Distributed Differentially Private Mutual Information Ranking and Its Applications
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Microsoft Ignite 2018 September 24–28 // Orlando, FL Contents | 2 Contents
Microsoft Ignite 2018 September 24–28 // Orlando, FL contents | 2 contents Foreword by Frank X. Shaw 5 Chapter 1 Security 6 1.1 Microsoft Threat Protection 1.2 Password-free sign-in for thousands of apps 1.3 Microsoft Secure Score 1.4 Azure confidential computing public preview 1.5 Modern Compliance enhancements 1.6 Expansion of work to bring the entire tech sector together through the Cybersecurity Tech Accord Chapter 2 Artificial intelligence and data 8 2.1 Artificial intelligence 2.1.1 AI for Humanitarian Action 2.1.2 Cortana Skills Kit for Enterprise 2.1.3 New Azure Machine Learning capabilities 2.1.4 Azure Cognitive Services update – Speech Service general availability 2.1.5 Microsoft Bot Framework v4 general availability 2.1.6 Unified search across Microsoft 365 2.1.7 New AI-powered meeting features in Microsoft 365 2.1.8 Ideas in Office 2.1.9 Intelligent enhancements in Excel 2.2 Data 2.2.1 SQL Server 2019 public preview 2.2.2 Azure SQL Database Hyperscale and Managed Instance 2.2.3 Azure Data Explorer public preview 2.2.4 Azure Cosmos DB Multi-master general availability 2.2.5 Azure Databricks Delta preview 2.2.6 Azure SQL Database intelligent features 2.2.7 New Azure SQL Data Warehouse pricing tier contents | 3 Chapter 3 Internet of things and edge computing 12 3.1 Internet of things 3.1.1 Azure Digital Twins 3.1.2 Azure IoT Central general availability 3.1.3 Azure Maps: Map Control update 3.1.4 New Azure IoT Edge features and capabilities 3.1.5 Azure IoT Hub Device Provisioning Service updates 3.1.6 Azure IoT Hub message routing -
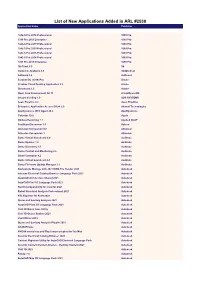
List of New Applications Added in ARL #2538 Application Name Publisher
List of New Applications Added in ARL #2538 Application Name Publisher 1042-S Pro 2018 Professional 1099 Pro 1099 Pro 2019 Enterprise 1099 Pro 1042-S Pro 2017 Professional 1099 Pro 1042-S Pro 2019 Professional 1099 Pro 1042-S Pro 2015 Professional 1099 Pro 1042-S Pro 2014 Professional 1099 Pro 1099 Pro 2015 Enterprise 1099 Pro 1E Client 5.0 1E Complete Anatomy 4.0 3D4Medical AdGuard 2.4 AdGuard Acrobat DC (2019) Pro Adobe Creative Cloud Desktop Application 5.2 Adobe Dimension 3.3 Adobe Open Java Development Kit 11 AdoptOpenJDK Integra Vending 1.0 ADS SYSTEMS Aeon Timeline 2.3 Aeon Timeline Enterprise Application Access Client 2.0 Akamai Technologies AppDynamics .NET Agent 20.4 AppDynamics Calendar 10.0 Apple Dodeca Reporting 7.1 Applied OLAP FastStats Discoverer 1.0 Apteco Atlassian Companion 0.6 Atlassian Atlassian Companion 1 Atlassian Dante Virtual Soundcard 4.0 Audinate Dante Updater 1.0 Audinate Dante Discovery 1.3 Audinate Dante Control and Monitoring 4.0 Audinate Dante Controller 4.2 Audinate Dante Virtual Soundcard 4.1 Audinate Dante Firmware Update Manager 3.1 Audinate Navisworks Manage with 2021 DWG File Reader 2021 Autodesk Inventor Electrical Catalog Browser Language Pack 2021 Autodesk AutoCAD Architecture Shared 2021 Autodesk AutoCAD Civil 3D Language Pack 2021 Autodesk Revit Interoperability for Inventor 2021 Autodesk Robot Structural Analysis Professional 2021 Autodesk STL Exporter for Revit 2020 Autodesk Storm and Sanitary Analysis 2021 Autodesk AutoCAD Plant 3D Language Pack 2021 Autodesk Civil 3D Batch Save Utility Autodesk -

AZ-900 Reading Guide - Sept 2020 Document V1.0, Researched by Scott Duffy
AZ-900 Reading Guide - Sept 2020 Document v1.0, researched by Scott Duffy Don’t forget that you can watch videos on each of these topics in my very reasonably priced AZ-900: Microsoft Azure Fundamentals Exam Prep course on Udemy: https://www.udemy.com/course/az900-azure/?referralCode=CBB97C39131AE1062B29 Describe Cloud Concepts (20-25%) Identify the benefits and considerations of using cloud services ● identify the benefits of cloud computing, such as High Availability, Scalability, Elasticity, Agility, and Disaster Recovery ○ https://docs.microsoft.com/en-us/azure/architecture/framework/resiliency/over view ○ https://docs.microsoft.com/en-us/azure/architecture/guide/design-principles/re dundancy ○ https://docs.microsoft.com/en-us/azure/architecture/guide/design-principles/sc ale-out ○ https://docs.microsoft.com/en-us/azure/architecture/best-practices/auto-scalin g ○ https://docs.microsoft.com/en-us/azure/cloud-adoption-framework/strategy/bu siness-outcomes/agility-outcomes ○ https://docs.microsoft.com/en-us/azure/architecture/framework/resiliency/mon itoring ○ https://docs.microsoft.com/en-us/azure/architecture/resiliency/recovery-loss-a zure-region ● identify the differences between Capital Expenditure (CapEx) and Operational Expenditure (OpEx) ○ https://docs.microsoft.com/en-us/azure/cloud-adoption-framework/strategy/bu siness-outcomes/fiscal-outcomes#capital-expenses-and-operating-expenses ● describe the consumption-based model ○ https://docs.microsoft.com/en-us/azure/architecture/framework/cost/design-pri ce Describe the differences -
The Developer's Guide to Azure
E-book Series The Developer’s Guide to Azure Published May 2019 May The Developer’s 2 2019 Guide to Azure 03 / 40 / 82 / Introduction Chapter 3: Securing Chapter 6: Where your application and how to deploy We’re here to help your Azure services How can Azure help secure 05 / your app? How can Azure deploy your Encryption services? Chapter 1: Getting Azure Security Center Infrastructure as Code started with Azure Logging and monitoring Azure Blueprints Containers in Azure What can Azure do for you? Azure Stack Where to host your 51 / Where to deploy, application and when? Chapter 4: Adding Azure App Service Features Azure Functions intelligence to Azure Logic Apps your application 89 / Azure Batch Containers How can Azure integrate AI Chapter 7: Share your What to use, and when? into your app? code, track work, and ship Making your application Azure Search software more performant Cognitive Services Azure Front Door Azure Bot Service How can Azure help you plan Azure Content Delivery Azure Machine Learning smarter, collaborate better, and ship Network Studio your apps faster? Azure Redis Cache Developer tooling for AI Azure Boards AI and mixed reality Azure Repos Using events and messages in Azure Pipelines 22 / your application Azure Test Plans Azure Artifacts Chapter 2: Connecting your app with data 72 / 98 / What can Azure do for Chapter 5: Connect your your data? business with IoT Chapter 8: Azure in Action Where to store your data Azure Cosmos DB How can Azure connect, secure, Walk-through: Azure portal Azure SQL Database manage, monitor, -

Azure Sphere Mcus for Hardware-Based Security Design Security Monitor
Platform Security Summit Azure Sphere: A Secure IoT Platform Jewell Seay Principal Software Engineering Lead Microsoft © 2019/10/01Microsoft Corporation SECURITY IS FOUNDATIONAL It must be built in from the beginning. © Microsoft Corporation Mirai Botnet attack Everyday devices are used to launch an attack that takes down the internet for a day https://www.cloudflare.com/learning/ddos/glossary/mirai-botnet/ © Microsoft Corporation Hackers attack casino Attackers gain access to casino database through fish tank https://www.washingtonpost.com/news/innovations/wp/2017/07/21/how-a-fish-tank- helped-hack-a-casino/ © Microsoft Corporation OS Bug exposes 200M Devices RTOS TCP Flaw https://www.wired.com/story/vxworks-vulnerabilities-urgent11/ © Microsoft Corporation The 7 properties of highly secured devices https://aka.ms/7properties Hardware Root of Trust Unforgeable cryptographic keys generated and protected by hardware. Physical countermeasures resist side-channel attacks. Small Trusted Private keys stored in a hardware-protected vault, inaccessible to software. Division of software into Computing Base self-protecting layers. Multiple mitigations applied against each threat. Countermeasures mitigate the consequences of a Defense in Depth successful attack on any one vector. Hardware-enforced barriers between software components prevent a breach in one from propagating Dynamic Compartments to others. Certificate-Based Signed certificate, proven by unforgeable cryptographic key, proves the device identity and authenticity. Authentication Renewal brings the device forward to a secure state and revokes compromised assets for known Error Reporting vulnerabilities or security breaches. A software failure, such as a buffer overrun induced by an attacker probing security, is reported to Renewable Security cloud-based failure analysis system. -

Azure Sphere
IoT løsninger Cloud tjenester & Analyseværktøjer Ole Kjeldsen CTO & CISO Microsoft Danmark & Island Denne pptx: https://aka.ms/msiot2018 AGENDA Overblik … Trusler & mulige løsninger Sphere, Hub, Edge & cloud services …. meget mere i appendix & via bl.a. online træning hvis man vil nørde ☺ What is …. 9 billion IoT devices deployed per year © Microsoft Corporation Microcontrollers (MCUs) Wave 1: Wave 2: The Microcontroller (MCU) Internet Connectivity © Microsoft Corporation 1970’s 1980’s 1990’s 2000’s 2010’s 2020’s 2030’s 9 BILLION new MCU devices deployed every year IN TOYS... IN APPLIANCES… IN EQUIPMENT… FEWER THAN 1% ARE CONNECTED TODAY. North Carolina Highway Signs Compromised By a First/Largest known DDoS attack using insecure IoT Foreign Hacker* devices (2016) disrupted WW internet traffic ** *NSTAC Report to the President on the Internet of Things. www.dhs.gov/sites/default/files/publications/ ** https://www.wired.com/2016/12/botnet-broke-internet-isnt-going-away/ What is …. 5 billion USD Microsoft investment in IoT © Microsoft Corporation The internet security battle. We’ve been fighting it for decades. We have experience to share. © Microsoft Corporation Azure Sphere Announced at RSA Azure Sphere is an end-to-end solution for securing MCU powered devices A new Azure Sphere OS secured by Microsoft for the devices 10-year lifetime to create a trustworthy platform for new IoT experiences A new Azure Sphere class of MCUs, from silicon partners, with built-in Microsoft security technology provide connectivity and a dependable hardware root of trust. The Azure Sphere Security Service guards every Azure Sphere device; it brokers trust for device-to-device and device-to-cloud communication, detects emerging threats, and renews device security. -

Microsoft Ignite 2018 September 24–28 // Orlando, FL Contents | 2 Contents
Microsoft Ignite 2018 September 24–28 // Orlando, FL contents | 2 contents Foreword by Frank X. Shaw 5 Chapter 1 Security 6 1.1 Microsoft Threat Protection 1.2 Password-free sign-in for thousands of apps 1.3 Microsoft Secure Score 1.4 Azure confidential computing public preview 1.5 Modern Compliance enhancements 1.6 Expansion of work to bring the entire tech sector together through the Cybersecurity Tech Accord Chapter 2 Artificial intelligence and data 8 2.1 Artificial intelligence 2.1.1 AI for Humanitarian Action 2.1.2 Cortana Skills Kit for Enterprise 2.1.3 New Azure Machine Learning capabilities 2.1.4 Azure Cognitive Services update – Speech Service general availability 2.1.5 Microsoft Bot Framework v4 general availability 2.1.6 Unified search across Microsoft 365 2.1.7 New AI-powered meeting features in Microsoft 365 2.1.8 Ideas in Office 2.1.9 Intelligent enhancements in Excel 2.2 Data 2.2.1 SQL Server 2019 public preview 2.2.2 Azure SQL Database Hyperscale and Managed Instance 2.2.3 Azure Data Explorer public preview 2.2.4 Azure Cosmos DB Multi-master general availability 2.2.5 Azure Databricks Delta preview 2.2.6 Azure SQL Database intelligent features 2.2.7 New Azure SQL Data Warehouse pricing tier contents | 3 Chapter 3 Internet of things and edge computing 12 3.1 Internet of things 3.1.1 Azure Digital Twins 3.1.2 Azure IoT Central general availability 3.1.3 Azure Maps: Map Control update 3.1.4 New Azure IoT Edge features and capabilities 3.1.5 Azure IoT Hub Device Provisioning Service updates 3.1.6 Azure IoT Hub message routing -
Exam Ref AZ-900 Microsoft Azure Fundamentals
Exam Ref AZ-900 Microsoft Azure Fundamentals Jim Cheshire Exam Ref AZ-900 Microsoft Azure Fundamentals Published with the authorization of Microsoft Corporation by: CREDITS Pearson Education, Inc. Hoboken, NJ EDITOR-IN-CHIEF Brett Bartow Copyright © 2021 by Pearson Education, Inc. EXECUTIVE EDITOR All rights reserved. This publication is protected by copyright, and permission Loretta Yates must be obtained from the publisher prior to any prohibited reproduction, ASSISTANT SPONSORING storage in a retrieval system, or transmission in any form or by any means, EDITOR electronic, mechanical, photocopying, recording, or likewise. For information Charvi Arora regarding permissions, request forms, and the appropriate contacts within the Pearson Education Global Rights & Permissions Department, please visit www. DEVELOPMENT EDITOR pearson.com/permissions. No patent liability is assumed with respect to the use Rick Kughen of the information contained herein. Although every precaution has been taken MANAGING EDITOR in the preparation of this book, the publisher and author assume no responsi- Sandra Schroeder bility for errors or omissions. Nor is any liability assumed for damages resulting from the use of the information contained herein. SENIOR EDITOR Tracey Croom ISBN-13: 978-0-13-687718-9 COPY EDITOR ISBN-10: 0-13-687718-4 Rick Kughen Library of Congress Control Number: 2020940854 INDEXER Cheryl Ann Lenser ScoutAutomatedPrintCode PROOFREADER TRADEMARKS Abigail Manheim Microsoft and the trademarks listed at http://www.microsoft.com on the TECHNICAL EDITOR “Trademarks” webpage are trademarks of the Microsoft group of companies. Tim Warner All other marks are property of their respective owners. EDITORIAL ASSISTANT WARNING AND DISCLAIMER Cindy Teeters Every effort has been made to make this book as complete and as accurate as INTERIOR COMPOSITOR possible, but no warranty or fitness is implied. -

A Cloud Services Cheat Sheet for AWS, Azure, and Google Cloud
Cloud/DevOps Handbook EDITOR'S NOTE AI AND MACHINE LEARNING ANALYTICS APPLICATION INTEGRATION BUSINESS APPLICATIONS COMPUTE CONTAINERS COST CONTROLS DATABASES DEVELOPER TOOLS IoT MANAGEMENT AND GOVERNANCE MIGRATION MISCELLANEOUS A cloud services cheat sheet for AWS, NETWORKING Azure, and Google Cloud SECURITY STORAGE DECEMBER 2020 EDITOR'S NOTE HOME EDITOR'S NOTE cloud directories—a quick reference sheet for what each AI AND MACHINE A cloud services LEARNING vendor calls the same service. However, you can also use this as a starting point. You'll ANALYTICS cheat sheet for need to do your homework to get a more nuanced under- APPLICATION AWS, Azure and standing of what distinguishes the offerings from one an- INTEGRATION other. Follow some of the links throughout this piece and take that next step in dissecting these offerings. BUSINESS Google Cloud APPLICATIONS That's because not all services are equal—each has its —TREVOR JONES, SITE EDITOR own set of features and capabilities, and the functionality COMPUTE might vary widely across platforms. And just because a CONTAINERS provider doesn't have a designated service in one of these categories, that doesn't mean it's impossible to achieve the COST CONTROLS same objective. For example, Google Cloud doesn't offer an DATABASES AWS, MICROSOFT AND GOOGLE each offer well over 100 cloud explicit disaster recovery service, but it's certainly capable services. It's hard enough keeping tabs on what one cloud of supporting DR. DEVELOPER TOOLS offers, so good luck trying to get a handle on the products Here is our cloud services cheat sheet of the services IoT from the three major providers. -
Microsoft Azure Update
to fail Digital Feedback Loop Products Businesses & Assets Better Data Digital Feedback Loop Products Businesses & Assets Better Data Things Insights Actions Data storage Deployment Enterprise integration Cloud-to-device Business process integration commands Cold path analytics Device recovery Solution scale Operations monitoring Cost management Internationalization High availability Updating devices Provisioning devices Device lifecycle Transport protocols Warm path analytics Drivers Things Disaster recovery Insights Hot path analytics Actions Device updates Data ownership < ---- End-to-End Security ---- > On device analytics Data visualization Industry and government compliance HW certification Manufacturing scale Device commercialization Securing data … and why IoT needs simplifying MICROSOFT WILL INVEST $5 BILLION IN IoT Our goal is to give every customer the ability to transform their businesses, and the world at large, with connected solutions. https://blogs.microsoft.com/iot/2018/04/04/microsoft-will-invest-5-billion-in-iot-heres-why IoT Solutions (SaaS) Azure IoT Central Microsoft Connected Field Service IoT SaaS Field Service SaaS IoT Solution Accelerators (PaaS) Azure IoT solution accelerators Remote Monitoring Predictive Maintenance Connected factory Platform Services & Device Support Azure HD Insight Azure Stream Microsoft Power Azure IoT Edge Azure IoT Hub Spark, Storm, Microsoft Flow Azure Sphere Analytics BI Kafka Azure IoT Hub Azure Time Series Windows 10 IoT Device Provisioning Azure Event Hubs Azure Logic Apps Azure Maps -
With Connected Devices Leveraging Internet of Things
with connected devices leveraging Internet of Things Frank Callewaert - Global Technology Strategist This Photo by Unknown Author is licensed under CC BY-ND Microsoft IoT Viewpoint 2 …IoT enables an eCustoms and eTrade business revolution, enabled by technology Waves of Innovation Cloud Globally available, unlimited compute resources IoT Harnessing signals from sensors and devices, managed centrally by the cloud Edge Intelligence offloaded from the cloud to IoT devices AI Breakthrough intelligence capabilities, in the cloud and at the edge Internet of Things is everywhere Augmented reality Smart grids Multilayer QR - RFID Agriculture Buildings Airplanes Livestock Auto Construction Surveillance Workspaces Charging Location Buses Sports stations Trains Worker Safety Racing Elevators Security Pets Vending Medical devices Subways Factories Shopping Power Plants Equipment Engines Vaccine Manufacturing Traffic Systems dispensers Postboxes Communications Weather Systems Shipping wearables Smart meters Trucks Smart Seals Freight Drones Public Safety Internet of Things is big 80 billion connected “things” by 2025 - IDC 70% 180 zettabytes digital data by 2025 - IDC value enabled by IoT from B2B scenarios - McKinsey and Company $457 billion global IoT market by 2020 - Gartner A Simple View of an IoT Solution Things Data & Insights Actions A More Realistic View… Data storage Deployment Enterprise integration Cloud-to-device Business process integration commands Cold path analytics Device recovery Solution scale Operations monitoring Cost management -

AI + Machine Learning Analytics
Be Azure Ready – powered by First Distribution AI + Machine Learning Covering: Azure Batch AI, Azure Bot Service, Microsoft Genomics, Machine Learning services, Machine Learning Studio, Cognitive Services, Bing APIs, Computer Vision API, Content moderator, Custom Services, Emotion API, Face API, Language Understanding (LUIS), Linguistic Analysis API, QnA Maker API, Speaker Recognition API, Text Analytics API, Translator Speech API, Translator Text API, Web Language Model API Machine Learning and Azure Sphere Gurdeep Pall: Building the future of autonomy ML at the edge and in the Cloud with Azure Sphere | Internet of Things Show How to build a voice-enabled grocery chatbot with Azure AI How to build an intelligent travel journal using Azure AI How to build a personal finance app using Azure Azure Cognitive Services Translator - Inuktitut language text translation now available Get skilled on AI and ML ? on your terms with Azure AI Unified Neural Text Analyzer: an innovation to improve Neural TTS pronunciation accuracy General availability: Azure Machine Learning Output Datasets Public preview: Azure Machine Learning Data Labeling ? Image Instance Segmentation General availability: Text Analytics' Named Entity Recognition v3 now supports 10 languages with improved AI quality Analytics Covering: Azure Databricks, HDInsight, Data Factory, Stream Analytics, Data Lake Analytics, Event Hubs, Power BI, Azure Analysis Services, Apache Spark for HDInsight, Apache Storm for HDInsight, R Server for HDInsight, Data Catalog, Data Explorer Azure Data