Security Analysis of U2F Remember Me Implementations in the Wild Gwendal Patat, Mohamed Sabt
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Support for U2F FIDO Tokens in Mobile Applications
Masaryk University Faculty of Informatics Support for U2F FIDO tokens in mobile applications Bachelor’s Thesis Marek Hrašna Brno, Spring 2019 Masaryk University Faculty of Informatics Support for U2F FIDO tokens in mobile applications Bachelor’s Thesis Marek Hrašna Brno, Spring 2019 This is where a copy of the official signed thesis assignment and a copy ofthe Statement of an Author is located in the printed version of the document. Declaration Hereby I declare that this paper is my original authorial work, which I have worked out on my own. All sources, references, and literature used or excerpted during elaboration of this work are properly cited and listed in complete reference to the due source. Marek Hrašna Advisor: RNDr. Petr Švenda Ph.D. i Acknowledgements I would like to express my gratitude to my advisor, RNDr. Petr Švenda Ph.D. his guidance, patience, and helpful advice throughout the mak- ing of this thesis. iii Abstract One of the biggest security problems on the Internet is the usage of weak credentials, such as passwords, for user authentication. Second- Factor Authentication (2FA) provides a valid answer to this threat. Still, there are many 2FA schemes vulnerable to prominent web threats such as phishing attacks. The U2F protocol provides a phishing-resistant 2FA solution, optionally based on secure hardware elements. This thesis provides an analysis of the security brought by the U2F authen- tication scheme and shows its real-world adaptation in mobile plat- forms. It discusses problems that occur while using commercial tokens implementing this standard and describes the process of installing a U2F applet onto a JavaCard while discussing possible problems that may occur. -

Songs by Title Karaoke Night with the Patman
Songs By Title Karaoke Night with the Patman Title Versions Title Versions 10 Years 3 Libras Wasteland SC Perfect Circle SI 10,000 Maniacs 3 Of Hearts Because The Night SC Love Is Enough SC Candy Everybody Wants DK 30 Seconds To Mars More Than This SC Kill SC These Are The Days SC 311 Trouble Me SC All Mixed Up SC 100 Proof Aged In Soul Don't Tread On Me SC Somebody's Been Sleeping SC Down SC 10CC Love Song SC I'm Not In Love DK You Wouldn't Believe SC Things We Do For Love SC 38 Special 112 Back Where You Belong SI Come See Me SC Caught Up In You SC Dance With Me SC Hold On Loosely AH It's Over Now SC If I'd Been The One SC Only You SC Rockin' Onto The Night SC Peaches And Cream SC Second Chance SC U Already Know SC Teacher, Teacher SC 12 Gauge Wild Eyed Southern Boys SC Dunkie Butt SC 3LW 1910 Fruitgum Co. No More (Baby I'm A Do Right) SC 1, 2, 3 Redlight SC 3T Simon Says DK Anything SC 1975 Tease Me SC The Sound SI 4 Non Blondes 2 Live Crew What's Up DK Doo Wah Diddy SC 4 P.M. Me So Horny SC Lay Down Your Love SC We Want Some Pussy SC Sukiyaki DK 2 Pac 4 Runner California Love (Original Version) SC Ripples SC Changes SC That Was Him SC Thugz Mansion SC 42nd Street 20 Fingers 42nd Street Song SC Short Dick Man SC We're In The Money SC 3 Doors Down 5 Seconds Of Summer Away From The Sun SC Amnesia SI Be Like That SC She Looks So Perfect SI Behind Those Eyes SC 5 Stairsteps Duck & Run SC Ooh Child SC Here By Me CB 50 Cent Here Without You CB Disco Inferno SC Kryptonite SC If I Can't SC Let Me Go SC In Da Club HT Live For Today SC P.I.M.P. -
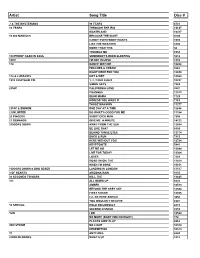
Copy UPDATED KAREOKE 2013
Artist Song Title Disc # ? & THE MYSTERIANS 96 TEARS 6781 10 YEARS THROUGH THE IRIS 13637 WASTELAND 13417 10,000 MANIACS BECAUSE THE NIGHT 9703 CANDY EVERYBODY WANTS 1693 LIKE THE WEATHER 6903 MORE THAN THIS 50 TROUBLE ME 6958 100 PROOF AGED IN SOUL SOMEBODY'S BEEN SLEEPING 5612 10CC I'M NOT IN LOVE 1910 112 DANCE WITH ME 10268 PEACHES & CREAM 9282 RIGHT HERE FOR YOU 12650 112 & LUDACRIS HOT & WET 12569 1910 FRUITGUM CO. 1, 2, 3 RED LIGHT 10237 SIMON SAYS 7083 2 PAC CALIFORNIA LOVE 3847 CHANGES 11513 DEAR MAMA 1729 HOW DO YOU WANT IT 7163 THUGZ MANSION 11277 2 PAC & EMINEM ONE DAY AT A TIME 12686 2 UNLIMITED DO WHAT'S GOOD FOR ME 11184 20 FINGERS SHORT DICK MAN 7505 21 DEMANDS GIVE ME A MINUTE 14122 3 DOORS DOWN AWAY FROM THE SUN 12664 BE LIKE THAT 8899 BEHIND THOSE EYES 13174 DUCK & RUN 7913 HERE WITHOUT YOU 12784 KRYPTONITE 5441 LET ME GO 13044 LIVE FOR TODAY 13364 LOSER 7609 ROAD I'M ON, THE 11419 WHEN I'M GONE 10651 3 DOORS DOWN & BOB SEGER LANDING IN LONDON 13517 3 OF HEARTS ARIZONA RAIN 9135 30 SECONDS TO MARS KILL, THE 13625 311 ALL MIXED UP 6641 AMBER 10513 BEYOND THE GREY SKY 12594 FIRST STRAW 12855 I'LL BE HERE AWHILE 9456 YOU WOULDN'T BELIEVE 8907 38 SPECIAL HOLD ON LOOSELY 2815 SECOND CHANCE 8559 3LW I DO 10524 NO MORE (BABY I'MA DO RIGHT) 178 PLAYAS GON' PLAY 8862 3RD STRIKE NO LIGHT 10310 REDEMPTION 10573 3T ANYTHING 6643 4 NON BLONDES WHAT'S UP 1412 4 P.M. -

Security Keys: Practical Cryptographic Second Factors for the Modern Web
Security Keys: Practical Cryptographic Second Factors for the Modern Web Juan Lang, Alexei Czeskis, Dirk Balfanz, Marius Schilder, and Sampath Srinivas Google, Inc., Mountain View, CA, USA Abstract. \Security Keys" are second-factor devices that protect users against phishing and man-in-the-middle attacks. Users carry a single de- vice and can self-register it with any online service that supports the protocol. The devices are simple to implement and deploy, simple to use, privacy preserving, and secure against strong attackers. We have shipped support for Security Keys in the Chrome web browser and in Google's online services. We show that Security Keys lead to both an increased level of security and user satisfaction by analyzing a two year deployment which began within Google and has extended to our consumer-facing web applications. The Security Key design has been standardized by the FIDO Alliance, an organization with more than 250 member companies spanning the industry. Currently, Security Keys have been deployed by Google, Dropbox, and GitHub. An updated and extended tech report is available at https://github.com/google/u2f- ref-code/docs/SecurityKeys_TechReport.pdf. 1 Introduction Recent account takeovers [1{3] have once again highlighted the challenge of securing user data online: accounts are often protected by no more than a weak password [4] and whatever implicit signals (if any) that the online service provider has collected to distinguish legitimate users from account hijackers. Academic research has produced numerous proposals to move away from passwords, but in practice such efforts have largely been unsuccessful [5, 6]. In- stead, many service providers augment password-based authentication with a second factor in the form of a one-time passcode (OTP), e.g., [7, 8]. -

A Tale of Two Studies: the Best and Worst of Yubikey Usability
A Tale of Two Studies: The Best and Worst of YubiKey Usability †∗ ∗ ∗ ∗ z ∗ Joshua Reynolds , Trevor Smith , Ken Reese , Luke Dickinson , Scott Ruoti , Kent Seamons y ∗ z University of Illinois at Urbana-Champaign, Brigham Young University, MIT Lincoln Laboratory [email protected], ftsmith, ken.reese, [email protected], [email protected], [email protected] Abstract—Two-factor authentication (2FA) significantly device that authenticates the user after the user presses a improves the security of password-based authentication. button on the security key [8]. The button tap is a test of Recently, there has been increased interest in Universal 2nd user presence and prevents malware on the host device from Factor (U2F) security keys—small hardware devices that require users to press a button on the security key to authenticate. To using the security key surreptitiously. Most commonly, security examine the usability of security keys in non-enterprise usage, keys are designed to be plugged into a USB port, though we conducted two user studies of the YubiKey, a popular line they can also communicate with other devices using wireless of U2F security keys. The first study tasked 31 participants protocols (e.g., NFC, Bluetooth). with configuring a Windows, Google, and Facebook account to U2F security keys are designed to be easy-to-adopt and authenticate using a YubiKey. This study revealed problems with setup instructions and workflow including users locking use in day-to-day life, while protecting users against phishing themselves out of their operating system or thinking they had and man-in-the-middle attacks [8]. -

Of Two Minds About Two-Factor: Understanding Everyday FIDO U2F
Of Two Minds about Two-Factor: Understanding Everyday FIDO U2F Usability through Device Comparison and Experience Sampling Stéphane Ciolino, OneSpan Innovation Centre & University College London; Simon Parkin, University College London; Paul Dunphy, OneSpan Innovation Centre https://www.usenix.org/conference/soups2019/presentation/ciolino This paper is included in the Proceedings of the Fifteenth Symposium on Usable Privacy and Security. August 12–13, 2019 • Santa Clara, CA, USA ISBN 978-1-939133-05-2 Open access to the Proceedings of the Fifteenth Symposium on Usable Privacy and Security is sponsored by USENIX. Of Two Minds about Two-Factor: Understanding Everyday FIDO U2F Usability through Device Comparison and Experience Sampling Stéphane Ciolino Simon Parkin Paul Dunphy OneSpan Innovation Centre University College London OneSpan Innovation Centre & University College London [email protected] [email protected] [email protected] Abstract words and tokens) is widely recognized as an effective tech- Security keys are phishing-resistant two-factor authentica- nique to protect both corporate and personal online accounts tion (2FA) tokens based upon the FIDO Universal 2nd Factor against account hijacking threats. Indeed, there are already ex- (U2F) standard. Prior research on security keys has revealed amples of citizens being advised to use Two-Factor Authenti- intuitive usability concerns, but there are open challenges to cation (2FA) by government agencies (as in the UK [35]). The better understand user experiences with heterogeneous de- most common second factor is a One-Time Passcode (OTP) vices and to determine an optimal user experience for every- received via a text message to a mobile device [5]. -

Karaoke Catalog Updated On: 11/01/2019 Sing Online on in English Karaoke Songs
Karaoke catalog Updated on: 11/01/2019 Sing online on www.karafun.com In English Karaoke Songs 'Til Tuesday What Can I Say After I Say I'm Sorry The Old Lamplighter Voices Carry When You're Smiling (The Whole World Smiles With Someday You'll Want Me To Want You (H?D) Planet Earth 1930s Standards That Old Black Magic (Woman Voice) Blackout Heartaches That Old Black Magic (Man Voice) Other Side Cheek to Cheek I Know Why (And So Do You) DUET 10 Years My Romance Aren't You Glad You're You Through The Iris It's Time To Say Aloha (I've Got A Gal In) Kalamazoo 10,000 Maniacs We Gather Together No Love No Nothin' Because The Night Kumbaya Personality 10CC The Last Time I Saw Paris Sunday, Monday Or Always Dreadlock Holiday All The Things You Are This Heart Of Mine I'm Not In Love Smoke Gets In Your Eyes Mister Meadowlark The Things We Do For Love Begin The Beguine 1950s Standards Rubber Bullets I Love A Parade Get Me To The Church On Time Life Is A Minestrone I Love A Parade (short version) Fly Me To The Moon 112 I'm Gonna Sit Right Down And Write Myself A Letter It's Beginning To Look A Lot Like Christmas Cupid Body And Soul Crawdad Song Peaches And Cream Man On The Flying Trapeze Christmas In Killarney 12 Gauge Pennies From Heaven That's Amore Dunkie Butt When My Ship Comes In My Own True Love (Tara's Theme) 12 Stones Yes Sir, That's My Baby Organ Grinder's Swing Far Away About A Quarter To Nine Lullaby Of Birdland Crash Did You Ever See A Dream Walking? Rags To Riches 1800s Standards I Thought About You Something's Gotta Give Home Sweet Home -
The Webauthn Standard: Why It Should Matter to the Public Sector and How It Works Executive Summary
WEBAUTHN WHITE PAPER SERIES: MAY 2020 The WebAuthn Standard: Why It Should Matter to the Public Sector and How It Works Executive Summary This paper is the second in a series of WebAuthn whitepapers published by Yubico. For an introduction to WebAuthn and why it is both more secure and easier to use, see the first paper, Introducing WebAuthn: Enabling a Streamlined and More Secure User Authentication Experience. Most websites, services, and applications have difficulty providing secure, convenient authentication for users. Passwords are the problem. They tend to be either so simple they are easily guessed by hackers or so complex they are hard for users to remember. And all passwords, regardless of their complexity, are vulnerable to phishing and data breaches. Fortunately, WebAuthn, a new web authentication standard approved in March 2019 by the World Wide Web Consortium (W3C), makes it easy for websites, services, and applications to offer strong authenti- cation without relying on passwords. By replacing passwords with strong authentication based on public key cryptography, in which the private key never leaves the user’s device, WebAuthn makes authentication both easier to use and more secure, benefitting users and service providers alike. The WebAuthn standard is already supported by all major browsers and most platforms including: ● Windows 10 ● Android ● Google Chrome ● Mozilla Firefox ● Microsoft Edge ● Apple Safari ● Apple iOS WebAuthn supports various models for account authentication, leveraging both external roaming authenticators, such as hardware security keys, and authenticators built into computing and mobile devices, such as fingerprint readers and facial recognition technology. Applications and web services can choose to implement WebAuthn for passwordless authentication, two-factor authentication (2FA), and multi-factor authentication (MFA). -

A Tale of Two Studies: the Best and Worst of Yubikey Usability
2018 IEEE Symposium on Security and Privacy A Tale of Two Studies: The Best and Worst of YubiKey Usability †∗ ∗ ∗ ∗ ‡ ∗ Joshua Reynolds , Trevor Smith , Ken Reese , Luke Dickinson , Scott Ruoti , Kent Seamons † ∗ ‡ University of Illinois at Urbana-Champaign, Brigham Young University, MIT Lincoln Laboratory [email protected], {tsmith, ken.reese, luke}@isrl.byu.edu, [email protected], [email protected] Abstract—Two-factor authentication (2FA) significantly device that authenticates the user after the user presses a improves the security of password-based authentication. button on the security key [8]. The button tap is a test of Recently, there has been increased interest in Universal 2nd user presence and prevents malware on the host device from Factor (U2F) security keys—small hardware devices that require users to press a button on the security key to authenticate. To using the security key surreptitiously. Most commonly, security examine the usability of security keys in non-enterprise usage, keys are designed to be plugged into a USB port, though we conducted two user studies of the YubiKey, a popular line they can also communicate with other devices using wireless of U2F security keys. The first study tasked 31 participants protocols (e.g., NFC, Bluetooth). with configuring a Windows, Google, and Facebook account to U2F security keys are designed to be easy-to-adopt and authenticate using a YubiKey. This study revealed problems with setup instructions and workflow including users locking use in day-to-day life, while protecting users against phishing themselves out of their operating system or thinking they had and man-in-the-middle attacks [8]. -

Songs by Artist
Sound Master Entertianment Songs by Artist smedenver.com Title Title Title .38 Special 2Pac 4 Him Caught Up In You California Love (Original Version) For Future Generations Hold On Loosely Changes 4 Non Blondes If I'd Been The One Dear Mama What's Up Rockin' Onto The Night Thugz Mansion 4 P.M. Second Chance Until The End Of Time Lay Down Your Love Wild Eyed Southern Boys 2Pac & Eminem Sukiyaki 10 Years One Day At A Time 4 Runner Beautiful 2Pac & Notorious B.I.G. Cain's Blood Through The Iris Runnin' Ripples 100 Proof Aged In Soul 3 Doors Down That Was Him (This Is Now) Somebody's Been Sleeping Away From The Sun 4 Seasons 10000 Maniacs Be Like That Rag Doll Because The Night Citizen Soldier 42nd Street Candy Everybody Wants Duck & Run 42nd Street More Than This Here Without You Lullaby Of Broadway These Are Days It's Not My Time We're In The Money Trouble Me Kryptonite 5 Stairsteps 10CC Landing In London Ooh Child Let Me Be Myself I'm Not In Love 50 Cent We Do For Love Let Me Go 21 Questions 112 Loser Disco Inferno Come See Me Road I'm On When I'm Gone In Da Club Dance With Me P.I.M.P. It's Over Now When You're Young 3 Of Hearts Wanksta Only You What Up Gangsta Arizona Rain Peaches & Cream Window Shopper Love Is Enough Right Here For You 50 Cent & Eminem 112 & Ludacris 30 Seconds To Mars Patiently Waiting Kill Hot & Wet 50 Cent & Nate Dogg 112 & Super Cat 311 21 Questions All Mixed Up Na Na Na 50 Cent & Olivia 12 Gauge Amber Beyond The Grey Sky Best Friend Dunkie Butt 5th Dimension 12 Stones Creatures (For A While) Down Aquarius (Let The Sun Shine In) Far Away First Straw AquariusLet The Sun Shine In 1910 Fruitgum Co. -

Understanding Everyday FIDO U2F Usability Through Device Comparison and Experience Sampling
Of Two Minds about Two-Factor: Understanding Everyday FIDO U2F Usability through Device Comparison and Experience Sampling Stéphane Ciolino Simon Parkin Paul Dunphy OneSpan Innovation Centre University College London OneSpan Innovation Centre & University College London [email protected] [email protected] [email protected] Abstract words and tokens) is widely recognized as an effective tech- Security keys are phishing-resistant two-factor authentica- nique to protect both corporate and personal online accounts tion (2FA) tokens based upon the FIDO Universal 2nd Factor against account hijacking threats. Indeed, there are already ex- (U2F) standard. Prior research on security keys has revealed amples of citizens being advised to use Two-Factor Authenti- intuitive usability concerns, but there are open challenges to cation (2FA) by government agencies (as in the UK [35]). The better understand user experiences with heterogeneous de- most common second factor is a One-Time Passcode (OTP) vices and to determine an optimal user experience for every- received via a text message to a mobile device [5]. While this day Web browsing. In this paper we contribute to the growing technique conveniently leverages pre-existing telecommuni- usable security literature on security keys through two user cations infrastructure and mobile devices that users already studies: (i) a lab-based study evaluating the first-time user ex- own, it is vulnerable to Person-In-The-Middle (PITM) at- perience of a cross-vendor set of security keys and SMS-based tacks [8, 23, 32], such as phishing attacks. Hardware-based one-time passcodes; (ii) a diary study, where we collected authentication tokens have historically been deployed for 2FA 643 entries detailing how participants accessed accounts and in closed user communities such as corporations, or for bank- experienced one particular security key over the period of ing customers, particularly in territories such as Europe. -

Songs by Artist
Songs by Artist Title Title (Hed) Planet Earth 2 Live Crew Bartender We Want Some Pussy Blackout 2 Pistols Other Side She Got It +44 You Know Me When Your Heart Stops Beating 20 Fingers 10 Years Short Dick Man Beautiful 21 Demands Through The Iris Give Me A Minute Wasteland 3 Doors Down 10,000 Maniacs Away From The Sun Because The Night Be Like That Candy Everybody Wants Behind Those Eyes More Than This Better Life, The These Are The Days Citizen Soldier Trouble Me Duck & Run 100 Proof Aged In Soul Every Time You Go Somebody's Been Sleeping Here By Me 10CC Here Without You I'm Not In Love It's Not My Time Things We Do For Love, The Kryptonite 112 Landing In London Come See Me Let Me Be Myself Cupid Let Me Go Dance With Me Live For Today Hot & Wet Loser It's Over Now Road I'm On, The Na Na Na So I Need You Peaches & Cream Train Right Here For You When I'm Gone U Already Know When You're Young 12 Gauge 3 Of Hearts Dunkie Butt Arizona Rain 12 Stones Love Is Enough Far Away 30 Seconds To Mars Way I Fell, The Closer To The Edge We Are One Kill, The 1910 Fruitgum Co. Kings And Queens 1, 2, 3 Red Light This Is War Simon Says Up In The Air (Explicit) 2 Chainz Yesterday Birthday Song (Explicit) 311 I'm Different (Explicit) All Mixed Up Spend It Amber 2 Live Crew Beyond The Grey Sky Doo Wah Diddy Creatures (For A While) Me So Horny Don't Tread On Me Song List Generator® Printed 5/12/2021 Page 1 of 334 Licensed to Chris Avis Songs by Artist Title Title 311 4Him First Straw Sacred Hideaway Hey You Where There Is Faith I'll Be Here Awhile Who You Are Love Song 5 Stairsteps, The You Wouldn't Believe O-O-H Child 38 Special 50 Cent Back Where You Belong 21 Questions Caught Up In You Baby By Me Hold On Loosely Best Friend If I'd Been The One Candy Shop Rockin' Into The Night Disco Inferno Second Chance Hustler's Ambition Teacher, Teacher If I Can't Wild-Eyed Southern Boys In Da Club 3LW Just A Lil' Bit I Do (Wanna Get Close To You) Outlaw No More (Baby I'ma Do Right) Outta Control Playas Gon' Play Outta Control (Remix Version) 3OH!3 P.I.M.P.