Security and Privacy of Smartphone Messaging Applications1
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Ten Steps to Smartphone Security
Ten Steps to Smartphone Security Smartphones continue to grow in popularity and are now as powerful and functional as many computers. It is important to protect your smartphone just like you protect your computer as mobile cybersecurity threats are growing. These mobile security tips can help you reduce the risk of exposure to mobile security threats: 1. Set PINs and passwords. To prevent unauthorized access to your phone, set a password or Personal Identification Number (PIN) on your phone’s home screen as a first line of defense in case your phone is lost or stolen. When possible, use a different password for each of your important log-ins (email, banking, personal sites, etc.). You should configure your phone to automatically lock after five minutes or less when your phone is idle, as well as use the SIM password capability available on most smartphones. 2. Do not modify your smartphone’s security settings. Do not alter security settings for convenience. Tampering with your phone’s factory settings, jailbreaking, or rooting your phone undermines the built-in security features offered by your wireless service and smartphone, while making it more susceptible to an attack. 3. Backup and secure your data. You should backup all of the data stored on your phone – such as your contacts, documents, and photos. These files can be stored on your computer, on a removal storage card, or in the cloud. This will allow you to conveniently restore the information to your phone should it be lost, stolen, or otherwise erased. 4. Only install apps from trusted sources. -
Sophos Mobile Security
Sophos Mobile Security Protect your Android devices against malware and other threats The market dominance of Android devices and the inherent openness of Android led to the proliferation of malware and Potentially Unwanted Applications (PUA). SophosLabs detected over a million new pieces of malware in 2014 alone, and the growth rate is accelerating. Malware can lead to data loss, reputation loss, additional costs, and reduced performance. Highlights Protection and performance The Sophos Mobile Security antivirus app protects your Android devices without compromising Ì Privacy Advisor warns performance or battery life. The app uses up-to-the-minute intelligence from SophosLabs and the Sophos of potential privacy core antivirus engine. This means your apps are automatically scanned for malware as you install them. breaches Sophos Mobile Security’s consistent performance has earned recognition from independent testing agencies including AV-Test. Ì Security Advisor gives tips to improve device Malware protection security Our Sophos Mobile Security antivirus app protects your Android devices with proactive identification of malware. Your apps are automatically scanned for malware as you install them. Sophos includes protection Ì Loss and Theft for PUAs and low-reputation apps—new apps that have no known history and may pose a threat. PUAs Protection include adware, rootkits, diallers, and any association the app may have to previous malicious behaviour such as a certificate that has been compromised. Ì App Protection with additional passwords for Web protection sensitive apps Surf securely on the internet from your Android device. Sophos Mobile Security checks all websites against a Ì Spam Filter SophosLabs database for known malicious sites and prevents users from accessing them. -

An Empirical Survey on How Much Security and Privacy Customers Want in Instant Messengers
SECURWARE 2016 : The Tenth International Conference on Emerging Security Information, Systems and Technologies An Empirical Survey on how Much Security and Privacy Customers Want in Instant Messengers Thomas Paul Hans-Joachim Hof MuSe – Munich IT Security Research Group Munich University of Applied Sciences Munich University of Applied Sciences Lothstrasse 64, Munich, Germany Lothstraße 64, Munich, Germany e-mail: [email protected] e-mail: [email protected] Abstract— Instant messengers are popular communication developers of future instant messengers to decide on tools used by many people for everyday communication, as security features to implement. well as for work related communication. Following the This paper is structured as follows: Section II discusses disclosure of a massive surveillance system by Edward related work. Section III presents the design of the user Snowden, many users became aware of the risks of unsecure survey. Section IV discusses in detail the findings of the communication. Users increasingly ask for secure communication. However, unsecure instant messengers are still user survey. Section V presents the features of an ideal popular nowadays. This could be due to the fact, that, besides instant messenger fulfilling all the user preferences the large number of available instant messengers, no instant identified by the survey. A market simulation is used to messenger fully satisfies the users preferences. To research the show the potential of this ideal instant messenger. Section acceptance of security mechanisms in instant messengers, this VI summarizes the findings of the paper. paper presents an evaluation of user preferences for secure instant messengers. A user survey was conducted to rate the II. -

Total Defense Mobile Security
USER'S GUIDE Total Defense Mobile Security Total Defense Mobile Security User's Guide Publication date 2015.04.09 Copyright© 2015 Total Defense Mobile Security Legal Notice All rights reserved. No part of this book may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage and retrieval system, without written permission from an authorized representative of Total Defense. The inclusion of brief quotations in reviews may be possible only with the mention of the quoted source. The content can not be modified in any way. Warning and Disclaimer. This product and its documentation are protected by copyright. The information in this document is provided on an “as is” basis, without warranty. Although every precaution has been taken in the preparation of this document, the authors will not have any liability to any person or entity with respect to any loss or damage caused or alleged to be caused directly or indirectly by the information contained in this work. This book contains links to third-party Websites that are not under the control of Total Defense, therefore Total Defense is not responsible for the content of any linked site. If you access a third-party website listed in this document, you will do so at your own risk. Total Defense provides these links only as a convenience, and the inclusion of the link does not imply that Total Defense endorses or accepts any responsibility for the content of the third-party site. Trademarks. Trademark names may appear in this book. -
Investigating Mobile Messaging Security
Technische Universitat¨ Munchen¨ Department of Informatics Interdisciplinary Project in Electrical Engineering Investigating Mobile Messaging Security Elias Hazboun Technische Universitat¨ Munchen¨ Department of Informatics Interdisciplinary Project in Electrical Engineering Investigating Mobile Messaging Security Untersuchung von Mobile Messaging Sicherheit Author Elias Hazboun Supervisor Prof. Dr.-Ing. Georg Carle Advisor Dr. Matthias Wachs, Quirin Scheitle Date April 27, 2016 Informatik VIII Chair for Network Architectures and Services Abstract In this report we document our work in analyzing the security of a selection of mobile messaging apps. Focusing on network based security, we studied traffic generated by the apps to gain an understanding of the current state of applying encryption and authentication protocols. Our findings show a positive trend in security with developers steadily improving security with newer app updates partly due to the increased scrutiny from the community and academia. Although not all apps analyzed had perfect state of the art security properties, none have shown any major vulnerabilities exploited by normal adversaries. It was also evident that only one app - namely TextSecure - is using the industry standard TLS for server-client authentication and security while others have opted for custom made protocols and algorithms. I Contents 1 Introduction 1 1.1 Research Question . .2 1.2 Outline . .2 2 Background and Related Work 3 2.1 Methodology . .3 2.1.1 App Selection . .3 2.1.2 Approach . .3 2.2 Definition of Security Concepts . .4 2.2.1 Layers of Encryption . .4 2.2.2 Transport Layer Security Protocol (TLS) . .5 2.2.3 Perfect Forward Secrecy (PFS) . .5 2.2.4 Asynchronous Messaging Security . -
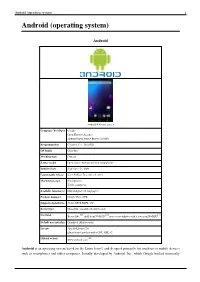
Android (Operating System) 1 Android (Operating System)
Android (operating system) 1 Android (operating system) Android Android 4.4 home screen Company / developer Google Open Handset Alliance Android Open Source Project (AOSP) Programmed in C (core), C++, Java (UI) OS family Unix-like Working state Current Source model Open source with proprietary components Initial release September 23, 2008 Latest stable release 4.4.2 KitKat / December 9, 2013 Marketing target Smartphones Tablet computers Available language(s) Multi-lingual (46 languages) Package manager Google Play, APK Supported platforms 32-bit ARM, MIPS, x86 Kernel type Monolithic (modified Linux kernel) [1] [2] [3] Userland Bionic libc, shell from NetBSD, native core utilities with a few from NetBSD Default user interface Graphical (Multi-touch) License Apache License 2.0 Linux kernel patches under GNU GPL v2 [4] Official website www.android.com Android is an operating system based on the Linux kernel, and designed primarily for touchscreen mobile devices such as smartphones and tablet computers. Initially developed by Android, Inc., which Google backed financially Android (operating system) 2 and later bought in 2005, Android was unveiled in 2007 along with the founding of the Open Handset Alliance: a consortium of hardware, software, and telecommunication companies devoted to advancing open standards for mobile devices. The first publicly available smartphone running Android, the HTC Dream, was released on October 22, 2008. The user interface of Android is based on direct manipulation, using touch inputs that loosely correspond to real-world actions, like swiping, tapping, pinching and reverse pinching to manipulate on-screen objects. Internal hardware such as accelerometers, gyroscopes and proximity sensors are used by some applications to respond to additional user actions, for example adjusting the screen from portrait to landscape depending on how the device is oriented. -

Enterprise Edition
Secure Communication. Simplified. SAFECHATS Problem Most companies use popular insecure email and ⛔ messaging services to communicate confidential information P The information flow within the Company is ⛔ disorganized Metadata is exposed and available to third-party ⛔ services SAFECHATS Introducing SAFECHATS Ultra-secure communication solution P Designed with security in mind SAFECHATS Why SAFECHATS? ✔ Information is always end-to-end encrypted by default P ✔ All-in-one communication suite: • Text messaging (one-on-one and group chats) • Voice calls • File transfers (no size and file type limits) SAFECHATS How does SAFECHATS solve the problem? ✔ Customizable white label solution ✔ Integrates with existing softwareP infrastructure ✔ Enterprise-wide account and contact list management, supervised audited chats for compliance SAFECHATS What makes SAFECHATS different? ✔ Your own isolated cloud environment or on-premise deployment P ✔ Customizable solution allows to be compliant with internal corporate security policies ✔ No access to your phone number and contact list SAFECHATS Screenshot Protection ✔ Notifications on iOS P ✔ DRM protection on Android SAFECHATS Identity Verification ✔ Protection from man-in-the-middle attacksP ✔ SMP Protocol SAFECHATS Privacy Features ✔ Show / hide messages and files P ✔ Recall messages and files ✔ Self-destructing messages and files SAFECHATS Additional Protection ✔ History retention control P ✔ Application lock: • PIN-code • Pattern-lock on Android devices • Touch ID on iOS devices SAFECHATS How does SAFECHATS -
Mobile Security Companion to the CIS Critical Security Controls (Version 6)
Mobile Security Companion to the CIS Critical Security Controls (Version 6) 1 Mobile Security Companion to the CIS Critical Security Controls (Version 6) Introduction ................................................................................................................................................................................................................................................................. 3 Description ................................................................................................................................................................................................................................................................... 5 CIS Critical Security Controls (Version 6): Mobile Security .................................................................................................................................................................... 5 2 Introduction Mobile devices are starting to replace laptops for regular business use. Organizations are building or porting their applications to mobile platforms, so users are increasingly accessing the same data with mobile as with their laptops. Also, organizations have increasingly implemented Bring Your Own Device (BYOD) policies to manage this trend. However, many organizations have been struggling with the increase of personal mobile devices, and don’t fully understand the security risks they may bring. There are concerns that their compact size makes them easy to lose, that they run newer operating systems that don’t -
Cryptography Whitepaper
Cryptography Whitepaper Threema uses modern cryptography based on open source components that strike an optimal balance between security, performance and message size. In this whitepaper, the algorithms and design decisions behind the cryptography in Threema are explained. VERSION: JUNE 21, 2021 Contents Overview 4 Open Source 5 End-to-End Encryption 5 Key Generation and Registration 5 Key Distribution and Trust 6 Message Encryption 7 Group Messaging 8 Key Backup 8 Client-Server Protocol Description 10 Chat Protocol (Message Transport Layer) 10 Directory Access Protocol 11 Media Access Protocol 11 Cryptography Details 12 Key Lengths 12 Random Number Generation 13 Forward Secrecy 14 Padding 14 Repudiability 15 Replay Prevention 15 Local Data Encryption 15 iOS 15 Android 16 Key Storage 16 iOS 16 Android 16 Push Notifications 17 iOS 17 Android 17 Threema • Cryptography Whitepaper Address Book Synchronization 17 Linking 18 ID Revocation 19 An Example 19 Profile Pictures 19 Web Client 20 Architecture 20 Connection Buildup 21 WebRTC Signaling 22 WebRTC Connection Buildup 22 Trusted Keys / Stored Sessions 23 Push Service 23 Self Hosting 24 Links 24 Threema Calls 24 Signaling 24 Call Encryption 24 Audio Encoding 25 Video Encoding 25 Privacy / IP Exposure 25 Threema Safe 26 Overview 26 Backup Format 27 Encryption 27 Upload/Storage 27 Backup Intervals 28 Restore/Decryption 28 Running a Custom Threema Safe Server 28 Threema • Cryptography Whitepaper Overview Threema uses two different encryption layers to protect messages between the sender and the recipient. • End-to-end encryption layer: this layer is between the sender and the recipient. • Transport layer: each end-to-end encrypted message is encrypted again for transport between the client and the server, in order to protect the header information. -
Securing and Managing Wearables in the Enterprise
White Paper: Securing and Managing Wearables in the Enterprise Streamline deployment and protect smartwatch data with Samsung Knox Configure White Paper: Securing and Managing Wearables in the Enterprise 2 Introduction: Smartwatches in the Enterprise As the wearable device market heats up, wrist-worn devices Industries as varied as healthcare, such as smartwatches are leading the pack. According to CCS Insight, forecasts for global sales of smart wearable devices finance, energy, transportation, will grow strongly over the next five years, with the global public safety, retail and hospitality market reaching nearly $30 billion by 2023.1 are deploying smartwatches for While smartwatches for fitness and activity tracking are popular, consumer demand is only part of the equation. added business value. Enterprises are also seeing business value in wearable devices. In a report by Robert Half Technology, 81 percent of CIOs surveyed expect wearable devices like smartwatches to Samsung has been working to address these concerns and become common tools in the workplace.2 has developed the tools to make its Galaxy and Galaxy Active smartwatches customizable, easily manageable and highly secure for enterprise users. This white paper will look at how these tools address key wearable security and manageability challenges, as well as considerations for smartwatch 81% deployments. of CIOs surveyed expect wearable devices like smartwatches to become common tools in the workplace. Industries as varied as healthcare, finance, energy, transportation, public safety, retail and hospitality are deploying smartwatches for added business value, such as hands-free communication for maintenance workers, task management, as well as physical monitoring of field workers in dangerous or remote locations. -

Threat Modeling Framework for Mobile Communication Systems
Threat modeling framework for mobile communication systems Siddharth Prakash Rao Silke Holtmanns Tuomas Aura Aalto University Nokia-Bell Labs Aalto University Espoo, Finland Espoo, Finland Espoo, Finland siddharth:rao@aalto: silke:holtmanns@nokia-bell- tuomas:aura@aalto: labs:com ABSTRACT protocols, which evolved in a more open setup, security tools avail- Due to the complex nature of mobile communication systems, most able in the public domain for the laer are now used by hackers to of the security eorts in its domain are isolated and scaered across exploit the mobile networks [9]. underlying technologies. is has resulted in an obscure view of Despite the odds, mobile communication systems have under- the overall security. In this work, we aempt to x this problem gone a fair amount of scrutiny from the security research com- by proposing a domain-specic threat modeling framework. By munity. For example, internal components of a mobile device [71, gleaning from a diverse and large body of security literature, we 74, 101], radio communication between the phone and the cell systematically organize the aacks on mobile communications into towers[37, 162], and mobile core network protocols [55, 80, 122] various tactics and techniques. Our framework is designed to model have been tested for security-critical issues. All these isolated adversarial behavior in terms of its aack phases and to be used as research eorts are scaered across underlying protocols and tech- a common taxonomy matrix. We also provide concrete examples nologies, and, it has resulted in an obscure and complex view of mo- of using the framework for modeling the aacks individually and bile communication security. -

How Secure Is Textsecure?
How Secure is TextSecure? Tilman Frosch∗y, Christian Mainkay, Christoph Badery, Florian Bergsmay,Jorg¨ Schwenky, Thorsten Holzy ∗G DATA Advanced Analytics GmbH firstname.lastname @gdata.de f g yHorst Gortz¨ Institute for IT-Security Ruhr University Bochum firstname.lastname @rub.de f g Abstract—Instant Messaging has gained popularity by users without providing any kind of authentication. Today, many for both private and business communication as low-cost clients implement only client-to-server encryption via TLS, short message replacement on mobile devices. However, until although security mechanisms like Off the Record (OTR) recently, most mobile messaging apps did not protect confi- communication [3] or SCIMP [4] providing end-to-end con- dentiality or integrity of the messages. fidentiality and integrity are available. Press releases about mass surveillance performed by intelli- With the advent of smartphones, low-cost short-message gence services such as NSA and GCHQ motivated many people alternatives that use the data channel to communicate, to use alternative messaging solutions to preserve the security gained popularity. However, in the context of mobile ap- and privacy of their communication on the Internet. Initially plications, the assumption of classical instant messaging, fueled by Facebook’s acquisition of the hugely popular mobile for instance, that both parties are online at the time the messaging app WHATSAPP, alternatives claiming to provide conversation takes place, is no longer necessarily valid. secure communication experienced a significant increase of new Instead, the mobile context requires solutions that allow for users. asynchronous communication, where a party may be offline A messaging app that claims to provide secure instant for a prolonged time.