Avaya Definity ECS Whats New in R9.0.Pdf
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Strange Birth and Long Life of Unix - IEEE Spectrum Page 1 of 6
The Strange Birth and Long Life of Unix - IEEE Spectrum Page 1 of 6 COMPUTING / SOFTWARE FEATURE The Strange Birth and Long Life of Unix The classic operating system turns 40, and its progeny abound By WARREN TOOMEY / DECEMBER 2011 They say that when one door closes on you, another opens. People generally offer this bit of wisdom just to lend some solace after a misfortune. But sometimes it's actually true. It certainly was for Ken Thompson and the late Dennis Ritchie, two of the greats of 20th-century information technology, when they created the Unix operating system, now considered one of the most inspiring and influential pieces of software ever written. A door had slammed shut for Thompson and Ritchie in March of 1969, when their employer, the American Telephone & Telegraph Co., withdrew from a collaborative project with the Photo: Alcatel-Lucent Massachusetts Institute of KEY FIGURES: Ken Thompson [seated] types as Dennis Ritchie looks on in 1972, shortly Technology and General Electric after they and their Bell Labs colleagues invented Unix. to create an interactive time- sharing system called Multics, which stood for "Multiplexed Information and Computing Service." Time-sharing, a technique that lets multiple people use a single computer simultaneously, had been invented only a decade earlier. Multics was to combine time-sharing with other technological advances of the era, allowing users to phone a computer from remote terminals and then read e -mail, edit documents, run calculations, and so forth. It was to be a great leap forward from the way computers were mostly being used, with people tediously preparing and submitting batch jobs on punch cards to be run one by one. -

The Strange Birth and Long Life of Unix - IEEE Spectrum
The Strange Birth and Long Life of Unix - IEEE Spectrum http://spectrum.ieee.org/computing/software/the-strange-birth-and-long-li... COMPUTING / SOFTWARE FEATURE The Strange Birth and Long Life of Unix The classic operating system turns 40, and its progeny abound By WARREN TOOMEY / DECEMBER 2011 They say that when one door closes on you, another opens. People generally offer this bit of wisdom just to lend some solace after a misfortune. But sometimes it's actually true. It certainly was for Ken Thompson and the late Dennis Ritchie, two of the greats of 20th-century information technology, when they created the Unix operating system, now considered one of the most inspiring and influential pieces of software ever written. A door had slammed shut for Thompson and Ritchie in March of 1969, when their employer, the American Telephone & Telegraph Co., withdrew from a collaborative project with the Photo: Alcatel-Lucent Massachusetts Institute of KEY FIGURES: Ken Thompson [seated] types as Dennis Ritchie looks on in 1972, shortly Technology and General Electric after they and their Bell Labs colleagues invented Unix. to create an interactive time-sharing system called Multics, which stood for "Multiplexed Information and Computing Service." Time-sharing, a technique that lets multiple people use a single computer simultaneously, had been invented only a decade earlier. Multics was to combine time-sharing with other technological advances of the era, allowing users to phone a computer from remote terminals and then read e-mail, edit documents, run calculations, and so forth. It was to be a great leap forward from the way computers were mostly being used, with people tediously preparing and submitting batch jobs on punch cards to be run one by one. -
Avaya 1120E IP Deskphone User Guide
Avaya 1120E IP Deskphone User Guide Avaya Communication Server 1000 Document Status: Standard Document Version: 07.02 Part Code: NN43112-103 Date: March 2013 Licenses THE SOFTWARE LICENSE TERMS AVAILABLE ON © 2013 Avaya Inc. All Rights Reserved. THE AVAYA WEBSITE, HTTP:// Notice SUPPORT.AVAYA.COM/LICENSEINFO ARE APPLICABLE TO ANYONE WHO DOWNLOADS, While reasonable efforts have been made to ensure USES AND/OR INSTALLS AVAYA SOFTWARE, that the information in this document is complete and PURCHASED FROM AVAYA INC., ANY AVAYA accurate at the time of printing, Avaya assumes no AFFILIATE, OR AN AUTHORIZED AVAYA liability for any errors. Avaya reserves the right to RESELLER (AS APPLICABLE) UNDER A make changes and corrections to the information in COMMERCIAL AGREEMENT WITH AVAYA OR AN this document without the obligation to notify any AUTHORIZED AVAYA RESELLER. UNLESS person or organization of such changes. OTHERWISE AGREED TO BY AVAYA IN WRITING, Documentation disclaimer AVAYA DOES NOT EXTEND THIS LICENSE IF THE SOFTWARE WAS OBTAINED FROM ANYONE “Documentation” means information published by OTHER THAN AVAYA, AN AVAYA AFFILIATE OR AN Avaya in varying mediums which may include product AVAYA AUTHORIZED RESELLER; AVAYA information, operating instructions and performance RESERVES THE RIGHT TO TAKE LEGAL ACTION specifications that Avaya generally makes available to AGAINST YOU AND ANYONE ELSE USING OR users of its products. Documentation does not include SELLING THE SOFTWARE WITHOUT A LICENSE. marketing materials. Avaya shall not be responsible BY INSTALLING, DOWNLOADING OR USING THE for any modifications, additions, or deletions to the SOFTWARE, OR AUTHORIZING OTHERS TO DO original published version of documentation unless SO, YOU, ON BEHALF OF YOURSELF AND THE such modifications, additions, or deletions were ENTITY FOR WHOM YOU ARE INSTALLING, performed by Avaya. -

Introduction to UNIX What Is UNIX? Why UNIX? Brief History of UNIX Early UNIX History UNIX Variants
What is UNIX? A modern computer operating system Introduction to UNIX Operating system: “a program that acts as an intermediary between a user of the computer and the computer hardware” CS 2204 Software that manages your computer’s resources (files, programs, disks, network, …) Class meeting 1 e.g. Windows, MacOS Modern: features for stability, flexibility, multiple users and programs, configurability, etc. *Notes by Doug Bowman and other members of the CS faculty at Virginia Tech. Copyright 2001-2003. (C) Doug Bowman, Virginia Tech, 2001- 2 Why UNIX? Brief history of UNIX Used in many scientific and industrial settings Ken Thompson & Dennis Richie Huge number of free and well-written originally developed the earliest software programs versions of UNIX at Bell Labs for Open-source OS internal use in 1970s Internet servers and services run on UNIX Borrowed best ideas from other Oss Largely hardware-independent Meant for programmers and computer Based on standards experts Meant to run on “mini computers” (C) Doug Bowman, Virginia Tech, 2001- 3 (C) Doug Bowman, Virginia Tech, 2001- 4 Early UNIX History UNIX variants Thompson also rewrote the operating system Two main threads of development: in high level language of his own design Berkeley software distribution (BSD) which he called B. Unix System Laboratories System V Sun: SunOS, Solaris The B language lacked many features and Ritchie decided to design a successor to B GNU: Linux (many flavors) which he called C. SGI: Irix They then rewrote UNIX in the C FreeBSD programming language to aid in portability. Hewlett-Packard: HP-UX Apple: OS X (Darwin) … (C) Doug Bowman, Virginia Tech, 2001- 5 (C) Doug Bowman, Virginia Tech, 2001- 6 1 Layers in the UNIX System UNIX Structure User Interface The kernel is the core of the UNIX Library Interface Users system, controlling the system Standard Utility Programs hardware and performing various low- (shell, editors, compilers, etc.) System Interface calls User Mode level functions. -
LINCS Server Release 1.0 Administration
LINCS Server Release 1.0 Administration 585-313-507 Comcode 108599200 October 1999 Issue 2 Copyright © 1999 by Lucent Technologies. All rights reserved. For trademark, regulatory compliance, and related legal information, see the copyright and legal notices section of this document. Copyright and legal notices Copyright Copyright © 1999 by Lucent Technologies. All rights reserved. Printed in the USA. This material is protected by the copyright laws of the United States and other countries. It may not be reproduced, distributed, or altered in any fashion by any entity (either internal or external to Lucent Technologies), except in accordance with applicable agreements, contracts or licensing, without the express written consent of the Business Communications Systems (BCS) Global Learning Solutions organization and the business management owner of the material. Acknowledgment This document was prepared by the Global Learning Solutions organization of the BCS division of Lucent Technologies. Offices are located in Denver CO, Columbus OH, Middletown NJ, and Basking Ridge NJ, USA. LINCS Server Administration 585-313-507 Issue 2 October 1999 iii Copyright and legal notices Trademarks Lucent Technologies has made every effort to supply the following trademark information about company names, products, and services mentioned in the LINCS server documentation library: • Adobe Systems, Inc. — Trademarks: Adobe, Acrobat. • Enhanced Software Technologies, Inc. — Trademark: Quickstart. • Equinox Systems, Inc — Registered trademark: Equinox • Hewlett Packard Corporation — Registered trademarks: Hewlett-Packard and HP • Intel Corporation — Registered trademarks: Pentium. • International Business Machines Corporation — Registered trademarks: IBM, VTAM. • Lucent Technologies — Registered trademarks: 4ESS, 5ESS, AUDIX, CONVERSANT, DEFINITY, Voice Power. Trademarks: FlexWord, Intuity, Lucent. • Microsoft Corporation — Registered trademarks: Excel, Internet Explorer, Microsoft, MS, MS-DOS, Windows, Windows NT. -

Supply Chain Risk Management (SCRM) Task Force (TF) Threat Evaluation Working Group: Threat Scenarios, CISA, February 2020 TLP: WHITE
Appendix 1 Information And Communications Technology (ICT) Supply Chain Risk Management (SCRM) Task Force (TF) Threat Evaluation Working Group: Threat Scenarios, CISA, February 2020 TLP: WHITE CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY INFORMATION AND COMMUNICATIONS TECHNOLOGY SUPPLY CHAIN RISK MANAGEMENT TASK FORCE Threat Evaluation Working Group: Threat Scenarios February 2020 TLP: WHITE TLP: WHITE This page is intentionally left blank. CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY TLP: WHITE ii TLP: WHITE EXECUTIVE SUMMARY Cyber Supply Chain Risk Management (C-SCRM) is the process of identifying, assessing, preventing, and mitigating the risks associated with the distributed and interconnected nature of Information and Communications Technology (ICT) (including the Internet of Things) product and service supply chains. C-SCRM covers the entire life cycle of ICT, and encompasses hardware, software, and information assurance, along with traditional supply chain management and supply chain security considerations. In October 2018, the Cybersecurity and Infrastructure Security Agency (CISA) launched the ICT Supply Chain Risk Management Task Force, a public-private partnership to provide advice and recommendations to CISA and its stakeholders on means for assessing and managing risks associated with the ICT supply chain. Working Group 2 (WG2), Threat Evaluation, was established for the purpose of the identification of processes and criteria for threat-based evaluation of ICT suppliers, products, and services. WG2 focused on threat evaluation as opposed to the more comprehensive task of risk assessment which considers threats as well as an organization’s tolerance for risk, the criticality of the specific asset or business/mission purpose, and the impact of exploitation of specific vulnerabilities that might be exploited by an external threat. -

Federal Communications Commission FCC 15-35 Before the Federal
Federal Communications Commission FCC 15-35 Before the Federal Communications Commission Washington, D.C. 20554 In the Matters of ) ) Telcordia Technologies, Inc. Petition to Reform ) WC Docket No. 07-149 Amendment 57 and to Order a Competitive ) Bidding Process for Number Portability ) Administration ) ) Petition of Telcordia Technologies, Inc. to Reform ) WC Docket No. 09-109 or Strike Amendment 70, to Institute Competitive ) Bidding for Number Portability ) Administration, and to End the NAPM LLC’s ) Interim Role in Number Portability ) Administration Contract Management ) ) Telephone Number Portability ) CC Docket No. 95-116 ) ORDER Adopted: March 26, 2015 Released: March 27, 2015 By the Commission: Chairman Wheeler and Commissioners Clyburn and Pai issuing separate statements; Commissioner O’Rielly approving in part, concurring in part, and issuing a statement. TABLE OF CONTENTS Heading Paragraph # I. INTRODUCTION .................................................................................................................................. 1 II. BACKGROUND .................................................................................................................................... 4 A. First LNPA Selection ....................................................................................................................... 5 B. Current LNPA Selection .................................................................................................................. 8 III. DISCUSSION ..................................................................................................................................... -

DEFINITY ECS Network Call Redirection
'(),1,7< (QWHUSULVH&RPPXQLFDWLRQV6HUYHU Network Call Redirection 555-233-759 Comcode 700156342 Issue 2.0 July 2001 Copyright 2001, Avaya Inc. To prevent intrusions to your telecommunications equipment, you and All Rights Reserved, Printed in U.S.A. your peers should carefully program and configure your: Notice • Lucent-provided telecommunications systems and their interfaces Every effort was made to ensure that the information in this book was com- • Lucent-provided software applications, as well as their underlying plete and accurate at the time of printing. However, information is subject hardware/software platforms and interfaces to change. • Any other equipment networked to your Lucent products Avaya Inc. Web Page Avaya Inc. does not warrant that this product or any of its networked equip- The world wide web home page for Avaya Inc. is: ment is either immune from or will prevent either unauthorized or mali- http://www.avaya.com cious intrusions. Avaya Inc.Avaya Inc. will not be responsible for any Preventing Toll Fraud charges, losses, or damages that result from such intrusions. “Toll fraud” is the unauthorized use of your telecommunications system by Federal Communications Commission Statement an unauthorized party (for example, a person who is not a corporate Part 15: Class A Statement. This equipment has been tested and found to employee, agent, subcontractor, or working on your company’s behalf). Be comply with the limits for a Class A digital device, pursuant to Part 15 of aware that there may be a risk of toll fraud associated with your system and the FCC Rules. These limits are designed to provide reasonable protection that, if toll fraud occurs, it can result in substantial additional charges for against harmful interference when the equipment is operated in a commer- your telecommunications services. -
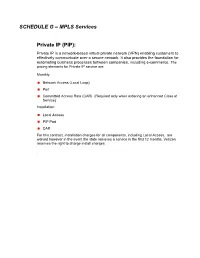
SCHEDULE G – MPLS Services Private IP (PIP)
SCHEDULE G – MPLS Services Private IP (PIP): Private IP is a network-based virtual private network (VPN) enabling customers to effectively communicate over a secure network. It also provides the foundation for automating business processes between companies, including e-commerce, The pricing elements for Private IP service are: Monthly: Network Access (Local Loop) Port Committed Access Rate (CAR) (Required only when ordering an enhanced Class of Service) Installation: Local Access PIP Port CAR For this contract, installation charges for all components, including Local Access, are waived however in the event the state removes a service in the first 12 months, Verizon reserves the right to charge install charges. Private IP Service Local Access pricing is as per the table in Schedule F2 INSTALLATION WAIVER Verizon will not charge Installation up front. If the State disconnects the service prior to 12 months, Verizon reserves the right to charge the standard installtion fee. This applies to PIP Ports only. Features and Optional services are not included PORT CHARGES Port Speed MRC NRC Port Speed MRC NRC 64 Kbps $ 36.75 $ 50.00 600M Sub-Rate OC12 $ 8,433.81 $ 600.00 256 Kbps $ 78.33 $ 100.00 1M Ethernet $ 162.12 $ 600.00 512 Kbps $ 123.69 $ 100.00 2M Ethernet $ 124.00 $ 600.00 1.024 Mbps $ 162.12 $ 100.00 3M Ethernet $ 149.00 $ 600.00 T1 $ 155.00 $ 200.00 4M Ethernet $ 175.00 $ 600.00 3.072 Mbps $ 269.00 $ 600.00 6M Ethernet $ 229.00 $ 600.00 4.608 Mbps $ 350.00 $ 600.00 8M Ethernet $ 268.00 $ 600.00 6.144 Mbps $ 402.00 $ 600.00 10M -
A Brief History of Unix
A Brief History of Unix Tom Ryder [email protected] https://sanctum.geek.nz/ I Love Unix ∴ I Love Linux ● When I started using Linux, I was impressed because of the ethics behind it. ● I loved the idea that an operating system could be both free to customise, and free of charge. – Being a cash-strapped student helped a lot, too. ● As my experience grew, I came to appreciate the design behind it. ● And the design is UNIX. ● Linux isn’t a perfect Unix, but it has all the really important bits. What do we actually mean? ● We’re referring to the Unix family of operating systems. – Unix from Bell Labs (Research Unix) – GNU/Linux – Berkeley Software Distribution (BSD) Unix – Mac OS X – Minix (Intel loves it) – ...and many more Warning signs: 1/2 If your operating system shows many of the following symptoms, it may be a Unix: – Multi-user, multi-tasking – Hierarchical filesystem, with a single root – Devices represented as files – Streams of text everywhere as a user interface – “Formatless” files ● Data is just data: streams of bytes saved in sequence ● There isn’t a “text file” attribute, for example Warning signs: 2/2 – Bourne-style shell with a “pipe”: ● $ program1 | program2 – “Shebangs” specifying file interpreters: ● #!/bin/sh – C programming language baked in everywhere – Classic programs: sh(1), awk(1), grep(1), sed(1) – Users with beards, long hair, glasses, and very strong opinions... Nobody saw it coming! “The number of Unix installations has grown to 10, with more expected.” — Ken Thompson and Dennis Ritchie (1972) ● Unix in some flavour is in servers, desktops, embedded software (including Intel’s management engine), mobile phones, network equipment, single-board computers.. -

Matching Gift Programs * Please Note, This List Is Not All Inclusive
Companies With Matching Gift Programs * Please note, this list is not all inclusive. If your employer is not listed, please check with human resources to see if your company matches and the guidelines for matches. A AlliedSignal Inc. Archer Daniels Midland 3Com Corporation Allstate Foundation, Allstate Giving ARCO Chemical Co. 3M Company Altera Corp. Contributions Program Ares Advanced Technology AAA Altria Employee Involvement Ares Management LLC Abacus Capital Investments Altria Group Argonaut Group Inc. Abbot Laboratories AMB Group Aristokraft Inc. Accenture Foundation, Inc. Ambac Arkansas Best Corporation Access Group, Inc. AMD Corporate Giving Arkwright Mutual Insurance Co. ACE INA Foundation American Express Co. Armco Inc. Acsiom Corp. American Express Foundation Armstrong Foundation Adams Harkness and Hill Inc. American Fidelity Corp. Arrow Electronics Adaptec Foundation American General Corp. Arthur J. Gallagher ADC Foundation American Honda Motor Co. Inc. Ashland Oil Foundation, Inc. ADC Telecommunications American Inter Group Aspect Global Giving Program Adobe Systems Inc. American International Group, Inc. Aspect Telecommunications Associates ADP Foundation American National Bank and Trust Co. Corp. of North America A & E Television Networks of Chicago Assurant Health AEGON TRANSAMERICA American Standard Foundation Astra Merck Inc. AEP American Stock Exchange AstraZeneca Pharmaceutical LP AES Corporation Ameriprise Financial Atapco A.E. Staley Manufacturing Co. Ameritech Corp. ATK Foundation Aetna Foundation, Inc. Amgen Center Atlantic Data Services Inc. AG Communications Systems Amgen Foundation Atochem North America Foundation Agilent Technologies Amgen Inc. ATOFINA Chemicals, Inc. Aid Association for Lutherans AMN Healthcare Services, Inc. ATO FINA Pharmaceutical Foundation AIG Matching Grants Program Corporate Giving Program AT&T Aileen S. Andrew Foundation AmSouth BanCorp. -
Supplier, Products, and Services Threat Evaluation (To Include Impact Analysis and Mitigation) Version 3.0
CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY INFORMATION AND COMMUNICATIONS TECHNOLOGY SUPPLY CHAIN RISK MANAGEMENT TASK FORCE Threat Evaluation Working Group: Supplier, Products, and Services Threat Evaluation (to include Impact Analysis and Mitigation) Version 3.0 July 2021 This page is intentionally left blank. This latest report from the Threat Evaluation Working Group adds the assessment of Products and Executive Services to include impacts and mitigating controls to each of the Supplier Threat Scenarios Summary provided in the original version released in February 2020, and later augmented with impacts and mitigating controls in October 2020. These additional sections are included in Appendix C, Threat Scenarios, of this report. The Working Group (WG) chose to include these updates as a standalone report to benefit the audience without the need to include numerous references to the original reports. Cyber Supply Chain Risk Management (C-SCRM) is the process of identifying, assessing, preventing, and mitigating the risks associated with the distributed and interconnected nature of Information and Communications Technology (ICT) (including the Internet of Things [IoT]) product and service supply chains. C-SCRM covers the entire life cycle of ICT, and encompasses hardware, software, and information assurance, along with traditional supply chain management and supply chain security considerations. In October 2018, the Cybersecurity and Infrastructure Security Agency (CISA) launched the ICT Supply Chain Risk Management Task Force, a public-private partnership to provide advice and recommendations to CISA and its stakeholders on means for assessing and managing risks associated with the ICT supply chain. Working Group 2 (WG2), Threat Evaluation, was established for the purpose of the identification of processes and criteria for threat-based evaluation of ICT suppliers, products, and services.