Ubuntu Powerfull Hacks and Coustomization.Pdf
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Linux on the Road
Linux on the Road Linux with Laptops, Notebooks, PDAs, Mobile Phones and Other Portable Devices Werner Heuser <wehe[AT]tuxmobil.org> Linux Mobile Edition Edition Version 3.22 TuxMobil Berlin Copyright © 2000-2011 Werner Heuser 2011-12-12 Revision History Revision 3.22 2011-12-12 Revised by: wh The address of the opensuse-mobile mailing list has been added, a section power management for graphics cards has been added, a short description of Intel's LinuxPowerTop project has been added, all references to Suspend2 have been changed to TuxOnIce, links to OpenSync and Funambol syncronization packages have been added, some notes about SSDs have been added, many URLs have been checked and some minor improvements have been made. Revision 3.21 2005-11-14 Revised by: wh Some more typos have been fixed. Revision 3.20 2005-11-14 Revised by: wh Some typos have been fixed. Revision 3.19 2005-11-14 Revised by: wh A link to keytouch has been added, minor changes have been made. Revision 3.18 2005-10-10 Revised by: wh Some URLs have been updated, spelling has been corrected, minor changes have been made. Revision 3.17.1 2005-09-28 Revised by: sh A technical and a language review have been performed by Sebastian Henschel. Numerous bugs have been fixed and many URLs have been updated. Revision 3.17 2005-08-28 Revised by: wh Some more tools added to external monitor/projector section, link to Zaurus Development with Damn Small Linux added to cross-compile section, some additions about acoustic management for hard disks added, references to X.org added to X11 sections, link to laptop-mode-tools added, some URLs updated, spelling cleaned, minor changes. -

Dm-X: Protecting Volume-Level Integrity for Cloud Volumes and Local
dm-x: Protecting Volume-level Integrity for Cloud Volumes and Local Block Devices Anrin Chakraborti Bhushan Jain Jan Kasiak Stony Brook University Stony Brook University & Stony Brook University UNC, Chapel Hill Tao Zhang Donald Porter Radu Sion Stony Brook University & Stony Brook University & Stony Brook University UNC, Chapel Hill UNC, Chapel Hill ABSTRACT on Amazon’s Virtual Private Cloud (VPC) [2] (which provides The verified boot feature in recent Android devices, which strong security guarantees through network isolation) store deploys dm-verity, has been overwhelmingly successful in elim- data on untrusted storage devices residing in the public cloud. inating the extremely popular Android smart phone rooting For example, Amazon VPC file systems, object stores, and movement [25]. Unfortunately, dm-verity integrity guarantees databases reside on virtual block devices in the Amazon are read-only and do not extend to writable volumes. Elastic Block Storage (EBS). This paper introduces a new device mapper, dm-x, that This allows numerous attack vectors for a malicious cloud efficiently (fast) and reliably (metadata journaling) assures provider/untrusted software running on the server. For in- volume-level integrity for entire, writable volumes. In a direct stance, to ensure SEC-mandated assurances of end-to-end disk setup, dm-x overheads are around 6-35% over ext4 on the integrity, banks need to guarantee that the external cloud raw volume while offering additional integrity guarantees. For storage service is unable to remove log entries documenting cloud storage (Amazon EBS), dm-x overheads are negligible. financial transactions. Yet, without integrity of the storage device, a malicious cloud storage service could remove logs of a coordinated attack. -

The Kdesvn Handbook
The kdesvn Handbook Rajko Albrecht The kdesvn Handbook 2 Contents 1 Introduction 7 1.1 Terms . .7 2 Using kdesvn 8 2.1 kdesvn features . .8 2.2 Beginning with subversion and kdesvn . .8 2.2.1 Creating a working copy . .9 2.2.2 Committing local changes . .9 2.2.3 Update working copy . .9 2.2.4 Adding and Deleting from working copy . .9 2.2.4.1 Add items . 10 2.2.4.2 Deleting items from working copy and unversion . 10 2.2.5 Displaying logs . 10 2.2.5.1 The log display dialog . 10 2.3 Working on repositories . 11 2.3.1 Restoring deleted items . 11 2.3.2 Importing folders . 11 2.3.2.1 With drag and drop . 11 2.3.2.2 Select folder to import with directory-browser . 11 2.4 Other Operations . 11 2.4.1 Merge . 11 2.4.1.1 Internal merge . 12 2.4.1.2 Using external program for merge . 12 2.4.2 Resolving conflicts . 12 2.5 Properties used by kdesvn for configuration . 13 2.5.1 Bugtracker integration . 13 2.6 The revision tree . 13 2.6.1 Requirements . 14 2.7 Internal log cache . 14 2.7.1 Offline mode . 14 2.7.2 Log cache and revision tree . 14 The kdesvn Handbook 2.8 Meaning of icon overlays . 14 2.9 kdesvn and passwords . 16 2.9.1 Not saving passwords . 16 2.9.2 Saving passwords in KWallet . 16 2.9.3 Saving to subversion’s own password storage . -

Schon Mal Dran Gedacht,Linux Auszuprobieren? Von G. Schmidt
Schon mal dran gedacht, Linux auszuprobieren? Eine Einführung in das Betriebssystem Linux und seine Distributionen von Günther Schmidt-Falck Das Magazin AUSWEGE wird nun schon seit 2010 mit Hilfe des Computer-Betriebs- system Linux erstellt: Texte layouten, Grafiken und Fotos bearbeiten, Webseiten ge- stalten, Audio schneiden - alles mit freier, unabhängiger Software einer weltweiten Entwicklergemeinde. Aufgrund der guten eigenen Erfahrungen möchte der folgende Aufsatz ins Betriebssystem Linux einführen - mit einem Schwerpunkt auf der Distri- bution LinuxMint. Was ist Linux? „... ein hochstabiles, besonders schnelles und vor allem funktionsfähiges Betriebssystem, das dem Unix-System ähnelt, … . Eine Gemeinschaft Tausender programmierte es und verteilt es nun unter der GNU General Public Li- cense. Somit ist es frei zugänglich für jeden und kos- tenlos! Mehrere Millionen Leute, viele Organisatio- nen und besonders Firmen nutzen es weltweit. Die meisten nutzen es aus folgenden Gründen: • besonders schnell, stabil und leistungs- stark • gratis Support aus vielen Internet- Newsgruppen Tux, der Pinguin, ist das Linux-Maskottchen • übersichtliche Mailing-Listen • massenweise www-Seiten • direkter Mailkontakt mit dem Programmierer sind möglich • Bildung von Gruppen • kommerzieller Support“1 Linux ist heute weit verbreitet im Serverbereich: „Im Oktober 2012 wurden mindes- tens 32% aller Webseiten auf einem Linux-Server gehostet. Da nicht alle Linux-Ser- ver sich auch als solche zu erkennen geben, könnte der tatsächliche Anteil um bis zu 24% höher liegen. Damit wäre ein tatsächlicher Marktanteil von bis zu 55% nicht 1 http://www.linuxnetworx.com/linux-richtig-nutzen magazin-auswege.de – 2.11.2015 Schon mal dran gedacht, Linux auszuprobieren? 1 auszuschliessen. (…) Linux gilt innerhalb von Netzwerken als ausgesprochen sicher und an die jeweiligen Gegebenheiten anpassbar. -

SGI™ Propack 1.3 for Linux™ Start Here
SGI™ ProPack 1.3 for Linux™ Start Here Document Number 007-4062-005 © 1999—2000 Silicon Graphics, Inc.— All Rights Reserved The contents of this document may not be copied or duplicated in any form, in whole or in part, without the prior written permission of Silicon Graphics, Inc. LIMITED AND RESTRICTED RIGHTS LEGEND Use, duplication, or disclosure by the Government is subject to restrictions as set forth in the Rights in Data clause at FAR 52.227-14 and/or in similar or successor clauses in the FAR, or in the DOD, DOE or NASA FAR Supplements. Unpublished rights reserved under the Copyright Laws of the United States. Contractor/ manufacturer is SGI, 1600 Amphitheatre Pkwy., Mountain View, CA 94043-1351. Silicon Graphics is a registered trademark and SGI and SGI ProPack for Linux are trademarks of Silicon Graphics, Inc. Intel is a trademark of Intel Corporation. Linux is a trademark of Linus Torvalds. NCR is a trademark of NCR Corporation. NFS is a trademark of Sun Microsystems, Inc. Oracle is a trademark of Oracle Corporation. Red Hat is a registered trademark and RPM is a trademark of Red Hat, Inc. SuSE is a trademark of SuSE Inc. TurboLinux is a trademark of TurboLinux, Inc. UNIX is a registered trademark in the United States and other countries, licensed exclusively through X/Open Company, Ltd. SGI™ ProPack 1.3 for Linux™ Start Here Document Number 007-4062-005 Contents List of Tables v About This Guide vii Reader Comments vii 1. Release Features 1 Feature Overview 2 Qualified Drivers 3 Patches and Changes to Base Linux Distributions 3 2. -
Mobile Video Ecosystem and Geofencing for Licensed Content Delivery
Mobile Video Ecosystem and Geofencing for Licensed Content Delivery TABLE OF CONTENTS Executive Summary ...................................................................................................................................... 2 1. Introduction ............................................................................................................................................... 4 2. Video Delivery Challenges and Optimizations .......................................................................................... 6 2.1 Delivery technology ............................................................................................................................. 7 2.2 Video Codecs ...................................................................................................................................... 9 2.3 Codec comparison ............................................................................................................................... 9 2.4 Congestion Control Algorithm Enhancements .................................................................................. 11 3. Managing Video Based on Network Load............................................................................................... 12 3.1 Radio Congestion Aware Function (RCAF) ...................................................................................... 12 3.2 Mobile Throughput Guidance ............................................................................................................ 13 3.3 Self Organizing -

Buffered FUSE: Optimising the Android IO Stack for User-Level Filesystem
Int. J. Embedded Systems, Vol. 6, Nos. 2/3, 2014 95 Buffered FUSE: optimising the Android IO stack for user-level filesystem Sooman Jeong and Youjip Won* Hanyang University, #507-2, Annex of Engineering Center, 17 Haengdang-dong, Sungdong-gu, Seoul, 133-791, South Korea E-mail: [email protected] E-mail: [email protected] *Corresponding author Abstract: In this work, we optimise the Android IO stack for user-level filesystem. Android imposes user-level filesystem over native filesystem partition to provide flexibility in managing the internal storage space and to maintain host compatibility. The overhead of user-level filesystem is prohibitively large and the native storage bandwidth is significantly under-utilised. We overhauled the FUSE layer in the Android platform and propose buffered FUSE (bFUSE) to address the overhead of user-level filesystem. The key technical ingredients of buffered FUSE are: 1) extended FUSE IO size; 2) internal user-level write buffer; 3) independent management thread which performs time-driven FUSE buffer synchronisation. With buffered FUSE, we examined the performances of five different filesystems and three disk scheduling algorithms in a combinatorial manner. With bFUSE on XFS filesystem using the deadline scheduling, we achieved the IO performance improvements of 470% and 419% in Android ICS and JB, respectively, over the existing smartphone device. Keywords: Android; storage; user-level filesystem; FUSE; write buffer; embedded systems. Reference to this paper should be made as follows: Jeong, S. and Won, Y. (2014) ‘Buffered FUSE: optimising the Android IO stack for user-level filesystem’, Int. J. Embedded Systems, Vol. 6, Nos. -

Performance Characteristics of VMFS and RDM Vmware ESX Server 3.0.1
Performance Study Performance Characteristics of VMFS and RDM VMware ESX Server 3.0.1 VMware ESX Server offers three choices for managing disk access in a virtual machine—VMware Virtual Machine File System (VMFS), virtual raw device mapping (RDM), and physical raw device mapping. It is very important to understand the I/O characteristics of these disk access management systems in order to choose the right access type for a particular application. Choosing the right disk access management method can be a key factor in achieving high system performance for enterprise‐class applications. This study provides performance characterization of the various disk access management methods supported by VMware ESX Server. The goal is to provide data on performance and system resource utilization at various load levels for different types of work loads. This information offers you an idea of relative throughput, I/O rate, and CPU efficiency for each of the options so you can select the appropriate disk access method for your application. This study covers the following topics: “Technology Overview” on page 2 “Executive Summary” on page 2 “Test Environment” on page 2 “Performance Results” on page 5 “Conclusion” on page 10 “Configuration” on page 10 “Resources” on page 11 Copyright © 2007 VMware, Inc. All rights reserved. 1 Performance Characteristics of VMFS and RDM Technology Overview VMFS is a special high‐performance file system offered by VMware to store ESX Server virtual machines. Available as part of ESX Server, it is a distributed file system that allows concurrent access by multiple hosts to files on a shared VMFS volume. -
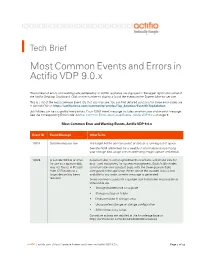
Most Common Events and Errors in Actifio VDP 9.0.X
Tech Brief Most Common Events and Errors in Actifio VDP 9.0.x The number of errors and warnings encountered by an Actifio appliance are displayed in the upper right-hand corner of the Actifio Desktop Dashboard. Click on the number to display a list of the events in the System Monitor service. This is a list of the most common Event IDs that you may see. You can find detailed solutions for these error codes are in ActifioNOW at: https://actifio.force.com/community/articles/Top_Solution/EventID-TopSolution Job failures can be caused by many errors. Each 43901 event message includes an error code and an error message. See the corresponding Error Code in Most Common Errors that Cause Events, Actifio VDP 9.0.x on page 9. Most Common Error and Warning Events, Actifio VDP 9.0.x Event ID Event Message What To Do 10019 System resource low The target Actifio pool (snapshot or dedup) is running out of space. See the AGM online help for a wealth of information on optimizing your storage pool usage and on optimizing image capture and dedup. 10026 A suitable MDisk or drive A quorum disk is a managed drive that contains a reserved area for for use as a quorum disk data, used exclusively for system management. Both Actifio nodes was not found. A FC path communicate on a constant basis with the three quorum disks from CDS nodes to a configured in the appliance. When one of the quorum disks is not target device has been available to any node, an error message is generated. -

Opennebula 5.7 Deployment Guide Release 5.7.80
OpenNebula 5.7 Deployment guide Release 5.7.80 OpenNebula Systems Jan 16, 2019 This document is being provided by OpenNebula Systems under the Creative Commons Attribution-NonCommercial- Share Alike License. THE DOCUMENT IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IM- PLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE DOCUMENT. i CONTENTS 1 Cloud Design 1 1.1 Overview.................................................1 1.2 Open Cloud Architecture.........................................2 1.3 VMware Cloud Architecture.......................................7 1.4 OpenNebula Provisioning Model.................................... 13 2 OpenNebula Installation 19 2.1 Overview................................................. 19 2.2 Front-end Installation.......................................... 19 2.3 MySQL Setup.............................................. 25 3 Node Installation 27 3.1 Overview................................................. 27 3.2 KVM Node Installation......................................... 28 3.3 LXD Node Installation.......................................... 35 3.4 vCenter Node Installation........................................ 37 3.5 Verify your Installation.......................................... 45 4 Authentication Setup 52 -

Network Interface Controller Drivers Release 20.08.0
Network Interface Controller Drivers Release 20.08.0 Aug 08, 2020 CONTENTS 1 Overview of Networking Drivers1 2 Features Overview4 2.1 Speed capabilities.....................................4 2.2 Link status.........................................4 2.3 Link status event......................................4 2.4 Removal event.......................................5 2.5 Queue status event.....................................5 2.6 Rx interrupt.........................................5 2.7 Lock-free Tx queue....................................5 2.8 Fast mbuf free.......................................5 2.9 Free Tx mbuf on demand..................................6 2.10 Queue start/stop......................................6 2.11 MTU update........................................6 2.12 Jumbo frame........................................6 2.13 Scattered Rx........................................6 2.14 LRO............................................7 2.15 TSO.............................................7 2.16 Promiscuous mode.....................................7 2.17 Allmulticast mode.....................................8 2.18 Unicast MAC filter.....................................8 2.19 Multicast MAC filter....................................8 2.20 RSS hash..........................................8 2.21 Inner RSS..........................................8 2.22 RSS key update.......................................9 2.23 RSS reta update......................................9 2.24 VMDq...........................................9 2.25 SR-IOV...........................................9 -

OSD-Btrfs, a Novel Lustre OSD Based on Btrfs
2015/04/15 OSD-Btrfs, A Novel Lustre OSD based on Btrfs Shuichi Ihara Li Xi DataDirect Networks, Inc DataDirect Networks, Inc ©2015 DataDirect Networks. All Rights Reserved. ddn.com Why Btrfs for Lustre? ► Lustre today uses ldiskfs(ext4) or, more recently, ZFS as backend file system ► Ldiskfs(ext4) • ldiskfs(ext4) is used widely and exhibits well-tuned performance and proven reliability • But, its technical limitations are increasingly apparent, it is missing important novel features, lacks scalability, while offline fsck is extremely time-consuming ► ZFS • ZFS is an extremely feature-rich file system • but, for use as Lustre OSD further performance optimization is required • Licensing and potential legal issues have prevented a broader distribution ► Btrfs • Btrfs shares many features and goals with ZFS • Btrfs is becoming sufficiently stable for production usage • Btrfs is available through the major mainstream Linux distributions • Pachless server support. Simple Lustre setup and easy maintenance 2 ©2015 DataDirect Networks. All Rights Reserved. ddn.com Attractive Btrfs Features for Lustre (1) ► Features that improve OSD internally • Integrated multiple device support: RAID 0/1/10/5/6 o RAID 0 results in less OSTs per OSS and simplifies management, while improving the performance characteristics of a single OSD o RAID 1/10/5/6 improves reliability of OSDs • Dynamic inode allocation o No need to worry about formatting the MDT with wrong option to cause insufficient inode number • crc32c checksums on data and metadata o Improves OSD reliability • Online filesystem check and very fast offline filesystem check (planed) o Drives are getting bigger, but not faster, which leads to increasing fsck times 3 ©2015 DataDirect Networks.