Ibm Linux Tutorials
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Filesystem Maintenance
Filesystem Maintenance René Serral-Gracià Xavier Martorell-Bofill1 1Universitat Politècnica de Catalunya (UPC) May 26, 2014 Introduction Filesystems Disk verification LVM Backups Lectures 1 System administration introduction 2 Operating System installation 3 User management 4 Application management 5 System monitoring 6 Filesystem Maintenance 7 Local services 8 Network services 9 Security and Protection 10 Virtualization R. Serral-Gracià, et. al Filesystem 2 Introduction Filesystems Disk verification LVM Backups Outline 1 Introduction Goals 2 Filesystems 3 Disk verification 4 Logical Volume Manager (LVM) 5 Backups R. Serral-Gracià, et. al Filesystem 3 Introduction Filesystems Disk verification LVM Backups Goals Knowledge Filesystems Backup tools Backup media Abilities Filesystem ampliation Filesystem verification Perform and restore backups R. Serral-Gracià, et. al Filesystem 4 Introduction Filesystems Disk verification LVM Backups Outline 1 Introduction 2 Filesystems 3 Disk verification 4 Logical Volume Manager (LVM) 5 Backups R. Serral-Gracià, et. al Filesystem 5 Introduction Filesystems Disk verification LVM Backups Filesystems (I) FAT (FAT16) –> DOS Small disks (< 4GB) File names 8+3 FAT32 (VFAT) –> Win95 Larger disks Long filenames Partial definition of soft-links No owner or file access privileges exFAT FAT32 Extension Theoretical maximum capacity of 64ZiB (512TiB real) NTFS –> WinNT, XP, Vista, Windows 7 Integrates ownership and privileges (create, modify, access...) Maps to Windows NT security model R. Serral-Gracià, et. al Filesystem 6 Introduction Filesystems Disk verification LVM Backups Filesystems (II) ext2 UNIX Filesystem Soft/hard links Access privileges Long filenames ext3 Adds journaling (eases error recovery) reiserfs Files and directories organized similarly to a database Features journaling Very efficient in small files No internal block fragmentation R. -

Systems Programmer, Heal Thy PC Part 2: Tune-Up Time Session
Systems Programmer, Heal Thy PC Part 2: Tune-Up Time Session 10254, Thursday, March 15, 2012 James Willette, Sunrise e-Services Victor Freyer, Lemon Bay Computer Service Do-It-Yourself PC Tune-Up • Why do it yourself? • Personal privacy • Can’t live without your computer • Sense of accomplishment • Second career? • The Geek Squad™ wants to charge what!? • What do you need? • A plan • A toolkit full of free tools Simple 15-Step Process • Boot to Windows • Remove unneeded • Shutdown Windows programs from startup • Evaluate hard drive health • Remove Internet Explorer • Backup Windows partition toolbars • • Virus review and removal Remove temporary files • • Correct file system errors Defragment Windows • partition Windows System File • Checker Update system BIOS • • Uninstall unnecessary Update programs programs • Install anti-virus software Boot and Shutdown • Computer must not be Suspended or Hibernating • Likelihood of corrupting your file system • Benchmark startup time • So you can compare when you’re done • Shutdown to insure a clean file system close • Save yourself from problems later Evaluate Hard Drive Health • Boot SystemRescueCD • Download the live Linux cd www.sysresccd.org • Burn with isorecorder.alexfeinman.com • Review hard drive SMART statistics • smartctl -a /dev/sda • Run SMART self test • smartctl -t short /dev/sda • smartctl -l selftest /dev/sda SMART Statistics • smartctl -a /dev/sda Model Family: Western Digital Scorpio family Device Model: WDC WD800BEVE-00UYT0 Serial Number: WD-WXE408L96343 Firmware Version: 01.04A01 User Capacity: 80,026,361,856 bytes ... SMART Attributes Data Structure revision number: 16 Vendor Specific SMART Attributes with Thresholds: ID# ATTRIBUTE_NAME FLAG VALUE WORST THRESH TYPE UPDATED WHEN_FAILED RAW_VALUE .. -

Oracle® Linux 7 Managing File Systems
Oracle® Linux 7 Managing File Systems F32760-07 August 2021 Oracle Legal Notices Copyright © 2020, 2021, Oracle and/or its affiliates. This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. If this is software or related documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, then the following notice is applicable: U.S. GOVERNMENT END USERS: Oracle programs (including any operating system, integrated software, any programs embedded, installed or activated on delivered hardware, and modifications of such programs) and Oracle computer documentation or other Oracle data delivered to or accessed by U.S. Government end users are "commercial computer software" or "commercial computer software documentation" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, the use, reproduction, duplication, release, display, disclosure, modification, preparation of derivative works, and/or adaptation of i) Oracle programs (including any operating system, integrated software, any programs embedded, installed or activated on delivered hardware, and modifications of such programs), ii) Oracle computer documentation and/or iii) other Oracle data, is subject to the rights and limitations specified in the license contained in the applicable contract. -

Netinfo 2009-06-11 Netinfo 2009-06-11
Netinfo 2009-06-11 Netinfo 2009-06-11 Microsoft släppte 2009-06-09 tio uppdateringar som täpper till 31 stycken säkerhetshål i bland annat Windows, Internet Explorer, Word, Excel, Windows Search. 18 av buggfixarna är märkta som kritiska och elva av dem är märkta som viktiga, uppdateringarna finns för både servrar och arbetsstationer. Säkerhetsuppdateringarna finns tillgängliga på Windows Update. Den viktigaste säkerhetsuppdateringen av de som släpptes är den för Internet Explorer 8. Netinfo 2009-06-11 Security Updates available for Adobe Reader and Acrobat Release date: June 9, 2009 Affected software versions Adobe Reader 9.1.1 and earlier versions Adobe Acrobat Standard, Pro, and Pro Extended 9.1.1 and earlier versions Severity rating Adobe categorizes this as a critical update and recommends that users apply the update for their product installations. These vulnerabilities would cause the application to crash and could potentially allow an attacker to take control of the affected system. Netinfo 2009-06-11 SystemRescueCd Description: SystemRescueCd is a Linux system on a bootable CD-ROM for repairing your system and recovering your data after a crash. It aims to provide an easy way to carry out admin tasks on your computer, such as creating and editing the partitions of the hard disk. It contains a lot of system tools (parted, partimage, fstools, ...) and basic tools (editors, midnight commander, network tools). It is very easy to use: just boot the CDROM. The kernel supports most of the important file systems (ext2/ext3/ext4, reiserfs, reiser4, btrfs, xfs, jfs, vfat, ntfs, iso9660), as well as network filesystems (samba and nfs). -

Managing Network File Systems in Oracle® Solaris 11.4
Managing Network File Systems in ® Oracle Solaris 11.4 Part No: E61004 August 2021 Managing Network File Systems in Oracle Solaris 11.4 Part No: E61004 Copyright © 2002, 2021, Oracle and/or its affiliates. This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. If this is software or related documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, then the following notice is applicable: U.S. GOVERNMENT END USERS: Oracle programs (including any operating system, integrated software, any programs embedded, installed or activated on delivered hardware, and modifications of such programs) and Oracle computer documentation or other Oracle data delivered to or accessed by U.S. Government end users are "commercial computer software" or "commercial computer software documentation" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, the use, reproduction, duplication, release, display, disclosure, modification, preparation of derivative works, and/or adaptation of i) Oracle programs (including any operating system, integrated software, any programs embedded, installed or activated on delivered hardware, and modifications of such programs), ii) Oracle computer documentation and/or iii) other Oracle data, is subject to the rights and limitations specified in the license contained in the applicable contract. -

Systems Programmer, Heal Thy PC Part 1: Virus Removal Session
Systems Programmer, Heal Thy PC Part 1: Virus Removal Session 10255, Tuesday, March 13, 2012 James Willette, Sunrise e-Services Victor Freyer, Lemon Bay Computer Service Disclaimer • I use “virus” to refer to the whole class of malware that may infect your PC. • Purists would say that virii are programs that spread themselves. • Most of today’s malware is installed by the end user, and by definition is not a virus. Do-It-Yourself Virus Removal • Why do it yourself? • Company has Draconian rules about PC use • Anger and disbelief • Pride • Second career? • The Geek Squad™ wants to charge what!? • What do you need? • Clean boot environment • An eye for what’s unusual • A toolkit full of free tools So you think you have a virus? • Signs of malware • Computer is slow • Click on a Google result and go to some unrelated page • Lots of “undeliverable message” alerts in your inbox • “Warning, you have 732 viruses!!!!!” • Unable to run Windows updates • Unable to update your anti-virus program • Unable to connect to the Internet • Excessive TCP connections popup warning • “Do you want to allow this program to run?” So you think you have a virus? • Simple five step process • Turn the machine off – no graceful shutdown • Boot to a clean environment • Back up the boot drive • Disable the virus program • Fix corrupted registry and configuration files Boot to a Clean Envionment • WinBuilder – freeware to build Windows boot disks http://reboot.pro/forum/22 (registration required) • XP, Vista, Windows 7, Windows 8, Driveimage XML • EaseUS Todo Backup -
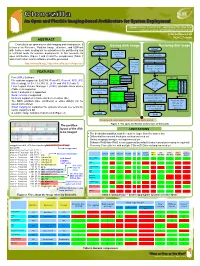
Clonezilla an Open and Flexible Imaging-Based Architecture for System Deployment
Clonezilla An Open and Flexible Imaging-based Architecture for System Deployment Steven Shiau, Ceasar Sun, Jazz Wang, Thomas Tsai {steven , ceasar , jazz , thomas }@ nchc . org . tw Free Software Lab NCHC, Taiwan ABSTRACT Clonezilla is an open-source disk imaging and cloning suite. It Saving disk image Restoring disk image is based on Partclone, Partition Image, ntfsclone, and UDPcast Start with features such as plug-ins for subsystems like partitioning and Start a multicast mode for massive deployments. In this research, its Parse partition Find the file table system of Read image open architecture (Figure 1 and 2) and the comparisons (Table 1 device and 2) with other similar software would be presented. NO Create partition table Use dd http://clonezilla.org , http://clonezilla.sourceforge.net/ to save Smart Create LV if LV Find the copying? image Device to image found in (partition stdout image dir FEATURES /LV) YES Decide partclone Free (GPL) Software device YES partimage File systems supported: Ext2/3/4, ReiserFS, Reiser4, XFS, JFS, imaging p p Save Find the Decide n ntfsclone a a engine t MBR/GPT data r Btrfs (testing), HFS+, FAT, NTFS , UFS+ and VMFS (Table 1) f image r t device s t i c c Linux Logical Volume Manager 2 (LVM2) stackable block device of m l imaging l o o Save device device a n n (Table 2) is supported engine g e Save partition image to stdout e e Grub 1 and grub 2 is supported table gzip NO Serial console is supported Decide bzip2 Tune the file compressing lzma Multicast supported in Clonezilla Server Edition (SE) engine lzip system size to fit Save xz partition size Restore the The MBR, partition table, partition(s) or entire disk(s) can be hardware info image of saved and restored Save stdin as Reinstall grub device to Smart copying on supported file systems whereas use sector-to- file in the device sector copying via dd image dir if assigned A tunable image format is implemented (Figure 2) End End Imaging and compressing engines can be easily added Figure 1. -

Linux Based Diskless System Using RSYNC Algorithm
International Journal of Computer Applications (0975 – 8887) Volume 155 – No 3, December 2016 Linux based Diskless System using RSYNC Algorithm August Anthony N. Balute Dennis B. Gonzales, PhD CAP College Foundation Inc. University of the East Makati, Philippines Manila, Philippines Mateo D. Macalaguing Jr., Ed.D Caroline J. Aga-ab CAP College Foundation Inc. AMA University Makati Philippines Quezon City, Philippines ABSTRACT Centers, Offices, Cybercafe, Karaoke, and can likewise be The objective of this venture is to give a cost effective open utilized as a part of bunch registering. Diskless workstation is source Remote Desktop based registering environment to a PC framework with no plate drives introduced locally along clients by utilizing Virtualization Technology and existing these lines booting it's working framework from a server in open source programming and apparatuses. In this venture, we the neighborhood. Now and then when a PC framework is have utilized LTSP (Linux Terminal Server Project) to get to having a circle drive yet don't utilizing it that framework is Remote Desktop and Xen hypervisor to give virtual desktop additionally called a diskless workstation. Diskless environment at server. A client gets a customized desktop as a Workstations give less expensive however more secure VM (Virtual Machine) running over remote server. It is not systems administration answers for undertakings. Qualities of the same as the old Remote Desktop arrangements in a route diskless workstations are, the working framework is stacked that rather than a login session on single OS remote server, from the server when booting up. Clearly the various client will get a completely fledged desktop with fancied OS. -

Disk Imaging Technologies
Disk Imaging Technologies Backup and Restoration Challenges Topics • Manufacture Firmware Changes • File System Landscape – UEFI – Introduction to GUID Partition Table (GPT) – Partitions & Limitations • Imaging Utilities Windows & Linux • Full Disk Encryption • Source Web-Links Manufacture Firmware Changes • Industry push to a new standard: – BIOS vs. UEFI • UEFI is to replace and extend the old BIOS firmware. • UEFI is not a new thing. Intel has been working in EFI/UEFI since mid 1990s, and there are vendors like HP or Apple that provided EFI machines since a long time ago. But it is when Microsoft announced Windows 8 that UEFI became the required way to boot the new certified machines. • Secure boot is an extension of UEFI. One of the key points of UEFI is that it can be extended. UEFI has an internal virtual machine that is independent of the architecture that it is using. The standard accepts special binary files compiled for this virtual machine (EFI binaries) that can be executed inside the environment. These binaries can be device drivers, applications or extensions to the UEFI standard. UEFI, in some sense, is like a small operative system that runs when the machine is powered on and whose main task is to find and load another operating system. Unified Extensible Firmware Interface Unified Extensible Firmware Interface (UEFI) is meant as a replacement for the Basic Input/Output System (BIOS) firmware interface ● Initially (1998) designed by Intel for Itanium processor ● Since 2005 managed by the Unified EFI Forum (uefi.org) Source: http://loadays.org/archives/2013/static/slides/Integrating-UEFI-into-rear.pdf Why UEFI? • BIOS has its (aging) limitations – 16-bit processes – max. -

The Ultimate Guide to Hard Drive Partitioning
Home SQL Server Cloud Computing Windows Server Cisco Exchange Windows 7 Active Directory Virtualization Forums IT Job Board Get Our FREE Newsletter! Search Site Gain access to white The Ultimate Guide to Hard Drive Partitioning papers, special offers and by Daniel Petri - March 11, 2009 the most recent IT tips! Printer Friendly Version Sponsors Email Address Disk partitioning divides the data storage space of a hard disk into separate areas referred to as Sign Up Now! Windows Application 'partitions'. Partitions are usually created when the hard disk is first being prepared for usage. Once a Monitoring Made Easy disk is divided into partitions, directories and files may be stored on them. Because of later changes on Quick Links the computer and operating system, often an administrator or power user will be faced with the need to Knowledge Base resize partitions, create new partitions in the unallocated space, and sometimes even undelete Take the guesswork out of Backup & Storage partitions that were previously removed or deleted. which WMI counters to use Security for apps like Microsoft® Active Directory Active Directory™ and Cisco and Routing Hard disk partitioning tools will allow you to create additional partitions from existing ones by resizing SharePoint™. SolarWinds Windows Networking FREE WMI Monitor makes it Exchange Server the existing partitions and creating empty, un-used space on which you can create new partitions. The easy! Download this FREE Virtualization desktop tool now! Windows Server 2008 most important aspect of such tools is their ability to do this without losing your data that is currently on Windows 7 your existing partitions. -

Lustre 1.8 Operations Manual
Lustre™ 1.8 Operations Manual Part No. 821-0035-12 Lustre manual version: Lustre_1.8_man_v1.4 June 2011 Copyright© 2007-2010 Sun Microsystems, Inc., 4150 Network Circle, Santa Clara, California 95054, U.S.A. All rights reserved. U.S. Government Rights - Commercial software. Government users are subject to the Sun Microsystems, Inc. standard license agreement and applicable provisions of the FAR and its supplements. Sun, Sun Microsystems, the Sun logo and Lustre are trademarks or registered trademarks of Sun Microsystems, Inc. in the U.S. and other countries. UNIX is a registered trademark in the U.S. and other countries, exclusively licensed through X/Open Company, Ltd. Products covered by and information contained in this service manual are controlled by U.S. Export Control laws and may be subject to the export or import laws in other countries. Nuclear, missile, chemical biological weapons or nuclear maritime end uses or end users, whether direct or indirect, are strictly prohibited. Export or reexport to countries subject to U.S. embargo or to entities identified on U.S. export exclusion lists, including, but not limited to, the denied persons and specially designated nationals lists is strictly prohibited. DOCUMENTATION IS PROVIDED "AS IS" AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. This work is licensed under a Creative Commons Attribution-Share Alike 3.0 United States License. To view a copy of this license and obtain more information about Creative Commons licensing, visit Creative Commons Attribution-Share Alike 3.0 United States or send a letter to Creative Commons, 171 2nd Street, Suite 300, San Francisco, California 94105, USA. -

DIGILIANT Windows Storage Server 2003 R2
DIGILIANT Windows Storage Server 2003 R2 User’s Guide Copyright © 2003-2006 Digiliant, LLC. All rights reserved. The technical documentation is being delivered to you AS-IS, and Digiliant, LLC makes no warranty as to its accuracies or use. Any use of the technical documentation or the information contained therein is at the risk of the user. Documentation may include technical or other inaccuracies or typographical errors. Digiliant reserves the right to make changes without prior notice. Digiliant and the Digiliant Logo are registered trademarks of Digiliant, LLC and may not be used without written permission. Microsoft, Microsoft Windows Storage Server 2003 and all other trademarks are the property of their respective owners. No part of this documentation may be reproduced, transmitted, or translated in any form or by any means, electronic, mechanical, manual, optical, or otherwise, without the prior written permission of Digiliant, LLC. 1 OVERVIEW OF WINDOWS STORAGE SERVER 2003 R2 .......................................................................................... 1 NETWORKING ................................................................................................................................................................................. 1 Network Data Transmission Protocols ................................................................................................................................ 1 NETWORK SECURITY ....................................................................................................................................................................