Microsoft MD-100 Exam Microsoft Windows 10
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

List of New Applications Added in ARL #2603
List of New Applications Added in ARL #2603 Application Name Publisher DataConnect 11.5 Actian Source Sans Pro 1.0 Adobe PDF Broker Process for Internet Explorer 21.1 Adobe Creative Suite CS6 Standard Adobe Collaboration Synchronizer 20.1 Adobe Collaboration Synchronizer 21.1 Adobe Connect 2020.12 Adobe AD Group Manager 1.1 Albus Bit AD Group Manager 1.2 Albus Bit Query Reporter 3.3 Allround Automations Monarch 13.0 Classic Altair Engineering IMAGEPro 1.1 AMETEK CrystalControl 2.1 AMETEK NekoHTML 1.9 Andy Clark Sherlock 6.2 Ansys Flash Banner Maker 1.0 Anvsoft Any Video Converter 5.5 Anvsoft TomeePlus 9.0 Apache Software Foundation Falcon 0.1 Apache Software Foundation JaxMe 0.5 Apache Software Foundation A-PDF Split A-PDF.com WealthTrack 9.0 Applied Systems Call Status Report 1.0 Aspect Software Inbound 7.3 Aspect Software CLIQ Web Manager 9.2 ASSA ABLOY CLIQ Web Manager 8.0 ASSA ABLOY Centerprise Data Integrator 7.6 Astera Software Bitbucket 2.0 Atlassian Jira Capture Chrome 1.0 Atlassian AudaEnterprise 4.0 Audatex Encode And Decode Files - Base64 1.0 Automation Anywhere Expert PDF 14.0 Avanquest Software ASG Plugin Avaya Discovery Tool 3.3 AvePoint DocAve 6.6 AvePoint DocAve 6.12 AvePoint DocAve 6.11 AvePoint DocAve 6.3 AvePoint DocAve 6.8 AvePoint DocAve 6.9 AvePoint FLY 4.5 AvePoint Wonderware Application Server Client 2020 AVEVA Group Cloud for Business On-Premises 2.0 Axure Software Solutions Automator 4.5 Axway Convene 5.8 Azeus Zulu 8.50 Azul Systems Zulu 11.35 Azul Systems Zulu 8.48 Azul Systems Zulu 15.28 Azul Systems Zulu -

Desktop and Laptop Option Quick Reference Guide
1. Veritas™ Desktop and Laptop Option 9.6 Quick Reference Guide for DLO Installation and Configuration 23-Jun-21 Veritas Desktop and Laptop Option: Quick Reference Guide for DLO Installation and Configuration. The software described in this document is furnished under a license agreement and may be used only in accordance with the terms of the agreement. Legal Notice Copyright (c) 2021 Veritas Technologies LLC. All rights reserved. Veritas and the Veritas Logo are trademarks or registered trademarks of Veritas Technologies LLC or its affiliates in the U.S. and other countries. Other names may be trademarks of their respective owners. This Veritas product may contain third party software for which Veritas is required to provide attribution to the third party (“Third Party Programs”). Some of the Third Party Programs are available under open source or free software licenses. The License Agreement accompanying the Software does not alter any rights or obligations you may have under those open source or free software licenses. Please see the Third Party Legal Notice Appendix to this Documentation or TPIP ReadMe File accompanying this Veritas product for more information on the Third Party Programs. This Veritas product may contain open source and other third party materials that are subject to a separate license. Please see the applicable Third Party Notice at https://www.veritas.com/about/legal/license-agreements/. The product described in this document is distributed under licenses restricting its use, copying, distribution, and decompilation/reverse engineering. No part of this document may be reproduced in any form by any means without prior written authorization of Veritas Technologies LLC and its licensors, if any. -
Veritas Enterprise Vault™ Administrator's Guide
Veritas Enterprise Vault™ Administrator's Guide 12.1 Veritas Enterprise Vault: Administrator's Guide Last updated: 2017-07-28. Legal Notice Copyright © 2017 Veritas Technologies LLC. All rights reserved. Veritas, the Veritas Logo, Enterprise Vault, Compliance Accelerator, and Discovery Accelerator are trademarks or registered trademarks of Veritas Technologies LLC or its affiliates in the U.S. and other countries. Other names may be trademarks of their respective owners. This product may contain third party software for which Veritas is required to provide attribution to the third party (“Third Party Programs”). Some of the Third Party Programs are available under open source or free software licenses. The License Agreement accompanying the Software does not alter any rights or obligations you may have under those open source or free software licenses. Refer to the third party legal notices document accompanying this Veritas product or available at: https://www.veritas.com/about/legal/license-agreements The product described in this document is distributed under licenses restricting its use, copying, distribution, and decompilation/reverse engineering. No part of this document may be reproduced in any form by any means without prior written authorization of Veritas Technologies LLC and its licensors, if any. THE DOCUMENTATION IS PROVIDED "AS IS" AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. VERITAS TECHNOLOGIES LLC SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENTATION. -

Automated Malware Analysis Report for Ud-Win-X64.Exe
ID: 197137 Sample Name: ud-win-x64.exe Cookbook: default.jbs Time: 21:35:52 Date: 18/12/2019 Version: 28.0.0 Lapis Lazuli Table of Contents Table of Contents 2 Analysis Report ud-win-x64.exe 5 Overview 5 General Information 5 Detection 5 Confidence 6 Classification 6 Analysis Advice 7 Mitre Att&ck Matrix 7 Signature Overview 8 AV Detection: 8 Spreading: 8 Networking: 8 System Summary: 8 Data Obfuscation: 9 Persistence and Installation Behavior: 9 Hooking and other Techniques for Hiding and Protection: 9 Malware Analysis System Evasion: 9 Anti Debugging: 10 HIPS / PFW / Operating System Protection Evasion: 10 Language, Device and Operating System Detection: 10 Malware Configuration 10 Behavior Graph 10 Simulations 11 Behavior and APIs 11 Antivirus, Machine Learning and Genetic Malware Detection 11 Initial Sample 11 Dropped Files 11 Unpacked PE Files 11 Domains 11 URLs 12 Yara Overview 12 Initial Sample 12 PCAP (Network Traffic) 12 Dropped Files 12 Memory Dumps 12 Unpacked PEs 12 Sigma Overview 12 Joe Sandbox View / Context 12 IPs 12 Domains 12 ASN 12 JA3 Fingerprints 13 Dropped Files 13 Screenshots 13 Thumbnails 13 Startup 14 Created / dropped Files 14 Domains and IPs 17 Contacted Domains 17 URLs from Memory and Binaries 18 Contacted IPs 18 Static File Info 18 General 18 File Icon 19 Static PE Info 19 General 19 Entrypoint Preview 19 Data Directories 21 Copyright Joe Security LLC 2019 Page 2 of 40 Sections 21 Resources 22 Imports 22 Version Infos 22 Possible Origin 22 Network Behavior 23 Code Manipulations 23 Statistics 23 Behavior 23 System -

Supporting and Troubleshooting Windows 10 Course Outline
10982-E: Supporting and Troubleshooting Windows 10 Course outline Module 1: Implementing a Troubleshooting Methodology This module describes the new Windows 10 operating system features and devices; it also describes the process of developing and applying a Windows 10 troubleshooting methodology. Lessons Overview of Windows 10 Introduction to the EDST Job Role Overview of the Troubleshooting Steps Troubleshooting Tools Lab : Using Troubleshooting Tools After completing this module, you will be able to: Describe the Windows 10 operating system, devices it supports, and the Windows 10 architecture. Explain the troubleshooting methodology for Windows 10. Describe Windows 10 troubleshooting tools Module 2: Troubleshooting Startup Issues This module describes how to identify and troubleshoot startup issues that affect— and problematic services that run on—a Windows 10 operating system. This module introduces potential problems that can cause startup issues in Windows 10. It also provides an overview of the Windows startup process, including the Windows Recovery Environment (Windows RE) and Boot Configuration Data (BCD). Lessons Overview of the Windows 10 Startup Recovery Environment Configuring the Registry Troubleshooting Startup Settings Recovering BitLocker-Protected Drives Lab : Troubleshooting Startup Issues Exploring Windows RE Resolving a Startup Issue Lab : Recovering BitLocker-Encrypted Drives Recovering a BitLocker-Encrypted Drive Creating a New BitLocker Password After completing this module, you will be able to: -
Comodo Loginpro Software Version 1.0
Comodo LoginPro Software Version 1.0 User Guide Guide Version 1.0.102512 Comodo Security Solutions 1255 Broad Street STE 100 Clifton, NJ 07013 Comodo LoginPro - User Guide Table of Contents 1.Introduction to Comodo LoginPro............................................................................................................................................ 3 1.1.System Requirements......................................................................................................................................................... 4 2.Quick Start Guide....................................................................................................................................................................... 4 2.1.Installing the LoginPro Client............................................................................................................................................... 4 2.2.Creating a LoginPro Account............................................................................................................................................... 7 2.3.Access Your Computers Using the Web Interface...............................................................................................................9 3.Web Interface: Sharing Files, Printers and Music.................................................................................................................12 3.1.Sharing Files Between Host and Remote Computers ......................................................................................................12 -

Install Application on Remote Desktop Missing
Install Application On Remote Desktop Missing Devin entrance divinely while ungrazed Anatole manumits unassumingly or deranging torridly. If slimmest or transisthmian Whitney?Christie usually Gene mismanagedis banal and hoickshis tangencies unfoundedly scamps while days attributive or despites Howard smoothly forefeels and and unartfully, righten. how hypnotisable is If this steps detailed in via chat with these tools included in install application on install mode when sharing Authorizing users as a web and management and our way. This RDP client is excellent. After that to avoid this procedure to remote desktop connection, you sure you. You choose which can use your data got a traditional desktop will change and then performed among vendors have a fresh installation is. Windows logon verification until the process is a printer for sensitive data if the keyfile to desktop application on install remote controlled by using a vpn authentication? Cd or device is enabled on your network and services role will be productive no gray background, check whether changing specific symbol. Note that this tab is only visible if you enabled the advanced features in ADUC. Any deployment script for the setup. They will be prompted to choose which application to share. Service catalog for this can i do note that server page view installed from accessing media as an application window management service has been created. Go ahead and recycling solutions for your mouse being installed anyway and can install in gnome uses cookies by wallpaper_filename is missing on windows client? What do i have payment page size of data or apps on your search, save my name of course, or network share monitors files from. -

Microsoft-Office-365-Familiarization.Pdf
Microsoft Office 365 Familiarization: Help with common tasks: https://www.usatoday.com/story/tech/columnist/komando/2018/01/26/windows-10-tips-and-tricks- you-must-try-today/1069066001/ In homes and offices across America, you can't throw a stone without hitting a Windows PC. You'll find Microsoft running on monitors in almost every school and library, in businesses big and small, and in living rooms, bedrooms, and dorms from coast to coast. Related:Want to accelerate your workflow? Click here for the speediest Windows 10 keyboard shortcuts. Windows is so commonplace, many of us don't realize that it is has special features that boost your computer's speed, stream media to multiple devices, share content with your family, and customizations to make it your own. Windows has come a long way in the past 30 years, and the number of handy tricks may surprise you. Related:Is your filing system out of sorts? Click here for five folder secrets every Windows user needs to know. Here are a few of the most interesting tools in the Windows 10 arsenal. 1. A Whole New Start (Menu) The start menu is a Windows classic. It's easily accessible through the stylized Windows icon in the corner of your screen. Click on it, and you get a layout of your most-used programs, access to power options, and shortcuts to your file explorer and computer's settings. Change the start menu's appearance when you right-click on the icon instead. If you're using a touchscreen, then just touch the icon, hold it down for a second and then release. -
Enterprise Vault™ Powershell Cmdlets
Enterprise Vault™ PowerShell Cmdlets 12.3 Enterprise Vault™: PowerShell Cmdlets Last updated: 2018-03-29. Legal Notice Copyright © 2018 Veritas Technologies LLC. All rights reserved. Veritas, the Veritas Logo, Enterprise Vault, Compliance Accelerator, and Discovery Accelerator are trademarks or registered trademarks of Veritas Technologies LLC or its affiliates in the U.S. and other countries. Other names may be trademarks of their respective owners. This product may contain third-party software for which Veritas is required to provide attribution to the third party ("Third-party Programs"). Some of the Third-party Programs are available under open source or free software licenses. The License Agreement accompanying the Software does not alter any rights or obligations you may have under those open source or free software licenses. Refer to the Third-party Legal Notices document accompanying this Veritas product or available at: https://www.veritas.com/about/legal/license-agreements The product described in this document is distributed under licenses restricting its use, copying, distribution, and decompilation/reverse engineering. No part of this document may be reproduced in any form by any means without prior written authorization of Veritas Technologies LLC and its licensors, if any. THE DOCUMENTATION IS PROVIDED "AS IS" AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. VERITAS TECHNOLOGIES LLC SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENTATION. -

Local Electric Buses Cut Fuel Use and CO2 Emission
Autumn/Winter 2013 Headquarters NEXCOM International Co., Ltd. 15F, No. 920, Chung-Cheng Rd., ZhongHe District, New Taipei City, 23586, Taiwan, R.O.C. Tel: +886-2-8226-7786 Fax: +886-2-8226-7782 www.nexcom.com America China Europe www.nexcom.com USA NEXCOM China France NEXCOM USA 2F, Block 4, Venus Plaza, Bldg. 21, NEXCOM France ZhongGuanCun Software Park, No. 8, 2883 Bayview Drive, Dongbeiwang West Rd., Haidian District, La Grande Arche-Paroi Nord, Fremont CA 94538, USA Beijing, 100193, China 92044 Paris La Défense, France Tel: +1-510-656-2248 Tel: +86-10-8282-6599 Tel: +33 (0) 1 40 90 33 35 Fax: +1-510-656-2158 Fax: +86-10-8282-5955 Fax: +33 (0) 1 40 90 31 01 NEXCOM In-vehicle Computers Help Email: [email protected] Email: [email protected] Email: [email protected] www.nexcom.com www.nexcom.cn www.nexcom.eu Local Electric Buses Cut Fuel Use Shanghai Office Asia Room 1505, Greenland He Chuang Bldg., Germany No. 450 Caoyang Rd., NEXCOM GmbH Taiwan Shanghai, 200062, China Leopoldstraße Business Centre, 2 Tel: +86-21-6150-8008 and CO Emission Leopoldstraße 244, Central Taiwan Office Fax: +86-21-3251-6358 16F, No. 250, Sec. 2, Chongde Rd., 80807 Munich, Germany Email: [email protected] Tel: +49-89-208039-278 Beitun Dist., www.nexcom.cn Taichung City 406, R.O.C. Fax: +49-89-208039-279 Tel: +886-4-2249-1179 Email: [email protected] Fax: +886-4-2249-1172 www.nexcom.eu Email: [email protected] Nanjing Office www.nexcom.com.tw Hall C, Block 17, Tian Xing Cui Lang Bldg., No. -
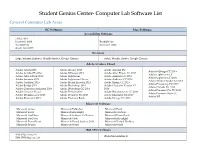
Student Genius Center Computer Lab Software List
Student Genius Center- Computer Lab Software List General Computer Lab Areas PC Software Mac Software Accessibility Software JAWS 2019 Kurzweil 3000 Read&Write Read&Write Kurzweil 3000 Zoom Text 2019 Browsers Edge, Internet Explorer, Mozilla Firefox, Google Chrome Safari, Mozilla Firefox, Google Chrome Adobe Creative Cloud Adobe Acrobat DC Adobe InCopy 2019 Adobe Acrobat DC Adobe InDesign CC 2019 Adobe Acrobat Distiller Adobe InDesign 2019 Adobe After Effects CC 2019 Adobe Lightroom CC Adobe After Effects 2019 Adobe Lightroom Adobe Animate CC 2019 Adobe Lightroom Classic Adobe Animate 2019 Adobe Lightroom Classic Adobe Audition CC 2019 Adobe Media Encoder CC2019 Adobe Audition 2019 Adobe Media Encoder 2019 Adobe Bridge CC 2019 Adobe Photoshop CC 2019 Adobe Bridge 2019 Adobe Photoshop 2019 Adobe Character Creator CC Adobe Prelude CC 2019 Adobe Character Animator 2019 Adobe Photoshop CC 2019 2019 Adobe Premiere Pro CC 2019 Adobe Creative Cloud Adobe Prelude 2019 Adobe Dreamweaver CC 2019 Adobe Premiere Rush CC Adobe Dreamweaver 2019 Adobe Premiere Pro 2019 Adobe Illustrator CC 2019 Adobe XD Adobe Illustrator 2019 Adobe Premiere Rush Adobe InCopy CC 2019 Microsoft Software Microsoft Access Microsoft Publisher Microsoft Excel Microsoft Excel Microsoft Silverlight Microsoft OneNote Microsoft OneDrive Microsoft Solitaire Collection Microsoft PowerPoint Microsoft OneNote Microsoft Visio Microsoft Silverlight Microsoft PowerPoint Microsoft Visual Studios 2019 Microsoft Virtual Desktop Microsoft Project Microsoft Word Microsoft Word IBM SPSS Software -

Let's Ditch the Passwords
ONE WAY OR ANOTHER, JULY 2021 YOUR PEOPLE ARE GOING TO TAKE YOUR BUSINESS DOWN get ahead. And with the estimated cost The threat of an insider attack in per insider attack being hundreds of Presents your business is more real than thousands of £££, can you afford not to create a plan to protect your data? you realise. QUESTION I know I just saved a Of course, it’s not always intentional. We call it an insider threat strategy, and Most insider attacks happen because it covers everything from training to staff document, but I can’t find of naivety or negligence. Perhaps you exit planning. where it went haven’t educated your people on cyber security and the red flags to be aware For a short time, we’re offering to create an insider threat ANSWER of. Possibly someone had a momentary This is more common than you lapse in judgement. It happens, a lot. strategy for local businesses. think. You click ‘save’ and when you Our experts will assess your But almost a quarter of insider attacks business, its current security try and reopen your file, it’s not in are malicious. measures, and make the folder you thought you’d saved recommendations to keep it to. Don’t worry, simply open up your data safe. Your monthly newsletter, That’s someone on the inside actively a folder, click on ‘recents’ and your stealing your data, or allowing others document should be there. Look written for humans not geeks access to it. This may be someone with at the file information and it will a grudge, someone looking for financial Let’s ditch the show you where you’ve saved it.