Web 2.0 Fundamentals : with Ajax, Development Tools, and Mobile
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Effects and Opportunities of Native Code Extensions For
Effects and Opportunities of Native Code Extensions for Computationally Demanding Web Applications DISSERTATION zur Erlangung des akademischen Grades Dr. Phil. im Fach Bibliotheks- und Informationswissenschaft eingereicht an der Philosophischen Fakultät I Humboldt-Universität zu Berlin von Dipl. Inform. Dennis Jarosch Präsident der Humboldt-Universität zu Berlin: Prof. Dr. Jan-Hendrik Olbertz Dekan der Philosophischen Fakultät I: Prof. Michael Seadle, Ph.D. Gutachter: 1. Prof. Dr. Robert Funk 2. Prof. Michael Seadle, Ph.D. eingereicht am: 28.10.2011 Tag der mündlichen Prüfung: 16.12.2011 Abstract The World Wide Web is amidst a transition from interactive websites to web applications. An increasing number of users perform their daily computing tasks entirely within the web browser — turning the Web into an important platform for application development. The Web as a platform, however, lacks the computational performance of native applications. This problem has motivated the inception of Microsoft Xax and Google Native Client (NaCl), two independent projects that fa- cilitate the development of native web applications. Native web applications allow the extension of conventional web applications with compiled native code, while maintaining operating system portability. This dissertation determines the bene- fits and drawbacks of native web applications. It also addresses the question how the performance of JavaScript web applications compares to that of native appli- cations and native web applications. Four application benchmarks are introduced that focus on different performance aspects: number crunching (serial and parallel), 3D graphics performance, and data processing. A performance analysis is under- taken in order to determine and compare the performance characteristics of native C applications, JavaScript web applications, and NaCl native web applications. -

Paying Attention to Public Readers of Canadian Literature
PAYING ATTENTION TO PUBLIC READERS OF CANADIAN LITERATURE: POPULAR GENRE SYSTEMS, PUBLICS, AND CANONS by KATHRYN GRAFTON BA, The University of British Columbia, 1992 MPhil, University of Stirling, 1994 A THESIS SUBMITTED IN PARTIAL FULFILLMENT OF THE REQUIREMENTS FOR THE DEGREE OF DOCTOR OF PHILOSOPHY in THE FACULTY OF GRADUATE STUDIES (English) THE UNIVERSITY OF BRITISH COLUMBIA (Vancouver) August 2010 © Kathryn Grafton, 2010 ABSTRACT Paying Attention to Public Readers of Canadian Literature examines contemporary moments when Canadian literature has been canonized in the context of popular reading programs. I investigate the canonical agency of public readers who participate in these programs: readers acting in a non-professional capacity who speak and write publicly about their reading experiences. I argue that contemporary popular canons are discursive spaces whose constitution depends upon public readers. My work resists the common critique that these reading programs and their canons produce a mass of readers who read the same work at the same time in the same way. To demonstrate that public readers are canon-makers, I offer a genre approach to contemporary canons that draws upon literary and new rhetorical genre theory. I contend in Chapter One that canons are discursive spaces comprised of public literary texts and public texts about literature, including those produced by readers. I study the intertextual dynamics of canons through Michael Warner’s theory of publics and Anne Freadman’s concept of “uptake.” Canons arise from genre systems that are constituted to respond to exigencies readily recognized by many readers, motivating some to participate. I argue that public readers’ agency lies in the contingent ways they select and interpret a literary work while taking up and instantiating a canonizing genre. -

What Is Dart?
1 Dart in Action By Chris Buckett As a language on its own, Dart might be just another language, but when you take into account the whole Dart ecosystem, Dart represents an exciting prospect in the world of web development. In this green paper based on Dart in Action, author Chris Buckett explains how Dart, with its ability to either run natively or be converted to JavaScript and coupled with HTML5 is an ideal solution for building web applications that do not need external plugins to provide all the features. You may also be interested in… What is Dart? The quick answer to the question of what Dart is that it is an open-source structured programming language for creating complex browser based web applications. You can run applications created in Dart by either using a browser that directly supports Dart code, or by converting your Dart code to JavaScript (which happens seamlessly). It is class based, optionally typed, and single threaded (but supports multiple threads through a mechanism called isolates) and has a familiar syntax. In addition to running in browsers, you can also run Dart code on the server, hosted in the Dart virtual machine. The language itself is very similar to Java, C#, and JavaScript. One of the primary goals of the Dart developers is that the language seems familiar. This is a tiny dart script: main() { #A var d = “Dart”; #B String w = “World”; #C print(“Hello ${d} ${w}”); #D } #A Single entry point function main() executes when the script is fully loaded #B Optional typing (no type specified) #C Static typing (String type specified) #D Outputs “Hello Dart World” to the browser console or stdout This script can be embedded within <script type=“application/dart”> tags and run in the Dartium experimental browser, converted to JavaScript using the Frog tool and run in all modern browsers, or saved to a .dart file and run directly on the server using the dart virtual machine executable. -

TIBCO Activematrix® BPM Web Client Developer's Guide Software Release 4.3 April 2019 2
TIBCO ActiveMatrix® BPM Web Client Developer's Guide Software Release 4.3 April 2019 2 Important Information SOME TIBCO SOFTWARE EMBEDS OR BUNDLES OTHER TIBCO SOFTWARE. USE OF SUCH EMBEDDED OR BUNDLED TIBCO SOFTWARE IS SOLELY TO ENABLE THE FUNCTIONALITY (OR PROVIDE LIMITED ADD-ON FUNCTIONALITY) OF THE LICENSED TIBCO SOFTWARE. THE EMBEDDED OR BUNDLED SOFTWARE IS NOT LICENSED TO BE USED OR ACCESSED BY ANY OTHER TIBCO SOFTWARE OR FOR ANY OTHER PURPOSE. USE OF TIBCO SOFTWARE AND THIS DOCUMENT IS SUBJECT TO THE TERMS AND CONDITIONS OF A LICENSE AGREEMENT FOUND IN EITHER A SEPARATELY EXECUTED SOFTWARE LICENSE AGREEMENT, OR, IF THERE IS NO SUCH SEPARATE AGREEMENT, THE CLICKWRAP END USER LICENSE AGREEMENT WHICH IS DISPLAYED DURING DOWNLOAD OR INSTALLATION OF THE SOFTWARE (AND WHICH IS DUPLICATED IN THE LICENSE FILE) OR IF THERE IS NO SUCH SOFTWARE LICENSE AGREEMENT OR CLICKWRAP END USER LICENSE AGREEMENT, THE LICENSE(S) LOCATED IN THE “LICENSE” FILE(S) OF THE SOFTWARE. USE OF THIS DOCUMENT IS SUBJECT TO THOSE TERMS AND CONDITIONS, AND YOUR USE HEREOF SHALL CONSTITUTE ACCEPTANCE OF AND AN AGREEMENT TO BE BOUND BY THE SAME. ANY SOFTWARE ITEM IDENTIFIED AS THIRD PARTY LIBRARY IS AVAILABLE UNDER SEPARATE SOFTWARE LICENSE TERMS AND IS NOT PART OF A TIBCO PRODUCT. AS SUCH, THESE SOFTWARE ITEMS ARE NOT COVERED BY THE TERMS OF YOUR AGREEMENT WITH TIBCO, INCLUDING ANY TERMS CONCERNING SUPPORT, MAINTENANCE, WARRANTIES, AND INDEMNITIES. DOWNLOAD AND USE OF THESE ITEMS IS SOLELY AT YOUR OWN DISCRETION AND SUBJECT TO THE LICENSE TERMS APPLICABLE TO THEM. BY PROCEEDING TO DOWNLOAD, INSTALL OR USE ANY OF THESE ITEMS, YOU ACKNOWLEDGE THE FOREGOING DISTINCTIONS BETWEEN THESE ITEMS AND TIBCO PRODUCTS. -
Attacking AJAX Web Applications Vulns 2.0 for Web 2.0
Attacking AJAX Web Applications Vulns 2.0 for Web 2.0 Alex Stamos Zane Lackey [email protected] [email protected] Blackhat Japan October 5, 2006 Information Security Partners, LLC iSECPartners.com Information Security Partners, LLC www.isecpartners.com Agenda • Introduction – Who are we? – Why care about AJAX? • How does AJAX change Web Attacks? • AJAX Background and Technologies • Attacks Against AJAX – Discovery and Method Manipulation – XSS – Cross-Site Request Forgery • Security of Popular Frameworks – Microsoft ATLAS – Google GWT –Java DWR • Q&A 2 Information Security Partners, LLC www.isecpartners.com Introduction • Who are we? – Consultants for iSEC Partners – Application security consultants and researchers – Based in San Francisco • Why listen to this talk? – New technologies are making web app security much more complicated • This is obvious to anybody who reads the paper – MySpace – Yahoo – Worming of XSS – Our Goals for what you should walk away with: • Basic understanding of AJAX and different AJAX technologies • Knowledge of how AJAX changes web attacks • In-depth knowledge on XSS and XSRF in AJAX • An opinion on whether you can trust your AJAX framework to “take care of security” 3 Information Security Partners, LLC www.isecpartners.com Shameless Plug Slide • Special Thanks to: – Scott Stender, Jesse Burns, and Brad Hill of iSEC Partners – Amit Klein and Jeremiah Grossman for doing great work in this area – Rich Cannings at Google • Books by iSECer Himanshu Dwivedi – Securing Storage – Hackers’ Challenge 3 • We are -
Apachecon US 2008 with Apache Shindig
ApacheCon US 2008 Empowering the social web with Apache Shindig Henning Schmiedehausen Sr. Software Engineer – Ning, Inc. November 3 - 7 • New Orleans Leading the Wave of Open Source The Official User Conference of The Apache Software Foundation Freitag, 7. November 2008 1 • How the web became social • Get out of the Silo – Google Gadgets • OpenSocial – A social API • Apache Shindig • Customizing Shindig • Summary November 3 - 7 • New Orleans ApacheCon US 2008 Leading the Wave of Open Source The Official User Conference of The Apache Software Foundation Freitag, 7. November 2008 2 ApacheCon US 2008 In the beginning... Freitag, 7. November 2008 3 ApacheCon US 2008 ...let there be web 2.0 Freitag, 7. November 2008 4 • Web x.0 is about participation • Users have personalized logins Relations between users are graphs • "small world phenomenon", "six degrees of separation", Erdös number, Bacon number November 3 - 7 • New Orleans ApacheCon US 2008 Leading the Wave of Open Source The Official User Conference of The Apache Software Foundation Freitag, 7. November 2008 5 ApacheCon US 2008 The Silo problem Freitag, 7. November 2008 6 • How the web became social • Get out of the Silo – Google Gadgets • OpenSocial – A social API • Apache Shindig • Customizing Shindig • Summary November 3 - 7 • New Orleans ApacheCon US 2008 Leading the Wave of Open Source The Official User Conference of The Apache Software Foundation Freitag, 7. November 2008 7 ApacheCon US 2008 iGoogle Freitag, 7. November 2008 8 • Users adds Gadgets to their homepages Gadgets share screen space • Google experiments with Canvas view Javascript, HTML, CSS • A gadget runs on the Browser! Predefined Gadgets API • Core APIs for IO, JSON, Prefs; optional APIs (e.g. -
Tracking Known Security Vulnerabilities in Third-Party Components
Tracking known security vulnerabilities in third-party components Master’s Thesis Mircea Cadariu Tracking known security vulnerabilities in third-party components THESIS submitted in partial fulfillment of the requirements for the degree of MASTER OF SCIENCE in COMPUTER SCIENCE by Mircea Cadariu born in Brasov, Romania Software Engineering Research Group Software Improvement Group Department of Software Technology Rembrandt Tower, 15th floor Faculty EEMCS, Delft University of Technology Amstelplein 1 - 1096HA Delft, the Netherlands Amsterdam, the Netherlands www.ewi.tudelft.nl www.sig.eu c 2014 Mircea Cadariu. All rights reserved. Tracking known security vulnerabilities in third-party components Author: Mircea Cadariu Student id: 4252373 Email: [email protected] Abstract Known security vulnerabilities are introduced in software systems as a result of de- pending on third-party components. These documented software weaknesses are hiding in plain sight and represent the lowest hanging fruit for attackers. Despite the risk they introduce for software systems, it has been shown that developers consistently download vulnerable components from public repositories. We show that these downloads indeed find their way in many industrial and open-source software systems. In order to improve the status quo, we introduce the Vulnerability Alert Service, a tool-based process to track known vulnerabilities in software projects throughout the development process. Its usefulness has been empirically validated in the context of the external software product quality monitoring service offered by the Software Improvement Group, a software consultancy company based in Amsterdam, the Netherlands. Thesis Committee: Chair: Prof. Dr. A. van Deursen, Faculty EEMCS, TU Delft University supervisor: Prof. Dr. A. -

Writing a Book Using Google Docs
Share Report Abuse Next Blog» Create Blog Sign In Docs Blog News and notes from the Google Docs and Sites teams Guest post: Writing a book using Google Docs Looking for posts on your Monday, November 01, 2010 favorite product? Labels: documents, Google Apps Blog, Guest Post Google Sites Documents Guest post: November is National Writing Month and to celebrate, we’ve invited Dr. Steven Daviss Spreadsheets to talk about how he used Google Docs to write a book with two colleagues. Dr. Daviss is currently Presentations the Chairman of Psychiatry at Baltimore Washington Medical Center in Maryland and has been Forms increasingly leveraging his clinical and administrative experience towards a career merging health Drawings care policy, informatics, and health care reform. Docs list Archives Archives Site Feed Follow us on Twitter twitter.com/googledocs Followers Follow with Google Friend Connect Followers (5351) More » Two other psychiatrists (Anne Hanson and Dinah Miller) and I have been writing a popular blog (Shrink Rap) about the practice of psychiatry since 2006. A year later, we started a podcast (My Three Shrinks) that has received great reviews in iTunes. Late in 2007, we decided to take some of those posts and weave them together to write a book. We started out using a desktop word processor to write the book, each chapter being a separate document. We learned about the limitations of making edits and sending out each of our revisions to the other two: we very quickly had multiple out-of-sync versions and the whole thing was a mess. This is from one of Dinah’s emails back then: “With 3 people doing this, I need to be able to keep track of what everyone wants to write. -

Tipologie Di Dati Raccolti Modalità E
Privacy Policy di www.mcj.it Questa Applicazione raccoglie alcuni Dati Personali dei propri Utenti. Titolare del Trattamento dei Dati Mcj Sede legale: Corso Rosselli, 73 – 10129 Torino P.IVA 01370130336 Tipologie di Dati raccolti Fra i Dati Personali raccolti da questa Applicazione, in modo autonomo o tramite terze parti, ci sono: Cookie, Dati di utilizzo, Numero di Telefono, Email, Nome, Cognome, Posizione geografica, Indirizzo, Password, Codice Fiscale, Professione, Nazione, Provincia, CAP e Città. Altri Dati Personali raccolti potrebbero essere indicati in altre sezioni di questa privacy policy o mediante testi informativi visualizzati contestualmente alla raccolta dei Dati stessi. I Dati Personali possono essere inseriti volontariamente dall’Utente, oppure raccolti in modo automatico durante l'uso di questa Applicazione. L’eventuale utilizzo di Cookie - o di altri strumenti di tracciamento - da parte di questa Applicazione o dei titolari dei servizi terzi utilizzati da questa Applicazione, ove non diversamente precisato, ha la finalità di identificare l’Utente e registrare le relative preferenze per finalità strettamente legate all'erogazione del servizio richiesto dall’Utente. Il mancato conferimento da parte dell’Utente di alcuni Dati Personali potrebbe impedire a questa Applicazione di erogare i propri servizi. L'Utente si assume la responsabilità dei Dati Personali di terzi pubblicati o condivisi mediante questa Applicazione e garantisce di avere il diritto di comunicarli o diffonderli, liberando il Titolare da qualsiasi responsabilità verso terzi. Modalità e luogo del trattamento dei Dati raccolti Modalità di trattamento Il Titolare tratta i Dati Personali degli Utenti adottando le opportune misure di sicurezza volte ad impedire l’accesso, la divulgazione, la modifica o la distruzione non autorizzate dei Dati Personali. -

Cliente Twitter Con Compresión De Datos
PROYECTO FIN DE GRADO GRADO EN INGENIERÍA INFROMÁTICA CLIENTE TWITTER CON COMPRESIÓN DE DATOS Autor: Plácido Fernández Declara Tutores: Luis Miguel Sánchez García Rafael Sotomayor Fernández Colmenarejo, Febrero de 2013 RESUMEN La popular red social Twitter es usada hoy en día en diversos lugares y momentos, gracias también a las redes móviles que nos proporcionan conexión a internet en casi cualquier lugar. Twitter permite publicar y mandar mensajes cortos de texto plano con un máximo de 140 caracteres, así como la lectura de estos mensajes cortos de otros usuarios a los que podemos seguir para tal propósito. Hacer uso de este servicio en zonas con buena cobertura, o cuando usamos Wi-fi no supone generalmente ningún problema. Es cuando nos encontramos en zonas de poca cobertura cuando vemos problemas para hacer uso de este servicio, ya que las velocidades de descarga pueden disminuir hasta el punto de necesitar decenas de segundos para disponer de los mensajes cortos, los “Tweets”. A esto hay que añadir que los planes de datos actuales están limitados de alguna forma (al alcanzar un número de Mb), por lo que la cantidad de Mb usada es hoy también un factor importante. Para ello esta aplicación ofrece la experiencia de un cliente Twitter sencillo en el que consultar los “Tweets” de a quien seguimos, así como publicar “Tweets”, haciendo uso de un Proxy que comprime estos datos considerablemente de forma que se reducen los tiempos de descarga para las zonas de poca cobertura y además se reduce el número de Mb consumidos por el dispositivo móvil. Índice de contenido RESUMEN ................................................................................................................................. -
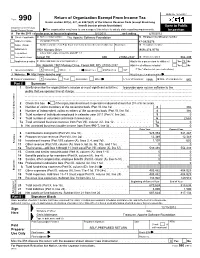
Return of Organization Exempt from Income
OMB No. 1545-0047 Return of Organization Exempt From Income Tax Form 990 Under section 501(c), 527, or 4947(a)(1) of the Internal Revenue Code (except black lung benefit trust or private foundation) Open to Public Department of the Treasury Internal Revenue Service The organization may have to use a copy of this return to satisfy state reporting requirements. Inspection A For the 2011 calendar year, or tax year beginning 5/1/2011 , and ending 4/30/2012 B Check if applicable: C Name of organization The Apache Software Foundation D Employer identification number Address change Doing Business As 47-0825376 Name change Number and street (or P.O. box if mail is not delivered to street address) Room/suite E Telephone number Initial return 1901 Munsey Drive (909) 374-9776 Terminated City or town, state or country, and ZIP + 4 Amended return Forest Hill MD 21050-2747 G Gross receipts $ 554,439 Application pending F Name and address of principal officer: H(a) Is this a group return for affiliates? Yes X No Jim Jagielski 1901 Munsey Drive, Forest Hill, MD 21050-2747 H(b) Are all affiliates included? Yes No I Tax-exempt status: X 501(c)(3) 501(c) ( ) (insert no.) 4947(a)(1) or 527 If "No," attach a list. (see instructions) J Website: http://www.apache.org/ H(c) Group exemption number K Form of organization: X Corporation Trust Association Other L Year of formation: 1999 M State of legal domicile: MD Part I Summary 1 Briefly describe the organization's mission or most significant activities: to provide open source software to the public that we sponsor free of charge 2 Check this box if the organization discontinued its operations or disposed of more than 25% of its net assets. -
Towards Secure and Reusable Web Applications
Mashups and Modularity: Towards Secure and Reusable Web Applications Antero Taivalsaari Tommi Mikkonen Sun Microsystems Laboratories [email protected] http://research.sun.com/projects/lively 2 Evolution of the Web 1) Simple pages with text and static images only (e.g., http://www.google.com) 2) Animated pages with plug-ins (e.g., http://www.cadillac.com) 3) Rich Internet Applications (e.g., docs.google.com) What's Next? 3 Web Applications – Implications • Web-based software will dramatically change the way people develop, deploy and use software. • No more installations! > Applications will simply run off the Web. • No more upgrades! > Always run the latest application version. • Instant worldwide deployment! > No middlemen or distributors needed. • No CPU dependencies, OS dependencies, ... > The Web is the Platform. 4 Unfortunately... • The web browser was not designed for running real applications. > It was designed in the early 1990s for viewing documents, forms and other page-structured artifacts – not applications. > Programming capabilities on the web were an afterthought, not something inherent in the design of the browser. • Various Rich Internet Application (RIA) technologies have been introduced recently to retrofit application execution capabilities into the web browser. 5 Web Development vs. Conventional Software The Impedance Mismatch Web Development Conventional SW Development - Documents - Applications - Page / form oriented interaction - Direct manipulation - Managed graphics, static layout - Directly drawn, dynamic