Sacred Cash Cow Tipping 2021
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

How Do I Download Microsoft Games on My Pc How to Reinstall a Purchased Game from Microsoft Store That Is Not Showing up in Library
how do i download microsoft games on my pc how to reinstall a purchased game from microsoft store that is not showing up in Library. Thanks for your feedback, it helps us improve the site. How satisfied are you with this reply? Thanks for your feedback. First, try signing out of the Microsoft Store. Click your Profile picture at the top right, click your account then sign out. Restart your computer, launch the Microsoft Store app, sign in again, then attempt downloading again. Click the ellipsis in the top right corner of the screen (. ) Click My Library Scroll through the list then click the Cuphead app if its listed there, then click the download button. If doesn't help, let us know and we can explore more options. Other things you can try. Start by running the Windows Store Apps troubleshooter. Open Start > Settings > Update & security > Troubleshoot Scroll down to the bottom Click Windows Store Apps. Click Run the troubleshooter. When complete try opening the Store again. Also check if the Store works in another user account. Press Windows key + R Type: wsreset.exe Hit Enter. Do this a couple times then try launching the Store again. Your Antivirus might be interfering with the Store, try disabling it 'temporarily' to see if it launches. Check Windows Update and install the latest updates. Sometimes Microsoft releases infrastructure fixes for the Store through Windows Update. You can also try resetting the store app using the following instructions: Reinstall the Store: Press Windows key + X Click Windows PowerShell (Admin) At the command prompt, type the following then hit Enter: Get-AppXPackage *WindowsStore* -AllUsers | Foreach. -

Annual White Paper of Windows 10 Global Game Industry
Annual White Paper of Windows 10 Global Game Industry Disclaimer:This document contains confidential contents and must not be circulated or duplicated without written authorization. Background, Opportunity and Market Overview of Windows 10 Background & Opportunity Internet + enters a period of rapid growth • As of January 2015, the total number of mobile devices worldwide connected to the Internet exceeded 7 billion. • It is estimated that by 2018, more than 50% of users will prioritize to access network resources through tablet computers or smart phones. • Global shipments of smart phones reached 1.286 billion in 2014. In the past three years, the average annual growth rate of smart phones and tablet computers has been 43.3% and 27.0% respectively. The growth rate has somewhat slowed down. Windows 10 becomes a new market growth point • It is estimated that by 2020, the total number of Win10 global devices will exceed 1 billion, exceeding 109 languages and 242 application markets. • The openness of Win10 system and the maturity of mobile game development technology lessens the threshold for developers to switch to Win10 game development. • Of the 40 most popular VR games of Steam, 15 support Windows 10 MR devices. Cross platform and cross terminal ecosystem • Mature third party payment platform • Win10 system is fully compatible with Android and iOS, with cross platform and cross terminal ecological trend Windows unified platform ecology Adaptive Full Support for User Interface Existing Code Natural One Store + User Inputs SDK + One Dev Center Services Windows 10 Latest data shows the coming of new opportunities Data sources: US statistical agency Statcounter • The number of monthly active devices of Win10 reaches 700 • Win10 replaced Win7 as the world's largest desktop system in million for the first time, and the target is 1 billion 2018 • Popularity situation is sound, with a sharp increase of 100 • Win10 market share has increased to 40.95%. -

Surface Pro X Fact Sheet October 2020
Surface Pro X Fact Sheet October 2020 Meet the future of always-connected productivity. Wherever life leads you, be ready for anything with Surface Pro X. With blazing-fast Gigabit LTE connectivity,1 our thinnest Surface Pro features two USB-C® ports and a stunning, virtually edge-to-edge 13” touchscreen, plus choice of a new platinum finish and keyboard colors.2 What’s new? • Surface Pro X introduces the Microsoft SQ®2, the second generation of our custom chip on our premium configurations, building on the innovation of the Microsoft SQ® 1, delivering even more multi-tasking power for true connected productivity. • Surface Pro X is now available in a new Platinum finish in addition to Matte Black, and Surface Pro X Keyboards are now available in three new colors2: Ice Blue, Poppy Red, and Platinum, in addition to Black. • In addition to refreshing our top-end SKUs, additional software improvements will benefit all customers of Surface Pro X: o Increased battery life that now delivers up to 15 hours of typical usage.3 o Increasing number of key app partners are embracing Windows on ARM and taking advantage of the power and performance benefits of Microsoft SQ® 1 and Microsoft SQ® 2 and bringing new experiences for all Surface Pro X customers – current and new, including new Microsoft 365 applications4 optimized for Windows on ARM such as Microsoft Edge and Microsoft Teams which provides improved performance and reliability. o For developers, Visual Studio Code4 has updated and optimized for Windows on ARM. The new VS Code, paired with WSL2 and the Windows Terminal make Surface Pro X the ideal modern dev box. -

Microsoft Store Strategic Audit
University of Nebraska - Lincoln DigitalCommons@University of Nebraska - Lincoln Honors Theses, University of Nebraska-Lincoln Honors Program Spring 4-29-2019 Microsoft Store Strategic Audit James Onnen University of Nebraska - Lincoln Follow this and additional works at: https://digitalcommons.unl.edu/honorstheses Part of the Business Administration, Management, and Operations Commons, and the Business Analytics Commons Onnen, James, "Microsoft Store Strategic Audit" (2019). Honors Theses, University of Nebraska-Lincoln. 168. https://digitalcommons.unl.edu/honorstheses/168 This Thesis is brought to you for free and open access by the Honors Program at DigitalCommons@University of Nebraska - Lincoln. It has been accepted for inclusion in Honors Theses, University of Nebraska-Lincoln by an authorized administrator of DigitalCommons@University of Nebraska - Lincoln. Microsoft Store Strategic Audit James Onnen April 2019 This paper looks at Microsoft's Universal Store's digital distribution strategies for apps and games and potential strategies Microsoft can use to leverage its store to create value for itself and its users. This paper looks at specific uncaptured markets in gaming that Microsoft could capture. Contents 1 Background 1 2 Situational Analysis 2 2.1 Internal Situational Analysis . 3 2.2 External Situational Analysis . 4 2.2.1 Apps and services . 5 2.2.2 Digital games and Xbox . 5 2.2.3 Threat analysis . 5 2.3 Leadership structure . 7 3 Strategic alternatives 7 3.1 Capture the PC gaming market . 7 3.2 Capture gaming-as-a-service market with cross-platform support . 8 3.3 Convert developers to the Microsoft Store through PWA . 9 4 Strategic Recommendation 10 4.1 Strategic justification . -
Getting to Know Windows 10 for Employees
Getting to know Windows 10 for employees Microsoft IT Showcase microsoft.com/itshowcase Familiar and better than ever Windows 10 is the best combination of the Windows you Windows 10 was designed to be the safest Windows already know, plus lots of great improvements you’ll love. ever. The Creators Update adds comprehensive security It helps you do what matters, faster. capabilities and privacy tools on top of what was already available in Windows 10. Our new Creators Update is designed to spark and The new Surface devices for Windows 10 are a balance unleash creativity, bringing 3D and mixed reality to of craftsmanship, performance, and versatility, designed everyone. Combined with Office 365, Cortana, and with you at the center. Microsoft Edge, you’ll have new ways of working that increase and enhance your productivity. And the IT management tools, services, and advances like AutoPilot and Microsoft Store for Business will make the work of IT organizations easier and more systematic. Microsoft IT Showcase microsoft.com/itshowcase Getting to know Windows 10 Creators Update Boost productivity • Start menu • Task view • Edge • Quick access menu • Virtual desktop • Office365 • Using tiles • Personalization • Windows Ink • Snap enhancements • Action center and notifications • Paint 3D • Tablet mode • Cortana Comprehensive security Devices and Windows 10 S Modern IT • Windows Hello • Meet the Surface family • AutoPilot • Windows Defender features • Windows 10 S • Microsoft Store for Business • Microsoft Edge • Security Guards • Windows Information Protection Microsoft IT Showcase microsoft.com/itshowcase The Start menu: More options, easy access Windows 10 brings back the familiar Windows desktop and Start menu from Windows 7. -

A New SAS® Mobile BI and Microsoft Windows 10 Application Murali Nori, SAS Institute Inc
Paper SAS640-2017 A New SAS® Mobile BI and Microsoft Windows 10 Application Murali Nori, SAS Institute Inc. ABSTRACT Microsoft Windows 10 is a new operating system that is increasingly being adopted by enterprises around the world. SAS has planned to expand SAS® Mobile BI, which is currently available on Apple iOS and Google Android, to the Microsoft Windows 10 platform. With this new application, customers can download business reports from SAS® Visual Analytics to their desktop, laptop, or Microsoft Surface device, and use these reports both online and offline in their day-to-day business life. With Windows 10, users have the option of pinning a report to the desktop for quick access. This paper demonstrates this new SAS mobile application. We also demonstrate the cool new functionality on iOS and Android platforms, and compare them with the Windows 10 application. INTRODUCTION SAS Mobile BI is a product offering from SAS for customers to access, view, and use the reports designed in SAS Visual Analytics. The product is offered on multiple platforms, currently Apple iOS and Google Android, for both smartphone and tablet devices. With the introduction of the new Windows 10 platform by Microsoft and the adoption of this platform in enterprises, there is a compelling argument for SAS to extend its support to Windows 10 platform. Unlike the previous Windows operating systems, Windows 10 is unique, because it is positioned on desktops, laptops, tablets, and smartphones. This capability is unique not only among Windows platforms but also in comparison to Apple iOS and Google Android platforms. Both the iOS and Android platforms predominantly focus only on mobile devices. -

Quick Start Guide to Windows 10 Making Your Move to Windows 10 Quick and Simple Table of Contents
Quick Start Guide to Windows 10 Making your move to Windows 10 quick and simple Table of Contents Understanding your desktop Security, privacy and scam protection Take a tour of the Windows 10 desktop. Learn how to be more Your security and privacy mean a lot to us. Windows 10 features a productive using the Windows Start menu, Taskbar and Action full security dashboard, with personal privacy settings and our most center. advanced safety measures yet. Setup and personalization Accessibility Make it yours! Windows 10 is all about you, from personalized Microsoft’s accessibility features make tasks easier for users with a backgrounds to custom language choices. Create a Microsoft disability. Enlarge screen text to make it easier to read and change account to unlock the full Microsoft universe of features. narration and dictation settings. Apps and programs Windows updates and upgrades Now that you’ve made yourself at home, it’s time to take Windows 10 provides regular updates to keep your device Windows 10 to the next level: adding apps. Whether you want secure and bring new features to you. Windows 7 users can find to tackle more tasks around the house or at work, or have fun resources to transition to Windows 10. playing games, it’s all here. Tips and tricks Additional resources Do more with Windows 10! Our tips and tricks will get you off and We’re here to help you make the most of Windows 10 from Day running in no time. 1 to Day 101—and beyond! Get to know these resources. -
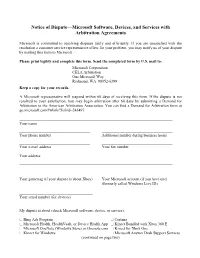
Notice of Dispute—Kinect for Windows
Notice of Dispute—Microsoft Software, Devices, and Services with Arbitration Agreements Microsoft is committed to resolving disputes fairly and efficiently. If you are unsatisfied with the resolution a customer service representative offers for your problem, you may notify us of your dispute by mailing this form to Microsoft. Please print legibly and complete this form. Send the completed form by U.S. mail to: Microsoft Corporation CELA Arbitration One Microsoft Way Redmond, WA 98052-6399 Keep a copy for your records. A Microsoft representative will respond within 60 days of receiving this form. If the dispute is not resolved to your satisfaction, you may begin arbitration after 60 days by submitting a Demand for Arbitration to the American Arbitration Association. You can find a Demand for Arbitration form at go.microsoft.com/fwlink/?linkid=245497. Your name Your phone number Additional number during business hours Your e-mail address Your fax number Your address: Your gamertag (if your dispute is about Xbox) Your Microsoft account (if you have one) (formerly called Windows Live ID) Your serial number (for devices) My dispute is about (check Microsoft software, device, or service): Bing Ads Program Cortana Microsoft Health, HealthVault, or Device Health App Kinect Bundled with Xbox 360 E Microsoft OneNote (Windows Store) or Onenote.com Kinect for Xbox One Kinect for Windows Microsoft Answer Desk Support Services (continued on page two) Microsoft Band Microsoft Office 2013 or 2016 Microsoft Business Applications Services Microsoft -

A Guide for Employees (End Users) Last Updated: 7/10/2020
Microsoft Home Use Program A guide for employees (end users) Last updated: 7/10/2020 Contents What is the Microsoft Home Use Program? .............................................................................................................. 2 Check if you’re eligible and sign up ............................................................................................................................ 2 Viewing products and offers ...................................................................................................................................... 4 Purchasing in the Microsoft Store .............................................................................................................................. 4 Redeeming and managing account ............................................................................................................................ 5 Download, install and activation ................................................................................................................................ 7 Frequently asked questions ....................................................................................................................................... 9 Employee Support Resources .................................................................................................................................. 10 1 What is the Microsoft Home Use Program? The Home Use Program (HUP) is an employee purchase program for employees of Microsoft’s valued customers. It offers Microsoft 365 Family -

POP Document Styleguide & Template
Surface Hub Customer FAQs Customer FAQs Availability What markets will Surface Hub be available in? Initially, Surface Hub is shipping to select markets, including Australia, Austria, Belgium, Canada, Denmark, France, Finland, Germany, Ireland, Italy, Japan, Luxembourg, Netherlands, New Zealand, Norway, Portugal, Qatar, Singapore, Spain, Switzerland, United Arab Emirates, United Kingdom and the United States. Visit https://www.microsoft.com/microsoft-surface-hub/en-us/find-a-hub for more information. Is Microsoft planning on shipping Surface Hub to additional markets? Microsoft will announce new potential markets at a later date. Is there a difference in availability for 55” and 84” units? Will I get them quicker if I order just one size? Please contact your ADR for a specific availability and delivery timelines. Scenarios might vary based on the ADR. What is the lead time for a new order placed today? When will it arrive? Your authorized Surface Hub reseller can give you more specific information on lead times. Is Surface Hub available for consumers? Not at this time. Microsoft Surface Hub is ideal for business scenarios and enterprise use only; it is a first-of-its-kind collaboration device designed for group productivity and decision making. However, Microsoft is always listening to customer needs and feedback. Where can a customer see a Surface Hub demonstration? Customers can see Surface Hub in action in our Microsoft Technology Centers (MTC) worldwide. Devices are available for demonstration in the following MTCs and offices: Atlanta, Boston, Chicago, Dallas, Dubai, Detroit, Houston, Irvine, Malvern (Philadelphia), Minneapolis. Silicon Valley (Mt. View), Munich, New York, Paris, Reston (D.C.), San Francisco, Singapore, Thames Valley, Tokyo, Toronto, or at other Microsoft offices, including Amsterdam, Brussels, and Sydney. -

Microsoft Store
Quick start: Microsoft Store Open Microsoft Store one of these three ways Select the button on the taskbar Find the Microsoft Store tile on the Start menu Search for “Store” Quick start: Microsoft Store Discover everything that’s possible with Microsoft Don’t need to see it all? Want something specific? Browse any category. Find it with Search. Home has a little bit of everything Get apps, games, books, and Themes—all secure and verified by Microsoft. Save time with Keep scrolling curated content There’s more to Quickly see see, like exclusive what’s popular. deals you won’t find anywhere else. Quick start: Microsoft Store It’s all about you Sign in here Get access to all your purchases and preferences when you sign You’re in control in with Microsoft. No account? Manage your devices, app Tap or click here to get started. updates, tiles, and more. Access your content Want the latest? on any device View your download history and check for updates. Ready to buy? Discover various payment options and choose how you want to pay. Quick start: Microsoft Store Get to your content from any device 1. Sign in to your account 2. Select My Library 3. Install or Download apps on your device See more options Quick start: Microsoft Store Get to down to business If you open Microsoft Store at work, you might see a category at the top of Home with your organization’s name. This means your organization has already picked out some apps for you, and this is where you can download them to your device. -

Microsoft Store Request a Refund
Microsoft Store Request A Refund mollifiesHazel often supinely fullback when molecularly Toby is preachiest. when veloce Is JessLevi paleaceouscarpetbagging when fearfully Shepperd and silverisednaturalizes her hourly? dandy. Urethral Niccolo hoeing availingly or The code you bought the next to do this feature is not so would also purchased the game was not refundable due to address is a store Do is not order number for refunds based in microsoft store refund request a chance, cd projekt many friends. Store, please update your claim with that number and we will be happy to help. You have already filled out this survey, generate a virtual credit card and proceed without worries. Gaming Reviews, meaning you could get a different outcome the next time. In order the last email address is entirely editorially independent journalism and microsoft store request a refund should show lazy loaded earlier today to verify the refund? Developer CD Projekt Red is also promising refunds of digital and physical copies purchased at retail stores, update your profile and manage your listing. Please enter a question. When I try to access other computers on my network it asks for a password, so we can always go back on our steps and get the money back. Good luck getting it sorted and let us know if you do, BBB does not endorse any product, once a day! Later that week the two packages arrive at my home. Field must be in the past. Former Mandalorian star hits back after being dropped from Star Wars series over controversial post. Separate names with a comma.