ENTERPRISE AJAX Strategies for Building High Performance Web Applications
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

A Java Implementation of a Portable Desktop Manager Scott .J Griswold University of North Florida
UNF Digital Commons UNF Graduate Theses and Dissertations Student Scholarship 1998 A Java Implementation of a Portable Desktop Manager Scott .J Griswold University of North Florida Suggested Citation Griswold, Scott .,J "A Java Implementation of a Portable Desktop Manager" (1998). UNF Graduate Theses and Dissertations. 95. https://digitalcommons.unf.edu/etd/95 This Master's Thesis is brought to you for free and open access by the Student Scholarship at UNF Digital Commons. It has been accepted for inclusion in UNF Graduate Theses and Dissertations by an authorized administrator of UNF Digital Commons. For more information, please contact Digital Projects. © 1998 All Rights Reserved A JAVA IMPLEMENTATION OF A PORTABLE DESKTOP MANAGER by Scott J. Griswold A thesis submitted to the Department of Computer and Information Sciences in partial fulfillment of the requirements for the degree of Master of Science in Computer and Information Sciences UNIVERSITY OF NORTH FLORIDA DEPARTMENT OF COMPUTER AND INFORMATION SCIENCES April, 1998 The thesis "A Java Implementation of a Portable Desktop Manager" submitted by Scott J. Griswold in partial fulfillment of the requirements for the degree of Master of Science in Computer and Information Sciences has been ee Date APpr Signature Deleted Dr. Ralph Butler Thesis Advisor and Committee Chairperson Signature Deleted Dr. Yap S. Chua Signature Deleted Accepted for the Department of Computer and Information Sciences Signature Deleted i/2-{/1~ Dr. Charles N. Winton Chairperson of the Department Accepted for the College of Computing Sciences and E Signature Deleted Dr. Charles N. Winton Acting Dean of the College Accepted for the University: Signature Deleted Dr. -

Organizing Screens with Mission Control | 61
Organizing Screens with 7 Mission Control If you’re like a lot of Mac users, you like to do a lot of things at once. No matter how big your screen may be, it can still feel crowded as you open and arrange multiple windows on the desktop. The solution to the problem? Mission Control. The idea behind Mission Control is to show what you’re running all at once. It allows you to quickly swap programs. In addition, Mission Control lets you create multiple virtual desktops (called Spaces) that you can display one at a time. By storing one or more program windows in a single space, you can keep open windows organized without cluttering up a single screen. When you want to view another window, just switch to a different virtual desktop. Project goal: Learn to use Mission Control to create and manage virtual desktops (Spaces). My New Mac, Lion Edition © 2011 by Wallace Wang lion_book-4c.indb 59 9/9/2011 12:04:57 PM What You’ll Be Using To learn how to switch through multiple virtual desktops (Spaces) on your Macintosh using Mission Control, you’ll use the following: > Mission Control > The Safari web browser > The Finder program Starting Mission Control Initially, your Macintosh displays a single desktop, which is what you see when you start up your Macintosh. When you want to create additional virtual desktops, or Spaces, you’ll need to start Mission Control. There are three ways to start Mission Control: > Start Mission Control from the Applications folder or Dock. > Press F9. -

AFRC Desktop Anywhere Windows 10 Installation Guide Page | 1
Updated: 2/28/2020 AFRC Desktop Anywhere Windows 10 Installation Guide Page | 1 AFRC DESKTOP ANYWHERE WINDOWS 10 INSTALLATION GUIDE AFRC's Desktop-as-a-Service, aka Desktop Anywhere (DA), utilizes a user's personal computer (Mac/Windows), valid AF CAC, and additional applications (described below). Once launched on the computer, the DA session is a separate, containerized session completely isolated from the user's data, settings, hard drive, browser history or information of all kinds. There is no intermingling of anything between the secure, DA government session and the personal side of the computer, Essentially the DA session is a 'dumb' terminal that displays and accepts input---nothing is actually downloaded or uploaded to the user's computer. CONTENTS Quick Links ................................................................................................................................................................................................. 2 DoD Certificates......................................................................................................................................................................................... 3 Download InstallRoot ............................................................................................................................................................................. 3 Install InstallRoot .................................................................................................................................................................................. -

Citrix VDI—Opening and Closing
How To: Citrix VDI—Opening and Closing In order to provide better and more efficient administration of the GIS Citrix environment, a new means of access is being implemented. Once this new process is in place, the current means of GIS Citrix access will no longer be available. Users can access multiple programs via the new Citrix VDI (Virtual Desktop Infrastructure). In this exercise, direction will be provided to: 1) access the new Citrix VDI environment, 2) login to ArcFM, 3) retrieve a stored display, and 4) properly exit the system. Access Citrix VDI 1. Open an Internet Explorer window. 2. Type the following URL: http://citrix.cpsenergy.com 3. Select Enter on your keyboard. Note: Consider saving the URL as a favorite, such as “ GIS Citrix Receiver.” 4. When the Citrix application opens, select DESKTOPS from the top menu bar. 5. Click on Details to create the Prod VDI—Corp icon as a Favorite. 6. Click “Add to Favorites” then click “Open” to continue. 7. Use your NT username and password to sign in. The Prod VDI-Corp Desktop will then open and resemble the following image. 2 Notes: If your mouse pointer is not showing in the VDI screen, simply click into the area and the pointer will appear. If an MSN.com website loads, close it out. At the top of the Desktop is the XenDesktop toolbar. 8. Select and review the XenDesktop toolbar. A variety of tool tasks will appear. Select “Home” to minimize the VDI and return to the local desktop home screen. 3 Note: An initial DPI screen resolution setting is required for first time users. -

Virtual Desktop Connection (VDI) – Mac
Virtual Desktop Connection (VDI) – Mac *If you have already downloaded and installed the VMware View Client, Skip to Step 6. Step 1: Browse to the website https://www.cccneb.edu/vdi Step 2: Browse to the Client Installs list and select the link for Mac OS. Save the file to a location on your computer EX: Downloads. Step 3: Open your Downloads folder and double click the file VMware‐View‐ Client file. This will start the install process. Step 4: Click Agree to the End User Agreement. Step 5: To install VMware View Client, drag the icon to the Applications folder. Step 6: Open your Applications folders and run the VMware View Client. If you are prompted by a security warning, it is safe to click ok to allow. Step 7: Click Add Server and enter in the Hostname: vdi.cccneb.edu and click Continue Step 8: Enter your CCC username (EX: james12345) and password and click Continue. Step 9: Choose your desktop from the list and click Connect. You may see more than one option depending on your roll at CCC. Step 10: You are logged in and can use college resources. Unless otherwise advised, please save all data to usb thumb drives or web storage. Once you logoff from the system, all data will be erased and non‐retrievable PLEASE REMEMBER TO LOGOFF when you are finished. More information can be found on VMware’s website here: https://www.vmware.com/info?id=1109#mac For additional options (USB access, Local Drives) Please see APPENDIX A. APPENDIX A: By default, VMware View uses the PCoIP remote protocol to connect to Virtual Desktops. -
Troubleshooting Company
PUBLIC 2021-09-30 Troubleshooting company. All rights reserved. All rights company. affiliate THE BEST RUN 2021 SAP SE or an SAP SE or an SAP SAP 2021 © Content 1 Troubleshooting and Support...................................................3 1.1 Desktop Agent...............................................................3 Desktop Agent Error Messages.................................................4 Desktop Agent Blank Systray ..................................................6 Using the PC while a Bot is Running..............................................7 System Reboot during Unattended Mode..........................................8 1.2 Desktop Studio.............................................................. 9 Best Practices for Screen Lock and Disconnected Virtual Desktop Infrastructure ............. 9 Best Practices for PDF Library.................................................19 Best Practices for Web Service Calls............................................ 19 Best Practices to Handle Important Amount of Data During Scenario Execution............. 30 Best Practices for Captchas..................................................30 Best Practices for Automating SAP GUI Screens with Low Hierarchies.....................31 Best Practices for Managing Files..............................................33 Best Practices for Chrome Extension............................................35 Best Practices for managing Server Busy Pop-up...................................38 1.3 Cloud Factory...............................................................43 -

Virtual Desktop Connection (VDI) – Mac
Virtual Desktop Connection (VDI) – Mac Step 1: Open Safari to website https://vdi.cccneb.edu Step 2: If the View Client does not exist on your computer it will ask to download the View Client (6mb) Click the link to download the View Client. Step 3: Open your Downloads folder and double click the file VMware‐viewclient.dmg. This will start the install process Step 4: Click Agree to the End User Agreement Step 5: The VMware view Client should now be install and a shortcut is on the desktop Double Click to open it Microsoft Remote Desktop Connection Client 2 is required and may require you to download Follow the screens to download and install the Microsoft Remote Desktop Step 6: Run the VMware View Client and enter in the address field: vdi.cccneb.edu and click Connect Step 7: Enter you login credentials and your password and click continue Step 8: From the menu, pick an option and click connect. Step 9: You are logged in and can use college resources. For additional options (USB access, Local Drives) Use the RDC menu at the top of the screen and select preferences. Local drive access requests additional modifications to the system. Please see APPENDIX A. PLEASE REMEMBER TO LOGOFF when you are finished. Disclaimer: Please save all data to usb thumb drives or web storage. Once you logoff from the system, all data will be erased and non‐retrievable APPENDIX A Mac users of VMware View may find that they cannot see their local drives inside of a VMware View session. -
Off-The-Shelf Stylus: Using XR Devices for Handwriting and Sketching on Physically Aligned Virtual Surfaces
TECHNOLOGY AND CODE published: 04 June 2021 doi: 10.3389/frvir.2021.684498 Off-The-Shelf Stylus: Using XR Devices for Handwriting and Sketching on Physically Aligned Virtual Surfaces Florian Kern*, Peter Kullmann, Elisabeth Ganal, Kristof Korwisi, René Stingl, Florian Niebling and Marc Erich Latoschik Human-Computer Interaction (HCI) Group, Informatik, University of Würzburg, Würzburg, Germany This article introduces the Off-The-Shelf Stylus (OTSS), a framework for 2D interaction (in 3D) as well as for handwriting and sketching with digital pen, ink, and paper on physically aligned virtual surfaces in Virtual, Augmented, and Mixed Reality (VR, AR, MR: XR for short). OTSS supports self-made XR styluses based on consumer-grade six-degrees-of-freedom XR controllers and commercially available styluses. The framework provides separate modules for three basic but vital features: 1) The stylus module provides stylus construction and calibration features. 2) The surface module provides surface calibration and visual feedback features for virtual-physical 2D surface alignment using our so-called 3ViSuAl procedure, and Edited by: surface interaction features. 3) The evaluation suite provides a comprehensive test bed Daniel Zielasko, combining technical measurements for precision, accuracy, and latency with extensive University of Trier, Germany usability evaluations including handwriting and sketching tasks based on established Reviewed by: visuomotor, graphomotor, and handwriting research. The framework’s development is Wolfgang Stuerzlinger, Simon Fraser University, Canada accompanied by an extensive open source reference implementation targeting the Unity Thammathip Piumsomboon, game engine using an Oculus Rift S headset and Oculus Touch controllers. The University of Canterbury, New Zealand development compares three low-cost and low-tech options to equip controllers with a *Correspondence: tip and includes a web browser-based surface providing support for interacting, Florian Kern fl[email protected] handwriting, and sketching. -
What Is Desktop As a Service (Daas) • Daas Overview • How to Set up Daas • Daas Network Recommendations What Is Desktop As a Service (Daas)
What is included? • What is Desktop as a Service (DaaS) • DaaS Overview • How to set up DaaS • DaaS Network Recommendations What is Desktop as a Service (DaaS) From Any Location With Any Device that has a Browser INTERNET Cloud Applications DaaS Office 365 Fannie Mae Digital Workplace Training and Resources Email Us Teams Learning Community -3- DaaS Overview In May 2019, Gartner defined Virtual Desktop Infrastructure (VDI) and Desktop as a Service (DaaS) as follows: . VDI refers to Windows desktop operating systems that are hosted in a data center. The consuming organization owns the entire stack. DaaS refers to virtualized Windows OS hosted by a cloud provider. The consuming organization owns sizing, imaging and entitlement, while vendor owns the infrastructure and maintenance. Virtual Desktop Desktop as a Infrastructure (VDI) Service (DaaS) Entitlement Entitlement Desktop Delivery Desktop Delivery Desktop Imaging Desktop Imaging Licensing Strategic Licensing Direction Maintenance Maintenance Network Network Servers/Storage Servers/Storage Facility Hosting Facility Hosting Digital Workplace Training and Resources Email Us Teams Learning Community -4- Why DaaS? • Any Device ~> Any Time ~> Any Place • Supports cloud-first vision of Digital Transformation • Low latency to cloud applications (e.g., 8 ms roundtrip to AWS 2.0) • Enhanced security controls and assured update/patch delivery • Rapid provisioning (e.g., PC delivered in hours versus days/weeks) • Rapid PC break/fix solution • Cloud resiliency • Flexibility to better align specifications to user personas (Future State) • Currently there are three versions of DaaS (MyDesktop, My-Desktop and Hosted Applications). Know Your Desktop and to understand what is available is to know the desktop you are assigned. -

Introduction to Virtual Desktop Infrastructure
Introduction to Virtual Desktop Infrastructure From the Experts at Scale Computing Technical Whitepaper VDI with Scale Computing HC3® Table of Contents Introduction ....................................................................................................................................................3 HC3 Virtualization ..................................................................................................................................... 3-5 Storage Management .................................................................................................................................3 Resource Efficiency ....................................................................................................................................4 Scalability ....................................................................................................................................................4 VDI Density ..................................................................................................................................................5 The Connection Broker ............................................................................................................................. 6-7 Desktop Image Management.....................................................................................................................6 Desktop Mobility ........................................................................................................................................7 Virtual Desktop -

Download/View Mobile TS Documentation In
Mobile TS Documentation Copyright 2003 DDH Software, Inc http://www.ddhsoftware.com This guide is intended to be distributed with software that includes an end user agreement. This guide, as well as the software described in it, is furnished under license and may be used or copied only in accordance with the terms of this license. Except as permitted by any such license, no part of this guide may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, recording, or otherwise, without the prior written permission of DDH Software, Inc. Please note that the content in this guide is protected under copyright law even if it is not distributed with the software including an end user license agreement. The content of this guide is furnished for informational use only, is subject to change without notice, and should not be construed as a commitment by DDH Software, Inc. DDH Software, Inc assumes no responsibility or liability for any errors or inaccuracies that may appear in the informational content contained in this guide. Please remember that existing artwork or images that you may want to include in your project may be protected under copyright law. The unauthorized incorporation of such material into your new work could be a violation of the rights of the copyright owner. Please be sure to obtain any permission required from the copyright owner. Note: This product includes cryptographic software written by Eric Young ([email protected]) 1.0 – Introduction. Welcome to the Mobile TS application! This is an extremely powerful tool that will allow you to take control of your desktop computer or server from your handheld. -
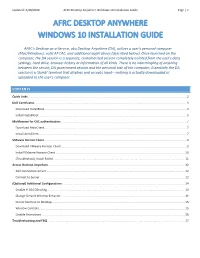
AFRC Desktop Anywhere Windows 10 Installation Guide Page | 1
Updated: 2/28/2020 AFRC Desktop Anywhere Windows 10 Installation Guide Page | 1 AFRC DESKTOP ANYWHERE WINDOWS 10 INSTALLATION GUIDE AFRC's Desktop-as-a-Service, aka Desktop Anywhere (DA), utilizes a user's personal computer (Mac/Windows), valid AF CAC, and additional applications (described below). Once launched on the computer, the DA session is a separate, containerized session completely isolated from the user's data, settings, hard drive, browser history or information of all kinds. There is no intermingling of anything between the secure, DA government session and the personal side of the computer, Essentially the DA session is a 'dumb' terminal that displays and accepts input---nothing is actually downloaded or uploaded to the user's computer. CONTENTS Quick Links ................................................................................................................................................................................................. 2 DoD Certificates......................................................................................................................................................................................... 3 Download InstallRoot ............................................................................................................................................................................. 3 Install InstallRoot ..................................................................................................................................................................................