Emailbestpractices Postfix and Dovecot
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Cyrus Mail Server 2 Table of Contents
Univention Corporate Server Cyrus mail server 2 Table of Contents 1. Introduction ........................................................................................................................ 4 2. Installation ......................................................................................................................... 5 3. Management of the mail server data ....................................................................................... 6 3.1. Management of mail domains ..................................................................................... 6 3.2. Assignment of e-mail addresses to users ........................................................................ 6 3.3. Management of mailing lists ....................................................................................... 7 3.4. Management of mail groups ........................................................................................ 7 3.5. Management of shared IMAP folders ........................................................................... 8 3.6. Mail quota ............................................................................................................... 9 4. Spam detection and filtering ................................................................................................ 10 5. Identification of viruses and malware .................................................................................... 11 6. Identification of Spam sources with DNS-based Blackhole Lists (DNSBL) ................................... -

Release Notes for Debian 7.0 (Wheezy), Kfreebsd 64-Bits PC
Release Notes for Debian 7.0 (wheezy), kFreeBSD 64-bits PC The Debian Documentation Project (http://www.debian.org/doc/) November 20, 2018 Release Notes for Debian 7.0 (wheezy), kFreeBSD 64-bits PC This document is free software; you can redistribute it and/or modify it under the terms of the GNU General Public License, version 2, as published by the Free Software Foundation. This program is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU General Public License for more details. You should have received a copy of the GNU General Public License along with this program; if not, write to the Free Software Foundation, Inc., 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA. The license text can also be found at http://www.gnu.org/licenses/gpl-2.0.html and /usr/ share/common-licenses/GPL-2 on Debian. ii Contents 1 Introduction 1 1.1 Reporting bugs on this document . 1 1.2 Contributing upgrade reports . 1 1.3 Sources for this document . 2 2 What’s new in Debian 7.0 3 2.1 Supported architectures . 3 2.2 What’s new for kFreeBSD? . 4 2.3 What’s new in the distribution? . 4 2.3.1 CDs, DVDs and BDs . 5 2.3.2 Multiarch . 5 2.3.3 Dependency booting . 5 2.3.4 systemd . 5 2.3.5 Multimedia . 5 2.3.6 Hardened security . 6 2.3.7 AppArmor . -

Ispmail Tutorial for Debian Lenny
6.10.2015 ISPmail tutorial for Debian Lenny ISPmail tutorial for Debian Lenny Add new comment 223533 reads This tutorial is for the former stable version "Debian Lenny". If you are using "Debian Squeeze" then please follow the new tutorial. A spanish translation of this tutorial is also available courtesy of José Ramón Magán Iglesias. What this tutorial is about You surely know the internet service providers that allow you to rent a domain and use it to receive emails. If you have a computer running Debian which is connected to the internet permanently you can do that yourself. You do not even need to have a fixed IP address thanks to dynamic DNS services like dyndns.org. All you need is this document, a cup of tea and a little time. When you are done your server will be able to... receive and store emails for your users from other mail servers let your users retrieve the email through IMAP and POP3 even with SSL to encrypt to connection receive and forward ("relay") email for your users if they are authenticated offer a webmail interface to read emails in a web browser detect most spam emails and filter them out or tag them License/Copyright This tutorial book is copyrighted 2009 Christoph Haas (email@christophhaas.de). It can be used freely under the terms of the GNU General Public License. Don't forget to refer to this URL when using it. Thank you. Changelog 17.6.09: Lenny tutorial gets published. 19.6.09: The page on SPF checks is temporarily offline. -

School and Email Systems
Email system survey: Top 50 US Colleges US Note Email system Server queried Greeting News School ranking 1 Harvard University Mail2World imap.college.harvard.edu OK Mail2World IMAP4 Server 2.5 ready Sun Java SMS imap.princeton.edu OK [CAPABILITY IMAP4 IMAP4rev1 ACL QUOTA LITERAL+ NAMESPACE UIDPLUS CHILDREN BINARY LANGUAGE XSENDER X-NETSCAPE XSERVERINFO Princeton University 1 AUTH=PLAIN] Messaging Multiplexor (Sun Java(tm) System Messaging Server 6.2-5.05 (built Feb 16 2006)) Unknown mail.yale.edu OK [CAPABILITY IMAP4REV1 LOGIN-REFERRALS AUTH=PLAIN AUTH=LOGIN] pantheon-po14.its.yale.edu IMAP4rev1 2002.336 at Mon, 26 Jul 2010 14:10:23 Yale University 3 -0400 (EDT) Dovecot imap-server.its.caltech.edu OK Dovecot ready. Cyrus mail.alumni.caltech.edu OK posteaux1.caltech.edu Cyrus IMAP4 v2.2.12-Invoca-RPM-2.2.12-10.el4_8.4 server ready 4 California Institute of Technology Dovecot imap.gps.caltech.edu OK dovecot ready. Dovecot theory.caltech.edu OK dovecot ready. 4 Massachusetts Institute of Technology Unable to find a server to query (username.mail.mit.edu)Unknown 4 Stanford University Zimbra zm01.stanford.edu OK zm01.stanford.edu Zimbra IMAP4rev1 server ready Zimbra mailbox.zimbra.upenn.edu OK mailbox.zimbra.upenn.edu Zimbra IMAP4rev1 service ready 4 University of Pennsylvania Exchange 2010 webmail.wharton.upenn.edu OK The Microsoft Exchange IMAP4 service is ready. Dovecot imap.nevis.columbia.edu OK [CAPABILITY IMAP4rev1 LITERAL+ SASL-IR LOGIN-REFERRALS ID ENABLE AUTH=PLAIN] Dovecot ready. Lotus Domino equinox.law.columbia.edu OK Domino IMAP4 -
The Bioinformatics Lab SS11 Mail / DNS Antonia Stank 20.06.2011
The bioinformatics lab SS11 Mail / DNS Antonia Stank 20.06.2011 1 Introduction The Domain Name System (DNS) is a one of the most important systems in the network. It is a hierarchical naming system which is built on a distributed database for computers, services or any resource connected to the Internet. The DNS can also be used in a private or local network. The main service of a DNS is that it serves as a kind of “phone book” for the internet or local network by translating user-friendly hostnames into specific IP addresses. For example it is much easier to remember the internet address: www.google.de than the corresponding IP address 209.85.148.99. So it can translate names to numbers and vice versa and helps therefore to connect on a specific IP address without knowing the number. An e-mail-server or just mail server is a server which can handle the mail traffic. It is necessary for sending, receiving, forwarding and saving mails. An Internet Message Access Protocol (IMAP) server is a server that provides the usage of the most prevalent IMAP protocol. There is also another common protocol which is the so called Post Office Protocol (POP). The advantage of the IMAP is that it allows an e-mail client access to a remote mail server. The e-mail clients using IMAP leave the mails on the server until they are explicitly deleted by the user. This and some other advantages make it possible to allow multiple clients to have access to the same mailbox. -

Efficient Spam Filtering System Based on Smart Cooperative Subjective and Objective Methods*
Int. J. Communications, Network and System Sciences, 2013, 6, 88-99 http://dx.doi.org/10.4236/ijcns.2013.62011 Published Online February 2013 (http://www.scirp.org/journal/ijcns) Efficient Spam Filtering System Based on Smart * Cooperative Subjective and Objective Methods Samir A. Elsagheer Mohamed1,2 1College of Computer, Qassim University, Qassim, KSA 2Electrical Engineering Department, Faculty of Engineering, Aswan University, Aswan, Egypt Email: [email protected], [email protected] Received September 17, 2012; revised January 16, 2013; accepted January 25, 2013 ABSTRACT Most of the spam filtering techniques are based on objective methods such as the content filtering and DNS/reverse DNS checks. Recently, some cooperative subjective spam filtering techniques are proposed. Objective methods suffer from the false positive and false negative classification. Objective methods based on the content filtering are time con- suming and resource demanding. They are inaccurate and require continuous update to cope with newly invented spammer’s tricks. On the other side, the existing subjective proposals have some drawbacks like the attacks from mali- cious users that make them unreliable and the privacy. In this paper, we propose an efficient spam filtering system that is based on a smart cooperative subjective technique for content filtering in addition to the fastest and the most reliable non-content-based objective methods. The system combines several applications. The first is a web-based system that we have developed based on the proposed technique. A server application having extra features suitable for the enter- prises and closed work groups is a second part of the system. Another part is a set of standard web services that allow any existing email server or email client to interact with the system. -

Analysis and Performance Optimization of E-Mail Server
Analysis and Performance Optimization of E-mail Server Disserta¸c~aoapresentada ao Instituto Polit´ecnicode Bragan¸capara cumprimento dos requisitos necess´arios `aobten¸c~aodo grau de Mestre em Sistemas de Informa¸c~ao,sob a supervis~aode Prof. Dr. Rui Pedro Lopes. Eduardo Manuel Mendes Costa Outubro 2010 Preface The e-mail service is increasingly important for organizations and their employees. As such, it requires constant monitoring to solve any performance issues and to maintain an adequate level of service. To cope with the increase of traffic as well as the dimension of organizations, several architectures have been evolving, such as cluster or cloud computing, promising new paradigms of service delivery, which can possibility solve many current problems such as scalability, increased storage and processing capacity, greater rationalization of resources, cost reduction, and increase in performance. However, it is necessary to check whether they are suitable to receive e-mail servers, and as such the purpose of this dissertation will concentrate on evaluating the performance of e-mail servers, in different hosting architectures. Beyond computing platforms, was also analze different server applications. They will be tested to determine which combinations of computer platforms and applications obtained better performances for the SMTP, POP3 and IMAP services. The tests are performed by measuring the number of sessions per ammount of time, in several test scenarios. This dissertation should be of interest for all system administrators of public and private organizations that are considering implementing enterprise wide e-mail services. i Acknowledgments This work would not be complete without thanking all who helped me directly or indirectly to complete it. -

Dual Stack E-Mail
V6home: Deploying Dual Stack E-mail Lawrence E. Hughes Chairman & CTO, InfoWeapons [email protected] (legacy) [email protected] (Dual Stack Postfix/Dovecot) [email protected] (Dual Stack Exchange 2007) Once you get a dual stack network going, what next? • With most Operating Systems supporting IPv6 today, it is no longer rocket science to deploy a dual stack network, complete with DNS (especially with a dual stack DNS appliance). • It is not that difficult to get Internet Information Server or Apache to provide web content over IPv6, and most web applications pretty much get a “free ride” once the web server supports dual stack. • The next major application that most people think of is Internet e-mail. If you read the relevant documentation, you discover: Exchange Server 2007 (running on Windows Server 2008) has IPv6 support. Most open-source mail server applications (Postfix, Dovecot, etc) have IPv6 support. Most e-mail clients (e.g. Outlook, Windows Live Mail) have IPv6 support. • Making webmail (Exchange OWA or Squirrelmail) available over IPv6 is not difficult – these are just web applications. Making SMTP, POP3 and IMAP protocols work over IPv6 is a bit more of a challenge. What is the advantage of using IPv6 for email? • The big win currently is the ability to do client access from anywhere (that has IPv6 connectivity) without having to have one of the scarce, precious IPv4 “static external” (real) addresses for every email server in your organization. • The mail gateway for your organization will still need one of these precious IPv4 addresses, to exchange mail with other legacy mail servers over SMTP, but in a typical organization there might be many internal servers where the user accounts live. -

Linux Sendmail Installation/Configuration
Sendmail Installation & Configuration: (26 Jan 2006) SMTP (Simple Mail Transfer Protocol) Email Primer: An email address: emailId@domainà [email protected] à bms is email Id & iitk.ac.in is domain Mail client: A system from where a sender (person) can send an email using any email client like mail, mh, elm, pine, Netscape messenger, Mozilla, Outlook Express, Eudora, Horde, Squirrelmail etc. Mail host: It is able to decode any address and reroutes the mail within the domain. Relay Host: It manages communication with network outside the domain. If you want a local mail system for your organization then relay host is not required. A good system for relay host is a router to internet. Gateway: It is a system between differing communication networks, like a mail from a Unix user must pass through a gateway to reach a VMS user. Mail Server: A mail storage system. This server keeps all mail boxes in /var/spool/mail (Linux) or /var/mail (Solaris) Standard Practice: Practically only one machine can act as: (Mailhost + MailRelay+ MailServer). Another configuration: Use separate servers for incoming & outgoing mails. Email Address resolution: When email sender sends an email. Destination address will be match with sender’s local aliases kept in .mailrc|.addressbook (pine uses it)|.elm/aliases.text etc. In second step it will try to expand/resolve destination address using local /etc/mail/aliases In third step it will try to expand/resolve the address using NIS aliases (If NIS is running and aliases are kept in NIS database) In fourth step it will use /etc/mail/aliases of mailhost to expand the destination Address. -
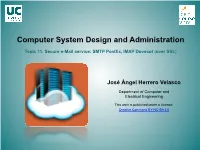
Computer System Administration. Topic 11. Secure E-Mail Service
Computer System Design and Administration Topic 11. Secure e-Mail service: SMTP Postfix, IMAP Dovecot (over SSL) José Ángel Herrero Velasco Department of Computer and Electrical Engineering This work is published under a License: Creative Commons BY-NC-SA 4.0 Computer System Design and Administration Topic 11. Secure e-Mail service: SMTP Postfix, IMAP Dovecot (over SSL) Puzzle Secure Information Server Clients Active ISC Directory DHCP Open ISC client SSL SSL LDAP DNS OpenLDAP DB LDAP ISC SSL NTP SSH IMAP (mail client) NFSv4 CIFS Secure MAIL Server Network file server/ MS Windows-Linux/UNIX interoperability SMTP IMAP (Postfix) (Dovecot) RAID/LVM SAMBA NFSv4 SSL Secure Web Server Ganglia Apache2 Hosts Core (web data) User (web data) Virtual MailLISTs Webmail pool pool (MailMan) (squirrelmail) (public_html) SSL Webmin Nagios 2 (.html, php …) WordPress José Ángel Herrero Velasco Computer System Design and Administration Topic 11. Secure e-Mail service: SMTP Postfix, IMAP Dovecot (over SSL) Target: e-Mail services • Deployment and development of an INTERNET secure e-MAIL service based on SMTP/IMAP protocols: – Sending mail using SMTP protocol: Pos(ix. – Receiving mail using IMAP protocol: Dovecot. – Management of Maildrop: Maildirs. – MUA-MTA secure communicaon (encrypted): TLS/SSL. • Installaon, configuraon and start up of a Webmail client: – Roundcube. – Mailmain. José Ángel Herrero Velasco Computer System Design and Administration Topic 11. Secure e-Mail service: SMTP Postfix, IMAP Dovecot (over SSL) The e-Mail system HTTP SMTP IMAP • Definions and basics: TCP TCP UDP – E-Mail: the electronic mail system: • Network service that enables 2 users from different computers IP to send and receive (exchange) digital messages. -
Native Microsoft Outlook Configuration Guide for Version 3.2.10 Native Microsoft Outlook Configuration Guide Version 3.2.10 - July 2017
Native Microsoft Outlook Configuration Guide for version 3.2.10 Native Microsoft Outlook Configuration Guide Version 3.2.10 - July 2017 Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with no Invariant Sections, no Front-Cover Texts, and no Back-Cover Texts. A copy of the license is included in the section entitled "GNU Free Documentation License". The fonts used in this guide are licensed under the SIL Open Font License, Version 1.1. This license is available with a FAQ at: http:// scripts.sil.org/OFL Copyright © Łukasz Dziedzic, http://www.latofonts.com, with Reserved Font Name: "Lato". Copyright © Raph Levien, http://levien.com/, with Reserved Font Name: "Inconsolata". Table of Contents About this Guide ............................................................................................................... 1 Introduction ...................................................................................................................... 2 Architecture ...................................................................................................................... 3 Requirements .................................................................................................................... 4 LDAP Server ............................................................................................................. 4 Microsoft Active Directory ........................................................................................ -

Zimbra Course Content
Zimbra Enterprise Mail & Zimbra Backup Server Administration Who should attend This course is aimed at network administrators, integrators, managers, IT consultants and other technical users who want to gain deeply knowledge on Linux System & Network Administration. Course Prerequisites . Basic knowledge of TCP/IP and routing. We will be expanding on this during the course, but we suggest that the participants have a good working knowledge of IP addressing and routing. Basic knowledge of wired and wireless networking. Course Duration 30 Hours, 10 Classes, 3 Hours per class Zimbra Course Content Module 01: Domain & DNS Servers. Email Gateway with Transport Queue & Log files Management. Describe Domain Directory Primary DNS server Secondary DNS server. Module 04: Zimbra Mail Server Basic Forward & Reverse Zone Setup Internal DNS configure Setup PTR/ SPF/ DKIM/ DMARC Entry Prepare to install zimbra (ZCS) Server DNS Service Using Locally/Remotely. Setup Zimbra Collaboration Server (ZCS) DNS Server Securities. Login to Webmail, Compose, Send/Receive, Signature, Module 02: Postfix Mail Server Basic. Change Password, Forward, Filtering, Distribution list Management. Postfix Architecture Aliases Email id. Assigning Hosts Name Administering Control Panel Interface. Postfix Setup with Domain GAL Sync & Sharing Contact list. Allow Networks with SMTP Service Locally Mail sending & receiving Email Aliasing Module 05: Zimbra Mail server Advance Dovecote setup Squirrel mail setup. Multiple Domain Configure. Outlook, Eudora,