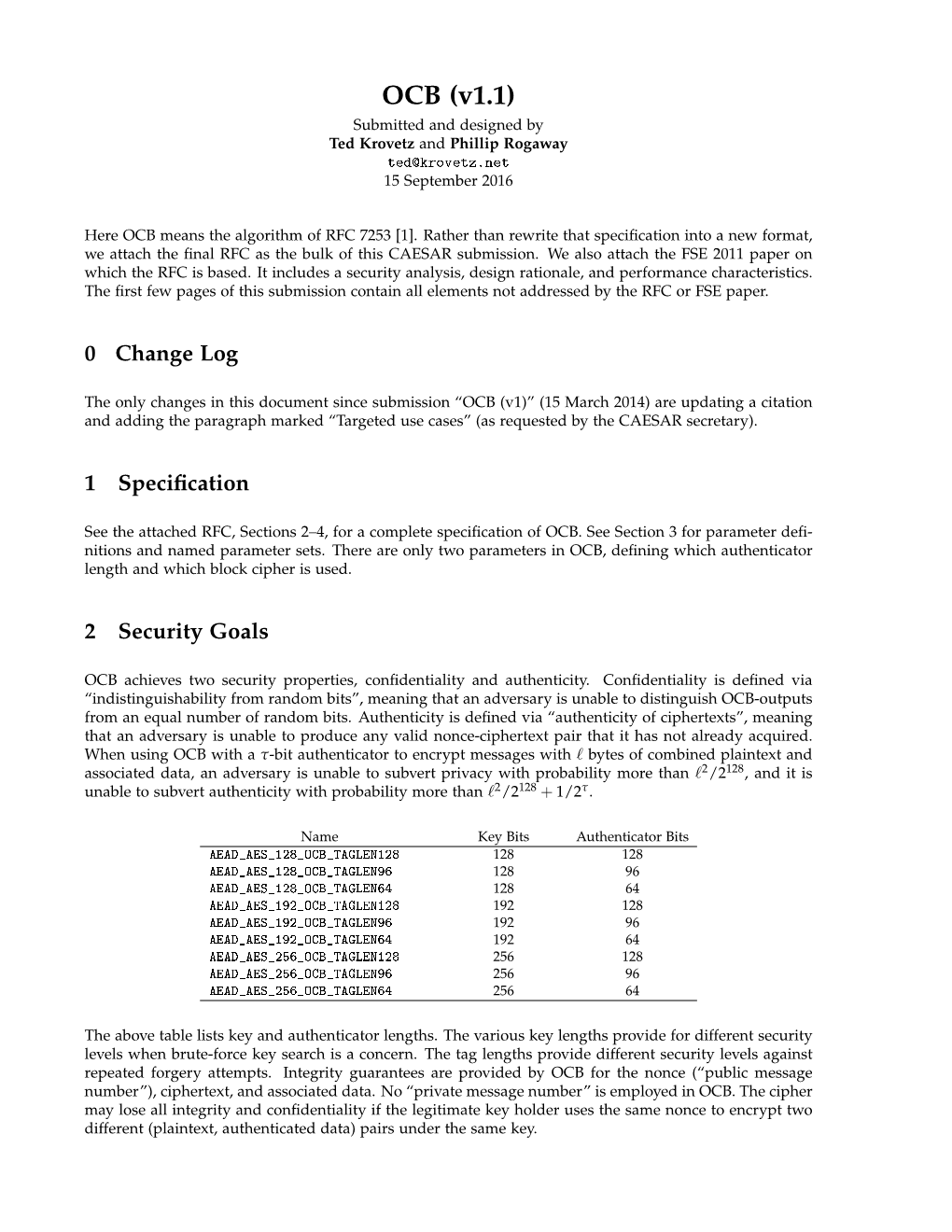
OCB (V1.1) Submitted and Designed by Ted Krovetz and Phillip Rogaway [email protected] 15 September 2016
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Analysis of Selected Block Cipher Modes for Authenticated Encryption
Analysis of Selected Block Cipher Modes for Authenticated Encryption by Hassan Musallam Ahmed Qahur Al Mahri Bachelor of Engineering (Computer Systems and Networks) (Sultan Qaboos University) – 2007 Thesis submitted in fulfilment of the requirement for the degree of Doctor of Philosophy School of Electrical Engineering and Computer Science Science and Engineering Faculty Queensland University of Technology 2018 Keywords Authenticated encryption, AE, AEAD, ++AE, AEZ, block cipher, CAESAR, confidentiality, COPA, differential fault analysis, differential power analysis, ElmD, fault attack, forgery attack, integrity assurance, leakage resilience, modes of op- eration, OCB, OTR, SHELL, side channel attack, statistical fault analysis, sym- metric encryption, tweakable block cipher, XE, XEX. i ii Abstract Cryptography assures information security through different functionalities, es- pecially confidentiality and integrity assurance. According to Menezes et al. [1], confidentiality means the process of assuring that no one could interpret infor- mation, except authorised parties, while data integrity is an assurance that any unauthorised alterations to a message content will be detected. One possible ap- proach to ensure confidentiality and data integrity is to use two different schemes where one scheme provides confidentiality and the other provides integrity as- surance. A more compact approach is to use schemes, called Authenticated En- cryption (AE) schemes, that simultaneously provide confidentiality and integrity assurance for a message. AE can be constructed using different mechanisms, and the most common construction is to use block cipher modes, which is our focus in this thesis. AE schemes have been used in a wide range of applications, and defined by standardisation organizations. The National Institute of Standards and Technol- ogy (NIST) recommended two AE block cipher modes CCM [2] and GCM [3]. -

GCM) for Confidentiality And
NIST Special Publication 800-38D Recommendation for Block DRAFT (April, 2006) Cipher Modes of Operation: Galois/Counter Mode (GCM) for Confidentiality and Authentication Morris Dworkin C O M P U T E R S E C U R I T Y Abstract This Recommendation specifies the Galois/Counter Mode (GCM), an authenticated encryption mode of operation for a symmetric key block cipher. KEY WORDS: authentication; block cipher; cryptography; information security; integrity; message authentication code; mode of operation. i Table of Contents 1 PURPOSE...........................................................................................................................................................1 2 AUTHORITY.....................................................................................................................................................1 3 INTRODUCTION..............................................................................................................................................1 4 DEFINITIONS, ABBREVIATIONS, AND SYMBOLS.................................................................................2 4.1 DEFINITIONS AND ABBREVIATIONS .............................................................................................................2 4.2 SYMBOLS ....................................................................................................................................................4 4.2.1 Variables................................................................................................................................................4 -
Block Cipher Modes
Block Cipher Modes Data and Information Management: ELEN 3015 School of Electrical and Information Engineering, University of the Witwatersrand March 25, 2010 Overview Motivation for Cryptographic Modes Electronic Codebook Mode (ECB) Cipher Block Chaining (CBC) Cipher Feedback Mode (CFB) Output Feedback Mode (OFB) 1. Cryptographic Modes Problem: With block ciphers, same plaintext block always enciphers to the same ciphertext block under the same key 1. Cryptographic Modes Solution: Cryptographic mode: • block cipher • feedback • simple operations Simple operations, as the security lies in the cipher. 1. Cryptographic Modes 1.1 Considerations • The mode should not compromise security of cipher • Mode should conceal patterns in plaintext • Some random starting point is needed • Difficult to manipulate the plaintext by changing ciphertext • Requires multiple messages to be encrypted with same key • No significant impact on efficiency of cipher • Ciphertext same size as plaintext • Fault tolerance - recover from errors 2. Electronic Codebook Mode Uses the block cipher without modifications Same plaintext block encrypts to same ciphertext under same key Each plaintext block is encrypted independently of other plaintext blocks. Corrupted bits only affects one block Dropped/inserted bits cause sync errors ! all subsequent blocks decipher incorrectly 2. Electronic Codebook Mode 2.1 Advantages ECB exhibits `random access property' because plaintext blocks are encrypted independently • Encryption and decryption can be done in any order • Beneficial for databases, records can be added, deleted, modified, encrypted and deleted independently of other records Parallel implementation • Different blocks can simultaneously be decrypted on separate processors Many messages can be encrypted with the same key, since each block is independent. 2. -

Item Box Subject Author Title Exps Pages Size Inches Pub. Date Grand
Item Box Subject Author Title Exps Pages Size Inches Pub. Date Grand Total: 3, 139, 369, 104, 343, 159, [and the 210 Namibian 51, 612, 191, 21, 44, 1, 39, 95, 428, docs so far is 2809] (2599) Central Africa:3 1 Central Africa—General Economics UNECA Subregional Strategies 19 32 8x11.5 Hints to Businessmen Visiting The London Board of 2 Central Africa—General Economics Congo (Brazzaville), Chad, Gabon 19 32 4.75x7.125 Trade and Central African Republic Purpose and Perfection Pottery as 3 Central Africa—General Art The Smithsonian Institution 3 4 8x9.25 a Woman's Art in Central Africa Botswana:139 National Institute of Access to Manual Skills Training in 1 Botswana—Bibliographies Bibliography Development and Cultural Botswana: An Annotated 9 13 8x11.5 Research Bibliography Social Thandiwe Kgosidintsi and 2 Botswana—Bibliographies Sciences—Information Publishing in Botswana 2 2 8.5x11 Neil Parsons Science National Institute of 3 Botswana—Bibliographies Bibliography Development Rearch and Working Papers 5 8 5.75x8.25 Documentation University of Botswana and Department of Library Studies 1 Botswana—Social Sciences Social Sciences 28 25 8.25x11.75 Swaziland Prospectus Social Refugees In Botswana: a Policy of 2 Botswana—Social Sciences United Nations 3 7 4.125x10.5 Sciences—Refugees Resettlement Projet De College Exterieur Du 3 Botswana—Social Sciences Social Sciences unknown 3 3 8.25x11.75 Botswana Community Relations in Botswana, with special reference to Francistown. Statement 4 Botswana—Social Sciences Social Sciences Republic of Botswana Delivered to the National Assembly 4 5 5.5x8 1971 by His Honor the Vice President Dt. -

Rigorous Cache Side Channel Mitigation Via Selective Circuit Compilation
RiCaSi: Rigorous Cache Side Channel Mitigation via Selective Circuit Compilation B Heiko Mantel, Lukas Scheidel, Thomas Schneider, Alexandra Weber( ), Christian Weinert, and Tim Weißmantel Technical University of Darmstadt, Darmstadt, Germany {mantel,weber,weissmantel}@mais.informatik.tu-darmstadt.de, {scheidel,schneider,weinert}@encrypto.cs.tu-darmstadt.de Abstract. Cache side channels constitute a persistent threat to crypto implementations. In particular, block ciphers are prone to attacks when implemented with a simple lookup-table approach. Implementing crypto as software evaluations of circuits avoids this threat but is very costly. We propose an approach that combines program analysis and circuit compilation to support the selective hardening of regular C implemen- tations against cache side channels. We implement this approach in our toolchain RiCaSi. RiCaSi avoids unnecessary complexity and overhead if it can derive sufficiently strong security guarantees for the original implementation. If necessary, RiCaSi produces a circuit-based, hardened implementation. For this, it leverages established circuit-compilation technology from the area of secure computation. A final program analysis step ensures that the hardening is, indeed, effective. 1 Introduction Cache side channels are unintended communication channels of programs. Cache- side-channel leakage might occur if a program accesses memory addresses that depend on secret information like cryptographic keys. When these secret-depen- dent memory addresses are loaded into a shared cache, an attacker might deduce the secret information based on observing the cache. Such cache side channels are particularly dangerous for implementations of block ciphers, as shown, e.g., by attacks on implementations of DES [58,67], AES [2,11,57], and Camellia [59,67,73]. -

Cryptographic Sponge Functions
Cryptographic sponge functions Guido B1 Joan D1 Michaël P2 Gilles V A1 http://sponge.noekeon.org/ Version 0.1 1STMicroelectronics January 14, 2011 2NXP Semiconductors Cryptographic sponge functions 2 / 93 Contents 1 Introduction 7 1.1 Roots .......................................... 7 1.2 The sponge construction ............................... 8 1.3 Sponge as a reference of security claims ...................... 8 1.4 Sponge as a design tool ................................ 9 1.5 Sponge as a versatile cryptographic primitive ................... 9 1.6 Structure of this document .............................. 10 2 Definitions 11 2.1 Conventions and notation .............................. 11 2.1.1 Bitstrings .................................... 11 2.1.2 Padding rules ................................. 11 2.1.3 Random oracles, transformations and permutations ........... 12 2.2 The sponge construction ............................... 12 2.3 The duplex construction ............................... 13 2.4 Auxiliary functions .................................. 15 2.4.1 The absorbing function and path ...................... 15 2.4.2 The squeezing function ........................... 16 2.5 Primary aacks on a sponge function ........................ 16 3 Sponge applications 19 3.1 Basic techniques .................................... 19 3.1.1 Domain separation .............................. 19 3.1.2 Keying ..................................... 20 3.1.3 State precomputation ............................ 20 3.2 Modes of use of sponge functions ......................... -

The EAX Mode of Operation
A preliminary version of this papers appears in Fast Software Encryption ’04, Lecture Notes in Computer Science, vol. ?? , R. Bimal and W. Meier ed., Springer-Verlag, 2004. This is the full version. The EAX Mode of Operation (A Two-Pass Authenticated-Encryption Scheme Optimized for Simplicity and Efficiency) ∗ † ‡ M. BELLARE P. ROGAWAY D. WAGNER January 18, 2004 Abstract We propose a block-cipher mode of operation, EAX, for solving the problem of authenticated-encryption with associated-data (AEAD). Given a nonce N, a message M, and a header H, our mode protects the privacy of M and the authenticity of both M and H. Strings N, M, and H are arbitrary bit strings, and the mode uses 2|M|/n + |H|/n + |N|/n block-cipher calls when these strings are nonempty and n is the block length of the underlying block cipher. Among EAX’s characteristics are that it is on-line (the length of a message isn’t needed to begin processing it) and a fixed header can be pre-processed, effectively removing the per-message cost of binding it to the ciphertext. EAX is obtained by first creating a generic-composition method, EAX2, and then collapsing its two keys into one. EAX is provably secure under a standard complexity-theoretic assumption. The proof of this fact is novel and involved. EAX is an alternative to CCM [26], which was created to answer the wish within standards bodies for a fully-specified and patent-free AEAD mode. As such, CCM and EAX are two-pass schemes, with one pass for achieving privacy and one for authenticity. -

Security Policy: Informacast Java Crypto Library
FIPS 140-2 Non-Proprietary Security Policy: InformaCast Java Crypto Library FIPS 140-2 Non-Proprietary Security Policy InformaCast Java Crypto Library Software Version 3.0 Document Version 1.2 June 26, 2017 Prepared For: Prepared By: Singlewire Software SafeLogic Inc. 1002 Deming Way 530 Lytton Ave, Suite 200 Madison, WI 53717 Palo Alto, CA 94301 www.singlewire.com www.safelogic.com Document Version 1.2 © Singlewire Software Page 1 of 35 FIPS 140-2 Non-Proprietary Security Policy: InformaCast Java Crypto Library Abstract This document provides a non-proprietary FIPS 140-2 Security Policy for InformaCast Java Crypto Library. Document Version 1.2 © Singlewire Software Page 2 of 35 FIPS 140-2 Non-Proprietary Security Policy: InformaCast Java Crypto Library Table of Contents 1 Introduction .................................................................................................................................................. 5 1.1 About FIPS 140 ............................................................................................................................................. 5 1.2 About this Document.................................................................................................................................... 5 1.3 External Resources ....................................................................................................................................... 5 1.4 Notices ......................................................................................................................................................... -
Implementation and Evaluation of Secure Industrial Ethernet Communication
Implementation and Evaluation of Secure Industrial Ethernet Communication Master of Science Thesis, Communication Engineering KAN YU Department of Signals and Systems CHALMERS UNIVERSITY OF TECHNOLOGY Göteborg, Sweden, August 2010 Page 2/88 Abstract Automation network security becomes increasingly important due to the introduction of Ethernet- based fieldbus protocols and cryptographic algorithms play a vital important role in these protocols. Choosing the most suitable cryptographic algorithms under consideration of security and performance according to different application cases is essential. In this thesis, we first present a comprehensive survey of most commonly used cryptographic algorithms which can be applied in automation networks and then identify our candidates based on existing literature and related works for further evaluation in ARM platform for industrial purpose. Finally, according to our evaluation results, we choose suitable algorithms for different applications: for symmetric algorithms, Twofish is recommended for best performance and eXtended Tiny Encryption Algorithm (XTEA) and Corrected Block Tiny Encryption Algorithm (XXTEA) are recommended for the least footprint; for Message Authentication Code (MAC) algorithms, UMAC is strongly recommended for excellent speed; for asymmetric algorithms, Elliptic Curve Cryptography (ECC) has much better performance than RSA at the same security level in our platform. Page 3/88 TABLE OF CONTENTS 1 INTRODUCTION .................................................................................................................................. -

Cs 255 (Introduction to Cryptography)
CS 255 (INTRODUCTION TO CRYPTOGRAPHY) DAVID WU Abstract. Notes taken in Professor Boneh’s Introduction to Cryptography course (CS 255) in Winter, 2012. There may be errors! Be warned! Contents 1. 1/11: Introduction and Stream Ciphers 2 1.1. Introduction 2 1.2. History of Cryptography 3 1.3. Stream Ciphers 4 1.4. Pseudorandom Generators (PRGs) 5 1.5. Attacks on Stream Ciphers and OTP 6 1.6. Stream Ciphers in Practice 6 2. 1/18: PRGs and Semantic Security 7 2.1. Secure PRGs 7 2.2. Semantic Security 8 2.3. Generating Random Bits in Practice 9 2.4. Block Ciphers 9 3. 1/23: Block Ciphers 9 3.1. Pseudorandom Functions (PRF) 9 3.2. Data Encryption Standard (DES) 10 3.3. Advanced Encryption Standard (AES) 12 3.4. Exhaustive Search Attacks 12 3.5. More Attacks on Block Ciphers 13 3.6. Block Cipher Modes of Operation 13 4. 1/25: Message Integrity 15 4.1. Message Integrity 15 5. 1/27: Proofs in Cryptography 17 5.1. Time/Space Tradeoff 17 5.2. Proofs in Cryptography 17 6. 1/30: MAC Functions 18 6.1. Message Integrity 18 6.2. MAC Padding 18 6.3. Parallel MAC (PMAC) 19 6.4. One-time MAC 20 6.5. Collision Resistance 21 7. 2/1: Collision Resistance 21 7.1. Collision Resistant Hash Functions 21 7.2. Construction of Collision Resistant Hash Functions 22 7.3. Provably Secure Compression Functions 23 8. 2/6: HMAC And Timing Attacks 23 8.1. HMAC 23 8.2. -

Siderand: a Heuristic and Prototype of a Side-Channel-Based Cryptographically Secure Random Seeder Designed to Be Platform- and Architecture-Agnostic
SideRand: A Heuristic and Prototype of a Side-Channel-Based Cryptographically Secure Random Seeder Designed to Be Platform- and Architecture-Agnostic JV ROIG, Advanced Research Center – Asia Pacific College Generating secure random numbers is vital to the security and privacy infrastructures we rely on today. Having a computer system generate a secure random number is not a trivial problem due to the deterministic nature of computer systems. Servers commonly deal with this problem through hardware-based random number generators, which can come in the form of expansion cards, dongles, or integrated into the CPU itself. With the explosion of network- and internet-connected devices, however, the problem of cryptography is no longer a server-centric problem; even small devices need a reliable source of randomness for cryptographic operations – for example, network devices and appliances like routers, switches and access points, as well as various Internet-of-Things (IoT) devices for security and remote management. This paper proposes a software solution based on side-channel measurements as a source of high- quality entropy (nicknamed “SideRand”), that can theoretically be applied to most platforms (large servers, appliances, even maker boards like RaspberryPi or Arduino), and generates a seed for a regular CSPRNG to enable proper cryptographic operations for security and privacy. This paper also proposes two criteria – openness and auditability – as essential requirements for confidence in any random generator for cryptographic use, and discusses how SideRand meets the two criteria (and how most hardware devices do not). CCS Concepts: • Security and privacy → Cryptography KEYWORDS Cryptographically secure random number generation; side-channel based CSPRNG 1 INTRODUCTION 1.1 Generating Random Numbers for Privacy and Security The ability to generate strong random numbers is essential to cryptography, and central to security and privacy in the IT world. -

Kriptografske Tehničke Sigurnosne Mjere
Sigurnost računalnih sustava Computer Systems Security Kriptografske tehničke sigurnosne mjere Marin Golub Sadržaj • Uvod: Jesu li i koliko su kriptoalgoritmi sigurni? • Napadi na simetrične i asimetrične kriptosustave • Asimetrični kriptosustavi – Kriptosustavi zasnovani na eliptičkim krivuljama • Funkcije za izračunavanje sažetka poruke – Napadi na funkcije za izračunavanje sažetka poruke – Elektronički vs. digitalni potpis – SHA-2 i SHA-3 • Kvantna kriptografija • Natječaji za nove kriptografske algoritme koji su u tijeku – Kriptografija prilagođena ugrađenim računalima (Lightweight Cryptography ) – Asimetrična kriptografija nakon kvantnih računala (Post-Quantum Cryptography ) SRS-Crypto-2/79 Osnovni pojmovi Kriptologija = kriptografija + kriptoanaliza Kriptografija • znanstvena disciplina (ili umjetnost?) sastavljanja poruka sa ciljem skrivanja sadržaja poruka Kriptoanaliza • znanstvena disciplina koja se bavi analizom skrivenih aspekata sustava i koristi se kako bi se ispitala (ili narušila) sigurnost kriptografskog sustava SRS-Crypto-3/79 Jesu li i koliko su kriptoalgoritmi sigurni? • Postoje specijalizirana računala za napad grubom silom na DES kriptosustav: COPACOBANA (A Cost-Optimized PArallel COde Breaker) • 12.12.2009. faktoriziran RSA-768 • na kvantnom računalu je riješen problem faktoriziranja velikih brojeva i problem diskretnog logaritma • 17.8.2004. - kineski i francuski znanstvenici su objavili članak pod naslovom: "Kolizija za hash funkcije: MD4, MD5, Haval-128 i RIPEMD" • 13.2.2005. - kineski znanstvenici: "Collision