Command Line Interface Reference
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Commands to Control Device
Commands to Control Device New OTA firmware upgrade command. To try it via over-the-air update, use these commands: > fwe > fwd B6FMA186 The board will reboot after the first command, this is normal. After the second command wait 1-3 minutes (seems like a long time). After it resets again, go back to BlueFruit and press "info" the software should be 3.0.186 The default wakeup interval is still 4 hours (14400 seconds). To configure a unit for a different wakeup interval: >wakt 600 (this would be 60*10 = 10 minutes) No beeps (Command to turn off the beeps) nvap 6 120000 14400000 15000 5000 0 223 1 3 Command to Restore Beeps nvap 6 120000 14400000 15000 5000 0 223 1 65535 Main Menu commands ---- SubMenus -------------------------- >i - I2C menu >l - Log menu >M - Modem menu ---- Device Control Cmds --------------- >D [n] - set debug level to [n] >info - Show device info >cota - CDMA OTA reprovision >svrm [name] - Set server main >nvmr - Non-volatile memory revert >t - show system uptime >rst - Hard reset ---- General Cmds ---------------------- >c [str] - Execute remote command manually >batq - Query battery state >slp - Go to sleep immediately >slpt [n] - Set sleep timeout to [n] seconds >wakt [n] - Set wake timeout to [n] hours >sus - Suspend immediately >sts - Show statistics and send to server >bt [n] - Bluetooth disable/enable: n=0/1 >dsms [n] - DebugSMS configure 0/1=disabled/enabled >wss [p] [s] - WiMM Server Send [p]ort, [s]tring >wsr - WiMM Server Recv ---- Pos/Log Cmds ---------------------- >pn - Position now >plc {i} {t} - Position log ctrl, [i]nterval, [t]ripId Stop Logging >pla {i} {t} - Position log auto, [i]nterval, [t]ripId >plb {n} - Position log batch [n] records >ple - Position log erase --- Alarm Cmds ------------------------ >alm [m] - Alarm mode: m=0/1/2: Off/On/FireNow ---- Firmware Cmds --------------------- >fwd [v] - Firmware Download (WIMM{v}.hex) >fwl {i} - Firmware Launch (i=0/1: ImgA/B) >fwe - Firmware Erase (ImgB) To change the alarm delay You must be running firmware 145 or later. -

By Sebastiano Vigna and Todd M. Lewis Copyright C 1993-1998 Sebastiano Vigna Copyright C 1999-2021 Todd M
ne A nice editor Version 3.3.1 by Sebastiano Vigna and Todd M. Lewis Copyright c 1993-1998 Sebastiano Vigna Copyright c 1999-2021 Todd M. Lewis and Sebastiano Vigna Permission is granted to make and distribute verbatim copies of this manual provided the copyright notice and this permission notice are preserved on all copies. Permission is granted to copy and distribute modified versions of this manual under the conditions for verbatim copying, provided that the entire resulting derived work is distributed under the terms of a permission notice identical to this one. Permission is granted to copy and distribute translations of this manual into another language, under the above conditions for modified versions, except that this permission notice may be stated in a translation approved by the Free Software Foundation. Chapter 1: Introduction 1 1 Introduction ne is a full screen text editor for UN*X (or, more precisely, for POSIX: see Chapter 7 [Motivations and Design], page 65). I came to the decision to write such an editor after getting completely sick of vi, both from a feature and user interface point of view. I needed an editor that I could use through a telnet connection or a phone line and that wouldn’t fire off a full-blown LITHP1 operating system just to do some editing. A concise overview of the main features follows: • three user interfaces: control keystrokes, command line, and menus; keystrokes and menus are completely configurable; • syntax highlighting; • full support for UTF-8 files, including multiple-column characters; • 64-bit -
Administering Unidata on UNIX Platforms
C:\Program Files\Adobe\FrameMaker8\UniData 7.2\7.2rebranded\ADMINUNIX\ADMINUNIXTITLE.fm March 5, 2010 1:34 pm Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta UniData Administering UniData on UNIX Platforms UDT-720-ADMU-1 C:\Program Files\Adobe\FrameMaker8\UniData 7.2\7.2rebranded\ADMINUNIX\ADMINUNIXTITLE.fm March 5, 2010 1:34 pm Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Notices Edition Publication date: July, 2008 Book number: UDT-720-ADMU-1 Product version: UniData 7.2 Copyright © Rocket Software, Inc. 1988-2010. All Rights Reserved. Trademarks The following trademarks appear in this publication: Trademark Trademark Owner Rocket Software™ Rocket Software, Inc. Dynamic Connect® Rocket Software, Inc. RedBack® Rocket Software, Inc. SystemBuilder™ Rocket Software, Inc. UniData® Rocket Software, Inc. UniVerse™ Rocket Software, Inc. U2™ Rocket Software, Inc. U2.NET™ Rocket Software, Inc. U2 Web Development Environment™ Rocket Software, Inc. wIntegrate® Rocket Software, Inc. Microsoft® .NET Microsoft Corporation Microsoft® Office Excel®, Outlook®, Word Microsoft Corporation Windows® Microsoft Corporation Windows® 7 Microsoft Corporation Windows Vista® Microsoft Corporation Java™ and all Java-based trademarks and logos Sun Microsystems, Inc. UNIX® X/Open Company Limited ii SB/XA Getting Started The above trademarks are property of the specified companies in the United States, other countries, or both. All other products or services mentioned in this document may be covered by the trademarks, service marks, or product names as designated by the companies who own or market them. License agreement This software and the associated documentation are proprietary and confidential to Rocket Software, Inc., are furnished under license, and may be used and copied only in accordance with the terms of such license and with the inclusion of the copyright notice. -
(2) G: 9 Timeout Error Layer —T
US007831732B1 (12) United States Patent (10) Patent No.: US 7,831,732 B1 Zilist et al. (45) Date of Patent: Nov. 9, 2010 (54) NETWORK CONNECTION UTILITY 6,018,724 A 1/2000 Arent 6,182,139 B1 1/2001 Brendel ...................... TO9,226 (75) Inventors: Ira Zilist, Chicago, IL (US); Daniel 6,338,094 B1* 1/2002 Scott et al. .................. 709/245 Reimann, Mt. Prospect, IL (US); Devin 6,393,581 B1 5, 2002 Friedman et al. 6,731,625 B1 5/2004 Eastep et al. Henkel, Chicago, IL (US); Gurpreet 6,742,015 B1 5/2004 Bowman-Amuah Singh, Clarendon Hills, IL (US) 7,082,454 B1* 7/2006 Gheith ....................... TO9,203 2002/0120800 A1* 8/2002 Sugahara et al. .. ... 710,260 (73) Assignee: Federal Reserve Bank of Chicago, 2004/0010546 A1* 1/2004 Kluget al. ............ ... 709,203 Chicago, IL (US) 2004/0192383 A1* 9, 2004 Zacks et al. ................. 455/557 (*) Notice: Subject to any disclaimer, the term of this patent is extended or adjusted under 35 * cited by examiner U.S.C. 154(b) by 1196 days. Primary Examiner Ario Etienne Assistant Examiner Avi Gold (21) Appl. No.: 11/192,991 (74) Attorney, Agent, or Firm—Brinks Hofer Gilson & Lione (22) Filed: Jul. 29, 2005 (57) ABSTRACT Int. C. (51) A system is disclosed for masking errors that may occur G06F 15/16 (2006.01) during a delay of a client connecting with a server on a (52) U.S. Cl. ........................ 709/237; 709/217; 709/219 network. A connection utility requests a connection with the (58) Field of Classification Search ................ -
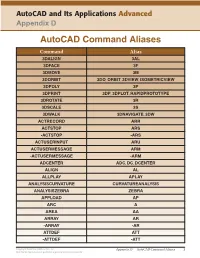
Autocad Command Aliases
AutoCAD and Its Applications Advanced Appendix D AutoCAD Command Aliases Command Alias 3DALIGN 3AL 3DFACE 3F 3DMOVE 3M 3DORBIT 3DO, ORBIT, 3DVIEW, ISOMETRICVIEW 3DPOLY 3P 3DPRINT 3DP, 3DPLOT, RAPIDPROTOTYPE 3DROTATE 3R 3DSCALE 3S 3DWALK 3DNAVIGATE, 3DW ACTRECORD ARR ACTSTOP ARS -ACTSTOP -ARS ACTUSERINPUT ARU ACTUSERMESSAGE ARM -ACTUSERMESSAGE -ARM ADCENTER ADC, DC, DCENTER ALIGN AL ALLPLAY APLAY ANALYSISCURVATURE CURVATUREANALYSIS ANALYSISZEBRA ZEBRA APPLOAD AP ARC A AREA AA ARRAY AR -ARRAY -AR ATTDEF ATT -ATTDEF -ATT Copyright Goodheart-Willcox Co., Inc. Appendix D — AutoCAD Command Aliases 1 May not be reproduced or posted to a publicly accessible website. Command Alias ATTEDIT ATE -ATTEDIT -ATE, ATTE ATTIPEDIT ATI BACTION AC BCLOSE BC BCPARAMETER CPARAM BEDIT BE BLOCK B -BLOCK -B BOUNDARY BO -BOUNDARY -BO BPARAMETER PARAM BREAK BR BSAVE BS BVSTATE BVS CAMERA CAM CHAMFER CHA CHANGE -CH CHECKSTANDARDS CHK CIRCLE C COLOR COL, COLOUR COMMANDLINE CLI CONSTRAINTBAR CBAR CONSTRAINTSETTINGS CSETTINGS COPY CO, CP CTABLESTYLE CT CVADD INSERTCONTROLPOINT CVHIDE POINTOFF CVREBUILD REBUILD CVREMOVE REMOVECONTROLPOINT CVSHOW POINTON Copyright Goodheart-Willcox Co., Inc. Appendix D — AutoCAD Command Aliases 2 May not be reproduced or posted to a publicly accessible website. Command Alias CYLINDER CYL DATAEXTRACTION DX DATALINK DL DATALINKUPDATE DLU DBCONNECT DBC, DATABASE, DATASOURCE DDGRIPS GR DELCONSTRAINT DELCON DIMALIGNED DAL, DIMALI DIMANGULAR DAN, DIMANG DIMARC DAR DIMBASELINE DBA, DIMBASE DIMCENTER DCE DIMCONSTRAINT DCON DIMCONTINUE DCO, DIMCONT DIMDIAMETER DDI, DIMDIA DIMDISASSOCIATE DDA DIMEDIT DED, DIMED DIMJOGGED DJO, JOG DIMJOGLINE DJL DIMLINEAR DIMLIN, DLI DIMORDINATE DOR, DIMORD DIMOVERRIDE DOV, DIMOVER DIMRADIUS DIMRAD, DRA DIMREASSOCIATE DRE DIMSTYLE D, DIMSTY, DST DIMTEDIT DIMTED DIST DI, LENGTH DIVIDE DIV DONUT DO DRAWINGRECOVERY DRM DRAWORDER DR Copyright Goodheart-Willcox Co., Inc. -

Types and Programming Languages by Benjamin C
< Free Open Study > . .Types and Programming Languages by Benjamin C. Pierce ISBN:0262162091 The MIT Press © 2002 (623 pages) This thorough type-systems reference examines theory, pragmatics, implementation, and more Table of Contents Types and Programming Languages Preface Chapter 1 - Introduction Chapter 2 - Mathematical Preliminaries Part I - Untyped Systems Chapter 3 - Untyped Arithmetic Expressions Chapter 4 - An ML Implementation of Arithmetic Expressions Chapter 5 - The Untyped Lambda-Calculus Chapter 6 - Nameless Representation of Terms Chapter 7 - An ML Implementation of the Lambda-Calculus Part II - Simple Types Chapter 8 - Typed Arithmetic Expressions Chapter 9 - Simply Typed Lambda-Calculus Chapter 10 - An ML Implementation of Simple Types Chapter 11 - Simple Extensions Chapter 12 - Normalization Chapter 13 - References Chapter 14 - Exceptions Part III - Subtyping Chapter 15 - Subtyping Chapter 16 - Metatheory of Subtyping Chapter 17 - An ML Implementation of Subtyping Chapter 18 - Case Study: Imperative Objects Chapter 19 - Case Study: Featherweight Java Part IV - Recursive Types Chapter 20 - Recursive Types Chapter 21 - Metatheory of Recursive Types Part V - Polymorphism Chapter 22 - Type Reconstruction Chapter 23 - Universal Types Chapter 24 - Existential Types Chapter 25 - An ML Implementation of System F Chapter 26 - Bounded Quantification Chapter 27 - Case Study: Imperative Objects, Redux Chapter 28 - Metatheory of Bounded Quantification Part VI - Higher-Order Systems Chapter 29 - Type Operators and Kinding Chapter 30 - Higher-Order Polymorphism Chapter 31 - Higher-Order Subtyping Chapter 32 - Case Study: Purely Functional Objects Part VII - Appendices Appendix A - Solutions to Selected Exercises Appendix B - Notational Conventions References Index List of Figures < Free Open Study > < Free Open Study > Back Cover A type system is a syntactic method for automatically checking the absence of certain erroneous behaviors by classifying program phrases according to the kinds of values they compute. -

CS101 Lecture 9
How do you copy/move/rename/remove files? How do you create a directory ? What is redirection and piping? Readings: See CCSO’s Unix pages and 9-2 cp option file1 file2 First Version cp file1 file2 file3 … dirname Second Version This is one version of the cp command. file2 is created and the contents of file1 are copied into file2. If file2 already exits, it This version copies the files file1, file2, file3,… into the directory will be replaced with a new one. dirname. where option is -i Protects you from overwriting an existing file by asking you for a yes or no before it copies a file with an existing name. -r Can be used to copy directories and all their contents into a new directory 9-3 9-4 cs101 jsmith cs101 jsmith pwd data data mp1 pwd mp1 {FILES: mp1_data.m, mp1.m } {FILES: mp1_data.m, mp1.m } Copy the file named mp1_data.m from the cs101/data Copy the file named mp1_data.m from the cs101/data directory into the pwd. directory into the mp1 directory. > cp ~cs101/data/mp1_data.m . > cp ~cs101/data/mp1_data.m mp1 The (.) dot means “here”, that is, your pwd. 9-5 The (.) dot means “here”, that is, your pwd. 9-6 Example: To create a new directory named “temp” and to copy mv option file1 file2 First Version the contents of an existing directory named mp1 into temp, This is one version of the mv command. file1 is renamed file2. where option is -i Protects you from overwriting an existing file by asking you > cp -r mp1 temp for a yes or no before it copies a file with an existing name. -
UNIX Workshop Series: Quick-Start Objectives
Part I UNIX Workshop Series: Quick-Start Objectives Overview – Connecting with ssh Command Window Anatomy Command Structure Command Examples Getting Help Files and Directories Wildcards, Redirection and Pipe Create and edit files Overview Connecting with ssh Open a Terminal program Mac: Applications > Utilities > Terminal ssh –Y [email protected] Linux: In local shell ssh –Y [email protected] Windows: Start Xming and PuTTY Create a saved session for the remote host name centos.css.udel.edu using username Connecting with ssh First time you connect Unix Basics Multi-user Case-sensitive Bash shell, command-line Commands Command Window Anatomy Title bar Click in the title bar to bring the window to the front and make it active. Command Window Anatomy Login banner Appears as the first line of a login shell. Command Window Anatomy Prompts Appears at the beginning of a line and usually ends in $. Command Window Anatomy Command input Place to type commands, which may have options and/or arguments. Command Window Anatomy Command output Place for command response, which may be many lines long. Command Window Anatomy Input cursor Typed text will appear at the cursor location. Command Window Anatomy Scroll Bar Will appear as needed when there are more lines than fit in the window. Command Window Anatomy Resize Handle Use the mouse to change the window size from the default 80x24. Command Structure command [arguments] Commands are made up of the actual command and its arguments. command -options [arguments] The arguments are further broken down into the command options which are single letters prefixed by a “-” and other arguments that identify data for the command. -

Windows Command Prompt Cheatsheet
Windows Command Prompt Cheatsheet - Command line interface (as opposed to a GUI - graphical user interface) - Used to execute programs - Commands are small programs that do something useful - There are many commands already included with Windows, but we will use a few. - A filepath is where you are in the filesystem • C: is the C drive • C:\user\Documents is the Documents folder • C:\user\Documents\hello.c is a file in the Documents folder Command What it Does Usage dir Displays a list of a folder’s files dir (shows current folder) and subfolders dir myfolder cd Displays the name of the current cd filepath chdir directory or changes the current chdir filepath folder. cd .. (goes one directory up) md Creates a folder (directory) md folder-name mkdir mkdir folder-name rm Deletes a folder (directory) rm folder-name rmdir rmdir folder-name rm /s folder-name rmdir /s folder-name Note: if the folder isn’t empty, you must add the /s. copy Copies a file from one location to copy filepath-from filepath-to another move Moves file from one folder to move folder1\file.txt folder2\ another ren Changes the name of a file ren file1 file2 rename del Deletes one or more files del filename exit Exits batch script or current exit command control echo Used to display a message or to echo message turn off/on messages in batch scripts type Displays contents of a text file type myfile.txt fc Compares two files and displays fc file1 file2 the difference between them cls Clears the screen cls help Provides more details about help (lists all commands) DOS/Command Prompt help command commands Source: https://technet.microsoft.com/en-us/library/cc754340.aspx. -

Secure Shell Encrypt and Authenticate Remote Connections to Secure Applications and Data Across Open Networks
Product overview OpenText Secure Shell Encrypt and authenticate remote connections to secure applications and data across open networks Comprehensive Data security is an ongoing concern for organizations. Sensitive, security across proprietary information must always be protected—at rest and networks in motion. The challenge for organizations that provide access to applications and data on host systems is keeping the data Support for Secure Shell (SSH) secure while enabling access from remote computers and devices, whether in a local or wide-area network. ™ Strong SSL/TLS OpenText Secure Shell is a comprehensive security solution that safeguards network ® encryption traffic, including internet communication, between host systems (mainframes, UNIX ™ servers and X Window System applications) and remote PCs and web browsers. When ™ ™ ™ ™ Powerful Kerberos included with OpenText Exceed or OpenText HostExplorer , it provides Secure Shell 2 (SSH-2), Secure Sockets Layer (SSL), LIPKEY and Kerberos security mechanisms to ensure authentication security for communication types, such as X11, NFS, terminal emulation (Telnet), FTP support and any TCP/IP protocol. Secure Shell encrypts data to meet the toughest standards and requirements, such as FIPS 140-2. ™ Secure Shell is an add-on product in the OpenText Connectivity suite, which encrypts application traffic across networks. It helps organizations achieve security compliance by providing Secure Shell (SSH) capabilities. Moreover, seamless integration with other products in the Connectivity suite means zero disruption to the users who remotely access data and applications from web browsers and desktop computers. Secure Shell provides support for the following standards-based security protocols: Secure Shell (SSH)—A transport protocol that allows users to log on to other computers over a network, execute commands on remote machines and securely move files from one machine to another. -

Secure Telnet
The following paper was originally published in the Proceedings of the Fifth USENIX UNIX Security Symposium Salt Lake City, Utah, June 1995. STEL: Secure TELnet David Vincenzetti, Stefano Taino, and Fabio Bolognesi Computer Emergency Resource Team Italy Department of Computer Science University of Milan, Italy For more information about USENIX Association contact: 1. Phone: 510 528-8649 2. FAX: 510 548-5738 3. Email: [email protected] 4. WWW URL: http://www.usenix.org STEL Secure TELnet David Vincenzetti Stefano Taino Fabio Bolognesi fvince k taino k b ologdsiunimiit CERTIT Computer Emergency Response Team ITaly Department of Computer Science University of Milan ITALY June Abstract Eavesdropping is b ecoming rampant on the Internet We as CERTIT have recorded a great numb er of sning attacks in the Italian community In fact sning is the most p opular hackers attack technique all over the Internet This pap er presents a secure telnet implementation whichhas b een designed by the Italian CERT to makeeavesdropping ineective to remote terminal sessions It is not to b e considered as a denitive solution but rather as a bandaid solution to deal with one of the most serious security threats of the moment Intro duction STEL stands for Secure TELnet We started developing STEL at the University of Milan when we realized that eavesdropping was a very serious problem and we did not like the freeware solutions that were available at that time It was ab out three years ago Still as far as we know e tapping problem and there are no really satisfying -

Telnet Client 5.11 Ssh Support
TELNET CLIENT 5.11 SSH SUPPORT This document provides This document describes how to install and configure SSH support in Wavelink Telnet Client 5.11. information on the SSH support available in Telnet Client 5.11 OVERVIEW OF SSH SUPPORT Secure Shell (SSH) is a protocol developed for transmitting private information over the Internet. SSH OVERVIEW encrypts data that is transferred over the Telnet session. • Overview of SSH The Telnet Client supports SSH version 1 and 2 and will automatically select the most secure protocol Support that the SSH server supports. • Installing Windows SSH Support This document describes the following: • Configuring the host • Installing Windows SSH support utility profile for SSH • Configuring the host profile for SSH support support • Deploying Windows • Deploying Windows SSH support to the device through Avalanche or ActiveSync SSH Support • Revision History INSTALLING WINDOWS SSH SUPPORT Installing SSH support is a two-step process. First, install SSH support on the PC from which you will deploy Telnet. Once you install SSH support on the PC, use Avalanche or ActiveSync to deploy the utility to the device. To install SSH support on your PC: 1. Obtain the installation executable for SSH support. NOTE: To obtain the Wavelink SSH support utility install, go to http://www.wavelink.com/downloads/ files/sshagreement.aspx. 2. Install SSH support on the PC from which you will deploy the Telnet Client. CONFIGURING THE HOST PROFILE FOR SSH SUPPORT SSH support is configured from the Host Profiles window of the configuration utility. NOTE: SSH is only an active option if SSH support has been installed on the PC running the Telnet Client configuration utility.