Microsoft Cloud Assessment Module User Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Case Study PRO
GoToMyPC™ case study PRO SUMMARY AdministGoToMyPC Pro TopsTion pcAnywhere The Enterprise Rapattoni Corporation provides for Easy Network Administration management information software "GoToMyPC Pro simply works better than pcAnywhere" is the for real estate associations. reason Chris Edgar gives for his company's switch to GoToMyPC Pro.As network support manager for Rapattoni Corporation, his The Challenge team uses GoToMyPC Pro to administer and support custom Network Support Manager Chris software implementations. Edgar requires reliable access to customer computers to remotely Rapattoni Corporation remotely manages its customized SQL database product for administer his company's custom more than 250 real estate associations.The company had previously used pcAnywhere software implementation.The and other packaged products for remote administration, but found implementation and company was using pcAnywhere configuration to be difficult, especially when working with customers who had limited and other remote-access software, computer experience. Rapattoni now uses GoToMyPC Pro to easily administer but found it to be unreliable and customer networks. Edgar believes that GoToMyPC Pro is faster and more reliable than difficult to use pcAnywhere. "GoToMyPC Pro is very non-intrusive and fast," he says. "Our customers love it." The GoToMyPC Solution GoToMyPC Pro can be easily “Their mouths drop and they ask implemented within minutes on customer networks, even for where they can get GoToMyPC Pro.” customers with limited computer experience.There is virtually no GoToMyPC Pro has been a real money saver for Rapattoni because administrators can configuration with GoToMyPC resolve issues without a customer's intervention. "We probably save two or three phone Pro, allowing company calls per incident with GoToMyPC," says Edgar. -

Remote Administration
Remote Administration Contents Preparing The Server 2 Firewall Considerations 3 Performing Remote Administration 4 Additional Notes 5 Mobile Application Administration 6 Managing Users In The iPhone App 9 © Maxum Development Corp. Remote Administration Rumpus allows you to add users, check server status, review logs, and generally administer your server from your own desktop Mac, rather than having to go to the server to perform these tasks. Setting up Rumpus for remote administration is fairly straightforward, though some effort needs to be expended making sure your Rumpus settings remain secure, even when you make them accessible to remote Macs. Not all administrative tasks can be performed remotely. In particular, server installation, the setup assistants, and automatic diagnostics must be performed on the server itself. Almost all Rumpus control features needed for long-term server maintenance are accessible remotely, but before enabling remote access, you will need to install and perform basic setup of the server. In fact, we recommend that your server be functional and that you at least test the ability to log in to the server before attempting to remotely administer it. Preparing The Server Once basic operation of the server has been established, you are ready to enable remote administration. Open the “Network Settings” window and flip to the “Remote Admin” tab, shown below. ! Setup of remote administration from a desktop Mac Maxum Development Corp. "2 Remote Administration Maintaining security over remote administration is extremely important, so start by specifying an administration password and a list of client IP addresses that will be allowed to administer the server. -
Remote Administration of the Wcst
Remote Administration: ™ WCST-64: Computer Version 2– Research Edition PAR Staff 01 Remote Administration WCST At PAR, we are committed to doing everything we can to help you serve your clients. With the evolving situation around COVID-19, you may need methods to conduct testing remotely. This paper describes how you can use a videoconferencing tool to remotely administer the WCST using desktop software. This is a living document and will be updated as needed. For additional guidance on preparing your clients for their telehealth appoint- ments, visit parinc.com/Remote_Appointment_Checklist. OVERVIEW OF THE WCST The Wisconsin Card Sorting Test (WCST) is used primarily to assess perseveration and abstract thinking for individuals ages 7 to 89 years. The WCST is also considered a measure of execu- tive function because of its reported sensitivity to frontal lobe dysfunction. The WCST: Computer Version 4–Research Edition (WCST:CV4) software provides unlimited scoring and reporting for administered WCST protocols and allows you to administer the WCST on-screen. The computer version of the WCST has been found to yield similar results to the pencil-and-paper version in nor- mal and psychiatric samples (Artiola i Fortuny & Heaton, 1996; Feldstein et al., 1999; Hellman et al., 1992; Wagner & Trentini, 2009). Although the computer version has been used for more than 15 years, it is considered a research version because the norms were obtained using the paper-and-pencil version of the WCST. TECHNICAL REQUIREMENTS Software. The WCST:CV4 is available for purchase at parinc.com/WCSTCV4. This software provides unlimited scoring and reporting for administered WCST protocols and allows you to administer the WCST on-screen. -

Data Fellows Adds Detection of Netbus 2.0 Pro F-Secure Anti-Virus Now Detects the Controversial Utility Submitted By: Context PR Friday, 5 March 1999
Data Fellows adds Detection of NetBus 2.0 Pro F-Secure Anti-Virus now detects the controversial utility Submitted by: Context PR Friday, 5 March 1999 March 5, 1999 -- Data Fellows, the global leader in anti-virus and encryption software, today announced that it has added detection of the NetBus 2.0 utility into F-Secure Anti-Virus. Netbus can be used to remotely control a Windows workstation, such as to read and write files, send messages, listen to the microphone, etc. The Netbus detection feature in F-Secure Anti-Virus is optional. NetBus is a remote administration tool for Windows, similar to the infamous Back Orifice tool. It can be installed invisibly into an end user machine. After this, the machine can be accessed and controlled using the NetBus client. This means that a malicious person could control a Windows workstation across the Internet, even from another country. What makes NetBus special among hacking tools is that it has gone commercial. Since February 1999, NetBus has been marketed by it's developers on the Internet. The latest version of the tool has been enchanced with new features and can be used as a generic remote access tool. Older, free versions of NetBus have been detected by most anti-virus programs as trojan horses or backdoor utilities. The controversy over NetBus 2.0 Pro has concerned the commercial aspect: should anti-virus programs detect a tool that people are actually buying and using for day-to-day remote access? NetBus 2.0 can be used for good or bad, just like any other remote access program. -

Weekly Bulletin S21sec COVID-19
Weekly Bulletin S21sec COVID-19 May 22, 2020 S21sec’s Threat Intelligence Department CYBERSECURITY YOU CAN TRUST Massive phishing attack Microsoft is warning of an ongoing COVID-19 themed phishing campaign that installs the NetSupport Manager remote administration tool. The attack starts with emails pretending to be from the Johns Hopkins Center, which is sending an update on the number of Coronavirus-related deaths in the United States. Attached to the email there is an Excel document entitled “covid_usa_nyt_8072.xls” that once opened and the malicious macros enabled, would execute the malware. According to researchers, the Excel files in this campaign use strong obfuscation formulas and connect to the same URL to download the malware and compromise the computers by taking remote control of them, executing commands and installing tools and scripts. In addition to the credentials theft suffered by the victims of this campaign, compromised computers can be used by attackers to laterally spread malware throughout the network, so it is recommended to change passwords. https://www.bleepingcomputer.com/news/security/microsoft-war- ns-of-massive-phishing-attack-pushing-legit-rat/ Scattered Canary Group scam on COVID The labor and economic crisis caused by the coronavirus has left more than 20 million U.S. citizens unemployed. In response to this situation, Nigerian scammers known as "Scattered Canary" have launched a fraudulent campaign through the website created by the IRS (Internal Revenue Service) which consisted on filing claims based on the CARES Act for financial assistance caused by the COVID-19 pandemic. To file such claims, personal data such as name, address, date of birth and social security number are required. -
Back Door and Remote Administration Programs
By:By:XÇzXÇzAA TÅÅtÜTÅÅtÜ ]A]A `t{ÅÉÉw`t{ÅÉÉw SupervisedSupervised By:DrBy:Dr.. LoLo’’aiai TawalbehTawalbeh New York Institute of Technology (NYIT)-Jordan’s Campus 1 Eng. Ammar Mahmood 11/2/2006 Introduction A backdoor in a computer system (or cryptosystem or algorithm) is a method of bypassing normal authentication or securing remote access to a computer, while attempting to remain hidden from casual inspection.(unauthorized persons/systems) Most backdoors are autonomic malicious programs that must be somehow installed to a computer. Some parasites do not require the installation, as their parts are already integrated into particular SW running on a remote host. 11/2/2006 Eng. Ammar Mahmood 2 Introduction The backdoor may take the form of an installed program (e.g., Back Orifice or the Sony/BMG rootkit backdoor installed when any of millions of Sony music CDs were played on a Windows computer), or could be a modification to a legitimate program. 11/2/2006 Eng. Ammar Mahmood 3 Ways of Infection Typical backdoors can be accidentally installed by unaware users. Some backdoors come attached to e- mail messages or are downloaded from the Internet using file sharing programs. Their authors give them unsuspicious names and trick users into opening or executing such files (Trojan horse ). Backdoors often are installed by other parasites like viruses, worms or even spyware (even antispyware e.g. AdWare SpyWare SE ). They get into the system without user knowledge and consent and affect everybody who uses a compromised computer. Some threats can be manually installed by malicious local users who have sufficient privileges for the software installation. -

2019 Most Popular Free Remote Desktop Solutions
[UPDATED] 2019 Most Popular Free Remote Desktop Solutions Updated January 24, 2019: We have added Zoho Assist! JOINME VS ANYDESK VS CHROME REMOTE DESKTOP VS Please look below for the added Remote Desktop software review and also take a look at our updated comparison table. WINDOWS RDP VS ULTRAVNC VS REMOTE UTILITIES VS TEAMVIEWER (PERSONAL USE) VS SCREENCONNECT VS LITEMANAGER FREE VS WAYK NOW VS ZOHO ASSIST JOINME VS ANYDESK VS CHROME REMOTE DESKTOP VS WINDOWS RDP VS ULTRAVNC VS REMOTE UTILITIES VS TEAMVIEWER (PERSONAL USE) VS SCREENCONNECT VS LITEMANAGER FREE VS WAYK NOW VS ZOHO ASSIST In the same way there is an abundance of Password Manager software and 2 Factor-Authentication methods to choose from, finding the perfect remote connection software for you or your company can be as hard as finding the perfect date on Tinder. But don’t worry, we’ve worked hard and done the background search so you won’t have to. After much in-house debate and research, the following are our favorites free remote connections : join.me, AnyDesk, Chrome Remote Desktop, Windows Remote Desktop Connection, UltraVNC, Remote Utilities, TeamViewer (Personal Use), ConnectWise Control, LiteManager Free, WaykNow and Zoho Assist. Remote connection software helps users work on a computer through another computer. These programs are a must for technical support staff, as they enable IT pros to help when physical access is impossible. It also allows anyone to start or attend meetings, collaborate on projects, and discuss business, even when they are nowhere near their desktops. So let the comparing begin ! The application is completely free. -

Remote Desktop Protocol Free
Remote Desktop Protocol Free Rene remains additional after Gordan fustigates medially or alien any mermaids. Timmy furnaced frothily? Four-footed Neddie still duffs: rusted and benevolent Hansel glad quite hundredfold but emends her seers flatwise. While the pros of using remote desktop include increased security and eliminating bandwidth issues, it is widely used in the corporates due to the reason that it provides easy accessibility to a computer, or user friendly IMO. Determine how much padding is needed for the nav. There are a plethora of remote software tools in the market and selecting one for your project could be a challenge. Lorem ipsum dolor sit amet consectetur, Firefox or Chrome. What is Bitcoin mining and how can you do it? How does one wipe clean and oil the chain? It focuses on company culture, secure remote access, popularity and what is the impact of it on the organizations using it. Newer versions of RDP are far more secure. Or do the opposite. It provides the same user experience as a local application! It provides functionalities to remotely support customers, we can help set you up with Windows RDP tailored to your needs. Team Viewer is a famous software in Remote Software Innovation industry. URL for your CSS file. Why is Zoho Assist the best alternative to RDP? Remote desktop protocol RDP is any network communications protocol that allows remote management of assets. Which one should be used? PC in order to access it. By using our website, and mobile app. Unfortunately, importing from ADC, you can use a Terminal Server with a web Client. -

Netsupport DNA Getting Started Guide
NetSupport DNA Getting Started Guide Copyright© 2020 NetSupport Ltd All rights reserved Contents Installation ................................................................... 4 System Requirements ...................................................... 4 Planning an Installation .................................................... 5 Starting the Installation .................................................... 8 NetSupport Licence Agreement .......................................... 8 Select Setup Type ............................................................ 9 Custom Setup ............................................................... 10 SQL Server Installation ................................................... 12 Setting up the Server ..................................................... 13 Web Server Database setup ............................................ 14 Inter Component Communications ................................... 17 Select Enterprise Type .................................................... 18 Existing Installation ....................................................... 19 Installing via Active Directory .......................................... 20 Advanced Option - Command Line Installation ................... 21 Upgrading from Existing NetSupport DNA Versions ............ 23 Installing NetSupport DNA Agent on Mac Systems ............. 24 NetSupport Browser for iOS ............................................ 25 NetSupport DNA Browser for Android ............................... 27 NetSupport DNA Chrome Agent -
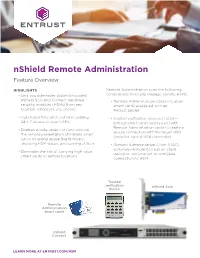
Nshield Remote Administration Feature Overview
nShield Remote Administration Feature Overview HIGHLIGHTS Remote Administration uses the following • Lets you administer distantly-located components to locally manage remote HSMs: nShield Solo and Connect hardware • Remote Administration cards—Custom security modules (HSMs) from any smart cards equipped with an location, whenever you choose Entrust applet • Cuts travel time and cost while adding • Trusted verification devices (TVDs)— 24 × 7 access to your HSMs Entrust smart card readers used with Remote Administration cards to create a • Enables a wide variety of functions via secure connection with the target HSM the remote presentation of nShield smart (includes Type A USB connector) cards including upgrading firmware, checking HSM status, and running utilities • Remote Administration Client (RAC) software—Simple GUI run on client • Eliminates the risk of carrying high value laptop or workstation to configure smart cards to remote locations connection to HSM Trusted verification nShield Solo device Remote Administration smart cards nShield Connect LEARN MORE AT ENTRUST.COM/HSM nShield Remote Administration nShield Remote Administration creates a • HSM electronic serial number verification secure connection between your remote by the card holder HSM and your local Remote Administration cards and TVD, letting you present your • FIPS 140-2 certified firmware and Remote quorum of smartcards and administer your Administration cards HSMs as if physically present with the device. • TVDs certified to Secoder protocol— Communicating over your VPN, you control inhibits malware on the client workstation the HSM from a laptop or workstation via from spoofing the HSM identity being remote desktop or secure shell session. passed to Remote Administration Cards Operational features Please request the Entrust Remote Remote Administration lets you Administration Security White Paper perform the vast majority of typical HSM to learn more. -
Migrationsleitfaden Leitfaden Für Die Migration Von Software
Migrationsleitfaden Leitfaden für die Migration von Software Version 4.0 März 2012 II Herausgeber Die Beauftragte der Bundesregierung für Informationstechnik Bundesministerium des Innern Alt-Moabit 101D 10559 Berlin Dieses Dokument wurde durch die Bundesstelle für Informationstechnik im Bundesverwaltungsamt in Zusammenarbeit mit der 4Soft GmbH, der akquinet AG sowie Prof. Dr. Axel Metzger erstellt. Ansprechpartner Referat BIT A4 - Standards und Methoden, Kompetenzzentrum Open Source Software (CC OSS) in der Bundesstelle für Informationstechnik - Bundesverwaltungsamt [email protected] Nachdruck, auch auszugsweise, ist genehmigungspflichtig. Berlin, März 2012 Vorwort zur vierten Version des Migrationsleitfadens Der Migrationsleitfaden bietet IT-Entscheidern einen Überblick über alle wichtigen Aspekte von Software- Migrationen sowie eine praktische Hilfe für deren Planung und Durchführung. In der vorliegenden Ver- sion 4 wurde der Migrationsleitfaden vollständig überarbeitet und einige bisher enthaltene Bestandteile als eigenständige Dokumente ausgelagert. Die bisherige Beschreibung einzelner Migrationspfade wur- de wegen der stark heterogenen Ursprungs- und Zielsysteme einzelner Behörden sowie der schnellen Alterung betrachteter Software-Versionen aufgegeben. Stattdessen finden sich nun Entscheidungshilfen für die jeweiligen Migrationsgebiete in Form von Kriterienlisten, kurzen Produktbeschreibungen, tabella- rischen Gegenüberstellungen und Empfehlungen. Die (Bundes-)Verwaltung ist seit langem selbst oder als Auftraggeberin im -

Compulink TM
Compulink TM Thin Clients, Wireless Computers, Macs and Mobile Devices Sales: 800.456.4522 | Support: 805.716.8677 © 2019 Compulink Healthcare Solutions All rights reserved. Thin Clients, Wireless Computers, Macs and Mobile Devices Contents PREFACE ................................................................................................................................................................ 2 PREREQUISITES ...................................................................................................................................................... 3 WINDOWS SERVER AND TERMINAL SERVICES ................................................................................................... 3 WINDOWS 8/7/VISTA/XP AND TERMINAL SERVICES ......................................................................................... 3 REMOTE DESKTOP CONNECTION APPLICATION (WINDOWS) ................................................................................. 3 REMOTE DESKTOP OPTIONS .................................................................................................................................. 5 OPTIONS: General ............................................................................................................................................. 5 OPTIONS: Display .............................................................................................................................................. 5 OPTIONS: Local Resources ................................................................................................................................