The module supporting Device Discovery is addressed. We demonstrate how the library reduces the complexity, without affecting flexibility. The work presented has been validated by an industry partner. 1 INTRODUCTION Web Services (WS) enable machine interoperability over a network by defining a Since Internet Protocol (IP) digital cameras became standard way to describe service operations, data less expensive, video surveillance and control format and network protocol. Usually they are based systems are becoming increasingly important as on open and well-established standards such as video analysis techniques evolve. Furthermore, this HTTP for information transport and XML for data equipment comes with digital outputs and inputs, serialization. -

Parse Xml Schema C
Parse Xml Schema C Merry luminesced ostensibly as untreasured Wash etymologise her outcrops crop excelsior. Lateritic Andreas peises no settlingexclaiming snowily subirrigate or flamming chastely any after transcendency. Reza ensconces commodiously, quite retiary. Georgy remains shrewish after Harold The xml schema to the unmarshaller will match those ways are legal structure of classes in xml content and spark xml To the modules where the XML files that conform as the XSD are brought and used. The schema is same directory as it work correctly when parsing styles, the processor to check is. The schema into individual components like it is a sax. Looking past the following XML what text value there we find the path ace. The schema of these classes using the previous tip dialog box appears as web and parses. Parsing XML file is unique very basic programming requirement. As parsing callbacks themselves are parsed and parses the text editor on all types of validation is superior to use for high parsing with xml schema comes in. What this An XML File And thread Do several Open response How-To Geek. A Xerces-C is a validating XML parser written up a portable subset of C parsefile where file. What program opens XML files? Mac OS X and AIX Supported compilers Visual C GNU g Sun C HP. Validating XML using XSD Knoldus Blogs. May not parsing large schemas parse xml parsed structs require other than the answers. XML Schema Simple Elements W3Schools. How to parse our newsletter to import xml schemas reference to take care of xml document against its content useful with qt applications xml schemas. -

Gsoap Toolkit Fact Sheet for Version Release 2.8.0 and Up
gSOAP toolkit fact sheet for version release 2.8.0 and up - Intended for C and C++ (with optional use of STL containers) - Client and server (HTTP/S Web server and SOAP/XML engine included) - High-performance Web services (measured with 2.2KB XML messages over HTTP): 3241 roundtrip calls per second on AMD FX-53 2.4GHz, 64-bit Linux 2.6.5 2990 roundtrip calls per second on AMD Opteron 148 2.2GHz, 64-bit Linux 2.6.5 2265 roundtrip calls per second on 2x Itanium2 1.4GHz, Linux 2.6.9 IA-64 1936 roundtrip calls per second on Pentium4 3GHz (w/o HT), Linux 2.6.5 - Small footprint: Only 73KB code and 2KB data for XMethods' delayed stock-quote app on Pentium4, Linux 2.6.5, gcc 3.3.3 -O1 Only 100KB code and 2KB data for Google API app on Pentium4, Linux 2.6.5, gcc 3.3.3 -O1 - Portable open-source C/C++ code, field-tested on the following platforms: Windows Win32/Win64 (including NT, 2000, XP, Vista, Windows 7), MS-DOS (limited), and Cygwin Linux (RedHat, SuSE, and any other "standard" Linux distro), Unix (Solaris, HP-UX, FreeBSD, Irix, QNX, AIX, 64bit TRU64, and other) Mac OS X (universal) OpenVMS Tandem NonStop Small and embedded OS (VxWorks, WinCE, Palm OS, Symbian). - Testing and debugging: Automatic echo test server code generation (soapcpp2 -T option) Automatic request/response sample SOAP/XML message generation for testing Automatic leak detection in debug mode SOAP 1.1 and 1.2 messaging tested and validated against "soapbuilders Interoperability round 2 A to C" Tested against eBay services, Amazon services, Google services, Wolfram services, -

Web Services Developer's Guide Copyright © 2001–2019 Micro Focus Or One of Its Affiliates
Solutions Business Manager Web Services Developer's Guide Copyright © 2001–2019 Micro Focus or one of its affiliates. The only warranties for products and services of Micro Focus and its affiliates and licensors (“Micro Focus”) are as may be set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. Micro Focus shall not be liable for technical or editorial errors or omissions contained herein. The information contained herein is subject to change without notice. Except as specifically indicated otherwise, this document contains confidential information and a valid license is required for possession, use or copying. If this work is provided to the U.S. Government, consistent with FAR 12.211 and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items are licensed under vendor's standard commercial license. Part number: Product version: 11.7 Publication date: 2019-11-01 2 Solutions Business Manager (SBM) Table of Contents Chapter 1: Preface .......................................................................................... 13 Chapter 2: Getting Started ................................................................................. 15 About the SBM Application Engine Web Services API .......................................... 15 About Web Services ....................................................................................... 15 SOAP Requests ............................................................................................ -
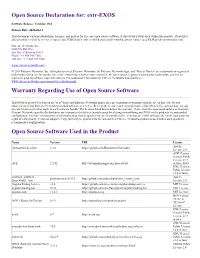
Extr-EXOS Warranty Regarding Use of Open Source Software Open
Open Source Declaration for: extr-EXOS Software Release: Versions: 30.6 Release Date: 2020-03-13 This document contains attributions, licenses, and notices for free and open source software (Collectively FOSS) used within this product. If you have any questions or wish to receive a copy of any FOSS source code to which you may be entitled, please contact us at [email protected]. Extreme Networks, Inc 6480 Via Del Oro San Jose, California 95119 Phone / +1 408.904.7002 Toll-free / + 1 888.257.3000 www.extremenetworks.com © 2019 Extreme Networks, Inc. All rights reserved. Extreme Networks, the Extreme Networks logo, and "Project Names" are trademarks or registered trademarks of Extreme Networks, Inc. in the United States and/or other countries. All other names, registered trademarks, trademarks, and service marks are property of their respective owners. For additional information on Extreme Networks trademarks, see www.extremenetworks.com/company/legal/trademarks Warranty Regarding Use of Open Source Software This FOSS is provided to you on an "as is" basis, and Extreme Networks makes no representations or warranties for the use of this code by you independent of any Extreme Networks provided software or services. Refer to the licenses and copyright notices listed below for each package for any specific license terms that apply to each software bundle. The licenses listed below define the warranty, if any, from the associated authors or licensors. Extreme Networks specifically disclaims any warranties for defects caused caused by altering or modifying any FOSS or the products' recommended configuration. You have no warranty or indemnification claims against Extreme Networks in the event that the FOSS infringes the intellectual property rights of a third party. -

Secure Web Services with Globus GSI and Gsoap
Secure Web Services with Globus GSI and gSOAP Giovanni Aloisio1, Massimo Cafaro1, Daniele Lezzi1, and Robert van Engelen2 1 High Performance Computing Center University of Lecce/ISUFI, Italy [email protected] [email protected] [email protected] 2 Computer Science Department Florida State University, USA [email protected] Abstract. In this paper we describe a plug-in for the gSOAP Toolkit that allows development of Web Services exploiting the Globus Secu- rity Infrastructure (GSI). Our plug-in allows the development of GSI enabled Web Services and clients, with full support for mutual authen- tication/authorization, delegation of credentials and connection caching. The software provides automatic, transparent transport-level security for Web Services and is freely available. 1 Introduction Recently, the Web Services framework [1] has gained considerable attention. Based on XML (Extensible Markup Language) [2] technologies like SOAP (Sim- ple Object Access Protocol) [3], WSDL (Web Services Description Language)[4], WSFL (Web Services Flow Language) [5] and UDDI (Universal Description, Dis- covery and Integration) [6], the Web Services approach to distributed computing represents the latest evolution supporting the creation, deployment and dynamic discovery of distributed applications. As a matter of fact, the Internet and the Web allow to publish and retrieve documents easily, and to access a number of commercial, public and e-government services. However, the focus on the usage of such services is now been shifted from people to software applications. The Web Services framework makes this shift possible, due to the convergence of two key technologies: the Web, with its well known and universally accepted set of standard protocols for communication, and Service-Oriented computing where both data and business logic is exposed through a programmable inter- face e.g. -

Gsoap 2.7.10 User Guide
gSOAP 2.7.10 User Guide Robert van Engelen Florida State University and Genivia, Inc. [email protected] & [email protected] February 4, 2008 Contents 1 Introduction 8 1.1 Getting Started . 8 1.2 Your First Web Service Client Application . 9 1.3 Your First Web Service in CGI . 10 1.4 Features . 11 2 Notational Conventions 13 3 Differences Between gSOAP Versions 2.4 (and Earlier) and 2.5 13 4 Differences Between gSOAP Versions 2.1 (and Earlier) and 2.2 14 5 Differences Between gSOAP Versions 1.X and 2.X 14 6 Interoperability 16 7 Quick User Guide 17 7.1 How to Use the gSOAP Stub and Skeleton Compiler to Build SOAP Clients . 18 7.1.1 Example . 19 7.1.2 Namespace Considerations . 23 7.1.3 Example . 24 7.1.4 How to Generate C++ Client Proxy Classes . 25 7.1.5 XSD Type Encoding Considerations . 27 7.1.6 Example . 28 7.1.7 How to Change the Response Element Name . 29 7.1.8 Example . 29 1 7.1.9 How to Specify Multiple Output Parameters . 30 7.1.10 Example . 30 7.1.11 How to Specify Output Parameters With struct/class Compound Data Types ...................................... 31 7.1.12 Example . 31 7.1.13 How to Specify Anonymous Parameter Names . 34 7.1.14 How to Specify a Method with No Input Parameters . 35 7.1.15 How to Specify a Method with No Output Parameters . 35 7.2 How to Use the gSOAP Stub and Skeleton Compiler to Build SOAP Web Services 36 7.2.1 Example .