VMPC-MAC: a Stream Cipher Based Authenticated Encryption Scheme
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Analysis of Selected Block Cipher Modes for Authenticated Encryption
Analysis of Selected Block Cipher Modes for Authenticated Encryption by Hassan Musallam Ahmed Qahur Al Mahri Bachelor of Engineering (Computer Systems and Networks) (Sultan Qaboos University) – 2007 Thesis submitted in fulfilment of the requirement for the degree of Doctor of Philosophy School of Electrical Engineering and Computer Science Science and Engineering Faculty Queensland University of Technology 2018 Keywords Authenticated encryption, AE, AEAD, ++AE, AEZ, block cipher, CAESAR, confidentiality, COPA, differential fault analysis, differential power analysis, ElmD, fault attack, forgery attack, integrity assurance, leakage resilience, modes of op- eration, OCB, OTR, SHELL, side channel attack, statistical fault analysis, sym- metric encryption, tweakable block cipher, XE, XEX. i ii Abstract Cryptography assures information security through different functionalities, es- pecially confidentiality and integrity assurance. According to Menezes et al. [1], confidentiality means the process of assuring that no one could interpret infor- mation, except authorised parties, while data integrity is an assurance that any unauthorised alterations to a message content will be detected. One possible ap- proach to ensure confidentiality and data integrity is to use two different schemes where one scheme provides confidentiality and the other provides integrity as- surance. A more compact approach is to use schemes, called Authenticated En- cryption (AE) schemes, that simultaneously provide confidentiality and integrity assurance for a message. AE can be constructed using different mechanisms, and the most common construction is to use block cipher modes, which is our focus in this thesis. AE schemes have been used in a wide range of applications, and defined by standardisation organizations. The National Institute of Standards and Technol- ogy (NIST) recommended two AE block cipher modes CCM [2] and GCM [3]. -

The EAX Mode of Operation
A preliminary version of this papers appears in Fast Software Encryption ’04, Lecture Notes in Computer Science, vol. ?? , R. Bimal and W. Meier ed., Springer-Verlag, 2004. This is the full version. The EAX Mode of Operation (A Two-Pass Authenticated-Encryption Scheme Optimized for Simplicity and Efficiency) ∗ † ‡ M. BELLARE P. ROGAWAY D. WAGNER January 18, 2004 Abstract We propose a block-cipher mode of operation, EAX, for solving the problem of authenticated-encryption with associated-data (AEAD). Given a nonce N, a message M, and a header H, our mode protects the privacy of M and the authenticity of both M and H. Strings N, M, and H are arbitrary bit strings, and the mode uses 2|M|/n + |H|/n + |N|/n block-cipher calls when these strings are nonempty and n is the block length of the underlying block cipher. Among EAX’s characteristics are that it is on-line (the length of a message isn’t needed to begin processing it) and a fixed header can be pre-processed, effectively removing the per-message cost of binding it to the ciphertext. EAX is obtained by first creating a generic-composition method, EAX2, and then collapsing its two keys into one. EAX is provably secure under a standard complexity-theoretic assumption. The proof of this fact is novel and involved. EAX is an alternative to CCM [26], which was created to answer the wish within standards bodies for a fully-specified and patent-free AEAD mode. As such, CCM and EAX are two-pass schemes, with one pass for achieving privacy and one for authenticity. -

How to Enhance the Security of the 3GPP Confidentiality and Integrity
How to Enhance the Security of the 3GPP Confidentiality and Integrity Algorithms Tetsu Iwata and Kaoru Kurosawa Dept. of Computer and Information Sciences, Ibaraki University 4–12–1 Nakanarusawa, Hitachi, Ibaraki 316-8511, Japan {iwata, kurosawa}@cis.ibaraki.ac.jp Abstract. We consider the 3GPP confidentiality and integrity schemes that were adopted by Universal Mobile Telecommunication System, an emerging standard for third generation wireless communications. The schemes, known as f8 and f9, are based on the block cipher KASUMI. Although previous works claim security proofs for f8 and f9, where f9 is a generalized version of f9, it was shown that these proofs are incorrect; it is impossible to prove f8 and f9 secure under the standard PRP assumption on the underlying block cipher. Following the results, it was shown that it is possible to prove f8 and f9 secure if we make the assumption that the underlying block cipher is a secure PRP-RKA against a certain class of related-key attacks; here f8 is a generalized version of f8. Needless to say, the assumptions here are stronger than the standard PRP assumptions, and it is natural to seek a practical way to modify f8 and f9 to establish security proofs under the standard PRP assumption. In this paper, we propose f8+ and f9+, slightly mod- ified versions of f8 and f9, but they allow proofs of security under the standard PRP assumption. Our results are practical in the sense that we insist on the minimal modifications; f8+ is obtained from f8 by setting the key modifier to all-zero, and f9+ is obtained from f9 by setting the key modifier to all-zero, and using the encryptions of two constants in the CBC MAC computation. -

AUTHENTICATED ENCRYPTION in HARDWARE by Milind M. Parelkar
AUTHENTICATED ENCRYPTION IN HARDWARE by Milind M. Parelkar A Thesis Submitted to the Graduate Faculty of George Mason University in Partial Ful¯llment of the the Requirements for the Degree of Master of Science Electrical and Computer Engineering Committee: Dr. Kris Gaj, Thesis Director Dr. William Sutton Dr. Peter Pachowicz Andre Manitius, Chairman, Department of Electrical and Computer Engineering Lloyd J. Gri±ths, Dean, School of Information Technology and Engineering Date: Fall 2005 George Mason University Fairfax, VA Authenticated Encryption in Hardware A thesis submitted in partial ful¯llment of the requirements for the degree of Master of Science at George Mason University By Milind M. Parelkar Bachelor of Engineering University of Mumbai(Bombay), India, 2002 Director: Dr. Kris Gaj, Associate Professor Department of Electrical and Computer Engineering Fall 2005 George Mason University Fairfax, VA ii Copyright °c 2005 by Milind M. Parelkar All Rights Reserved iii Acknowledgments I would like to thank Dr. Kris Gaj for helping me throughout the course of this research. Special thanks to Pawel Chodowiec, without whose help, it would have been very di±cult to come up with good results, on time. iv Table of Contents Page Abstract . xii 1 Authenticated Encryption - Introduction and Motivation . 1 1.1 Cryptographic Goals . 1 1.2 What is Authenticated - Encryption? . 2 1.3 Target Applications for Authenticated - Encryption . 7 1.3.1 Encryption and Authentication of FPGA Bitstream . 7 1.3.2 Authenticated - Encryption in 802.11 Wireless LANs . 11 1.4 Authentication Techniques . 12 1.4.1 Hash Functions . 12 1.4.2 Message Authentication Codes (MACs) . -

1 Block Cipher Modes of Operation from a Hardware Implementation Perspective
1 Block Cipher Modes of Operation from a Hardware Implementation Perspective Debrup Chakraborty and Francisco Rodr´ıguez-Henr´ıquez Computer Science Department Centro de Investigaci´on y de Estudios Avanzados del IPN Av. Instituto Polit´ecnico Nacional No. 2508, M´exico D.F. e-mail:{debrup,francisco}@cs.cinvestav.mx 1.1 Introduction Block ciphers are one of the most important primitives in cryptology. They are based on well-understood mathematical and cryptographic principles. Due to their inherent efficiency, these ciphers are used in many kinds of applications which require bulk encryption at high speed. Generally speaking, a block cipher consists of at least two closely related algo- rithms: block encryption and block decryption. Block encryption takes as an input a fixed-length block (known as the plaintext) and transform it into another block of the same length (known as the ciphertext) under the action of a fixed secret key that may or may not have the same length of the plaintext. A block cipher must be invertible in the sense that by using the block decryption algorithm it should be always possible to recover the original plaintext from the ciphertext and the secret key. Figure 1.1 shows schematically the situation just described. We stress that once that the plain- text has been encrypted using a given key then, a successful decryption can only be performed by knowing that key. Due to this feature, block ciphers are classified as a secret or symmetric key primitives. Formally a block cipher is considered to be secure if it behaves like a strong pseudorandom permutation, i.e., a block cipher is secure if an adversary cannot dis- tinguish its output from a randomly chosen permutation. -

Mcoe: a Family of Almost Foolproof On-Line Authenticated Encryption Schemes
McOE: A Family of Almost Foolproof On-Line Authenticated Encryption Schemes Ewan Fleischmann, Christian Forler, and Stefan Lucks Bauhaus-University Weimar, Germany {ewan.fleischmann,christian.forler,stefan.lucks}@uni-weimar.de Abstract. On-Line Authenticated Encryption (OAE) combines privacy with data integrity and is on-line computable. Most block cipher-based schemes for Authenticated Encryption can be run on-line and are prov- ably secure against nonce-respecting adversaries. But they fail badly for more general adversaries. This is not a theoretical observation only – in practice, the reuse of nonces is a frequent issue1. In recent years, cryptographers developed misuse-resistant schemes for Authenticated Encryption. These guarantee excellent security even against general adversaries which are allowed to reuse nonces. Their dis- advantage is that encryption can be performed in an off-line way, only. This paper considers OAE schemes dealing both with nonce-respecting and with general adversaries. It introduces McOE,anefficientdesignfor OAE schemes. For this we present in detail one of the family members, McOE-X, which is a design solely based on a standard block cipher. As all the other member of the McOE family, it provably guarantees reasonable security against general adversaries as well as standard security against nonce-respecting adversaries. Keywords: authenticated encryption, on-line encryption, provable se- curity, misuse resistant. 1 Introduction On-Line Authenticated Encryption (OAE). Application software often requires a network channel that guarantees the privacy and authenticity of data be- ing communicated between two parties. Cryptographic schemes able to meet both of these goals are commonly referred to as Authenticated Encryption (AE) schemes. -
Design and Cryptanalysis of a Customizable Authenticated Encryption Algorithm
Rochester Institute of Technology RIT Scholar Works Theses 8-2014 Design and Cryptanalysis of a Customizable Authenticated Encryption Algorithm Matthew Joseph Kelly Follow this and additional works at: https://scholarworks.rit.edu/theses Recommended Citation Kelly, Matthew Joseph, "Design and Cryptanalysis of a Customizable Authenticated Encryption Algorithm" (2014). Thesis. Rochester Institute of Technology. Accessed from This Thesis is brought to you for free and open access by RIT Scholar Works. It has been accepted for inclusion in Theses by an authorized administrator of RIT Scholar Works. For more information, please contact [email protected]. Design and Cryptanalysis of a Customizable Authenticated Encryption Algorithm by Matthew Joseph Kelly A Thesis Submitted in Partial Fulfillment of the Requirements for the Degree of Master of Science in Computer Engineering Supervised by Alan Kaminsky Department of Computer Science & Marcin Łukowiak Department of Computer Engineering Kate Gleason College of Engineering Rochester Institute of Technology Rochester, New York August 2014 ii The thesis “Design and Cryptanalysis of a Customizable Authenticated Encryption Algorithm” by Matthew Joseph Kelly has been examined and approved by the following Examination Commit- tee: Alan Kaminsky Professor, Department of Computer Science Primary Advisor Marcin Łukowiak Associate Professor, Department of Computer Engineering Primary Advisor Michael Kurdziel Harris Corporation Reza Azarderakhsh Assistant Professor, Department of Computer Engineering Thesis Release Permission Form Rochester Institute of Technology Kate Gleason College of Engineering Title: Design and Cryptanalysis of a Customizable Authenticated Encryption Algorithm I, Matthew Joseph Kelly, hereby grant permission to the Wallace Memorial Library to reproduce my thesis in whole or part. Matthew Joseph Kelly Date iv Dedication To my parents, Donna and Martin. -

Improving the Sphinx Mix Network
Improving the Sphinx Mix Network Filipe Beato1, Kimmo Halunen2, and Bart Mennink1 1 Dept. Electrical Engineering, ESAT/COSIC, KU Leuven, and iMinds, Belgium ffilipe.beato,[email protected] 2 VTT Technical Research Center of Finland, Oulu, Finland Abstract. Secure mix networks consider the presence of multiple nodes that relay encrypted messages from one node to another in such a way that anonymous communication can be achieved. We consider the Sphinx mix formatting protocol by Danezis and Goldberg (IEEE Security and Privacy 2009), and analyze its use of symmetric-key cryptographic prim- itives. We scrutinize the reliance on multiple distinct primitives, as well as the use of the ancient LIONESS cipher, and suggest various paths towards improving the security and efficiency of the protocol. Keywords: Sphinx; mix network; authenticated encryption; sponge 1 Introduction With the large growth of Internet services, modern users rely more on digital and ubiquitous communications. In this digital domain, privacy needs to be protected against the very nature of the communications, which tend to be easily traceable and produce massive amounts of metadata. Hiding the metadata of communications is hard, but there are systems, called mix networks, that provide such capabilities. One example is the Sphinx [15] mix network, that is used in privacy protecting applications. The Sphinx mix network format provides security against powerful adversaries and good communications possibilities such as replies, which are not easily available in other such systems. The Sphinx protocol (see Section 2) uses internally many symmetric-key primitives. At first, there is the SHA-2 hash function for hashing. -

On the Security of the CCM Encryption Mode and of a Slight Variant Pierre-Alain Fouque, Gwenaëlle Martinet, Frédéric Valette, Sebastien Zimmer
On the Security of the CCM Encryption Mode and of a Slight Variant Pierre-Alain Fouque, Gwenaëlle Martinet, Frédéric Valette, Sebastien Zimmer To cite this version: Pierre-Alain Fouque, Gwenaëlle Martinet, Frédéric Valette, Sebastien Zimmer. On the Security of the CCM Encryption Mode and of a Slight Variant. Applied Cryptography and Network Security : 6th International Conference, ACNS 2008, 2008, New York, United States. pp.411-428, 10.1007/978-3- 540-68914-0_25. inria-00556684 HAL Id: inria-00556684 https://hal.inria.fr/inria-00556684 Submitted on 17 Jan 2011 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. On the Security of the CCM Encryption Mode and of a Slight Variant Pierre-Alain Fouque1 and Gwena¨elle Martinet2 and Fr´ed´eric Valette3 and S´ebastien Zimmer1 1 Ecole´ normale sup´erieure, 45 rue d’Ulm, 75005 Paris, France {Pierre-Alain.Fouque;Sebastien.Zimmer}@ens.fr 2 DCSSI Crypto Lab, 51 Boulevard de la Tour-Maubourg F-75700 Paris 07 SP, France [email protected] 3 CELAR, 35 Bruz, France [email protected] Abstract. In this paper, we present an analysis of the CCM mode of operations and of a slight variant. -
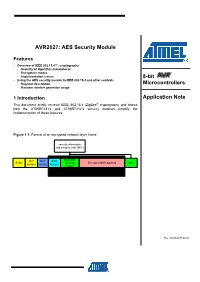
AVR2027: AES Security Module
AVR2027: AES Security Module Features • Overview of IEEE 802.15.4™, cryptography - Security of algorithm and protocol - Encryption modes - Implementation issues 8-bit • Using the AES security module in IEEE 802.15.4 and other contexts - Register description Microcontrollers - Random number generator usage 1 Introduction Application Note This document briefly reviews IEEE 802.15.4 /ZigBee® cryptography and shows how the AT86RF231’s and AT86RF212’s security modules simplify the implementation of these features. Figure 1-1. Format of an encrypted network layer frame security information and integrity code (MIC) Auxialiary PHY MAC NWK SYNC Security Encrypted NWK payload MIC Header Header Header Header part protected by MIC Rev. 8260A-AVR-09/09 2 Overview of IEEE 802.15.4 cryptography 2.1 Scope of IEEE 802.15.4 cryptography 2.1.1 Encryption Encryption is used to protect information to be read by some unauthorized third party, especially if a message is send over an unsecure channel. There should be no danger if a third party knows the implemented algorithm. The security must be based on a secret key only. The IEEE 802.15.4 standard uses AES-128 (Advanced Encryption Standard) with a 128 bit key length encryption. To the best knowledge of cryptographic research, this algorithm satisfies all modern security requirements; see [1], [2], [3]. However, the wrong application of a good algorithm may destroy security nevertheless. This can be avoided by so-called encryption modes, i.e. how a cryptographic algorithm is applied. Details are explained in 2.2.2. 2.1.2 Integrity protection Encryption is a defense against passive attacks, i.e. -

Atmel AT02333: Safe and Secure Bootloader Implementation for SAM3/4
APPLICATION NOTE Atmel AT02333: Safe and Secure Bootloader Implementation for SAM3/4 Atmel 32-bit Microcontroller Features • Getting familiar with the conception of in-field upgrading and bootloader • Discussing design considerations in the development of safe and secure bootloader • Understanding how the bootloader for SAM3/4 works Description This document introduces in-field firmware upgrading and describes various aspects of the implementation of a safe & secure bootloader. It discusses several design considerations in developing this kind of software, which readers can refer to when consulting this document. Correct bootloader implementation poses several challenges, such as correctly remapping the chip memory with the new-loaded program. Those issues will be described and solved in the following sections, with focus on Atmel® ARM® Cortex®-M based microcontroller. Simple bootloader software is also provided along with this application note as example. 42141A−SAM−06/2013 Table of Contents 1. Introduction ........................................................................................ 4 2. In-field Upgrading ............................................................................... 5 2.1 The Bootloader.................................................................................................. 5 2.2 Issues 6 2.2.1 Safety 7 2.2.2 Security ............................................................................................... 7 2.3 Possible Solutions ............................................................................................ -
CMAC CTR) and Encrypt-Then-MAC Composite (AES EAX) Modes of Operation in Cryptography Systems for Use in SMS-Based Secure Transmission
Comparison Between Encrypt-and-MAC Composite (CMAC CTR) and Encrypt-then-MAC Composite (AES EAX) Modes of Operation in Cryptography Systems for Use in SMS-based Secure Transmission Bao Guo and William Emmanuel Yu Abstract—In current mobile telecommunications systems, the II. OBJECTIVES OF THE STUDY security offered by these networks are limited. In order to be For particular M2M applications, the security of data used in use cases that require a high degree of security, such as M2M (financial, voting system), more security guarantees are transmission security is crucial. Security requirements may necessary. Therefore, additional security must be added on top vary depending on the type of service and business of existing networks. A common way to add security is by the requirements. For example, remote banking would require use of composite encryption schemes. Two (2) of these schemes privacy, authenticity and integrity while navigation systems are then compared in terms of performance: an would only need authenticity and integrity. It is shown that Encrypt-and-MAC composite scheme represented by AES in for these types of M2M applications Encrypt-then-MAC CTR mode and in CMAC mode and an Encrypt-then-MAC scheme using the EAX mode. These schemes are used in the composite schemes provide the most comprehensive amount context of an over the top protocol in SMS networks used in of security guarantee [3]. The goal of this study is to compare M2M applications. Results show that performance in terms of the performance of Encrypt-then-MAC versus transaction time is close between the two (2) composite schemes Encrypt-and-MAC composite schemes in cryptography when but the Encrypt-then-MAC scheme provides more guarantees.