Hacking Voip Takes a Dual Approach to Voip and Home Voip Solutions Like Yahoo! and Security, Explaining Its Many Security Holes to Vonage Hackers and Administrators
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

List of TCP and UDP Port Numbers from Wikipedia, the Free Encyclopedia
List of TCP and UDP port numbers From Wikipedia, the free encyclopedia This is a list of Internet socket port numbers used by protocols of the Transport Layer of the Internet Protocol Suite for the establishment of host-to-host communications. Originally, these ports number were used by the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP), but are also used for the Stream Control Transmission Protocol (SCTP), and the Datagram Congestion Control Protocol (DCCP). SCTP and DCCP services usually use a port number that matches the service of the corresponding TCP or UDP implementation if they exist. The Internet Assigned Numbers Authority (IANA) is responsible for maintaining the official assignments of port numbers for specific uses.[1] However, many unofficial uses of both well-known and registered port numbers occur in practice. Contents 1 Table legend 2 Well-known ports 3 Registered ports 4 Dynamic, private or ephemeral ports 5 See also 6 References 7 External links Table legend Use Description Color Official Port is registered with IANA for the application white Unofficial Port is not registered with IANA for the application blue Multiple use Multiple applications are known to use this port. yellow Well-known ports The port numbers in the range from 0 to 1023 are the well-known ports. They are used by system processes that provide widely used types of network services. On Unix-like operating systems, a process must execute with superuser privileges to be able to bind a network socket to an IP address using one of the well-known ports. -

Release Notes 2020 Callswitch Platform 6.0 Callswitch Communicator 6.0
‘Together we are stronger.’ RELEASE NOTES 2020 CALLSWITCH PLATFORM 6.0 CALLSWITCH COMMUNICATOR 6.0 www.unitetelecoms.co.uk TABLE OF OF CONTENTSCONTENTS INTRO CALLSWITCH PLATFORM V6.0 CALLSWITCH PLATFORM FEATURES MEETING MOBILE CHAT FILE SHARING SERVICE (FSS) AUTHENTICATION SECURITY IMPROVEMENTS MUSIC ON HOLD: AUTOMATIC SOUND CONVERSION AUTOMATIC SOUND CONVERSION FOR MUSIC ON HOLD GREETING ACCESS CODES IVR TREE EMERGENCY CALL NOTIFICATION SYSTEM > SOUND SIMPLIFICATION (SEARCH) PHONE BOOK WAKE-UP CALLS SHORT CODE CALLER IDS NEW CALL CENTRE AND DIALLER CALLER ID LIST (WITH EMERGENCY CALLER ID) CALL FORWARDING IMPORT AND EXPORT .CSV FOR OPERATION TIME DIRECT CONVERSION OF GREETING SOUND FILES CRM INTEGRATION SEND SOUND FILES OF CONFERENCES TO AN EMAIL ADDRESS SYSTEM > SOUND FILES > SEARCH PAGE SIMPLIFICATION AND UPLOAD IMPROVEMENTS 022 WANT TO KNOW MORE ABOUT ABOUT OUR OUR PRODUCTS? PRODUCTS? PLEASE PLEASE VISIT VISIT WWW.UNITETELECOMS.CO.UK WWW.TELCOSWITCH.COM OROR EMAILEMAIL [email protected]@TELCOSWITCH.COM. CALLSWITCH CONTACT CENTRE FEATURES AGENT STATISTICS AGENT GROUP IMPROVEMENTS AGENT REAL TIME STATISTICS BLENDING MODE (INBOUND/OUTBOUND) CALL AGENT BY NUMBER (DIRECT IN CALL) DIALLER MONITOR PAGES NEW MENU PROJECT CODES SKILL-BASED ROUTING (SBR) SCHEDULING REPORTS CALLSWITCH COMMUNICATOR V6.0 CALLSWITCH COMMUNICATOR FEATURES UNIFIED PRESENCE NEW DESIGN FOR AGENT EDITION OUTBOUND CALL CENTRE (DIALLER) PERSONAL CALLBACK INTEGRATED WEB BROWSER FOR CRM POPUP, CALL POPUP AND QUEUE URL POPUP PROJECT CODES EXTENDED SUPERVISOR -

List of TCP and UDP Port Numbers - Wikipedia, the Free Encyclopedia 6/12/11 3:20 PM
List of TCP and UDP port numbers - Wikipedia, the free encyclopedia 6/12/11 3:20 PM List of TCP and UDP port numbers From Wikipedia, the free encyclopedia (Redirected from TCP and UDP port numbers) This is a list of Internet socket port numbers used by protocols of the Transport Layer of the Internet Protocol Suite for the establishment of host-to-host communications. Originally, these port numbers were used by the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP), but are used also for the Stream Control Transmission Protocol (SCTP), and the Datagram Congestion Control Protocol (DCCP). SCTP and DCCP services usually use a port number that matches the service of the corresponding TCP or UDP implementation if they exist. The Internet Assigned Numbers Authority (IANA) is responsible for maintaining the official assignments of port numbers for specific uses.[1] However, many unofficial uses of both well-known and registered port numbers occur in practice. Contents 1 Table legend 2 Well-known ports: 0–1023 3 Registered ports: 1024–49151 4 Dynamic, private or ephemeral ports: 49152–65535 5 See also 6 References 7 External links Table legend Color coding of table entries Official Port/application combination is registered with IANA Unofficial Port/application combination is not registered with IANA Conflict Port is in use for multiple applications (may be official or unofficial) Well-known ports: 0–1023 The port numbers in the range from 0 to 1023 are the well-known ports. They are used by system processes that provide widely-used types of network services. -
NCID - Network Caller ID User Manual
NCID - Network Caller ID User Manual Copyright © 2014-2021 Authors: John L Chmielewski Todd A Andrews Last edited: Sep 26, 2021 Table of Contents Introduction Getting Started Installation Obtaining Caller ID Supported Clients Client Output Modules Using NCID FAQ Verbose Levels Contributors TODO LICENSE Introduction NCID (Network Caller ID) is Caller ID (CID) distributed over a network to a variety of devices and computers. The NCID server monitors either a modem, Caller ID device, or gateway (e.g., SIP, VoIP, smartphones) for the CID data. The data is collected and sent, via TCP, to one or more connected clients. The server supports multiple gateways which can be used with or without a modem or device. The server also supports one line text messages. The NCID project website is the central place to go for the latest downloads, updated documentation and user/technical support for the official NCID package and its optional client packages. This document contains information on how to get started with NCID, the hardware needed, a Frequently Asked Questions (FAQ) section and a TODO list. It also provides information on supported clients, gateways and optional server features. Troubleshooting information is also provided. Getting Started Table of Contents NCID can be overwhelming for users who have never used it. Current users of NCID are probably not aware of all of its features, or how to use them properly. This document will try to help with those cases. The FAQ should also be of some help. In this document: NCID is the package name ncidd is the server name ncid is the client name Unix is a generic term to mean any UNIX-like or Linux-like operating system, e.g., Fedora, FreeBSD, Mac OS X, Debian, etc. -

List of TCP and UDP Port Numbers from Wikipedia, the Free Encyclopedia
List of TCP and UDP port numbers From Wikipedia, the free encyclopedia This is a list of Internet socket port numbers used by protocols of the transport layer of the Internet Protocol Suite for the establishment of host-to-host connectivity. Originally, port numbers were used by the Network Control Program (NCP) in the ARPANET for which two ports were required for half- duplex transmission. Later, the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP) needed only one port for full- duplex, bidirectional traffic. The even-numbered ports were not used, and this resulted in some even numbers in the well-known port number /etc/services, a service name range being unassigned. The Stream Control Transmission Protocol database file on Unix-like operating (SCTP) and the Datagram Congestion Control Protocol (DCCP) also systems.[1][2][3][4] use port numbers. They usually use port numbers that match the services of the corresponding TCP or UDP implementation, if they exist. The Internet Assigned Numbers Authority (IANA) is responsible for maintaining the official assignments of port numbers for specific uses.[5] However, many unofficial uses of both well-known and registered port numbers occur in practice. Contents 1 Table legend 2 Well-known ports 3 Registered ports 4 Dynamic, private or ephemeral ports 5 See also 6 References 7 External links Table legend Official: Port is registered with IANA for the application.[5] Unofficial: Port is not registered with IANA for the application. Multiple use: Multiple applications are known to use this port. Well-known ports The port numbers in the range from 0 to 1023 are the well-known ports or system ports.[6] They are used by system processes that provide widely used types of network services. -

NCID Manual Pages
NCID Manual Pages Copyright © 2018-2021 NCID Development Team Last edited: June 27, 2021 INDEX(0) INDEX(0) Index NCID Package: Server • Server ncidd.8 4 • Server Alias File ncidd.alias.5 11 • Server Blacklist file ncidd.blacklist.5 12 • Server Whitelist file ncidd.whitelist.5 14 • Server Configuration file ncidd.conf.5 15 • Server Recordings ncid_recordings.7 17 ServerHangup Extensions • Overviewncid_extensions.7 18 • Calls hangup−calls.1 19 • Closed hangup−closed−skel.1 20 • Call twoextensions hangup−combo−skel.1 21 • • Fake Numbers hangup−fakenum.1 22 • FCC Complaint Calls List hangup−fcc.1 23 • Message hangup−message−skel.1 24 • No hangup on anycalls hangup−nohangup.1 25 • Skel hangup−skel.1 26 Client • Client ncid.1 27 • Client configuration file ncid.conf.5 30 Client Modules • Overviewncid_modules.7 31 • Alert ncid−alert.1 33 • Initmodem ncid−initmodem.1 34 • Kpopup ncid−kpopup.1 35 • Notify ncid−notify.1 36 • Page ncid−page.1 37 • Samba ncid−samba.1 40 • Speak ncid−speak.1 41 • MySQL ncid−mysql.1 42 • MythTV ncid−mythtv.1 44 • Skel ncid−skel.1 45 • Wakeup ncid−wakeup.1 47 • Yacncid−yac.1 48 Gateways • Overviewncid_gateways.7 49 • Email to NCID email2ncid.1 50 1 INDEX(0) INDEX(0) • Email to NCID configuration file email2ncid.conf.5 52 • Obihai devices to NCID obi2ncid.1 53 • Obihai devices to NCID configuration file obi2ncid.conf.5 57 • NCID to NCID ncid2ncid.1 58 • NCID to NCID configuration file ncid2ncid.conf.5 61 • Remote Notifier to NCID rn2ncid.1 62 • Remote Notifier to NCID configuration file rn2ncid.conf.5 64 • SIP to NCID sip2ncid.8 66 • -

NCID API Documentation
NCID API Documentation API 1.11 Last edited: August 3, 2021 Copyright © 2010-2021 John L Chmielewski Todd A Andrews This document contains information needed to develop servers, clients, client output modules and gateways for NCID (Network Caller ID). All example phone numbers and names contained herein are intended to be fictional. There are 5 feature sets of NCID conformance: Feature Set 1: Modem and Device Support (required) Feature Set 2: Gateway Support (optional) Feature Set 3: Client Job Support (optional) Feature Set 4: Acknowledgment Support (optional) Feature Set 5: Relay Job Support (optional) Table of Contents Before you begin ABOUT CONFIGURATION OPTIONS FOR SERVER IMPLEMENTATIONS ABOUT END-OF-LINE TERMINATORS ABOUT LINE TYPES AND FIELD PAIRS ENSURING CONNECTIVITY WITH THE SERVER COMPANION DOCUMENTS Call/Message Line Types, Categories and Structure (new in API 1.7) OVERVIEW TABLE {CALLTYPE} CATEGORY STRUCTURE {MSGTYPE} CATEGORY STRUCTURE Server Output Lines Client/Gateway Output Lines Feature Set 1: Modem and Device Support SERVER IMPLEMENTATION Server Output Lines Server Alias Support Server Hangup Support Modem-to-Server Optional Server Extensions Optional Server Hangup Extension Optional NetCallerID Device-to-Server Optional TCI Device-to-Server (new in API 1.1) CLIENT IMPLEMENTATION Client-to-Server Optional Client-to-Module Optional Client-to-TiVo Display (Removed in API 1.6) Feature Set 2: Gateway Support SERVER IMPLEMENTATION XDMF Input (new in API 1.8) Server Output Lines GATEWAY IMPLEMENTATION Gateway-to-Server Forwarding -
Measurement & Sensors
iETHERNET DESIGN CONTEST WINNERS P. 30 • DESIGN YOUR OWN CONTROLLER CIRCUITRY P. 70 • PROGRAMMABLE LOGIC 101 P. 76 w w w . c i r c u i t c e l l a r . c o m CIRCUITTHE MAGAZINE FOR COMPUTER CELLAR APPLICATIONS #214 May 2008 MEASUREMENT & SENSORS Build An Ultrasonic Height-Sensing System Electronic Data Logging & Motion Analysis The coLinux Development Platform Making Sense Of Compiler Output Construct A Portable LCR Meter ATA Interfaces For I/O Apps 05> 7925274 75349 $4.95 U.S. ($5.95 Canada) C2.qxp 3/3/2008 11:16 AM Page 1 SERIAL TO ETHERNET SOLUTIONS Simple Ethernet connectivity for serial devices Works out of the box - no programming is required Device P/N: SB70-100CR Customize to suit any Kit P/N: NNDK-SB70-KIT application with low-cost $69 SB70 development kit 2-port serial-to-Ethernet server Features: Qty. 100 with TTL support 10/100 Ethernet TCP/UDP mode DHCP/Static IP Support Data rates up to 921.6kbps Web-based configuration Need a custom solution? NetBurner Serial to Ethernet Development Kits are available Device P/N: SB72-EX-100CR to customize any aspect of Kit P/N: NNDK-SB72EX-KIT operation including web pages, data filtering, or custom network SB72EX $139 applications. All kits include 2-port serial-to-Ethernet server platform hardware, ANSI C/C++ Qty. 100 with RS-232 & RS-485/422 support compiler,TCP/IP stack, web server, e-mail protocols, RTOS, flash file system, Eclipse IDE, debugger, cables and power supply. Device P/N: PK70EX-232CR Information and Sales | [email protected] Kit P/N: NNDK-PK70EX232-KIT Web | www.netburner.com $269 PK70EX232 Telephone | 1-800-695-6828 4-port serial-to-Ethernet server Qty. -

List of TCP and UDP Port Numbers - Wikipedia, the Free Encyclopedia
List of TCP and UDP port numbers - Wikipedia, the free encyclopedia http://en.wikipedia.org/wiki/List_of_TCP_and_UDP_port_numbers List of TCP and UDP port numbers From Wikipedia, the free encyclopedia This is a list of Internet socket port numbers used by protocols of the Transport Layer of the Internet Protocol Suite for the establishment of host-to-host connectivity. Originally, these port numbers were used by the Network Control Program (NCP) and two ports were needed as transmission was done at half duplex. As Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) were adopted, only one port was needed. The even numbered ports were dropped. This is why some even numbers in the well-known port number range are unassigned. TCP and UDP port numbers are also used for the Stream Control Transmission Protocol (SCTP), and the Datagram Congestion Control Protocol (DCCP). SCTP and DCCP services usually use a port number that matches the service of the corresponding TCP or UDP implementation if they exist. The Internet Assigned Numbers Authority (IANA) is responsible for maintaining the official assignments of port numbers for specific uses. [1] However, many unofficial uses of both well-known and registered port numbers occur in practice. Contents 1 Table legend 2 Well-known ports 3 Registered ports 4 Dynamic, private or ephemeral ports 5 See also 6 References 7 External links Table legend Use Description Color Official Port is registered with IANA for the application [1] White Unofficial Port is not registered with IANA for the application Blue Multiple use Multiple applications are known to use this port. -

List of TCP and UDP Port Numbers 1 List of TCP and UDP Port Numbers
List of TCP and UDP port numbers 1 List of TCP and UDP port numbers This is a list of Internet socket port numbers used by protocols of the Transport Layer of the Internet Protocol Suite for the establishment of host-to-host communications. Originally, these ports number were used by the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP), but are also used for the Stream Control Transmission Protocol (SCTP), and the Datagram Congestion Control Protocol (DCCP). SCTP and DCCP services usually use a port number that matches the service of the corresponding TCP or UDP implementation if they exist. The Internet Assigned Numbers Authority (IANA) is responsible for maintaining the official assignments of port numbers for specific uses.[1] However, many unofficial uses of both well-known and registered port numbers occur in practice. Table legend Use Description Color Official Port is registered with IANA for the application white Unofficial Port is not registered with IANA for the application blue Multiple use Multiple applications are known to use this port. yellow Well-known ports The port numbers in the range from 0 to 1023 are the well-known ports. They are used by system processes that provide widely-used types of network services. On Unix-like operating systems, a process must execute with superuser privileges to be able to bind a network socket to an IP address using one of the well-known ports. Port TCP UDP Description Status 0 UDP Reserved Official 1 TCP UDP TCP Port Service Multiplexer (TCPMUX) Official [2] [3] -
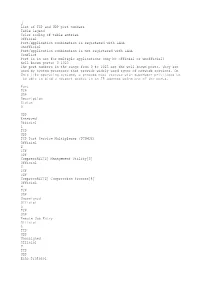
List of TCP and UDP Port Numbers
List of TCP and UDP port numbers Table legend Color coding of table entries Official Port/application combination is registered with IANA Unofficial Port/application combination is not registered with IANA Conflict Port is in use for multiple applications (may be official or unofficial) Wellknown ports: 0–1023 The port numbers in the range from 0 to 1023 are the wellknown ports. They are used by system processes that provide widelyused types of network services. On Unixlike operating systems, a process must execute with superuser privileges to be able to bind a network socket to an IP address using one of the ports. Port TCP UDP Description Status 0 UDP Reserved Official 1 TCP UDP TCP Port Service Multiplexer (TCPMUX) Official 2 TCP UDP CompressNET[2] Management Utility[3] Official 3 TCP UDP CompressNET[2] Compression Process[4] Official 4 TCP UDP Unassigned Official 5 TCP UDP Remote Job Entry Official 6 TCP UDP Unassigned Official 7 TCP UDP Echo Protocol Official 8 TCP UDP Unassigned Official 9 TCP UDP Discard Protocol Official 10 TCP UDP Unassigned Official 11 TCP UDP Active Users (systat service)[5][6] Official 12 TCP UDP Unassigned Official 13 TCP UDP Daytime Protocol (RFC 867) Official 14 TCP UDP Unassigned Official 15 TCP UDP netstat service[5] Unofficial 16 TCP UDP Unassigned Official 17 TCP UDP Quote of the Day Official 18 TCP UDP Message Send Protocol Official 19 TCP UDP Character Generator Protocol (CHARGEN) Official 20 TCP FTP—data transfer Official 21 TCP FTP—control (command) Official 22 TCP UDP Secure Shell (SSH)—used for secure logins, file transfers (scp, sftp) and port for warding Official 23 TCP Telnet protocol—unencrypted text communications Official 24 TCP UDP Privmail: any private mail system.