1 Measurable Sets
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

A Class of Symmetric Difference-Closed Sets Related to Commuting Involutions John Campbell
A class of symmetric difference-closed sets related to commuting involutions John Campbell To cite this version: John Campbell. A class of symmetric difference-closed sets related to commuting involutions. Discrete Mathematics and Theoretical Computer Science, DMTCS, 2017, Vol 19 no. 1. hal-01345066v4 HAL Id: hal-01345066 https://hal.archives-ouvertes.fr/hal-01345066v4 Submitted on 18 Mar 2017 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. Discrete Mathematics and Theoretical Computer Science DMTCS vol. 19:1, 2017, #8 A class of symmetric difference-closed sets related to commuting involutions John M. Campbell York University, Canada received 19th July 2016, revised 15th Dec. 2016, 1st Feb. 2017, accepted 10th Feb. 2017. Recent research on the combinatorics of finite sets has explored the structure of symmetric difference-closed sets, and recent research in combinatorial group theory has concerned the enumeration of commuting involutions in Sn and An. In this article, we consider an interesting combination of these two subjects, by introducing classes of symmetric difference-closed sets of elements which correspond in a natural way to commuting involutions in Sn and An. We consider the natural combinatorial problem of enumerating symmetric difference-closed sets consisting of subsets of sets consisting of pairwise disjoint 2-subsets of [n], and the problem of enumerating symmetric difference-closed sets consisting of elements which correspond to commuting involutions in An. -

Fast and Private Computation of Cardinality of Set Intersection and Union
Fast and Private Computation of Cardinality of Set Intersection and Union Emiliano De Cristofaroy, Paolo Gastiz, and Gene Tsudikz yPARC zUC Irvine Abstract. With massive amounts of electronic information stored, trans- ferred, and shared every day, legitimate needs for sensitive information must be reconciled with natural privacy concerns. This motivates var- ious cryptographic techniques for privacy-preserving information shar- ing, such as Private Set Intersection (PSI) and Private Set Union (PSU). Such techniques involve two parties { client and server { each with a private input set. At the end, client learns the intersection (or union) of the two respective sets, while server learns nothing. However, if desired functionality is private computation of cardinality rather than contents, of set intersection, PSI and PSU protocols are not appropriate, as they yield too much information. In this paper, we design an efficient crypto- graphic protocol for Private Set Intersection Cardinality (PSI-CA) that yields only the size of set intersection, with security in the presence of both semi-honest and malicious adversaries. To the best of our knowl- edge, it is the first protocol that achieves complexities linear in the size of input sets. We then show how the same protocol can be used to pri- vately compute set union cardinality. We also design an extension that supports authorization of client input. 1 Introduction Proliferation of, and growing reliance on, electronic information trigger the increase in the amount of sensitive data stored and processed in cyberspace. Consequently, there is a strong need for efficient cryptographic techniques that allow sharing information with privacy. Among these, Private Set Intersection (PSI) [11, 24, 14, 21, 15, 22, 9, 8, 18], and Private Set Union (PSU) [24, 15, 17, 12, 32] have attracted a lot of attention from the research community. -

Julia's Efficient Algorithm for Subtyping Unions and Covariant
Julia’s Efficient Algorithm for Subtyping Unions and Covariant Tuples Benjamin Chung Northeastern University, Boston, MA, USA [email protected] Francesco Zappa Nardelli Inria of Paris, Paris, France [email protected] Jan Vitek Northeastern University, Boston, MA, USA Czech Technical University in Prague, Czech Republic [email protected] Abstract The Julia programming language supports multiple dispatch and provides a rich type annotation language to specify method applicability. When multiple methods are applicable for a given call, Julia relies on subtyping between method signatures to pick the correct method to invoke. Julia’s subtyping algorithm is surprisingly complex, and determining whether it is correct remains an open question. In this paper, we focus on one piece of this problem: the interaction between union types and covariant tuples. Previous work normalized unions inside tuples to disjunctive normal form. However, this strategy has two drawbacks: complex type signatures induce space explosion, and interference between normalization and other features of Julia’s type system. In this paper, we describe the algorithm that Julia uses to compute subtyping between tuples and unions – an algorithm that is immune to space explosion and plays well with other features of the language. We prove this algorithm correct and complete against a semantic-subtyping denotational model in Coq. 2012 ACM Subject Classification Theory of computation → Type theory Keywords and phrases Type systems, Subtyping, Union types Digital Object Identifier 10.4230/LIPIcs.ECOOP.2019.24 Category Pearl Supplement Material ECOOP 2019 Artifact Evaluation approved artifact available at https://dx.doi.org/10.4230/DARTS.5.2.8 Acknowledgements The authors thank Jiahao Chen for starting us down the path of understanding Julia, and Jeff Bezanson for coming up with Julia’s subtyping algorithm. -
Naïve Set Theory Basic Definitions Naïve Set Theory Is the Non-Axiomatic Treatment of Set Theory
Naïve Set Theory Basic Definitions Naïve set theory is the non-axiomatic treatment of set theory. In the axiomatic treatment, which we will only allude to at times, a set is an undefined term. For us however, a set will be thought of as a collection of some (possibly none) objects. These objects are called the members (or elements) of the set. We use the symbol "∈" to indicate membership in a set. Thus, if A is a set and x is one of its members, we write x ∈ A and say "x is an element of A" or "x is in A" or "x is a member of A". Note that "∈" is not the same as the Greek letter "ε" epsilon. Basic Definitions Sets can be described notationally in many ways, but always using the set brackets "{" and "}". If possible, one can just list the elements of the set: A = {1,3, oranges, lions, an old wad of gum} or give an indication of the elements: ℕ = {1,2,3, ... } ℤ = {..., -2,-1,0,1,2, ...} or (most frequently in mathematics) using set-builder notation: S = {x ∈ ℝ | 1 < x ≤ 7 } or {x ∈ ℝ : 1 < x ≤ 7 } which is read as "S is the set of real numbers x, such that x is greater than 1 and less than or equal to 7". In some areas of mathematics sets may be denoted by special notations. For instance, in analysis S would be written (1,7]. Basic Definitions Note that sets do not contain repeated elements. An element is either in or not in a set, never "in the set 5 times" for instance. -

Fast and Private Computation of Cardinality of Set Intersection and Union*
Fast and Private Computation of Cardinality of Set Intersection and Union* Emiliano De Cristofaroy, Paolo Gastiz, Gene Tsudikz yPARC zUC Irvine Abstract In many everyday scenarios, sensitive information must be shared between parties without com- plete mutual trust. Private set operations are particularly useful to enable sharing information with privacy, as they allow two or more parties to jointly compute operations on their sets (e.g., intersec- tion, union, etc.), such that only the minimum required amount of information is disclosed. In the last few years, the research community has proposed a number of secure and efficient techniques for Private Set Intersection (PSI), however, somewhat less explored is the problem of computing the magnitude, rather than the contents, of the intersection – we denote this problem as Private Set In- tersection Cardinality (PSI-CA). This paper explores a few PSI-CA variations and constructs several protocols that are more efficient than the state-of-the-art. 1 Introduction Proliferation of, and growing reliance on, electronic information generate an increasing amount of sensitive data stored and processed in the cyberspace. Consequently, there is a compelling need for efficient cryptographic techniques that allow sharing information while protecting privacy. Among these, Private Set Intersection (PSI) [15, 29, 18, 26, 19, 27, 12, 11, 22], and Private Set Union (PSU) [29, 19, 21, 16, 36] have recently attracted a lot of attention from the research community. In particular, PSI allows one party (client) to compute the intersection of its set with that of another party (server), such that: (i) server does not learn client input, and (ii) client learns no information about server input, beyond the intersection. -
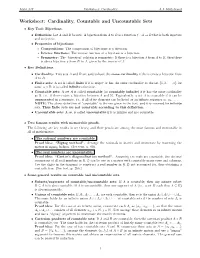
Worksheet: Cardinality, Countable and Uncountable Sets
Math 347 Worksheet: Cardinality A.J. Hildebrand Worksheet: Cardinality, Countable and Uncountable Sets • Key Tool: Bijections. • Definition: Let A and B be sets. A bijection from A to B is a function f : A ! B that is both injective and surjective. • Properties of bijections: ∗ Compositions: The composition of bijections is a bijection. ∗ Inverse functions: The inverse function of a bijection is a bijection. ∗ Symmetry: The \bijection" relation is symmetric: If there is a bijection f from A to B, then there is also a bijection g from B to A, given by the inverse of f. • Key Definitions. • Cardinality: Two sets A and B are said to have the same cardinality if there exists a bijection from A to B. • Finite sets: A set is called finite if it is empty or has the same cardinality as the set f1; 2; : : : ; ng for some n 2 N; it is called infinite otherwise. • Countable sets: A set A is called countable (or countably infinite) if it has the same cardinality as N, i.e., if there exists a bijection between A and N. Equivalently, a set A is countable if it can be enumerated in a sequence, i.e., if all of its elements can be listed as an infinite sequence a1; a2;::: . NOTE: The above definition of \countable" is the one given in the text, and it is reserved for infinite sets. Thus finite sets are not countable according to this definition. • Uncountable sets: A set is called uncountable if it is infinite and not countable. • Two famous results with memorable proofs. -

Some Set Theory We Should Know Cardinality and Cardinal Numbers
SOME SET THEORY WE SHOULD KNOW CARDINALITY AND CARDINAL NUMBERS De¯nition. Two sets A and B are said to have the same cardinality, and we write jAj = jBj, if there exists a one-to-one onto function f : A ! B. We also say jAj · jBj if there exists a one-to-one (but not necessarily onto) function f : A ! B. Then the SchrÄoder-BernsteinTheorem says: jAj · jBj and jBj · jAj implies jAj = jBj: SchrÄoder-BernsteinTheorem. If there are one-to-one maps f : A ! B and g : B ! A, then jAj = jBj. A set is called countable if it is either ¯nite or has the same cardinality as the set N of positive integers. Theorem ST1. (a) A countable union of countable sets is countable; (b) If A1;A2; :::; An are countable, so is ¦i·nAi; (c) If A is countable, so is the set of all ¯nite subsets of A, as well as the set of all ¯nite sequences of elements of A; (d) The set Q of all rational numbers is countable. Theorem ST2. The following sets have the same cardinality as the set R of real numbers: (a) The set P(N) of all subsets of the natural numbers N; (b) The set of all functions f : N ! f0; 1g; (c) The set of all in¯nite sequences of 0's and 1's; (d) The set of all in¯nite sequences of real numbers. The cardinality of N (and any countable in¯nite set) is denoted by @0. @1 denotes the next in¯nite cardinal, @2 the next, etc. -

Regularity Properties and Determinacy
Regularity Properties and Determinacy MSc Thesis (Afstudeerscriptie) written by Yurii Khomskii (born September 5, 1980 in Moscow, Russia) under the supervision of Dr. Benedikt L¨owe, and submitted to the Board of Examiners in partial fulfillment of the requirements for the degree of MSc in Logic at the Universiteit van Amsterdam. Date of the public defense: Members of the Thesis Committee: August 14, 2007 Dr. Benedikt L¨owe Prof. Dr. Jouko V¨a¨an¨anen Prof. Dr. Joel David Hamkins Prof. Dr. Peter van Emde Boas Brian Semmes i Contents 0. Introduction............................ 1 1. Preliminaries ........................... 4 1.1 Notation. ........................... 4 1.2 The Real Numbers. ...................... 5 1.3 Trees. ............................. 6 1.4 The Forcing Notions. ..................... 7 2. ClasswiseConsequencesofDeterminacy . 11 2.1 Regularity Properties. .................... 11 2.2 Infinite Games. ........................ 14 2.3 Classwise Implications. .................... 16 3. The Marczewski-Burstin Algebra and the Baire Property . 20 3.1 MB and BP. ......................... 20 3.2 Fusion Sequences. ...................... 23 3.3 Counter-examples. ...................... 26 4. DeterminacyandtheBaireProperty.. 29 4.1 Generalized MB-algebras. .................. 29 4.2 Determinacy and BP(P). ................... 31 4.3 Determinacy and wBP(P). .................. 34 5. Determinacy andAsymmetric Properties. 39 5.1 The Asymmetric Properties. ................. 39 5.2 The General Definition of Asym(P). ............. 43 5.3 Determinacy and Asym(P). ................. 46 ii iii 0. Introduction One of the most intriguing developments of modern set theory is the investi- gation of two-player infinite games of perfect information. Of course, it is clear that applied game theory, as any other branch of mathematics, can be modeled in set theory. But we are talking about the converse: the use of infinite games as a tool to study fundamental set theoretic questions. -

06. Naive Set Theory I
Topics 06. Naive Set Theory I. Sets and Paradoxes of the Infinitely Big II. Naive Set Theory I. Sets and Paradoxes of the Infinitely Big III. Cantor and Diagonal Arguments Recall: Paradox of the Even Numbers Claim: There are just as many even natural numbers as natural numbers natural numbers = non-negative whole numbers (0, 1, 2, ..) Proof: { 0 , 1 , 2 , 3 , 4 , ............ , n , ..........} { 0 , 2 , 4 , 6 , 8 , ............ , 2n , ..........} In general: 2 criteria for comparing sizes of sets: (1) Correlation criterion: Can members of one set be paired with members of the other? (2) Subset criterion: Do members of one set belong to the other? Can now say: (a) There are as many even naturals as naturals in the correlation sense. (b) There are less even naturals than naturals in the subset sense. To talk about the infinitely Moral: notion of sets big, just need to be clear makes this clear about what’s meant by size Bolzano (1781-1848) Promoted idea that notion of infinity was fundamentally set-theoretic: To say something is infinite is “God is infinite in knowledge” just to say there is some set means with infinite members “The set of truths known by God has infinitely many members” SO: Are there infinite sets? “a many thought of as a one” -Cantor Bolzano: Claim: The set of truths is infinite. Proof: Let p1 be a truth (ex: “Plato was Greek”) Let p2 be the truth “p1 is a truth”. Let p3 be the truth “p3 is a truth”. In general, let pn be the truth “pn-1 is a truth”, for any natural number n. -
Session 5 – Main Theme
Database Systems Session 5 – Main Theme Relational Algebra, Relational Calculus, and SQL Dr. Jean-Claude Franchitti New York University Computer Science Department Courant Institute of Mathematical Sciences Presentation material partially based on textbook slides Fundamentals of Database Systems (6th Edition) by Ramez Elmasri and Shamkant Navathe Slides copyright © 2011 and on slides produced by Zvi Kedem copyight © 2014 1 Agenda 1 Session Overview 2 Relational Algebra and Relational Calculus 3 Relational Algebra Using SQL Syntax 5 Summary and Conclusion 2 Session Agenda . Session Overview . Relational Algebra and Relational Calculus . Relational Algebra Using SQL Syntax . Summary & Conclusion 3 What is the class about? . Course description and syllabus: » http://www.nyu.edu/classes/jcf/CSCI-GA.2433-001 » http://cs.nyu.edu/courses/fall11/CSCI-GA.2433-001/ . Textbooks: » Fundamentals of Database Systems (6th Edition) Ramez Elmasri and Shamkant Navathe Addition Wesley ISBN-10: 0-1360-8620-9, ISBN-13: 978-0136086208 6th Edition (04/10) 4 Icons / Metaphors Information Common Realization Knowledge/Competency Pattern Governance Alignment Solution Approach 55 Agenda 1 Session Overview 2 Relational Algebra and Relational Calculus 3 Relational Algebra Using SQL Syntax 5 Summary and Conclusion 6 Agenda . Unary Relational Operations: SELECT and PROJECT . Relational Algebra Operations from Set Theory . Binary Relational Operations: JOIN and DIVISION . Additional Relational Operations . Examples of Queries in Relational Algebra . The Tuple Relational Calculus . The Domain Relational Calculus 7 The Relational Algebra and Relational Calculus . Relational algebra . Basic set of operations for the relational model . Relational algebra expression . Sequence of relational algebra operations . Relational calculus . Higher-level declarative language for specifying relational queries 8 Unary Relational Operations: SELECT and PROJECT (1/3) . -

Understanding the New-Keynesian Model When Monetary Policy Switches Regimes
NBER WORKING PAPER SERIES UNDERSTANDING THE NEW-KEYNESIAN MODEL WHEN MONETARY POLICY SWITCHES REGIMES Roger E.A. Farmer Daniel F. Waggoner Tao Zha Working Paper 12965 http://www.nber.org/papers/w12965 NATIONAL BUREAU OF ECONOMIC RESEARCH 1050 Massachusetts Avenue Cambridge, MA 02138 March 2007 We thank Zheng Liu and Richard Rogerson for helpful discussions. The views expressed herein do not necessarily reflect those of the Federal Reserve Bank of Atlanta nor those of the Federal Reserve System. Farmer acknowledges the support of NSF grant SBR 0418174. The views expressed herein are those of the author(s) and do not necessarily reflect the views of the National Bureau of Economic Research. © 2007 by Roger E.A. Farmer, Daniel F. Waggoner, and Tao Zha. All rights reserved. Short sections of text, not to exceed two paragraphs, may be quoted without explicit permission provided that full credit, including © notice, is given to the source. Understanding the New-Keynesian Model when Monetary Policy Switches Regimes Roger E.A. Farmer, Daniel F. Waggoner, and Tao Zha NBER Working Paper No. 12965 March 2007 JEL No. E3,E5,E52 ABSTRACT This paper studies a New-Keynesian model in which monetary policy may switch between regimes. We derive sufficient conditions for indeterminacy that are easy to implement and we show that the necessary and sufficient condition for determinacy, provided by Davig and Leeper, is necessary but not sufficient. More importantly, we use a two-regime model to show that indeterminacy in a passive regime may spill over to an active regime, no matter how active the latter regime is. -

The Axiom of Choice
THE AXIOM OF CHOICE THOMAS J. JECH State University of New York at Bufalo and The Institute for Advanced Study Princeton, New Jersey 1973 NORTH-HOLLAND PUBLISHING COMPANY - AMSTERDAM LONDON AMERICAN ELSEVIER PUBLISHING COMPANY, INC. - NEW YORK 0 NORTH-HOLLAND PUBLISHING COMPANY - 1973 AN Rights Reserved. No part of this publication may be reproduced, stored in a retrieval system or transmitted, in any form or by any means, electronic, mechanical, photocopying, recording or otherwise, without the prior permission of the Copyright owner. Library of Congress Catalog Card Number 73-15535 North-Holland ISBN for the series 0 7204 2200 0 for this volume 0 1204 2215 2 American Elsevier ISBN 0 444 10484 4 Published by: North-Holland Publishing Company - Amsterdam North-Holland Publishing Company, Ltd. - London Sole distributors for the U.S.A. and Canada: American Elsevier Publishing Company, Inc. 52 Vanderbilt Avenue New York, N.Y. 10017 PRINTED IN THE NETHERLANDS To my parents PREFACE The book was written in the long Buffalo winter of 1971-72. It is an attempt to show the place of the Axiom of Choice in contemporary mathe- matics. Most of the material covered in the book deals with independence and relative strength of various weaker versions and consequences of the Axiom of Choice. Also included are some other results that I found relevant to the subject. The selection of the topics and results is fairly comprehensive, nevertheless it is a selection and as such reflects the personal taste of the author. So does the treatment of the subject. The main tool used throughout the text is Cohen’s method of forcing.