Microsoft Revs Security Service
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Anyconnect および Host Scan のアンチウイルス/アンチスパイウェア
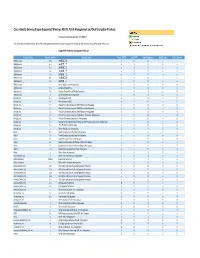
AnyConnect および Host Scan のアンチウイルス/アンチスパイウェア/ファイアウォール サポート表 AnyConnect ポスチャ モジュールにより、AnyConnect Secure Mobility クライアントはホストにインス トールされているオペレーティング システム、およびアンチウイルス、アンチスパイウェア、ファイアウォールの 各ソフトウェアを識別できます。 Host Scan アプリケーションはポスチャ モジュールのコンポーネントに含まれ る、こうした情報を収集するアプリケーションです。 AnyConnect 3.0 より、Host Scan パッケージは AnyConnect Secure Mobility クライアントおよび Cisco Secure Desktop(CSD)の共有コンポーネントになっています。 それ以前は、Host Scan パッケージは CSD を インストールすることによってのみ利用可能になるコンポーネントの 1 つでした。 Host Scan パッケージを CSD から分離したのは、CSD の一部として提供されていたときよりも、ユー ザが頻繁に Host Scan サポート表を更新できるようにするためです。 このサポート表には、ユーザが動的なア クセス ポリシーで使用しているアンチウイルス/アンチスパイウェア/ファイアウォール アプリケーションの製品 名とバージョン情報が記載されています。 シスコでは、Host Scan パッケージに Host Scan アプリケーション、 Host Scan サポート表、および他のコンポーネントを含めて提供しています。 Host Scan サポート表のリスト アンチウイルス アプリケーション総合リスト アンチスパイウェア アプリケーション総合リスト ファイアウォール アプリケーション総合リスト Windows 用アンチウイルス Windows 用アンチスパイウェア Windows 用ファイアウォール Linux 用アンチウイルス Linux 用ファイアウォール Mac OS 用アンチウイルス Mac OS 用アンチスパイウェア Mac OS 用ファイアウォール A B C D E F G H I J K L M N O P Q R S T U V W X Y Z AA AB AC AD AE ファイル データ ファ バージョ データ ファイ データ ファイル データ ファイ エンジンのバー RTP の RTP の 前回のスキャン スキャン/クリー システムのフル アンイン GUI のアク トレイ アイコンの トレイ アイコン 有効期 脅威ログの取 スキャン プログラ フル スキャンの進捗 インストール ディ 一括スキャ メモリ スキャ アンチウイルス製品名 ライブ更新 サービス GUI の表示 のスキャ 有効日の取得 更新の進捗表示 プログラム言語の取得 イル dir の取 市場での別名 ン ルの時刻 のバージョン ルの署名 ジョン チェック 設定 時刻 ニング スキャン ストール ティブ化 表示 の非表示 限 得 ムの実行 表示 レクトリの取得 ン ン 1 ン 得 2 3 360Safe.com 4 360 Antivirus 1.x 9989999898888898 8888 8 9 8 9 9 9 88 5 360杀毒 1.x 9999988898888898 8889 8 8 8 9 9 9 88 6 AEC, spol. s r.o. 7 TrustPort Antivirus 2.x 8888998899888999 9888 8 9 8 9 8 988 8 Agnitum Ltd. -

Computer Security Administration
Information Security Group Information + Technology Services University of Toronto Endpoint Security Policy System A Network Access Control System with Vulnerability Detection and User Remediation Evgueni Martynov UNIX Systems Group Mike Wiseman Computer Security Administration Endpoint Security Policy System Table of Contents Acknowledgements............................................................................. 3 Change History .................................................................................... 4 Summary ............................................................................................. 5 Overview .............................................................................................. 5 Network Isolation ............................................................................... 6 Vulnerability Detection ....................................................................... 6 User Remediation ................................................................................ 8 Administering ESP ............................................................................... 8 ESP Operations Experience ................................................................ 9 Appendix I – Installation and Configuration of ESP server ........... 10 Using init.sh ..................................................................................... 10 Post-Installation ................................................................................ 11 Configuring an ESP Server to Work with an ESP Agent ....................... -

Acer Lanscope Agent 2.2.25.84 Acer Lanscope Agent 2.2.25.84 X64
Acer LANScope Agent 2.2.25.84 Acer LANScope Agent 2.2.25.84 x64 Adaptive Security Analyzer 2.0 AEC TrustPort Antivirus 2.8.0.2237 AEC TrustPort Personal Firewall 4.0.0.1305 AhnLab SpyZero 2007 and SmartUpdate AhnLab V3 Internet Security 7.0 Platinum Enterprise AhnLab V3 Internet Security 7.0 Platinum Enterprise x64 ArcaVir Antivir/Internet Security 09.03.3201.9 Ashampoo AntiSpyware 2 v 2.05 Ashampoo AntiVirus AtGuard 3.2 Authentium Command Anti-Malware v 5.0.5 AVG Identity Protection 8.5 BitDefender Antivirus 2008 BitDefender Antivirus Plus 10.247 BitDefender Client Professional Plus 8.0.2 BitDefender Antivirus Plus 10 BitDefender Standard Edition 7.2 (Fr) Bit Defender Professional Edition 7.2 (Fr) BitDefender 8 Professional Plus BitDefender 8 Professional (Fr) BitDefender 8 Standard BitDefender 8 Standard (Fr) BitDefender 9 Professional Plus BitDefender 9 Standard BitDefender for FileServers 2.1.11 BitDefender Free Edition 2009 12.0.12.0 BitDefender Antivirus 2009 12.0.10 BitDefender 2009 12.0.11.5 BitDefender Internet Security 2008 BitDefender Internet Security 2009 12.0.8 BitDefender 2009 Internet Security 12.0.11.5 BitDefender Internet Security v10.108 BitDefender Total Security 2008 BitDefender 2009 Total Security 12.0.11.5 CA AntiVirus 2008 CA Anti-Virus r8.1 / CA eTrustITM Agent r8.1 CA eTrustITM 8.1 CA eTrustITM 8.1.00 CA eTrustITM Agent 8.0.403 CA eTrust Pestpatrol 5.0 CA HIPS Managed Client 1.0 CA eTrust Antivirus 7.1.0194 CA PC Security Suite 6.0 \ Private PC Security Suite 6.0 CA PC Security Suite 6.0.00 Cipafilter Client Tools -
Cisco Identity Services Engine Supported Windows AV/AS/PM/DE
Cisco Identity Services Engine Supported Windows AS/AV, Patch Management and Disk Encryption Products Compliance Module Version 3.6.10363.2 This document provides Windows AS/AV, Patch Management and Disk Encryption support information on the the Cisco AnyConnect Agent Version 4.2. Supported Windows Antispyware Products Vendor_Name Product_Version Product_Name Check_FSRTP Set_FSRTP VirDef_Signature VirDef_Time VirDef_Version 360Safe.com 10.x 360安全卫士 vX X v v 360Safe.com 4.x 360安全卫士 vX X v v 360Safe.com 5.x 360安全卫士 vX X v v 360Safe.com 6.x 360安全卫士 vX X v v 360Safe.com 7.x 360安全卫士 vX X v v 360Safe.com 8.x 360安全卫士 vX X v v 360Safe.com 9.x 360安全卫士 vX X v v 360Safe.com x Other 360Safe.com Antispyware Z X X Z X Agnitum Ltd. 7.x Outpost Firewall Pro vX X X O Agnitum Ltd. 6.x Outpost Firewall Pro 2008 [AntiSpyware] v X X v O Agnitum Ltd. x Other Agnitum Ltd. Antispyware Z X X Z X AhnLab, Inc. 2.x AhnLab SpyZero 2.0 vv O v O AhnLab, Inc. 3.x AhnLab SpyZero 2007 X X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2007 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2008 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2009 Platinum AntiSpyware v v O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 7.0 Platinum Enterprise AntiSpyware v X O v O AhnLab, Inc. 8.x AhnLab V3 Internet Security 8.0 AntiSpyware v v O v O AhnLab, Inc. -
Gateway to Visteon G2V Supported Anti-Virus Guide
. Siemens Enterprise Communications, Inc. ........Gateway to Visteon G2V Supported Anti-Virus Guide Version: 1.6.5 – November 2010 Siemens and Visteon Confidential and Proprietary This document may not be duplicated or distributed without prior authorization from Siemens Enterprise Communications, Inc. or Visteon . Supported Anti-Virus Software The following Anti-Virus applications are fully supported. It is highly recommended that one of the following applications be used for accessing G2V. Please note that this list will change as new versions are released by their vendors. Normally, the current and previous release of these applications will remain on the supported list. Newer versions released may not be immediately supported or compatible, please consult this list before updating to a newer version. Vendor Product Version Windows XP Windows Vista Windows 7 McAfee, Inc. VirusScan Enterprise 8.7.x ✔ ✔ ✔ VirusScan 2009 13.x ✔ ✔ ‐‐ VirusScan 2010 14.x ✔ ✔ ✔ Symantec Corp. Norton Anti-Virus 2010 17.x ✔ ✔ ‐‐ Norton Anti-Virus 2011 18.x ✔ ✔ ✔ Symantec Endpoint Protection 11.x ✔ ✔ ✔ Symantec Endpoint Protection 12.x ✔ ✔ ✔ Trend Micro, Inc. Anti‐Virus 17.x ✔ ✔ ‐‐ Anti‐Virus 17.5 ✔ ✔ ✔ OfficeScan 8.x ✔ ✔ ‐‐ OfficeScan 10.x ✔ ✔ ✔ Notes: Please see the notes at the end of this guide for special instructions for Vista users with Norton Anti-Virus 2009. The products highlighted in yellow will be removed from the supported list in the next update. If you are using one of these products, you should consider upgrading to a newer version. Compatible Anti-Virus Software The applications below have been specified as compatible by the Anti-Virus Host Check vendor. Support for these applications may be removed at any time, especially in the case of older versions that may be at or near end-of-life status. -
Microsoft Forefront Client Security FAQ
Microsoft Forefront Client Security FAQ Q. What is Microsoft Forefront? A. The Microsoft Forefront comprehensive family of business security products provides greater protection and control over the security of your network infrastructure. Microsoft Forefront security products easily integrate with each other and with your organization’s IT infrastructure; they can be supplemented through interoperable third-party solutions, enabling end-to-end, defense-in-depth security solutions. Microsoft Forefront includes: Microsoft Internet Security and Acceleration Server (ISA) 2006. Intelligent Application Gateway (IAG). Forefront Security for Exchange Server. Forefront Security for SharePoint. Forefront Security for Office Communications Server. Forefront Client Security. Simplified management, analysis, and deployment enable you to efficiently protect your organization’s information resources, and help secure access to applications and servers. With highly responsive protection supported by Microsoft technical guidance, Microsoft Forefront helps you confidently meet ever-changing threats and increased business demands. For more information, please visit the Microsoft Forefront Web site. Q. What is Microsoft Forefront Client Security? A. Microsoft Forefront Client Security provides unified malware protection for business desktops, laptops, and server operating systems that is easier to manage and control. Built on the same highly successful Microsoft protection technology already used by millions of people worldwide, Forefront Client Security helps guard against emerging threats, such as spyware and rootkits, as well as traditional threats, such as viruses, worms, and Trojan horses. Forefront Client Security integrates with your existing infrastructure software, such as Active Directory, and complements other Microsoft security technologies for enhanced protection and greater control. Q. What value does Microsoft Forefront Client Security deliver to customers? A. -

Tools-Tools Firewall
Computer Security Virus Komputer & Firewall Definisi Virus A virus is a program that reproduces its own code by attaching it self to other executable file in such a way that the virus code is executed when the infected executable file is executed. Suatu program komputer yang dapat menyebar pada komputer atau jaringan dengan cara membuat copy dari dirinya sendiri tanpa sepengetahuan dari pengguna komputer tersebut. VIRUS CRITERIA Having an ability to get an information Ex: Macro virus searching all files with doc extension Having an ability to check a file Ex: Macro virus check a *.doc file whether it is already infected or not Having an ability to reproduces itself and infect other – Reproducing by infect other files Having an ability to manipulate – Routine from virus will be executed to do manipulation such as displaying a picture changing file or message/picture, directory name etc Having an ability to hide itself – Virus program is stored in boot record or track or in the form of machine code that cannot easily recognized by other VIRUS CYCLES LIFE Dormant Phase (sleeping phase) Virus is inactive until activated by one condition such as date, executed by other program Propagation Phase (distributing phase) Virus start to clonning itself by copied itself to other files or to a place in storage media Triggering Phase (active phase) Virus become active Execution Phase (acting phase) Start manipulating such as displaying message etc Kategori Virus : - Boot Virus: Jika komputer dinyalakan, sebuah inisial program di boot sector akan dijalankan. Virus yang berada di boot sector disebut boot virus. - File Virus: File virus adalah virus yang menginfeksi executable program. -

Cisco Identity Services Engine Release 1.2 Supported Windows
Cisco Identity Services Engine Supported Windows AV/AS Products Compliance Module Version 3.5.6317.2 This document provides Windows 8/7/Vista/XP AV/AS support information on the Cisco NAC Agent version 4.9.0.x and later. For other support information and complete release updates, refer to the Release Notes for Cisco Identity Services Engine corresponding to your Cisco Identity Services Engine release version. Supported Windows AV/AS Product Summary Added New AV Definition Support: COMODO Antivirus 5.x COMODO Internet Security 3.5.x COMODO Internet Security 3.x COMODO Internet Security 4.x Kingsoft Internet Security 2013.x Added New AV Products Support: V3 Click 1.x avast! Internet Security 8.x avast! Premier 8.x avast! Pro Antivirus 8.x Gen-X Total Security 1.x K7UltimateSecurity 13.x Kaspersky Endpoint Security 10.x Kaspersky PURE 13.x Norman Security Suite 10.x Supported Windows AntiVirus Products Product Name Product Version Installation Virus Definition Live Update 360Safe.com 360 Antivirus 1.x 4.9.0.28 / 3.4.21.1 4.9.0.28 / 3.4.21.1 yes 360 Antivirus 3.x 4.9.0.29 / 3.5.5767.2 4.9.0.29 / 3.5.5767.2 - 360杀毒 1.x 4.9.0.28 / 3.4.21.1 4.9.0.28 / 3.4.21.1 - 360杀毒 2.x 4.9.0.29 / 3.4.25.1 4.9.0.29 / 3.4.25.1 - 360杀毒 3.x 4.9.0.29 / 3.5.2101.2 - Other 360Safe.com Antivirus x 4.9.0.29 / 3.5.2101.2 - AEC, spol. -

Viruses, Antivirus Software, Backup Software Computer Security Threats
Informatics Viruses, antivirus software, backup software Computer security threats different types targeting both servers and ordinary clients protection IS necessary Types of consequences difficult access, blocked services crashes of the operating system, programs, services loss of data, incl. deletion of programs and files theft of private data, incl. passwords, bank accounts and cards and potential loss of real money Types of threats denial of service site and server substitution unauthorized access to internal/private networks, programs, data traffic sniffing malicious software (malware) Denial of service (DoS) attacks could also be distributed denial of service (DDoS) attacks obstruct or stop completely the entire operating system, services (i.e. the web server), programs or network connections are usually performed remotely using the network and commonly consist of flooding primarily against servers but could also target ordinary client machines Site and server substitution site hacking / substitution and changing the content to some jokes, statements, etc. site imitation without that leads to users to believe it is the original site (phishing) so that they could enter confidential information DNS server attacks (DNS spoofing) that substitute real names with false (hackers') IP-addresses Unauthorized access to internal/private networks unauthorized access (usually over the Internet) to internal networks and resources (e.g. a company's network) can be used to obtain confidential information, to disrupt or stop the network personal data can -

Copyrighted Material
Contents Preface ...................................................................................................................................................xxvii Read This First .................................................................................................................................... 1 Don’t Believe the Hype .............................................................................................................................. 2 The Value of Vista ...................................................................................................................................... 3 Windows Vista in 15 Minutes ................................................................................................................... 3 The New Start Menu ............................................................................................................................. 4 Windows Aero........................................................................................................................................ 5 Flip 3D .................................................................................................................................................... 6 Programs Explorer Replaces Add/Remove Programs .........................................................................8 Putting Some Gadgets in Your Windows Sidebar .............................................................................. 8 Instant Search and the Search Pane ................................................................................................... -

Antivirus & Internet Security Products Performance Benchmarking
PassMark SOFTWARE Antivirus & Internet Security Performance Benchmarking Document: Antivirus & Internet Security Performance Benchmarking Authors: D.Wren, M. Fryer Company: PassMark Software Pty Ltd (www.passmark.com) Date: 10/Mar/08 Edition: 3 File: Antivirus-Performance-Testing-Ed3.docx PassMark Software Pty. Ltd. www.passmark.com ACN: 099 321 392 Benchmark Report Antivirus & Internet Security Performance TABLE OF CONTENTS TABLE OF CONTENTS ....................................................................................................................... 2 REVISION HISTORY ........................................................................................................................... 3 REFERENCES ....................................................................................................................................... 3 EXECUTIVE SUMMARY .................................................................................................................... 4 PRODUCTS TESTED ........................................................................................................................... 5 METRICS – CRITERIA MEASURED ................................................................................................ 6 BENCHMARK 1 - BOOT TIME .................................................................................................................. 6 BENCHMARK 2 - SCAN SPEED ................................................................................................................ 6 BENCHMARK 3 – -

Windows Live Dev Platform
The Windows Live Dev Platform Martin Parry Developer & Platform Group Microsoft Ltd [email protected] http://martinparry.com Agenda What is Windows Live? Authentication Maps Address Book Photos Windows Live Quick Apps Windows Live Desktop Apps What is Windows Live? Web Services Hotmail, Virtual Earth, LiveID, Spaces, etc., etc. Client Applications Messenger, Mail, Photo Gallery, etc. A platform of components Your app can consume any/all services Features that would be “hard” to build yourself Terms of Use Based on Unique Users Per Month Apps with fewer than 1 Million UUs per month... Pay nothing Averaged over a 3 month period Services exposed through controls... Pay nothing Services in beta... Pay nothing Apps with more than 1 Million UUs per month... You have a choice... Pay $0.25 per UU per year, or Enter into revenue-sharing ad-funding agreement with Microsoft There are some exceptions... Search: free up to 750,000 queries per month Virtual Earth: free up to 3,000,000 map tiles per month Our Demo Site Authentication Windows Live ID Service Ok, it’s Passport, but now it’s different... Federated Can integrate with Windows CardSpace 300 Million users have a Windows Live ID App still has a Users database, but freed from storing a secret-per-user (now 1 per app) Are all Live IDs [email protected] ? Managed vs. unmanaged members Windows Live ID Sign-in There’s a “control” – actually an iframe Register your application at MS website Tell us your hostname, a secret, and a return URL You get a unique ID; you embed it in your app Implement