Nessus 8.11 User Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

CIS Debian Linux 7 Benchmark V1.0.0 - 12-31-2015
CIS Debian Linux 7 Benchmark v1.0.0 - 12-31-2015 http://benchmarks.cisecurity.org The CIS Security Benchmarks division provides consensus-oriented information security products, services, tools, metrics, suggestions, and recommendations (the “SB Products”) as a public service to Internet users worldwide. Downloading or using SB Products in any way signifies and confirms your acceptance of and your binding agreement to these CIS Security Benchmarks Terms of Use. CIS SECURITY BENCHMARKS TERMS OF USE BOTH CIS SECURITY BENCHMARKS DIVISION MEMBERS AND NON-MEMBERS MAY: Download, install, and use each of the SB Products on a single computer, and/or Print one or more copies of any SB Product that is in a .txt, .pdf, .doc, .mcw, or .rtf format, but only if each such copy is printed in its entirety and is kept intact, including without limitation the text of these CIS Security Benchmarks Terms of Use. UNDER THE FOLLOWING TERMS AND CONDITIONS: SB Products Provided As Is. CIS is providing the SB Products “as is” and “as available” without: (1) any representations, warranties, or covenants of any kind whatsoever (including the absence of any warranty regarding: (a) the effect or lack of effect of any SB Product on the operation or the security of any network, system, software, hardware, or any component of any of them, and (b) the accuracy, utility, reliability, timeliness, or completeness of any SB Product); or (2) the responsibility to make or notify you of any corrections, updates, upgrades, or fixes. Intellectual Property and Rights Reserved. You are not acquiring any title or ownership rights in or to any SB Product, and full title and all ownership rights to the SB Products remain the exclusive property of CIS. -
1 Introduction
Technical report, IDE1202, February 2012 Enhancing Network Security in Linux Environment Master Thesis in Computer Network Engineering By Ali Mohammed, Sachin Sama and Majeed Mohammed School of Information Science, Computer and Electrical Engineering Halmstad University i Enhancing Network Security in Linux Environment Master Thesis in Computer Network Engineering School of Information Science, Computer and Electrical Engineering Halmstad University Box 823, S-301 18 Halmstad, Sweden February 2012 ii Preface First of all, we would like to express our sincere gratitude to our Supervisor Philip Heimer and Professor Tony Larsson for their supervision and assistance in the entire thesis work. We are also thankful to IDE department, Halmstad University for providing this opportunity to complete this thesis. Ali Mohammed Sachin Sama Majeed Mohammed iii iv Abstract Designing a secured network is the most important task in any enterprise or organization development. Securing a network mainly involves applying policies and procedures to protect different network devices from unauthorized access. Servers such as web servers, file servers, mail servers, etc., are the important devices in a network. Therefore, securing these servers is the first and foremost step followed in every security implementation mechanism. To implement this, it is very important to analyse and study the security mechanisms provided by the operating system. This makes it easier for security implementation in a network. This thesis work demonstrates the tasks needed to enhance the network security in Linux environment. The various security modules existing in Linux makes it different from other operating systems. The security measures which are mainly needed to enhance the system security are documented as a baseline for practical implementation. -
Access Control Framework
This material is based on work supported by the National Science Foundation under Grant No. 0802551 Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author (s) and do not necessarily reflect the views of the National Science Foundation C5L1S1 When working for an institution as a Linux Administrator, you may be required to protect certain information based on its sensitivity. For instance, most organizations will have an internal network in which data contained in certain directories or drives are made public—employees can access the contents. However, certain kinds of information such as employee salaries, classified research, secret prototypes, health information, military secrets, and private communications are considered highly sensitive and are usually restrictedU the from everyone except very few people authorized to access the data. In this lesson, we will explore processes, tools, and control lists that make it possible to limit access to sensitive data on a Linux-based system. Understanding this topic is important for any system administrator configuring systems in the workplace that require access control mechanisms. C5L1S2 You should know what will be expected of you when you complete this lesson. These expectations are presented as objectives. Objectives are short statements of expectations that tell you what you must be able to do, perform, learn, or adjust after reviewing the lesson. Lesson Objective: U the Given the need to secure a Linux server, the student will recommend a set of standard Linux tools such as PAM, Access Control Lists, and TCP Wrappers to effectively secure a Linux system and demonstrate the use of one set of tools for system lock-down. -
My Name Is Robert Kudyba and I Am the System Administrator for The
My name is Robert Kudyba and I am the System Administrator for the Department of Computer Science here at Fordham University and a recent graduate of the Master’s in Cybersecurity. The lab will require you to install VirtualBox with Ubuntu preferable from osboxes.org. The commands listed in the lab will assume you have installed this image. Any Ubuntu version will work but if you installed from ubuntu.com then you will have to substitute the username you created for every place I reference osboxes. If you use Kali, you will be using the root user and there may be other issues as I’ve only confirmed everything works on Ubuntu. 1 In this lab, I will be gong over Linux remote access protocols Telnet and SSH, providing a history, the various encryption methods used, the concept of security through obscurity, a program called Fail2ban, how to use a Certificate Authority in OpenSSH, TCPWrapper, and Port Knocking. 2 • Telnet is a simple, text-based network protocol that is used for accessing remote computers over TCP/IP networks like the Internet. Telnet was created and launched in 1969. • Prior to telnet, you had to physically walk to a server in order to access its data. This meant, among other things, that you had to spend some time arriving at the server's location and then you had to wait for your turn to work with the server. Even if the server had the hardware power to do multiple things at the same time, you were blocked from using if someone was before you so you had to wait for others to finish their work first. -

Nessus 8.3 User Guide
Nessus 8.3.x User Guide Last Updated: September 24, 2021 Table of Contents Welcome to Nessus 8.3.x 12 Get Started with Nessus 15 Navigate Nessus 16 System Requirements 17 Hardware Requirements 18 Software Requirements 22 Customize SELinux Enforcing Mode Policies 25 Licensing Requirements 26 Deployment Considerations 27 Host-Based Firewalls 28 IPv6 Support 29 Virtual Machines 30 Antivirus Software 31 Security Warnings 32 Certificates and Certificate Authorities 33 Custom SSL Server Certificates 35 Create a New Server Certificate and CA Certificate 37 Upload a Custom Server Certificate and CA Certificate 39 Trust a Custom CA 41 Create SSL Client Certificates for Login 43 Nessus Manager Certificates and Nessus Agent 46 Install Nessus 48 Copyright © 2021 Tenable, Inc. All rights reserved. Tenable, Tenable.io, Tenable Network Security, Nessus, SecurityCenter, SecurityCenter Continuous View and Log Correlation Engine are registered trade- marks of Tenable,Inc. Tenable.sc, Tenable.ot, Lumin, Indegy, Assure, and The Cyber Exposure Company are trademarks of Tenable, Inc. All other products or services are trademarks of their respective Download Nessus 49 Install Nessus 51 Install Nessus on Linux 52 Install Nessus on Windows 54 Install Nessus on Mac OS X 56 Install Nessus Agents 58 Retrieve the Linking Key 59 Install a Nessus Agent on Linux 60 Install a Nessus Agent on Windows 64 Install a Nessus Agent on Mac OS X 70 Upgrade Nessus and Nessus Agents 74 Upgrade Nessus 75 Upgrade from Evaluation 76 Upgrade Nessus on Linux 77 Upgrade Nessus on Windows 78 Upgrade Nessus on Mac OS X 79 Upgrade a Nessus Agent 80 Configure Nessus 86 Install Nessus Home, Professional, or Manager 87 Link to Tenable.io 88 Link to Industrial Security 89 Link to Nessus Manager 90 Managed by Tenable.sc 92 Manage Activation Code 93 Copyright © 2021 Tenable, Inc. -

Absolute BSD—The Ultimate Guide to Freebsd Table of Contents Absolute BSD—The Ultimate Guide to Freebsd
Absolute BSD—The Ultimate Guide to FreeBSD Table of Contents Absolute BSD—The Ultimate Guide to FreeBSD............................................................................1 Dedication..........................................................................................................................................3 Foreword............................................................................................................................................4 Introduction........................................................................................................................................5 What Is FreeBSD?...................................................................................................................5 How Did FreeBSD Get Here?..................................................................................................5 The BSD License: BSD Goes Public.......................................................................................6 The Birth of Modern FreeBSD.................................................................................................6 FreeBSD Development............................................................................................................7 Committers.........................................................................................................................7 Contributors........................................................................................................................8 Users..................................................................................................................................8 -
TASK \ OS TASK \ OS TASK \ OS Show/Set EEPROM
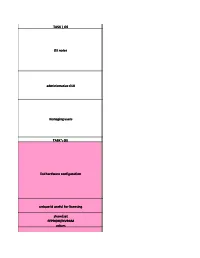
TASK \ OS OS notes administrative GUI managing users TASK \ OS list hardware configuration unique id useful for licensing show/set EEPROM/NVRAM values add device without reboot remove device tape device stdin/ stdout/ stderr X kvm config TASK \ OS read a disk label whole disk in partition label a disk partition a disk TASK \ OS kernel show/set kernel parameters limit physical memory loaded kernel modules load module unload module make disk bootable startup scripts start/ stop/ config services shutdown (& power off if possible) run levels 1 *=normal states for more detail see www.phildev.net/runlevels.html show runlevel 1 time zone info check swap space bind process to CPU TASK \ OS "normal" filesystem volume-based filesystem file system description volume manipulation create filesystem create non-0-length empty file mount CDROM eject CDROM create/mount ISO image ACL management Fibre Channel / SAN TASK \ OS NFS share definitions NFS share command NFS information name resolution order show network interface info change IP start DHCP client ping one packet sniff network route definitions telnetd, ftpd banner set date/time (from net: ntp or other) TASK \ OS auditing encrypted passwords in min password length allow/deny root logins firewall config TASK \ OS show installed software file is in which package add software precompiled binaries of GPLware and freeware C compiler show patch level and/or patches patch tool configure/show runtime linking fortran-2000.com/ ArnaudRecipes/ sharedlib.html link library path tracing utility define user defaults csh global .login default syslog and messages system error reporting tool performance monitoring match process to file or port X pop-up Wikipedia FAQs (see also faqs.org) mailing list mailing list archives man pages www.freebsd.org/ cgi/man.cgi newsgroup(s) and forums groups.google user groups magazines vendor home page vendor docs and patches (see also man pages) vendor phone (US) wikis FreeBSD Derived from 4.4BSD-Lite and 386BSD. -
Firewalls and IDS
Firewalls and IDS Dr. Natarajan Meghanathan Associate Professor of Computer Science Jackson State University E-mail: [email protected] Firewalls • A firewall is a device that filters traffic between a “protected” or inside network and a “less trustworthy” or outside network. • A firewall is basically an executable code run on a dedicated computer. • As all traffic should pass through the firewall, it is not a point of bottleneck for system performance and hence non-firewall functions are not performed on that machine running the firewall. • Also, since non-firewall code does not exist in the computer, it is hard for an attacker to make use of any vulnerability to compromise the firewall. • Design idea: – Firewalls implement a security policy that is specifically designed to address what bad things that should not happen in a “protected environment” – Security policies that dictate what to allow: Standard security practices dictate a “default-deny” ruleset for firewalls, implying that the only network connections allowed are the ones that have been explicitly stated to be allowed. – Security policies that dictate what not to allow: Users and business community who lack such a detailed understanding to explicitly state what should be allowed in prefer a “default-allow” ruleset, in which all traffic is allowed unless it has been specifically blocked. – Even though this configuration is relatively more prone to inadvertent network connections and system compromise, it is more commonly used because of mere lack of knowledge and new applications that come into existence. Firewalls • Not all firewalls need to have the same capability. • One cannot compare the “goodness” of two firewalls based on the security policies they are configured with. -

Securing Mac OS X 10.4 Tiger V1.0.Doc
The natural choice for information security solutions AA CCoorrssaaiirree WWhhiittee PPaappeerr:: SSeeccuurriinngg MMaacc OOSS XX Author Stephen de Vries Document Reference Securing Mac OS X 10.4 Tiger v1.0.doc Document Revision 1.0 Released Date 19 August 2005 © Copyright 2000 – 2005 Corsaire Limited All Rights Reserved A Corsaire White Paper: Securing Mac OS X Table of Contents TABLE OF CONTENTS............................................................................................................ 2 1. INTRODUCTION................................................................................................................ 3 2. USING THIS GUIDE .......................................................................................................... 3 2.1 The Common Criteria..................................................................................................... 3 3. SUMMARY OF SECURITY HARDENING......................................................................... 4 4. SECURITY HARDENING GUIDELINES ........................................................................... 4 4.1 General Security Settings ............................................................................................. 4 4.2 Patching & Maintenance................................................................................................ 7 4.3 Physical Access Controls ............................................................................................. 8 4.4 Keychain ...................................................................................................................... -

1999 CERT Advisories
1999 CERT Advisories CERT Division [DISTRIBUTION STATEMENT A] Approved for public release and unlimited distribution. http://www.sei.cmu.edu REV-03.18.2016.0 [DISTRIBUTION STATEMENT A] Approved for public release and unlimited distribution. Copyright 2017 Carnegie Mellon University. All Rights Reserved. This material is based upon work funded and supported by the Department of Defense under Contract No. FA8702-15-D-0002 with Carnegie Mellon University for the operation of the Software Engineering Institute, a federally funded research and development center. The view, opinions, and/or findings contained in this material are those of the author(s) and should not be con- strued as an official Government position, policy, or decision, unless designated by other documentation. References herein to any specific commercial product, process, or service by trade name, trade mark, manu- facturer, or otherwise, does not necessarily constitute or imply its endorsement, recommendation, or favoring by Carnegie Mellon University or its Software Engineering Institute. This report was prepared for the SEI Administrative Agent AFLCMC/AZS 5 Eglin Street Hanscom AFB, MA 01731-2100 NO WARRANTY. THIS CARNEGIE MELLON UNIVERSITY AND SOFTWARE ENGINEERING INSTITUTE MATERIAL IS FURNISHED ON AN "AS-IS" BASIS. CARNEGIE MELLON UNIVERSITY MAKES NO WARRANTIES OF ANY KIND, EITHER EXPRESSED OR IMPLIED, AS TO ANY MATTER INCLUDING, BUT NOT LIMITED TO, WARRANTY OF FITNESS FOR PURPOSE OR MERCHANTABILITY, EXCLUSIVITY, OR RESULTS OBTAINED FROM USE OF THE MATERIAL. CARNEGIE MELLON UNIVERSITY DOES NOT MAKE ANY WARRANTY OF ANY KIND WITH RESPECT TO FREEDOM FROM PATENT, TRADEMARK, OR COPYRIGHT INFRINGEMENT. [DISTRIBUTION STATEMENT A] This material has been approved for public release and unlimited distribu- tion. -

Linux Server Configuration Guidelines
Linux Server Configuration Guidelines This document is meant to be a living document and intended to accompany more detailed, step-by-step resources. Suggestions in this document are taken from administrators around campus and are provided to serve either as a checklist and reference for those who may work with servers on a regular basis, or a starting point to those who are new to the task. Content in this document is provided as a suggestion or reminder with emphasis on best practice. ITS has a license for Qualys Vulnerability Management scanning. Contact us if you would like to learn more and potentially configure scans of your servers to help identify potential vulnerabilities. Table of Contents Table of Contents ....................................................................................................................................... 1 Do You Really Need a Server? .............................................................................................................. 2 A Note on PCI Compliance ................................................................................................................................ 2 Planning ......................................................................................................................................................... 2 Server Role .............................................................................................................................................................. 2 Vulnerable Services ............................................................................................................................................ -

Administering TCP/IP Networks, IPMP, and IP Tunnels in Oracle Solaris 11.3 Part No: E54741 Copyright © 2011, 2019, Oracle And/Or Its Affiliates
Administering TCP/IP Networks, IPMP, ® and IP Tunnels in Oracle Solaris 11.3 Part No: E54741 March 2019 Administering TCP/IP Networks, IPMP, and IP Tunnels in Oracle Solaris 11.3 Part No: E54741 Copyright © 2011, 2019, Oracle and/or its affiliates. All rights reserved. This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. If this is software or related documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, then the following notice is applicable: U.S. GOVERNMENT END USERS: Oracle programs, including any operating system, integrated software, any programs installed on the hardware, and/or documentation, delivered to U.S. Government end users are "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, use, duplication, disclosure, modification, and adaptation of the programs, including any operating system, integrated software, any programs installed on the hardware, and/or documentation, shall be subject to license terms and license restrictions applicable to the programs.