The Value of Z Systems Virtualization Security
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

IBM Power Systems Solution Edition for Scale-Out Cloud
IBM Systems and Technology Solution Brief IBM Power Systems and Storage Solution Edition for Scale-Out Cloud Open source, Linux solution for scale-out data virtualization and cloud Cloud computing is no longer a question of “if” for IT organizations, but Highlights rather one of when, how and for which workloads. Cloud is widely understood to be an IT delivery model that can improve IT asset utilization, Allows open infrastructures to scale out intelligently, with less hardware, flexibility and responsiveness while reducing complexity and lowering power and cooling requirements costs. With these benefits come many complexities which need to be and better economics, using over considered as organizations define and implement a cloud delivery strategy. twice the bandwidth from previous Some technology options can hinder the efficiency and costs saving generations potential of the cloud by impeding interoperability, hampering workload Built-in data virtualization delivers performance, exposing security vulnerabilities and limiting scalability. seamless storage management from a single control point with no Building on the performance advantaged IBM POWER8™ architecture, the impact to applications Power Systems™ and Storage Solution Edition for Scale-Out Cloud Flexibility, agility and provides a superior cost effective platform with open source PowerKVM interoperability with open source, hypervisor, powerful data virtualized with IBM Storwize ® V7000, and community-driven virtualization and a single pane of glass for OpenStack-based cloud management for a single pane of glass cloud heterogeneous cloud management management. The Solution Edition reduces the timeframe for infrastructure deployments from months to days with integrated infrastructure and automated provisioning of virtualized resources. It ensures optimal cost effectiveness with Power scale out systems, automated Easy Tier® for flash and disk storage and Real-Time Compression™ that can store up to 5x as much data in the same physical space. -

IBM Power® Systems for SAS® Empowers Advanced Analytics Harry Seifert, Laurent Montaron, IBM Corporation
Paper 4695-2020 IBM Power® Systems for SAS® Empowers Advanced Analytics Harry Seifert, Laurent Montaron, IBM Corporation ABSTRACT For over 40+ years of partnership between IBM and SAS®, clients have been benefiting from the added value brought by IBM’s infrastructure platforms to deploy SAS analytics, and now SAS Viya’s evolution of modern analytics. IBM Power® Systems and IBM Storage empower SAS environments with infrastructure that does not make tradeoffs among performance, cost, and reliability. The unified solution stack, comprising server, storage, and services, reduces the compute time, controls costs, and maximizes resilience of SAS environment with ultra-high bandwidth and highest availability. INTRODUCTION We will explore how to deploy SAS on IBM Power Systems platforms and unleash the full potential of the infrastructure, to reduce deployment risk, maximize flexibility and accelerate insights. We will start by reviewing IBM and SAS’s technology relationship and the current state of SAS products on IBM Power Systems. Then we will look at some of the infrastructure options to deploy SAS 9.4 on IBM Power Systems and IBM Storage, while maximizing resiliency & throughput by leveraging best practices. Next, we will look at SAS Viya, which introduces changes to the underlying infrastructure requirements while remaining able to be deployed alongside a traditional SAS 9.4 operation. We’ll explore the various deployment modes available. Finally, we’ll look at tuning practices and reference materials available for a deeper dive in deploying SAS on IBM platforms. SAS: 40 YEARS OF PARTNERSHIP WITH IBM IBM and SAS have been partners since the founding of SAS. -

POWER® Processor-Based Systems
IBM® Power® Systems RAS Introduction to IBM® Power® Reliability, Availability, and Serviceability for POWER9® processor-based systems using IBM PowerVM™ With Updates covering the latest 4+ Socket Power10 processor-based systems IBM Systems Group Daniel Henderson, Irving Baysah Trademarks, Copyrights, Notices and Acknowledgements Trademarks IBM, the IBM logo, and ibm.com are trademarks or registered trademarks of International Business Machines Corporation in the United States, other countries, or both. These and other IBM trademarked terms are marked on their first occurrence in this information with the appropriate symbol (® or ™), indicating US registered or common law trademarks owned by IBM at the time this information was published. Such trademarks may also be registered or common law trademarks in other countries. A current list of IBM trademarks is available on the Web at http://www.ibm.com/legal/copytrade.shtml The following terms are trademarks of the International Business Machines Corporation in the United States, other countries, or both: Active AIX® POWER® POWER Power Power Systems Memory™ Hypervisor™ Systems™ Software™ Power® POWER POWER7 POWER8™ POWER® PowerLinux™ 7® +™ POWER® PowerHA® POWER6 ® PowerVM System System PowerVC™ POWER Power Architecture™ ® x® z® Hypervisor™ Additional Trademarks may be identified in the body of this document. Other company, product, or service names may be trademarks or service marks of others. Notices The last page of this document contains copyright information, important notices, and other information. Acknowledgements While this whitepaper has two principal authors/editors it is the culmination of the work of a number of different subject matter experts within IBM who contributed ideas, detailed technical information, and the occasional photograph and section of description. -
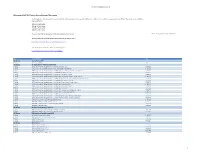
IBM Power Systems Solution for Mariadb
IBM Power Systems solution for MariaDB Performance overview of MariaDB Enterprise on Linux on Power featuring the new IBM POWER8 technology Axel Schwenke MariaDB Corporation Hari Reddy IBM Systems and Technology Group ISV Enablement Basu Vaidyanathan IBM Systems and Technology Group Performance Analysis October 2014 © Copyright IBM Corporation, 2014 Table of contents Abstract........................................................................................................................................1 Introduction .................................................................................................................................1 Advantages of MariaDB on Power Systems.............................................................................1 MariaDB architecture ..................................................................................................................2 Sysbench OLTP benchmark.................................................................................................................... 3 MariaDB performance.............................................................................................................................. 3 Relative performance of IBM Power S822L and IBM System x3650 M4 ................................................ 3 Power Systems built with the POWER8 technology................................................................6 Tested configuration details ......................................................................................................7 -

IBM Power System E850 the Most Agile 4-Socket System in the Marketplace, Optimized for Performance, Reliability and Expansion
IBM Systems Data Sheet IBM Power System E850 The most agile 4-socket system in the marketplace, optimized for performance, reliability and expansion Businesses today are demanding faster insights that analyze more data in Highlights new ways. They need to implement applications in days versus months, and they need to achieve all these goals while reducing IT costs. This is ●● ●●Designed for data and analytics, delivers creating new demands on IT infrastructures, requiring new levels of per- secure, reliable performance in a compact, 4-socket system formance and the flexibility to respond to new business opportunities, all at an affordable price. ●● ●●Can flexibly scale to rapidly respond to changing business needs The IBM® Power® System E850 server offers a unique blend of ●● ●●Can reduce IT costs through application enterprise-class capabilities in a space-efficient, 4-socket system with consolidation, higher availability and excellent price performance. With up to 48 IBM POWER8™ processor virtualization to yield over 70 percent utilization cores, advanced IBM PowerVM® virtualization that can yield over 70 percent system utilization and Capacity on Demand (CoD), no other 4-socket system in the industry delivers this combination of performance, efficiency and business agility. These capabilities make the Power E850 server an ideal platform for medium-size businesses and as a departmental server or data center building block for large enterprises. Designed for the demands of big data and analytics Businesses are amassing a wealth of data and IBM Power Systems™, built with innovation to support today’s data demands, can store it, secure it and, most important, extract actionable insight from it. -

IBM Power Systems Performance Report Apr 13, 2021
IBM Power Performance Report Power7 to Power10 September 8, 2021 Table of Contents 3 Introduction to Performance of IBM UNIX, IBM i, and Linux Operating System Servers 4 Section 1 – SPEC® CPU Benchmark Performance 4 Section 1a – Linux Multi-user SPEC® CPU2017 Performance (Power10) 4 Section 1b – Linux Multi-user SPEC® CPU2017 Performance (Power9) 4 Section 1c – AIX Multi-user SPEC® CPU2006 Performance (Power7, Power7+, Power8) 5 Section 1d – Linux Multi-user SPEC® CPU2006 Performance (Power7, Power7+, Power8) 6 Section 2 – AIX Multi-user Performance (rPerf) 6 Section 2a – AIX Multi-user Performance (Power8, Power9 and Power10) 9 Section 2b – AIX Multi-user Performance (Power9) in Non-default Processor Power Mode Setting 9 Section 2c – AIX Multi-user Performance (Power7 and Power7+) 13 Section 2d – AIX Capacity Upgrade on Demand Relative Performance Guidelines (Power8) 15 Section 2e – AIX Capacity Upgrade on Demand Relative Performance Guidelines (Power7 and Power7+) 20 Section 3 – CPW Benchmark Performance 19 Section 3a – CPW Benchmark Performance (Power8, Power9 and Power10) 22 Section 3b – CPW Benchmark Performance (Power7 and Power7+) 25 Section 4 – SPECjbb®2015 Benchmark Performance 25 Section 4a – SPECjbb®2015 Benchmark Performance (Power9) 25 Section 4b – SPECjbb®2015 Benchmark Performance (Power8) 25 Section 5 – AIX SAP® Standard Application Benchmark Performance 25 Section 5a – SAP® Sales and Distribution (SD) 2-Tier – AIX (Power7 to Power8) 26 Section 5b – SAP® Sales and Distribution (SD) 2-Tier – Linux on Power (Power7 to Power7+) -

POWER8: the First Openpower Processor
POWER8: The first OpenPOWER processor Dr. Michael Gschwind Senior Technical Staff Member & Senior Manager IBM Power Systems #OpenPOWERSummit Join the conversation at #OpenPOWERSummit 1 OpenPOWER is about choice in large-scale data centers The choice to The choice to The choice to differentiate innovate grow . build workload • collaborative • delivered system optimized innovation in open performance solutions ecosystem • new capabilities . use best-of- • with open instead of breed interfaces technology scaling components from an open ecosystem Join the conversation at #OpenPOWERSummit Why Power and Why Now? . Power is optimized for server workloads . Power8 was optimized to simplify application porting . Power8 includes CAPI, the Coherent Accelerator Processor Interconnect • Building on a long history of IBM workload acceleration Join the conversation at #OpenPOWERSummit POWER8 Processor Cores • 12 cores (SMT8) 96 threads per chip • 2X internal data flows/queues • 64K data cache, 32K instruction cache Caches • 512 KB SRAM L2 / core • 96 MB eDRAM shared L3 • Up to 128 MB eDRAM L4 (off-chip) Accelerators • Crypto & memory expansion • Transactional Memory • VMM assist • Data Move / VM Mobility • Coherent Accelerator Processor Interface (CAPI) Join the conversation at #OpenPOWERSummit 4 POWER8 Core •Up to eight hardware threads per core (SMT8) •8 dispatch •10 issue •16 execution pipes: •2 FXU, 2 LSU, 2 LU, 4 FPU, 2 VMX, 1 Crypto, 1 DFU, 1 CR, 1 BR •Larger Issue queues (4 x 16-entry) •Larger global completion, Load/Store reorder queue •Improved branch prediction •Improved unaligned storage access •Improved data prefetch Join the conversation at #OpenPOWERSummit 5 POWER8 Architecture . High-performance LE support – Foundation for a new ecosystem . Organic application growth Power evolution – Instruction Fusion 1600 PowerPC . -
IBM Services ISMS / PIMS Products / Pids in Scope
1H 2021 Certified Product List IBM services ISMS/PIMS Product/Service Offerings/PIDs in scope The following is a list of products associated with the offering bundles in scope of the IBM services information security management system (ISMS). The Cloud services ISMS has been certified on: ISO/IEC 27001:2013 ISO/IEC 27017:2015 ISO/IEC 27018:2019 ISO/IEC 27701:2019 As well as the IBM Cloud Services STAR Self-Assessment found here: This listing is current as of 07/20/2021 IBM Cloud Services STAR Self-Assessment Cloud Controls Matrix v3.0.1 https://cloudsecurityalliance.org/registry/ibm-cloud/ To find out more about IBM Cloud compliance go to: https://www.ibm.com/cloud/compliance/global type groupNameproductName pids ISO Group AccessHub-at-IBM Offering AccessHub-at-IBM N/A ISO Group AI Applications - Maximo and TRIRIGA Offering IBM Enterprise Asset Management Anywhere on Cloud (Maximo) 5725-Z55 Offering IBM Enterprise Asset Management Anywhere on Cloud (Maximo) Add-On 5725-Z55 Offering IBM Enterprise Asset Management on Cloud (Maximo) Asset Configuration Manager Add-On 5725-P73 Offering IBM Enterprise Asset Management on Cloud (Maximo) Aviation Add-On 5725-P73 Offering IBM Enterprise Asset Management on Cloud (Maximo) Calibration Add-On 5725-P73 Offering IBM Enterprise Asset Management on Cloud (Maximo) for Managed Service Provider Add-On 5725-P73 Offering IBM Enterprise Asset Management on Cloud (Maximo) Health, Safety and Environment Manager Add-On 5725-P73 Offering IBM Enterprise Asset Management on Cloud (Maximo) Life Sciences Add-On -

Improving Productivity with IBM ISPF Productivity Tool V7.1 for Z/OS
Front cover Improving Productivity with IBM ISPF Productivity Tool V7.1 for z/OS Enhance system navigation and access of your ISPF environment Use Point and Shoot functionality Enhance your IEBCOPY batch utility operation Steve Coalbran Mark Leung Michael Rotter Jean Mothersele Eugenie Alexander Chaitra Narayanaswamy Rodney Almodovar Kevin Neubert Balachandran Chandrasekaran Richard Pace Pearlson Christopher Walter Zakorchemny ibm.com/redbooks International Technical Support Organization Improving Productivity with IBM ISPF Productivity Tool V7.1 for z/OS April 2013 SG24-8093-00 Note: Before using this information and the product it supports, read the information in “Notices” on page xi. First Edition (April 2013) This edition applies to Version 7, Release 1, Modification 0 of ISPF Productivity Tool (product number 5655-SPF). © Copyright International Business Machines Corporation 2013. All rights reserved. Note to U.S. Government Users Restricted Rights -- Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents Notices . xi Trademarks . xii Preface . xiii The team who wrote this book . xiv Now you can become a published author, too! . xvii Comments welcome. xvii Stay connected to IBM Redbooks . xviii Chapter 1. Introduction to ISPF Productivity Tool V7.1 . 1 1.1 Targeted audience . 2 1.2 Definition of terms . 2 1.3 IPT batch utility . 3 1.4 IPT seamless integration with ISPF . 3 1.5 Learning IPT . 3 1.6 Increased productivity . 4 1.7 Integration with other products . 4 1.8 Object Linking and Embedding . 5 1.9 z/OS panel images . 5 1.10 Object List . 5 1.11 IPT functional overview . -
Power Systems Presentation Template Full Version
Power Systems Academic Initiative (PSAI) Program Overview November 2017 Teaching IBM Power Skills for 21 Years Historical Perspective 1996 2002 2004 2008 2009 2012 2017 Power Systems 361% Academic Initiative PSAI Mission Growth (since 2012) (PSAI) Transferred to STG Training IBM Academic Power Systems Initiative: iSeries announced AS/400 IBM Scholars zSeries Partners in Program: iSeries Education Mission: To help provide market-ready Power skills to our clients by working with colleges and universities worldwide Power2 Systems Academic Initiative 2 PSAI Snapshot Open to colleges and universities worldwide with 623 participating schools representing 68 countries. ✓ Educate: Increase awareness and education of students about Power Systems technology and operating systems -- IBM i, AIX, and Linux. ✓ Equip: Provide educators with materials, technology, and resources to teach Power Systems technology, skills, and business applications. Member schools are also eligible for significant discounts on hardware and software lease/purchase to be used for teaching and/or research. ✓ Connect: Help educators establish connections with their local IBM Power Systems business community to encourage collaboration. ✓ Employ: Facilitate linkage between graduates and clients for internships and jobs that require Power Systems skills. Provide access to Power Systems Job Board. * Participating means a school is: teaching IBM Power in a classroom or online, doing research on Power, using our academic cloud for homework/classwork/projects, downloading courses, -

Hortonworks Data Platform on IBM Power Systems
IBM Systems Solution brief Hortonworks Data Platform on IBM Power Systems Secure, enterprise-ready open source Apache Hadoop distribution for the leading open server for Big Data Analytics and artificial intelligence. Hortonworks Data Platform (HDP) on IBM Power Systems™ delivers Highlights a superior solution for the connected enterprise data platform. With industry-leading performance and IT efficiency combined with the • Superior performance and flexibility — best of open technology innovation to accelerate big data analytics Up to 1.7 times performance advantage versus competing x86-based solutions.1 and artificial intelligence, organizations can unlock and scale data- Right-size to your workload with an driven insights for the business like never before. unmatched range of Linux® server options. • Maximum efficiency—Reduce storage Hortonworks Data Platform infrastructure requirements by three times An industry-leading, secure and enterprise-ready open source Apache compared to HDFS when integrating with Hadoop distribution, HDP addresses a range of data-at-rest use cases, IBM® Elastic Storage™ Server with IBM Spectrum Scale™ erasure coding.2 powering real-time customer applications and delivering robust analytics to accelerate decision-making and innovation. • Ready for cognitive —Allows seamless integration of machine and deep learning using IBM’s PowerAI deep learning platform. HDP uses the Hadoop Distributed File System (HDFS) for scalable, fault-tolerant big data storage and Hadoop’s centralized Yet Another • Committed to client success and open Resource Negotiator (YARN) architecture for resource and workload innovation —Complete, enterprise-ready solution built on open hardware and management. YARN enables a range of data processing engines software technology that is fully tested including SQL, real-time streaming and batch processing, among and offered with industry-leading support others, to interact simultaneously with shared datasets, avoiding and expertise. -

IBM Power System S822LC for Big Data – Two-Socket Linux Server
IBM Systems Data Sheet IBM Power System S822LC for Big Data – two- socket Linux server A storage-rich, high-data- throughput server for data-intensive workloads In today’s demanding digital economy, business is competition, and you Highlights have to do everything you can to separate your business from the rest. With the constant influx of data and data sources, companies need to be ● Big data: The exponential growth in able to process data faster than ever before to stay ahead. OpenPOWER data needs a server designed for it. The IBM® Power System S822LC for Big Data LC servers are different by design—engineered at virtually every level and is purpose- built for high- data- intensive designed to be more powerful and open. Put your most data-intensive Linux workloads analytics workloads on the servers that were born to run them. ● Price-p erformance: Leveraging the IBM POWER8® architecture and a IBM Power System S822LC for Big Data is a scale-out Linux server purpose- built big data server design, that delivers a storage rich, high-data- throughput design built on open experience a total- cost- of- ownership (TCO) leadership standards to meet the big data workloads of today and grow with your needs for tomorrow. ● Open designs: OpenPOWER ecosystem and technologies from some of the world’s most innovative companies The IBM Power System S822LC for Big Data provides: ● Consolidated server footprint with 42 percent more virtual machines 1 (VMs) in the same footprint as competitive x86 servers ● Superior data throughput and performance for high-value