My Book Desktop Storage User Manual
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

What Is Cloud-Based Backup and Recovery?
White paper Cover Image Pick an image that is accurate and relevant to the content, in a glance, the image should be able to tell the story of the asset 550x450 What is cloud-based backup and recovery? Q120-20057 Executive Summary Companies struggle with the challenges of effective backup and recovery. Small businesses lack dedicated IT resources to achieve and manage a comprehensive data protection platform, and enterprise firms often lack the budget and resources for implementing truly comprehensive data protection. Cloud-based backup and recovery lets companies lower their Cloud-based backup and recovery lets data protection cost or expand their capabilities without raising costs or administrative overhead. Firms of all sizes can companies lower their data protection benefit from cloud-based backup and recovery by eliminating cost or expand their capabilities without on-premises hardware and software infrastructure for data raising costs or administrative overhead.” protection, and simplifying their backup administration, making it something every company should consider. Partial or total cloud backup is a good fit for most companies given not only its cost-effectiveness, but also its utility. Many cloud- based backup vendors offer continuous snapshots of virtual machines, applications, and changed data. Some offer recovery capabilities for business-critical applications such as Microsoft Office 365. Others also offer data management features such as analytics, eDiscovery and regulatory compliance. This report describes the history of cloud-based backup and recovery, its features and capabilities, and recommendations for companies considering a cloud-based data protection solution. What does “backup and recovery” mean? There’s a difference between “backup and recovery” and “disaster recovery.” Backup and recovery refers to automated, regular file storage that enables data recovery and restoration following a loss. -
STATEMENT of WORK: SGS File System
ATTACHMENT A STATEMENT OF WORK: SGS File System DOE National Nuclear Security Administration & the DOD Maryland Office April 25, 2001 File Systems SOW April 25, 2001 Table of Contents TABLE OF CONTENTS ..................................................................................................................................2 1.0 OVERVIEW.................................................................................................................................................4 1.1 INTRODUCTION ..........................................................................................................................................4 2.0 MOTIVATION ............................................................................................................................................5 2.1 THE NEED FOR IMPROVED FILE SYSTEMS .................................................................................................5 2.2 I/O CHARACTERIZATION OF IMPORTANT APPLICATIONS...........................................................................6 2.3 CURRENT AND PROJECTED ENVIRONMENTS AT LLNL, LANL, SANDIA, AND THE DOD .........................6 2.4 SUMMARY OF FIVE TECHNOLOGY CATEGORIES ........................................................................................9 3.0 MINIMUM REQUIREMENTS (GO/NO-GO CRITERIA)..................................................................12 3.1 POSIX-LIKE INTERFACE [MANDATORY]........................................................................................12 3.2 INTEGRATION -
Introduction to Computer Concepts
MANAGING PUBLIC SECTOR RECORDS A Training Programme Understanding Computers: An Overview for Records and Archives Staff INTERNATIONAL INTERNATIONAL RECORDS COUNCIL ON ARCHIVES MANAGEMENT TRUST MANAGING PUBLIC SECTOR RECORDS: A STUDY PROGRAMME UNDERSTANDING COMPUTERS: AN OVERVIEW FOR RECORDS AND ARCHIVES STAFF MANAGING PUBLIC SECTOR RECORDS A STUDY PROGRAMME General Editor, Michael Roper; Managing Editor, Laura Millar UNDERSTANDING COMPUTERS: AN OVERVIEW FOR RECORDS AND ARCHIVES STAFF INTERNATIONAL RECORDS INTERNATIONAL MANAGEMENT TRUST COUNCIL ON ARCHIVES MANAGING PUBLIC SECTOR RECORDS: A STUDY PROGRAMME Understanding Computers: An Overview for Records and Archives Staff © International Records Management Trust, 1999. Reproduction in whole or in part, without the express written permission of the International Records Management Trust, is strictly prohibited. Produced by the International Records Management Trust 12 John Street London WC1N 2EB UK Printed in the United Kingdom. Inquiries concerning reproduction or rights and requests for additional training materials should be addressed to International Records Management Trust 12 John Street London WC1N 2EB UK Tel: +44 (0) 20 7831 4101 Fax: +44 (0) 20 7831 7404 E-mail: [email protected] Website: http://www.irmt.org Version 1/1999 MPSR Project Personnel Project Director Anne Thurston has been working to define international solutions for the management of public sector records for nearly three decades. Between 1970 and 1980 she lived in Kenya, initially conducting research and then as an employee of the Kenya National Archives. She joined the staff of the School of Library, Archive and Information Studies at University College London in 1980, where she developed the MA course in Records and Archives Management (International) and a post-graduate research programme. -

Winreporter Documentation
WinReporter documentation Table Of Contents 1.1 WinReporter overview ............................................................................................... 1 1.1.1.................................................................................................................................... 1 1.1.2 Web site support................................................................................................. 1 1.2 Requirements.............................................................................................................. 1 1.3 License ....................................................................................................................... 1 2.1 Welcome to WinReporter........................................................................................... 2 2.2 Scan requirements ...................................................................................................... 2 2.3 Simplified Wizard ...................................................................................................... 3 2.3.1 Simplified Wizard .............................................................................................. 3 2.3.2 Computer selection............................................................................................. 3 2.3.3 Validate .............................................................................................................. 4 2.4 Advanced Wizard....................................................................................................... 5 2.4.1 -
PROTECTING DATA from RANSOMWARE and OTHER DATA LOSS EVENTS a Guide for Managed Service Providers to Conduct, Maintain and Test Backup Files
PROTECTING DATA FROM RANSOMWARE AND OTHER DATA LOSS EVENTS A Guide for Managed Service Providers to Conduct, Maintain and Test Backup Files OVERVIEW The National Cybersecurity Center of Excellence (NCCoE) at the National Institute of Standards and Technology (NIST) developed this publication to help managed service providers (MSPs) improve their cybersecurity and the cybersecurity of their customers. MSPs have become an attractive target for cyber criminals. When an MSP is vulnerable its customers are vulnerable as well. Often, attacks take the form of ransomware. Data loss incidents—whether a ransomware attack, hardware failure, or accidental or intentional data destruction—can have catastrophic effects on MSPs and their customers. This document provides recommend- ations to help MSPs conduct, maintain, and test backup files in order to reduce the impact of these data loss incidents. A backup file is a copy of files and programs made to facilitate recovery. The recommendations support practical, effective, and efficient back-up plans that address the NIST Cybersecurity Framework Subcategory PR.IP-4: Backups of information are conducted, maintained, and tested. An organization does not need to adopt all of the recommendations, only those applicable to its unique needs. This document provides a broad set of recommendations to help an MSP determine: • items to consider when planning backups and buying a backup service/product • issues to consider to maximize the chance that the backup files are useful and available when needed • issues to consider regarding business disaster recovery CHALLENGE APPROACH Backup systems implemented and not tested or NIST Interagency Report 7621 Rev. 1, Small Business planned increase operational risk for MSPs. -
Backup Reminders Once You Have Created Your Backup, Take a Moment 1
External Hard Drives—There are a number of easily accessible, but if your laptop was stolen you’d external hard drives that can be connected to your be without a machine and without your backup! computer through the Firewire or USB port. Many Treat your backups with extreme care! of these hard drives can be configured to automati- cally synchronize folders on your desktop with the Destroy your old backups. As you conduct your folders on the external drive. Although this some- backups more frequently, you’ll end up with a pile what automates the backup process, these drives can of old backup media. Be sure to dispose of old also be easily stolen! media properly. CD and DVDs can be destroyed simply by using a pair of scissors and scratching the How to Backup back of the CD several times. There are also media Backing up your data can be as easy as copying and shredders which work just like a paper shredder pasting the files to the backup drive or you can use leaving your backups in hundred of pieces. Just be specialized programs to help create your backup. sure that the data is no longer readable before you Most ITS Windows computers have Roxio Easy CD toss the backups in the trash. Creator installed. Instructions for using Roxio are located on our website at smu.edu/help/resources/ Keep a copy of your backup off site. You may wish backup/backup.asp. For Macs, simply drag the files to store a backup copy at home in the event of theft to the CDRW drive and click Burn. -

Chapter 9– Computer File Formats
PERA Employer Manual Chapter 9 - Computer File Formats IN THIS CHAPTER: • Testing Process Chapter 9– • Contribution (SDR) File Computer File Formats Layout » Contribution File Over 800 employers use PERA’s online Employer Reporting and Header Information System (ERIS) to send computer files to PERA for pro- » Plan Summary Record cessing. » Detail Transactions » Reporting an PERA has the following computer file formats. Adjustment • Contribution Edits 1. The Contribution file (also called the SDR file) provides the pay • Demographic File Layout period salary and contribution data for electronic submission of • Exclusion Report File the Salary Deduction Report (SDR). The file includes three types » Excel Format of records: the header, plan summary, and detail member trans- » Text File Format actions. As a general rule, the Contribution data file must be a fixed length text file. Employers that have more than 50 active members and do not have technical support to convert their pay- roll data into the text format may contact PERA staff at 651-296- 3636 or 1-888-892-7372 option #2 to discuss submitting their data via Excel. Last chapter 9 revision: 2. The Demographic Data Record format has a single record July 9, 2018 type that used to enroll new employees into a PERA plan or to update a member’s retirement account status as employment changes, such as leaves of absence or terminations occur, or to report member’s personal data changes, such as changes in name or address. 3. The Exclusion Report file is used to comply with the annual legal requirement of providing information about all employees – including elected officials – who worked during the reporting 9-1 PERA Employer Manual Chapter 9 - Computer File Formats year and were not members of a PERA Defined Benefit or Defined Contribution Plan or another Minnesota public retirement system. -
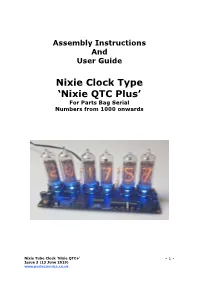
Nixie Clock Type 'Nixie QTC Plus'
Assembly Instructions And User Guide Nixie Clock Type ‘Nixie QTC Plus’ For Parts Bag Serial Numbers from 1000 onwards Nixie Tube Clock ‘Nixie QTC+’ - 1 - Issue 3 (13 June 2019) www.pvelectronics.co.uk REVISION HISTORY Issue Date Reason for Issue Number 3 13 June 2019 Added support for Dekatron Sync Pulse 2 01 October 2018 C5 changed to 15pF Draft 1 29 August 2018 New document Nixie Tube Clock ‘Nixie QTC+’ - 2 - Issue 3 (13 June 2019) www.pvelectronics.co.uk 1. INTRODUCTION 1.1 Nixie QTC Plus - Features Hours, Minutes and Seconds display Drives a wide range of medium sized solder-in tubes Uses a Quartz Crystal Oscillator as the timebase 12 or 24 hour modes Programmable leading zero blanking Date display in either DD.MM.YY or MM.DD.YY or YY.MM.DD format Programmable date display each minute Scrolling display of date or standard display Alarm, with programmable snooze period Optional GPS / WiFi / XTERNA synchronisation with status indicator LED Dedicated DST button to switch between DST and standard time Supercapacitor backup. Keeps time during short power outages Simple time setting using two buttons Configurable for leading zero blanking Double dot colon neon lamps 11 colon neon modes including AM / PM indication (top / bottom or left / right), railroad (slow or fast) etc. Seconds can be reset to zero to precisely the set time Programmable night mode - blanked or dimmed display to save tubes or prevent sleep disturbance Rear Indicator LEDs dim at night to prevent sleep disturbance Weekday aware ‘Master Blank’ function to turn off tubes and LEDs on weekends or during working hours Separate modes for colon neons during night mode Standard, fading, or crossfading with scrollback display modes ‘Slot Machine’ Cathode poisoning prevention routine Programmable RGB tube lighting – select your favourite colour palette 729 colours possible. -

Cloudberry Backup
CloudBerry Backup Installation and Configuration Guide CloudBerry Backup Installation and Configuration Guide Getting Started with CloudBerry Backup CloudBerry Backup (CBB) solution was designed to facilitate PC and server data backup operations to multiple remote locations. It is integrated with top Cloud storage providers, allowing you to access each of your storage or start a sign up to a Cloud platform directly from CBB. It also works fine with network destinations like NAS (Network Attached Storage) or directly connected drives. This document is the complete guide to the CloudBerry Backup deployment, configuration, and usage. Product Editions & Licensing The CBB can be downloaded directly from CloudBerry website with several editions. ● Windows Desktop (including FREE Edition) / Server. ● Microsoft SQL Server. ● Microsoft Exchange Server. ● Oracle Database. ● Ultimate (former Enterprise). ● CloudBerry Backup for NAS (QNAP and Synology). They differ in functionality, storage limits and individual solutions availability. We accomplished a chart with basic editions to give a clear perspective. CBB Edition Desktop Desktop Server MS SQL MS Ultimate Free Pro Exchange File-level + + + + + + Backup Image - - + + + + CloudBerry Backup Installation and Configuration Guide Based Backup MS SQL - - - + - + Server Backup MS - - - - + + Exchange Server Backup Encryption - - + + + + and Compressio n Storage 200GB 1TB 1TB 1TB 1TB Unlimited Limits (for one account) Network 1 1 5 5 5 Unlimited Shares for Backup Support Superuser.c Email, 48 Email, 48 Email, 48 Email, 48 Email, 48 Type om forum hours hours hours hours hours Only response response response response response On the download page, there are also links for Mac and Linux Editions. For Windows, CBB is distributed within Universal Installer so that you can choose the desired edition after the download. -

File Management – Saving Your Documents
File Management – Saving Your Documents You will save everything to your H: drive. This is your personal drive that is out on the server and only you have access to it. It is not accessible by others. Your H: drive is accessible from any CCPS computer or from home via Remote Access. Accessing Your H: Drive To access your H: drive via the desktop: 1. Double-click the “This PC” icon. 2. Under Network Locations, double-click the drive that begins with your username and ends with the letter “H”. To access your H: drive via File Explorer: 1. Click the yellow folder at the bottom left corner of the screen. 2. Under Network Locations, double-click the drive that begins with your username and ends with the letter “H”. Accessing Shared Drives If shared drives have been added to your profile, they will be located under Network Locations. If you need access to a departmental or school shared drive, please submit a work order so it can be added to your profile or email [email protected]. Creating Shortcuts on the Desktop Do not save documents/items directly to the desktop. If you would like to place documents on the desktop for quick- access, save your master documents to your H: drive and place a shortcut to the document on the desktop. To create a shortcut on the desktop to a program or file do the following: 1. Right-click an open area on the desktop, Select New, and then click Shortcut. 2. Click Browse. 3. Locate the program or file to which you want to create a shortcut, click the program or file, click Open, and then click Next. -

Extending File Systems Using Stackable Templates
THE ADVANCED COMPUTING SYSTEMS ASSOCIATION The following paper was originally published in the Proceedings of the USENIX Annual Technical Conference Monterey, California, USA, June 6-11, 1999 Extending File Systems Using Stackable Templates _ Erez Zadok, Ion Badulescu, and Alex Shender Columbia University © 1999 by The USENIX Association All Rights Reserved Rights to individual papers remain with the author or the author's employer. Permission is granted for noncommercial reproduction of the work for educational or research purposes. This copyright notice must be included in the reproduced paper. USENIX acknowledges all trademarks herein. For more information about the USENIX Association: Phone: 1 510 528 8649 FAX: 1 510 548 5738 Email: [email protected] WWW: http://www.usenix.org Extending File Systems Using Stackable Templates Erez Zadok, Ion Badulescu, and Alex Shender Computer Science Department, Columbia University ezk,ion,alex @cs.columbia.edu { } Abstract Kernel-resident native file systems are those that inter- Extending file system functionality is not a new idea, act directly with lower level media such as disks[9] and but a desirable one nonetheless[6, 14, 18]. In the several networks[11, 16]. Writing such file systems is difficult years since stackable file systems were first proposed, only because it requires deep understanding of specific operat- a handful are in use[12, 19]. Impediments to writing new ing system internals, especially the interaction with device file systems include the complexity of operating systems, drivers and the virtual memory system. Once such a file the difficulty of writing kernel-based code, the lack of a system is written, porting it to another operating system true stackable vnode interface[14], and the challenges of is just as difficult as the initial implementation, because porting one file system to another operating system. -
Hexadecimal Numbers
AP Computer Science Principles How Computers Work: Computer Architecture and Data Storage What You Will Learn . How to disassemble and rebuild a computer . How to choose the parts to build a new computer . Logic Gates . Data storage: . Binary . Hexadecimal . ASCII . Data compression . Computer Forensics . Limits of computing 2 2 Introduction to Computer Hardware 33 The Parts of a Computer 4 Image: By Gustavb. Source Wikimedia. License: CC BY-SA 3.0 4 Main parts of a computer . Case . Power supply . Motherboard . CPU . RAM . Adapter Cards . Internal and External Drives . Internal and External Cables 5 55 The Motherboard . The motherboard provides the electrical connections between the computer components. Comes in different sizes called “form factors.” . All the other components of the computer connect to the motherboard directly or through a cable. Image: By skeeze. Source Pixabay. License: CC BY-SA 3.0 6 66 A Case Needs to Name size (mm) be a Form BTX 325 × 266 ATX 305 × 244 Factor as Larger EATX 305 × 330 or Larger than (Extended) LPX 330 × 229 the microBTX 264 × 267 Motherboard. microATX 244 × 244 Mini-ITX 170 × 170 7 7 Image: By Magnus Manske. Source Wikimedia. License: CC BY-7SA 3.0 The Power Supply . Power Supplies come in different form factors and should match the form factor of the case. Power supplies are rated in watts and should have a rating larger than the total required watts of all the computer components. 8 8 Image: By Danrock Source: Wikimedia License: CC BY-SA 3.0 8 The Power Supply Connectors . The Power Supply will have lots of extra connectors so you can add additional components to your computer at a later time.