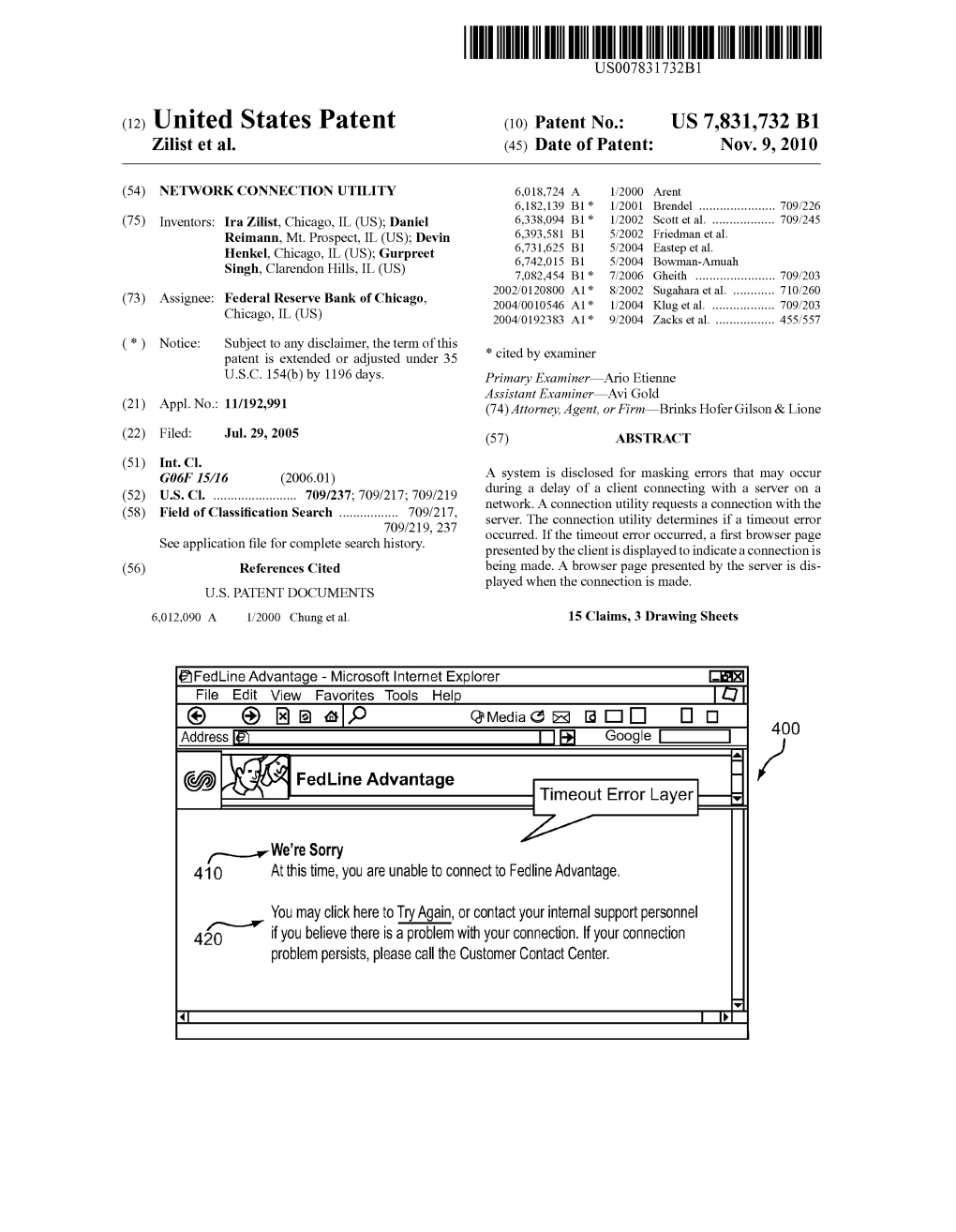
(2) G: 9 Timeout Error Layer —T
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Commands to Control Device
Commands to Control Device New OTA firmware upgrade command. To try it via over-the-air update, use these commands: > fwe > fwd B6FMA186 The board will reboot after the first command, this is normal. After the second command wait 1-3 minutes (seems like a long time). After it resets again, go back to BlueFruit and press "info" the software should be 3.0.186 The default wakeup interval is still 4 hours (14400 seconds). To configure a unit for a different wakeup interval: >wakt 600 (this would be 60*10 = 10 minutes) No beeps (Command to turn off the beeps) nvap 6 120000 14400000 15000 5000 0 223 1 3 Command to Restore Beeps nvap 6 120000 14400000 15000 5000 0 223 1 65535 Main Menu commands ---- SubMenus -------------------------- >i - I2C menu >l - Log menu >M - Modem menu ---- Device Control Cmds --------------- >D [n] - set debug level to [n] >info - Show device info >cota - CDMA OTA reprovision >svrm [name] - Set server main >nvmr - Non-volatile memory revert >t - show system uptime >rst - Hard reset ---- General Cmds ---------------------- >c [str] - Execute remote command manually >batq - Query battery state >slp - Go to sleep immediately >slpt [n] - Set sleep timeout to [n] seconds >wakt [n] - Set wake timeout to [n] hours >sus - Suspend immediately >sts - Show statistics and send to server >bt [n] - Bluetooth disable/enable: n=0/1 >dsms [n] - DebugSMS configure 0/1=disabled/enabled >wss [p] [s] - WiMM Server Send [p]ort, [s]tring >wsr - WiMM Server Recv ---- Pos/Log Cmds ---------------------- >pn - Position now >plc {i} {t} - Position log ctrl, [i]nterval, [t]ripId Stop Logging >pla {i} {t} - Position log auto, [i]nterval, [t]ripId >plb {n} - Position log batch [n] records >ple - Position log erase --- Alarm Cmds ------------------------ >alm [m] - Alarm mode: m=0/1/2: Off/On/FireNow ---- Firmware Cmds --------------------- >fwd [v] - Firmware Download (WIMM{v}.hex) >fwl {i} - Firmware Launch (i=0/1: ImgA/B) >fwe - Firmware Erase (ImgB) To change the alarm delay You must be running firmware 145 or later. -
Administering Unidata on UNIX Platforms
C:\Program Files\Adobe\FrameMaker8\UniData 7.2\7.2rebranded\ADMINUNIX\ADMINUNIXTITLE.fm March 5, 2010 1:34 pm Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta UniData Administering UniData on UNIX Platforms UDT-720-ADMU-1 C:\Program Files\Adobe\FrameMaker8\UniData 7.2\7.2rebranded\ADMINUNIX\ADMINUNIXTITLE.fm March 5, 2010 1:34 pm Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Notices Edition Publication date: July, 2008 Book number: UDT-720-ADMU-1 Product version: UniData 7.2 Copyright © Rocket Software, Inc. 1988-2010. All Rights Reserved. Trademarks The following trademarks appear in this publication: Trademark Trademark Owner Rocket Software™ Rocket Software, Inc. Dynamic Connect® Rocket Software, Inc. RedBack® Rocket Software, Inc. SystemBuilder™ Rocket Software, Inc. UniData® Rocket Software, Inc. UniVerse™ Rocket Software, Inc. U2™ Rocket Software, Inc. U2.NET™ Rocket Software, Inc. U2 Web Development Environment™ Rocket Software, Inc. wIntegrate® Rocket Software, Inc. Microsoft® .NET Microsoft Corporation Microsoft® Office Excel®, Outlook®, Word Microsoft Corporation Windows® Microsoft Corporation Windows® 7 Microsoft Corporation Windows Vista® Microsoft Corporation Java™ and all Java-based trademarks and logos Sun Microsystems, Inc. UNIX® X/Open Company Limited ii SB/XA Getting Started The above trademarks are property of the specified companies in the United States, other countries, or both. All other products or services mentioned in this document may be covered by the trademarks, service marks, or product names as designated by the companies who own or market them. License agreement This software and the associated documentation are proprietary and confidential to Rocket Software, Inc., are furnished under license, and may be used and copied only in accordance with the terms of such license and with the inclusion of the copyright notice. -

Webserver Cannot Be Started / No Web Access EAGLE20 / Eagleone
Knowledgebase > Products > Classic Firewalls > Webserver cannot be started / No web access EAGLE20 / EAGLEOne Webserver cannot be started / No web access EAGLE20 / EAGLEOne - 2018-02-09 - Classic Firewalls At the first startup of a brand new EAGLE or at the first startup after “clear certificates” the web certificates are generated. Affected products are EAGLE20 and EAGLEOne in rel. 05.3.00. If the power is removed during the certificate generation is in progress the webserver cannot be started and therefore no web access is possible. The cli command 'show login' displays the following output: !(Hirschmann EAGLE One) #show login Login parameters ---------------- Access per SSH..........................enabled SSH Access port number..................22 DSA Fingerprint for SSH.................""xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:ab:ab:ab:ab:0f "" RSA Fingerprint for SSH.................""xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:5e "" Access per Web (HTTPS)..................disabled Web Access port number (HTTPS)..........443 SNMP version 1..........................disabled SNMP version 2..........................disabled SNMP port number........................161 SNMP over HTTPS tunneling...............disabled RADIUS auth. of SNMP v3 local users.....disabled Inactivity timeout Web (minutes)........5 Inactivity timeout serial (minutes).....5 Inactivity timeout SSH (minutes)........5 Login prompt............................""Hirschmann EAGLE One"" Login banner............................"""" 23: 2013-01-01 01:00:01 [tCfgMgrTask, CRITICAL, WEB-S, 0x02080014] Web Server - start of web server failed 24: 2013-01-01 01:00:01 [tCfgMgrTask, ERROR, WEB-S, 0x02080028] Web Server - directory for https server certificate could not be created Possible solutions: 1. Reformat the flash file system in sysMon1 and to put the operating firmware on the device again. -

SLC Console Manager User Guide Available At
SLC™ Console Manager User Guide SLC8 SLC16 SLC32 SLC48 Part Number 900-449 Revision J July 2014 Copyright and Trademark © 2014 Lantronix, Inc. All rights reserved. No part of the contents of this book may be transmitted or reproduced in any form or by any means without the written permission of Lantronix. Lantronix is a registered trademark of Lantronix, Inc. in the United States and other countries. SLC, SLB, SLP, SLM, Detector and Spider are trademarks of Lantronix, Inc. Windows and Internet Explorer are registered trademarks of Microsoft Corporation. Firefox is a registered trademark of the Mozilla Foundation. Chrome is a trademark of Google, Inc. All other trademarks and trade names are the property of their respective holders. Warranty For details on the Lantronix warranty replacement policy, please go to our web site at http://www.lantronix.com/support/warranty. Open Source Software Some applications are Open Source software licensed under the Berkeley Software Distribution (BSD) license or the GNU General Public License (GPL) as published by the Free Software Foundation (FSF). Redistribution or incorporation of BSD or GPL licensed software into hosts other than this product must be done under their terms. A machine readable copy of the corresponding portions of GPL licensed source code may be available at the cost of distribution. Such Open Source Software is distributed WITHOUT ANY WARRANTY, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. See the GPL and BSD for details. A copy of the licenses is available from Lantronix. The GNU General Public License is available at http://www.gnu.org/licenses/. -

TEE Internal Core API Specification V1.1.2.50
GlobalPlatform Technology TEE Internal Core API Specification Version 1.1.2.50 (Target v1.2) Public Review June 2018 Document Reference: GPD_SPE_010 Copyright 2011-2018 GlobalPlatform, Inc. All Rights Reserved. Recipients of this document are invited to submit, with their comments, notification of any relevant patents or other intellectual property rights (collectively, “IPR”) of which they may be aware which might be necessarily infringed by the implementation of the specification or other work product set forth in this document, and to provide supporting documentation. The technology provided or described herein is subject to updates, revisions, and extensions by GlobalPlatform. This documentation is currently in draft form and is being reviewed and enhanced by the Committees and Working Groups of GlobalPlatform. Use of this information is governed by the GlobalPlatform license agreement and any use inconsistent with that agreement is strictly prohibited. TEE Internal Core API Specification – Public Review v1.1.2.50 (Target v1.2) THIS SPECIFICATION OR OTHER WORK PRODUCT IS BEING OFFERED WITHOUT ANY WARRANTY WHATSOEVER, AND IN PARTICULAR, ANY WARRANTY OF NON-INFRINGEMENT IS EXPRESSLY DISCLAIMED. ANY IMPLEMENTATION OF THIS SPECIFICATION OR OTHER WORK PRODUCT SHALL BE MADE ENTIRELY AT THE IMPLEMENTER’S OWN RISK, AND NEITHER THE COMPANY, NOR ANY OF ITS MEMBERS OR SUBMITTERS, SHALL HAVE ANY LIABILITY WHATSOEVER TO ANY IMPLEMENTER OR THIRD PARTY FOR ANY DAMAGES OF ANY NATURE WHATSOEVER DIRECTLY OR INDIRECTLY ARISING FROM THE IMPLEMENTATION OF THIS SPECIFICATION OR OTHER WORK PRODUCT. Copyright 2011-2018 GlobalPlatform, Inc. All Rights Reserved. The technology provided or described herein is subject to updates, revisions, and extensions by GlobalPlatform. -

Powerview Command Reference
PowerView Command Reference TRACE32 Online Help TRACE32 Directory TRACE32 Index TRACE32 Documents ...................................................................................................................... PowerView User Interface ............................................................................................................ PowerView Command Reference .............................................................................................1 History ...................................................................................................................................... 12 ABORT ...................................................................................................................................... 13 ABORT Abort driver program 13 AREA ........................................................................................................................................ 14 AREA Message windows 14 AREA.CLEAR Clear area 15 AREA.CLOSE Close output file 15 AREA.Create Create or modify message area 16 AREA.Delete Delete message area 17 AREA.List Display a detailed list off all message areas 18 AREA.OPEN Open output file 20 AREA.PIPE Redirect area to stdout 21 AREA.RESet Reset areas 21 AREA.SAVE Save AREA window contents to file 21 AREA.Select Select area 22 AREA.STDERR Redirect area to stderr 23 AREA.STDOUT Redirect area to stdout 23 AREA.view Display message area in AREA window 24 AutoSTOre .............................................................................................................................. -

U-Connectxpress at Commands Manual
u-connectXpress AT commands manual Abstract u-blox AT commands reference manual for the short range stand-alone modules. This document lists both the standard and proprietary AT- commands for u-connectXpress based modules with Bluetooth low energy, Bluetooth BR/EDR and Wi-Fi. www.u-blox.com UBX-14044127 - R48 C1-Public u-connectXpress - AT commands manual Document information Title u-connectXpress Subtitle Document type AT commands manual Document number UBX-14044127 Revision and date R48 06-Sep-2021 Disclosure restriction C1-Public u-blox reserves all rights to this document and the information contained herein. Products, names, logos and designs described herein may in whole or in part be subject to intellectual property rights. Reproduction, use, modification or disclosure to third parties of this document or any part thereof without the express permission of u-blox is strictly prohibited. The information contained herein is provided “as is” and u-blox assumes no liability for the use of the information. No warranty, either express or implied, is given, including but not limited, with respect to the accuracy, correctness, reliability and fitness for a particular purpose of the information. This document may be revised by u-blox at any time. For most recent documents, visit www.u-blox.com. Copyright © u-blox AG u-blox is a registered trademark of u-blox Holding AG in the EU and other countries. UBX-14044127 - R48 Page 2 of 176 u-connectXpress - AT commands manual Preface Applicable products This document applies to the following products: -

Command-Line IP Utilities This Document Lists Windows Command-Line Utilities That You Can Use to Obtain TCP/IP Configuration Information and Test IP Connectivity
Guide to TCP/IP: IPv6 and IPv4, 5th Edition, ISBN 978-13059-4695-8 Command-Line IP Utilities This document lists Windows command-line utilities that you can use to obtain TCP/IP configuration information and test IP connectivity. Command parameters and uses are listed for the following utilities in Tables 1 through 9: ■ Arp ■ Ipconfig ■ Netsh ■ Netstat ■ Pathping ■ Ping ■ Route ■ Tracert ARP The Arp utility reads and manipulates local ARP tables (data link address-to-IP address tables). Syntax arp -s inet_addr eth_addr [if_addr] arp -d inet_addr [if_addr] arp -a [inet_address] [-N if_addr] [-v] Table 1 ARP command parameters and uses Parameter Description -a or -g Displays current entries in the ARP cache. If inet_addr is specified, the IP and data link address of the specified computer appear. If more than one network interface uses ARP, entries for each ARP table appear. inet_addr Specifies an Internet address. -N if_addr Displays the ARP entries for the network interface specified by if_addr. -v Displays the ARP entries in verbose mode. -d Deletes the host specified by inet_addr. -s Adds the host and associates the Internet address inet_addr with the data link address eth_addr. The physical address is given as six hexadecimal bytes separated by hyphens. The entry is permanent. eth_addr Specifies physical address. if_addr If present, this specifies the Internet address of the interface whose address translation table should be modified. If not present, the first applicable interface will be used. Pyles, Carrell, and Tittel 1 Guide to TCP/IP: IPv6 and IPv4, 5th Edition, ISBN 978-13059-4695-8 IPCONFIG The Ipconfig utility displays and modifies IP address configuration information. -

Timeout Control in Distributed Systems Using Perturbation Analysis
2011 50th IEEE Conference on Decision and Control and European Control Conference (CDC-ECC) Orlando, FL, USA, December 12-15, 2011 Timeout Control in Distributed Systems Using Perturbation Analysis Ali Kebarighotbi and Christos G. Cassandras Division of Systems Engineering and Center for Information and Systems Engineering Boston University Brookline, MA 02446 [email protected],[email protected] Abstract— Timeout control is a simple mechanism used when direct feedback is either impossible, unreliable, or too costly, as is often the case in distributed systems. Its effectiveness is determined by a timeout threshold parameter and our goal is to quantify the effect of this parameter on the behavior of such systems. In this paper, we consider a basic communi- cation system with timeout control, model it as a stochastic flow system, and use Infinitesimal Perturbation Analysis to Fig. 1. Timeout controlled distributed system determine the sensitivity of a “goodput” performance metric with respect to the timeout threshold parameter. In conjunction with a gradient-based scheme, we show that we can determine an optimal value of this parameter. Some numerical examples with an action Ai, a proper response to a timeout event is are included. normally related to the state and action at time t − θi.A simple example is repeating Ai at t because no desirable NTRODUCTION I. I response has been observed in [t − θi; t). Thus, a controller Timeout control is a simple mechanism used in many must have some information about both current and past systems where direct feedback is either impossible, unreli- states and actions of the system. -

System Analysis and Tuning Guide System Analysis and Tuning Guide SUSE Linux Enterprise Server 15 SP1
SUSE Linux Enterprise Server 15 SP1 System Analysis and Tuning Guide System Analysis and Tuning Guide SUSE Linux Enterprise Server 15 SP1 An administrator's guide for problem detection, resolution and optimization. Find how to inspect and optimize your system by means of monitoring tools and how to eciently manage resources. Also contains an overview of common problems and solutions and of additional help and documentation resources. Publication Date: September 24, 2021 SUSE LLC 1800 South Novell Place Provo, UT 84606 USA https://documentation.suse.com Copyright © 2006– 2021 SUSE LLC and contributors. All rights reserved. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or (at your option) version 1.3; with the Invariant Section being this copyright notice and license. A copy of the license version 1.2 is included in the section entitled “GNU Free Documentation License”. For SUSE trademarks, see https://www.suse.com/company/legal/ . All other third-party trademarks are the property of their respective owners. Trademark symbols (®, ™ etc.) denote trademarks of SUSE and its aliates. Asterisks (*) denote third-party trademarks. All information found in this book has been compiled with utmost attention to detail. However, this does not guarantee complete accuracy. Neither SUSE LLC, its aliates, the authors nor the translators shall be held liable for possible errors or the consequences thereof. Contents About This Guide xii 1 Available Documentation xiii -

June 2021 Uptime Policy
June 2021 Uptime Policy The xx network is targeting 80% Uptime, 94% Round Success Rate and .5% Realtime Timeout requirements for June 2021. This means that generally, a node needs to be online for at least 80% of the month of May 2021, successfully complete at least 94% of the rounds the node participates in and not fail more than .5% of the Realtime phase of a round to receive compensation for the month. A node will be considered online as long as it is pinging the permissioning server regularly. If at the dashboard, your node is listed as either “Online” or “Error”, it is still online for the purpose of compensation for the month of June 2021. On the individual node pages on the dashboard there are monthly and weekly uptime metrics to inform you of your progress. Node uptime is not tracked while xx network’s servers are down and such periods will not be counted against the minimum. In the event the network is down due to a software update or a bug caused by the xx network team, those periods will also not count towards the 80% uptime minimum. Grace Period Nodes who are joining the network for the first time this month (Orange Team X) will have the entire month of June 2021 as a grace period. This only includes nodes who registered initially to start in June 2021. If this month is a grace period for your node, you will receive an email notifying you. The grace period in June 2021 is designed to allow new nodes adequate time to onboard. -

WLAN Timeouts
WLAN Timeouts • Timeout for Disabled Clients, on page 1 • Session Timeouts, on page 1 • User Idle Timeout per WLAN, on page 3 • Address Resolution Protocol Timeout, on page 4 • Authentication of Sleeping Clients, on page 4 Timeout for Disabled Clients You can configure a timeout for disabled clients. Clients who fail to authenticate three times when attempting to associate are automatically disabled from further association attempts. After the timeout period expires, the client is allowed to retry authentication until it associates or fails authentication and is excluded again. Use these commands to configure a timeout for disabled clients. Configuring Timeout for Disabled Clients (CLI) • Configure the timeout for disabled clients by entering the config wlan exclusionlist wlan_id timeout command. The valid timeout range is 1 to 2147483647 seconds. A value of 0 permanently disables the client. • Verify the current timeout by entering the show wlan command. Session Timeouts You can configure a WLAN with a session timeout. The session timeout is the maximum time for a client session to remain active before requiring reauthorization. If a WLAN is configured with Layer 2 security, for example WPA2-PSK, and a Layer 3 authentication is also configured, the WLAN session timeout value is overridden with the dot1x reauthentication timeout value. If apf reauthentication timeout value is greater than 65535, the WLAN session timeout is by default set to 65535; else, the configured dot1x reauthentication timeout value is applied as the WLAN session timeout. This section contains the following subsections: WLAN Timeouts 1 WLAN Timeouts Configuring a Session Timeout (GUI) Configuring a Session Timeout (GUI) Configurable session timeout range is: • 300-86400 for 802.1X(EAP) • 0-65535 for all other security types Note If you configure a session-timeout of 0, it means 86400 seconds for 802.1X (EAP), and it disables the session-timeout for all other security types.