Alcatel-Lucent 1300 XMC R8.0.0.12 EXTERNAL RELEASE NOTES
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Strange Birth and Long Life of Unix - IEEE Spectrum Page 1 of 6
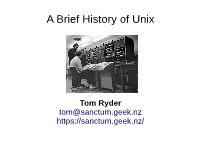
The Strange Birth and Long Life of Unix - IEEE Spectrum Page 1 of 6 COMPUTING / SOFTWARE FEATURE The Strange Birth and Long Life of Unix The classic operating system turns 40, and its progeny abound By WARREN TOOMEY / DECEMBER 2011 They say that when one door closes on you, another opens. People generally offer this bit of wisdom just to lend some solace after a misfortune. But sometimes it's actually true. It certainly was for Ken Thompson and the late Dennis Ritchie, two of the greats of 20th-century information technology, when they created the Unix operating system, now considered one of the most inspiring and influential pieces of software ever written. A door had slammed shut for Thompson and Ritchie in March of 1969, when their employer, the American Telephone & Telegraph Co., withdrew from a collaborative project with the Photo: Alcatel-Lucent Massachusetts Institute of KEY FIGURES: Ken Thompson [seated] types as Dennis Ritchie looks on in 1972, shortly Technology and General Electric after they and their Bell Labs colleagues invented Unix. to create an interactive time- sharing system called Multics, which stood for "Multiplexed Information and Computing Service." Time-sharing, a technique that lets multiple people use a single computer simultaneously, had been invented only a decade earlier. Multics was to combine time-sharing with other technological advances of the era, allowing users to phone a computer from remote terminals and then read e -mail, edit documents, run calculations, and so forth. It was to be a great leap forward from the way computers were mostly being used, with people tediously preparing and submitting batch jobs on punch cards to be run one by one. -

The Strange Birth and Long Life of Unix - IEEE Spectrum
The Strange Birth and Long Life of Unix - IEEE Spectrum http://spectrum.ieee.org/computing/software/the-strange-birth-and-long-li... COMPUTING / SOFTWARE FEATURE The Strange Birth and Long Life of Unix The classic operating system turns 40, and its progeny abound By WARREN TOOMEY / DECEMBER 2011 They say that when one door closes on you, another opens. People generally offer this bit of wisdom just to lend some solace after a misfortune. But sometimes it's actually true. It certainly was for Ken Thompson and the late Dennis Ritchie, two of the greats of 20th-century information technology, when they created the Unix operating system, now considered one of the most inspiring and influential pieces of software ever written. A door had slammed shut for Thompson and Ritchie in March of 1969, when their employer, the American Telephone & Telegraph Co., withdrew from a collaborative project with the Photo: Alcatel-Lucent Massachusetts Institute of KEY FIGURES: Ken Thompson [seated] types as Dennis Ritchie looks on in 1972, shortly Technology and General Electric after they and their Bell Labs colleagues invented Unix. to create an interactive time-sharing system called Multics, which stood for "Multiplexed Information and Computing Service." Time-sharing, a technique that lets multiple people use a single computer simultaneously, had been invented only a decade earlier. Multics was to combine time-sharing with other technological advances of the era, allowing users to phone a computer from remote terminals and then read e-mail, edit documents, run calculations, and so forth. It was to be a great leap forward from the way computers were mostly being used, with people tediously preparing and submitting batch jobs on punch cards to be run one by one. -

Introduction to UNIX What Is UNIX? Why UNIX? Brief History of UNIX Early UNIX History UNIX Variants
What is UNIX? A modern computer operating system Introduction to UNIX Operating system: “a program that acts as an intermediary between a user of the computer and the computer hardware” CS 2204 Software that manages your computer’s resources (files, programs, disks, network, …) Class meeting 1 e.g. Windows, MacOS Modern: features for stability, flexibility, multiple users and programs, configurability, etc. *Notes by Doug Bowman and other members of the CS faculty at Virginia Tech. Copyright 2001-2003. (C) Doug Bowman, Virginia Tech, 2001- 2 Why UNIX? Brief history of UNIX Used in many scientific and industrial settings Ken Thompson & Dennis Richie Huge number of free and well-written originally developed the earliest software programs versions of UNIX at Bell Labs for Open-source OS internal use in 1970s Internet servers and services run on UNIX Borrowed best ideas from other Oss Largely hardware-independent Meant for programmers and computer Based on standards experts Meant to run on “mini computers” (C) Doug Bowman, Virginia Tech, 2001- 3 (C) Doug Bowman, Virginia Tech, 2001- 4 Early UNIX History UNIX variants Thompson also rewrote the operating system Two main threads of development: in high level language of his own design Berkeley software distribution (BSD) which he called B. Unix System Laboratories System V Sun: SunOS, Solaris The B language lacked many features and Ritchie decided to design a successor to B GNU: Linux (many flavors) which he called C. SGI: Irix They then rewrote UNIX in the C FreeBSD programming language to aid in portability. Hewlett-Packard: HP-UX Apple: OS X (Darwin) … (C) Doug Bowman, Virginia Tech, 2001- 5 (C) Doug Bowman, Virginia Tech, 2001- 6 1 Layers in the UNIX System UNIX Structure User Interface The kernel is the core of the UNIX Library Interface Users system, controlling the system Standard Utility Programs hardware and performing various low- (shell, editors, compilers, etc.) System Interface calls User Mode level functions. -
LINCS Server Release 1.0 Administration
LINCS Server Release 1.0 Administration 585-313-507 Comcode 108599200 October 1999 Issue 2 Copyright © 1999 by Lucent Technologies. All rights reserved. For trademark, regulatory compliance, and related legal information, see the copyright and legal notices section of this document. Copyright and legal notices Copyright Copyright © 1999 by Lucent Technologies. All rights reserved. Printed in the USA. This material is protected by the copyright laws of the United States and other countries. It may not be reproduced, distributed, or altered in any fashion by any entity (either internal or external to Lucent Technologies), except in accordance with applicable agreements, contracts or licensing, without the express written consent of the Business Communications Systems (BCS) Global Learning Solutions organization and the business management owner of the material. Acknowledgment This document was prepared by the Global Learning Solutions organization of the BCS division of Lucent Technologies. Offices are located in Denver CO, Columbus OH, Middletown NJ, and Basking Ridge NJ, USA. LINCS Server Administration 585-313-507 Issue 2 October 1999 iii Copyright and legal notices Trademarks Lucent Technologies has made every effort to supply the following trademark information about company names, products, and services mentioned in the LINCS server documentation library: • Adobe Systems, Inc. — Trademarks: Adobe, Acrobat. • Enhanced Software Technologies, Inc. — Trademark: Quickstart. • Equinox Systems, Inc — Registered trademark: Equinox • Hewlett Packard Corporation — Registered trademarks: Hewlett-Packard and HP • Intel Corporation — Registered trademarks: Pentium. • International Business Machines Corporation — Registered trademarks: IBM, VTAM. • Lucent Technologies — Registered trademarks: 4ESS, 5ESS, AUDIX, CONVERSANT, DEFINITY, Voice Power. Trademarks: FlexWord, Intuity, Lucent. • Microsoft Corporation — Registered trademarks: Excel, Internet Explorer, Microsoft, MS, MS-DOS, Windows, Windows NT. -

Supply Chain Risk Management (SCRM) Task Force (TF) Threat Evaluation Working Group: Threat Scenarios, CISA, February 2020 TLP: WHITE
Appendix 1 Information And Communications Technology (ICT) Supply Chain Risk Management (SCRM) Task Force (TF) Threat Evaluation Working Group: Threat Scenarios, CISA, February 2020 TLP: WHITE CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY INFORMATION AND COMMUNICATIONS TECHNOLOGY SUPPLY CHAIN RISK MANAGEMENT TASK FORCE Threat Evaluation Working Group: Threat Scenarios February 2020 TLP: WHITE TLP: WHITE This page is intentionally left blank. CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY TLP: WHITE ii TLP: WHITE EXECUTIVE SUMMARY Cyber Supply Chain Risk Management (C-SCRM) is the process of identifying, assessing, preventing, and mitigating the risks associated with the distributed and interconnected nature of Information and Communications Technology (ICT) (including the Internet of Things) product and service supply chains. C-SCRM covers the entire life cycle of ICT, and encompasses hardware, software, and information assurance, along with traditional supply chain management and supply chain security considerations. In October 2018, the Cybersecurity and Infrastructure Security Agency (CISA) launched the ICT Supply Chain Risk Management Task Force, a public-private partnership to provide advice and recommendations to CISA and its stakeholders on means for assessing and managing risks associated with the ICT supply chain. Working Group 2 (WG2), Threat Evaluation, was established for the purpose of the identification of processes and criteria for threat-based evaluation of ICT suppliers, products, and services. WG2 focused on threat evaluation as opposed to the more comprehensive task of risk assessment which considers threats as well as an organization’s tolerance for risk, the criticality of the specific asset or business/mission purpose, and the impact of exploitation of specific vulnerabilities that might be exploited by an external threat. -
Avaya Definity ECS Whats New in R9.0.Pdf
DEFINITY® Enterprise Communications Server What’s New for Release 9 555-233-766 Issue 2 February 2001 Copyright 2001 Avaya Inc. All rights reserved. For trademark, regulatory compliance, and related legal information, see the copyright and legal notices section of this document. Copyright and legal notices Copyright Copyright 2001 by Avaya Inc. All rights reserved. This material is protected by the copyright laws of the United States and other countries. It may not be reproduced, distributed, or altered in any fashion by any entity (either internal or external to Avaya), except in accordance with applicable agreements, contracts or licensing, without the express written consent of the BCS Product Publications organization and the business management owner of the material. This document was prepared by the Product Publications department of the Business Communications Systems division of Avaya. Offices are located in Denver CO, Columbus OH, Middletown NJ, and Basking Ridge NJ, USA. DEFINITY ECS What’s New for Release 9 555-233-766 Issue 2 February 2001 iii Copyright and legal notices Trademarks DEFINITY, AUDIX, CONVERSANT, elemedia, SABLIME, Talkbak, Terranova, WaveLAN, MERLIN, MERLIN LEGEND and GuestWorks are registered trademarks and 4ESS, 5ESS, Intuity, OneMeeting, OneVision, PacketStar, PathStar, ProLogix, Lucent, Lucent Technologies, and the Lucent Technologies logo are trademarks of Lucent Technologies. Pentium is a registered trademark of Intel Corporation. Microsoft, Windows, and Windows NT are registered trademarks and Video for Windows is a trademark of Microsoft Corporation. UNIX is a registered trademark of UNIX System Laboratories, Inc., a wholly-owned subsidiary of Novell, Inc. X Window System is a trademark and product of the Massachusetts Institute of Technology. -
A Brief History of Unix
A Brief History of Unix Tom Ryder [email protected] https://sanctum.geek.nz/ I Love Unix ∴ I Love Linux ● When I started using Linux, I was impressed because of the ethics behind it. ● I loved the idea that an operating system could be both free to customise, and free of charge. – Being a cash-strapped student helped a lot, too. ● As my experience grew, I came to appreciate the design behind it. ● And the design is UNIX. ● Linux isn’t a perfect Unix, but it has all the really important bits. What do we actually mean? ● We’re referring to the Unix family of operating systems. – Unix from Bell Labs (Research Unix) – GNU/Linux – Berkeley Software Distribution (BSD) Unix – Mac OS X – Minix (Intel loves it) – ...and many more Warning signs: 1/2 If your operating system shows many of the following symptoms, it may be a Unix: – Multi-user, multi-tasking – Hierarchical filesystem, with a single root – Devices represented as files – Streams of text everywhere as a user interface – “Formatless” files ● Data is just data: streams of bytes saved in sequence ● There isn’t a “text file” attribute, for example Warning signs: 2/2 – Bourne-style shell with a “pipe”: ● $ program1 | program2 – “Shebangs” specifying file interpreters: ● #!/bin/sh – C programming language baked in everywhere – Classic programs: sh(1), awk(1), grep(1), sed(1) – Users with beards, long hair, glasses, and very strong opinions... Nobody saw it coming! “The number of Unix installations has grown to 10, with more expected.” — Ken Thompson and Dennis Ritchie (1972) ● Unix in some flavour is in servers, desktops, embedded software (including Intel’s management engine), mobile phones, network equipment, single-board computers.. -
Supplier, Products, and Services Threat Evaluation (To Include Impact Analysis and Mitigation) Version 3.0
CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY INFORMATION AND COMMUNICATIONS TECHNOLOGY SUPPLY CHAIN RISK MANAGEMENT TASK FORCE Threat Evaluation Working Group: Supplier, Products, and Services Threat Evaluation (to include Impact Analysis and Mitigation) Version 3.0 July 2021 This page is intentionally left blank. This latest report from the Threat Evaluation Working Group adds the assessment of Products and Executive Services to include impacts and mitigating controls to each of the Supplier Threat Scenarios Summary provided in the original version released in February 2020, and later augmented with impacts and mitigating controls in October 2020. These additional sections are included in Appendix C, Threat Scenarios, of this report. The Working Group (WG) chose to include these updates as a standalone report to benefit the audience without the need to include numerous references to the original reports. Cyber Supply Chain Risk Management (C-SCRM) is the process of identifying, assessing, preventing, and mitigating the risks associated with the distributed and interconnected nature of Information and Communications Technology (ICT) (including the Internet of Things [IoT]) product and service supply chains. C-SCRM covers the entire life cycle of ICT, and encompasses hardware, software, and information assurance, along with traditional supply chain management and supply chain security considerations. In October 2018, the Cybersecurity and Infrastructure Security Agency (CISA) launched the ICT Supply Chain Risk Management Task Force, a public-private partnership to provide advice and recommendations to CISA and its stakeholders on means for assessing and managing risks associated with the ICT supply chain. Working Group 2 (WG2), Threat Evaluation, was established for the purpose of the identification of processes and criteria for threat-based evaluation of ICT suppliers, products, and services. -

An Overview of the Netware Operating System
An Overview of the NetWare Operating System Drew Major Greg Minshall Kyle Powell Novell, Inc. Abstract The NetWare operating system is designed specifically to provide service to clients over a computer network. This design has resulted in a system that differs in several respects from more general-purpose operating systems. In addition to highlighting the design decisions that have led to these differences, this paper provides an overview of the NetWare operating system, with a detailed description of its kernel and its software-based approach to fault tolerance. 1. Introduction The NetWare operating system (NetWare OS) was originally designed in 1982-83 and has had a number of major changes over the intervening ten years, including converting the system from a Motorola 68000-based system to one based on the Intel 80x86 architecture. The most recent re-write of the NetWare OS, which occurred four years ago, resulted in an “open” system, in the sense of one in which independently developed programs could run. Major enhancements have occurred over the past two years, including the addition of an X.500-like directory system for the identification, location, and authentication of users and services. The philosophy has been to start as with as simple a design as possible and try to make it simpler as we gain experience and understand the problems better. The NetWare OS provides a reasonably complete runtime environment for programs ranging from multiprotocol routers to file servers to database servers to utility programs, and so forth. Because of the design tradeoffs made in the NetWare OS and the constraints those tradeoffs impose on the structure of programs developed to run on top of it, the NetWare OS is not suited to all applications. -

On the Feasibility of Providing Affordable Broadband Services
On the Feasibility of Providing Affordable Broadband Services using Backhaul in TV White Spaces Submitted in partial fulfillment of the requirements of the degrees of Master of Technology by Gaurang Naik Roll No. 123079009 Supervisors: Prof. Abhay Karandikar & Prof. Animesh Kumar DEPARTMENT OF ELECTRICAL ENGINEERING INDIAN INSTITUTE OF TECHNOLOGY BOMBAY JUNE, 2015 Approval Sheet This thesis entitled On the Feasibility of Providing Affordable Broadband Ser- vices using Backhaul in TV White Spaces by Gaurang Naik (Roll No. 123079009) is approved for the degree of Master of Technology in Communication and Signal Processing. Examiners Supervisors Chairperson Date: Place: Declaration I declare that this written submission represents my ideas in my own words and where others' ideas or words have been included, I have adequately cited and referenced the original sources. I also declare that I have adhered to all principles of academic honesty and integrity and have not misrepresented or fabricated or falsified any idea/data/fac- t/source in my submission. I understand that any violation of the above will be cause for disciplinary action by the Institute and can also evoke penal action from the sources which have thus not been properly cited or from whom proper permission has not been taken when needed. Gaurang Naik Date: Roll No: 123079009 To Amma & Anna Acknowledgements I would like to express my sincere gratitude to my supervisors, Prof. Abhay Karandikar and Prof. Animesh Kumar for the invaluable guidance they have provided over the last three years. The discussions I have had with them have helped me give a definite direc- tion to my thought process. -

MERLIN LEGEND Communications System Release 6.1 Installation
MERLIN LEGEND® Communications System Release 6.1 Installation 555-661-140 Comcode 108198029 Issue 1 August 1998 Copyright © 1998, Lucent Technologies 555-661-140 All Rights Reserved Issue 1 Printed in USA August 1998 Copyright © 1998, Lucent Technologies 555-661-140 All Rights Reserved Issue 1 Printed in USA August 1998 Notice Every effort was made to ensure that the information in this book was complete and accurate at the time of printing. However, information is subject to change. See Appendix A, “Customer Support Information,” for important information. It follows Maintenance and Troubleshooting in this binder. Your Responsibility for Your System’s Security Toll fraud is the unauthorized use of your telecommunications system by an unauthorized party, for example, persons other than your company’s employees, agents, subcontractors, or persons working on your company’s behalf. Note that there may be a risk of toll fraud associated with your telecommunications system, and if toll fraud occurs, it can result in substantial additional charges for your telecommunications services. You and your system manager are responsible for the security of your system, such as programming and configuring your equipment to prevent unauthorized use. The system manager is also responsible for reading all installation, instruction, and system administration documents provided with this product in order to fully understand the features that can introduce risk of toll fraud and the steps that can be taken to reduce that risk. Lucent Technologies does not warrant that this product is immune from or will prevent unauthorized use of common-carrier telecommunication services or facilities accessed through or connected to it. -
Applicationdec 433MP Software Installation Roadmap
dt applicationDEC 433MP Software Installation Roadmap Order Number: EK–PS100–SR–001 February 1991 This document is a guide to installing software on the applicationDEC 433MP system. The Roadmap addresses the following software products: • SCO UNIX • SCO Open Desktop • SCO MPX • SCO VP/ix • Digital PS1XG–AA graphics configuration utilities Digital Equipment Corporation Maynard, Massachusetts First Printing, February 1991 The information in this document is subject to change without notice and should not be construed as a commitment by Digital Equipment Corporation. Digital Equipment Corporation assumes no responsibility for any errors that may appear in this document. The software described in this document is furnished under a license and may be used or copied only in accordance with the terms of such license. No responsibility is assumed for the use or reliability of software on equipment that is not supplied by Digital Equipment Corporation or its affiliated companies. Restricted Rights: Use, duplication, or disclosure by the U.S. Government is subject to restrictions as set forth in subparagraph (c)(1)(ii) of the Rights in Technical Data and Computer Software clause at DFARS 252.227-7013. © Digital Equipment Corporation 1991. The following are trademarks of Digital Equipment Corporation: applicationDEC, DEC, VAX DOCUMENT, and the DIGITAL logo. The following are third-party trademarks: Intel is a trademark of Intel Corporation; MS-DOS is a registered trademark of Microsoft Corporation; NFS is a trademark of Sun Microsystems, Inc.; Open Desktop is a registered trademark of The Santa Cruz Operation, Inc.; OSF/Motif is a registered trademark of Open Software Foundation, Inc.; SCO is a registered trademark of The Santa Cruz Operation, Inc.; UNIX is a registered trademark of UNIX System Laboratories, Inc.; VP/ix is a registered trademark of VP/ix Joint Venture.