Automatic Detection of Security Vulnerabilities in Software Applications Using Static Analysis” Under the Guidance of Dr
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Configuring UNIX-Specific Settings: Creating Symbolic Links : Snap
Configuring UNIX-specific settings: Creating symbolic links Snap Creator Framework NetApp September 23, 2021 This PDF was generated from https://docs.netapp.com/us-en/snap-creator- framework/installation/task_creating_symbolic_links_for_domino_plug_in_on_linux_and_solaris_hosts.ht ml on September 23, 2021. Always check docs.netapp.com for the latest. Table of Contents Configuring UNIX-specific settings: Creating symbolic links . 1 Creating symbolic links for the Domino plug-in on Linux and Solaris hosts. 1 Creating symbolic links for the Domino plug-in on AIX hosts. 2 Configuring UNIX-specific settings: Creating symbolic links If you are going to install the Snap Creator Agent on a UNIX operating system (AIX, Linux, and Solaris), for the IBM Domino plug-in to work properly, three symbolic links (symlinks) must be created to link to Domino’s shared object files. Installation procedures vary slightly depending on the operating system. Refer to the appropriate procedure for your operating system. Domino does not support the HP-UX operating system. Creating symbolic links for the Domino plug-in on Linux and Solaris hosts You need to perform this procedure if you want to create symbolic links for the Domino plug-in on Linux and Solaris hosts. You should not copy and paste commands directly from this document; errors (such as incorrectly transferred characters caused by line breaks and hard returns) might result. Copy and paste the commands into a text editor, verify the commands, and then enter them in the CLI console. The paths provided in the following steps refer to the 32-bit systems; 64-bit systems must create simlinks to /usr/lib64 instead of /usr/lib. -
Buffer Overflow Exploits
Buffer overflow exploits EJ Jung A Bit of History: Morris Worm Worm was released in 1988 by Robert Morris • Graduate student at Cornell, son of NSA chief scientist • Convicted under Computer Fraud and Abuse Act, sentenced to 3 years of probation and 400 hours of community service • Now a computer science professor at MIT Worm was intended to propagate slowly and harmlessly measure the size of the Internet Due to a coding error, it created new copies as fast as it could and overloaded infected machines $10-100M worth of damage Morris Worm and Buffer Overflow One of the worm’s propagation techniques was a buffer overflow attack against a vulnerable version of fingerd on VAX systems • By sending special string to finger daemon, worm caused it to execute code creating a new worm copy • Unable to determine remote OS version, worm also attacked fingerd on Suns running BSD, causing them to crash (instead of spawning a new copy) For more history: • http://www.snowplow.org/tom/worm/worm.html Buffer Overflow These Days Most common cause of Internet attacks • Over 50% of advisories published by CERT (computer security incident report team) are caused by various buffer overflows Morris worm (1988): overflow in fingerd • 6,000 machines infected CodeRed (2001): overflow in MS-IIS server • 300,000 machines infected in 14 hours SQL Slammer (2003): overflow in MS-SQL server • 75,000 machines infected in 10 minutes (!!) Attacks on Memory Buffers Buffer is a data storage area inside computer memory (stack or heap) • Intended to hold pre-defined -

Practical C Programming, 3Rd Edition
Practical C Programming, 3rd Edition By Steve Oualline 3rd Edition August 1997 ISBN: 1-56592-306-5 This new edition of "Practical C Programming" teaches users not only the mechanics or programming, but also how to create programs that are easy to read, maintain, and debug. It features more extensive examples and an introduction to graphical development environments. Programs conform to ANSI C. 0 TEAM FLY PRESENTS Table of Contents Preface How This Book is Organized Chapter by Chapter Notes on the Third Edition Font Conventions Obtaining Source Code Comments and Questions Acknowledgments Acknowledgments to the Third Edition I. Basics 1. What Is C? How Programming Works Brief History of C How C Works How to Learn C 2. Basics of Program Writing Programs from Conception to Execution Creating a Real Program Creating a Program Using a Command-Line Compiler Creating a Program Using an Integrated Development Environment Getting Help on UNIX Getting Help in an Integrated Development Environment IDE Cookbooks Programming Exercises 3. Style Common Coding Practices Coding Religion Indentation and Code Format Clarity Simplicity Summary 4. Basic Declarations and Expressions Elements of a Program Basic Program Structure Simple Expressions Variables and Storage 1 TEAM FLY PRESENTS Variable Declarations Integers Assignment Statements printf Function Floating Point Floating Point Versus Integer Divide Characters Answers Programming Exercises 5. Arrays, Qualifiers, and Reading Numbers Arrays Strings Reading Strings Multidimensional Arrays Reading Numbers Initializing Variables Types of Integers Types of Floats Constant Declarations Hexadecimal and Octal Constants Operators for Performing Shortcuts Side Effects ++x or x++ More Side-Effect Problems Answers Programming Exercises 6. -

Software Comprehension Using Open Source Tools: a Study
International Journal of Computer Sciences and Engineering Open Access Survey Paper Vol.-7, Issue-3, March 2019 E-ISSN: 2347-2693 Software Comprehension Using Open Source Tools: A Study Jyoti Yadav Department of Computer Science, Savitribai Phule Pune University, Maharashtra, India *Corresponding Author: [email protected], Tel.: 9881252910 DOI: https://doi.org/10.26438/ijcse/v7i3.657668 | Available online at: www.ijcseonline.org Accepted: 12/Mar/2019, Published: 31/Mar/2019 Abstract: Software applications developed in recent times are written in lakhs of lines of code and have become increasingly complex in terms of structure, behaviour and functionality. At the same time, development life cycles of such applications reveal a tendency of becoming increasingly shorter, due to factors such as rapid evolution of supporting and enabling technologies. As a consequence, an increasing portion of software development cost shifts from the creation of new artefacts to the adaptation of existing ones. A key component of this activity is the understanding of the design, operation, and behaviour of existing artefacts of the code. For instance, in the software industry, it is estimated that maintenance costs exceed 80% of the total costs of a software product’s lifecycle, and software understanding accounts for as much as half of these maintenance costs. Software Comprehension is a key subtask of software maintenance and evolution phase, which is driven by the need to change software. This paper will help in enhancing the ability of the developers to read and comprehend large pieces of software in an organized manner, even in the absence of adequate documentation by using existing open source tools. -

Installation Guide LS Nav 2018 (11.0) Contents
LS Nav 2018 (11.0) Installation Guide © 2018 LS Retail ehf. All rights reserved. All trademarks belong to their respective holders. ii Installation Guide LS Nav 2018 (11.0) Contents Contents Installation Guide LS Nav 1 Files in This Version 1 LS Nav Setup File 1 Demonstration Database Backup 1 Documentation 1 Objects 2 Objects \ Uninstall 2 Objects \ Upgrade 2 Objects \ Auto Test 2 Online Help 2 Setup \ LS Nav Rapid Installer 2 Setup \ LS Nav Rapid Start 2 Setup \ LS Nav Toolbox 2 Setup \ LS Printing Station 2 Setup 2 Installation 2 Prerequisites 2 Microsoft Dynamics NAV Application Objects Added or Modified by LS Nav 3 Installing LS Nav in a New Database 4 Installing LS Nav in an Existing Database 4 Uninstall 5 Uninstall the LS Nav xx.x Client Components 5 Uninstall the LS Nav xx.x Service Components 5 Uninstall LS Nav from a Microsoft Dynamics NAV Database 5 Database Compilation 6 System Requirements 6 Security Hardening Guide for LS Nav 7 Clear Data Tables That Are Not Included in the Customer’s License 7 Online Help Installation 7 Installation Guide LS Nav 2018 (11.0) iii Contents Local Setup 8 Remote Setup 8 Older Documents 9 Toolbox Installation 10 See Also 10 Installing the Toolbox 10 Client Components Installer 11 Service Components Installer 12 Install Options (Silent Install) 13 Installing Into a Database (Control Add-Ins Table) 14 Web POS Installation 16 See Also (topics in LS Nav Online Help) 17 Installing Microsoft Dynamics NAV for Web POS 17 Importing Control Add-in for Web POS 17 Web POS in Full-Screen Mode 18 LS Nav Auto Tests 18 Prerequisites 18 Installation 19 Objects needed 19 Running 19 1. -

Automatic Discovery of API-Level Vulnerabilities
Automatic Discovery of API-Level Vulnerabilities Vinod Ganapathyy, Sanjit A. Seshiaz, Somesh Jhay, Thomas W. Repsy, Randal E. Bryantz yComputer Sciences Department, zSchool of Computer Science, University of Wisconsin-Madison Carnegie Mellon University fvg|jha|[email protected] fsanjit|[email protected] UW-MADISON COMPUTER SCIENCES TECHNICAL REPORT: UW-CS-TR-1512, JULY 2004. Abstract A system is vulnerable to an API-level attack if its security can be compromised by invoking an allowed sequence of operations from its API. We present a formal framework to model and analyze APIs, and develop an automatic technique based upon bounded model checking to discover API-level vulnerabilities. If a vulnerability exists, our technique produces a trace of API operations demonstrating an attack. Two case studies show the efficacy of our technique. In the first study we present a novel way to analyze printf-family format-string attacks as API-level attacks, and implement a tool to discover them automatically. In the second study, we model a subset of the IBM Common Cryptographic Architecture API, a popular cryptographic key-management API, and automatically detect a previously known vulnerability. 1 Introduction Software modules communicate through application programming interfaces (APIs). Failure to respect an API's usage conventions or failure to understand the semantics of an API may lead to security vulnerabilities. For instance, Chen et al. [13] demonstrated a security vulnerability in sendmail-8.10.1that was due to a misunderstanding of the semantics of UNIX user-id setting commands. A programmer mistakenly assumed that setuid(getuid()) would always drop all privileges. -

Getty Scholars' Workspace™ INSTALLATION INSTRUCTIONS
Getty Scholars’ Workspace™ INSTALLATION INSTRUCTIONS This document outlines methods to run the application locally on your personal computer or to do a full installation on a web server. Test Drive with Docker Getty Scholars' Workspace is a multi-tenant web application, so it is intended to be run on a web server. However, if you'd like to run it on your personal computer just to give it a test drive, you can use Docker to create a virtual server environment and run the Workspace locally. Follow the steps below to give it a spin. Scroll further for real deployment instructions. 1. Install Docker on your machine. Follow instructions on the Docker website: https://www.docker.com/ 2. If you are using Docker Machine (Mac or Windows), be sure to start it by using the Docker Quickstart Terminal. Docker is configured to use the default machine with IP 192.168.99.100. 3. At the command line, pull the Getty Scholars' Workspace image. $ docker pull thegetty/scholarsworkspace 4. Run the container. $ docker run -d -p 8080:80 --name=wkspc thegetty/scholarsworkspace supervisord -n 5. Point your browser to `<ip address>:8080/GettyScholarsWorkspace`. Use the IP address noted in Step 2. 6. The Drupal administrator login is `scholar` and the password is `workspace`. Be sure to change these in the Drupal admin interface. 7. To shut it down, stop the container: $ docker stop wkspc Web Server Installation These installation instructions assume you are installing Getty Scholars' Workspace on a server (virtual or physical) with a clean new instance of Ubuntu 14.04 as the operating system. -

CMSC 246 Systems Programming Spring 2018 Bryn Mawr College Instructor: Deepak Kumar
1/23/2018 CMSC 246 Systems Programming Spring 2018 Bryn Mawr College Instructor: Deepak Kumar Input • scanf() is the C library’s counterpart to printf. • Syntax for using scanf() scanf(<format-string>, <variable-reference(s)>) • Example: read an integer value into an int variable data. scanf("%d", &data); //read an integer; store into data • The & is a reference operator. More on that later! 2 1 1/23/2018 Reading Input • Reading a float: scanf("%f", &x); • "%f" tells scanf to look for an input value in float format (the number may contain a decimal point, but doesn’t have to). 3 Standard Input & Output Devices • In Linux the standard I/O devices are, by default, the keyboard for input, and the terminal console for output. • Thus, input and output in C, if not specified, is always from the standard input and output devices. That is, printf() always outputs to the terminal console scanf() always inputs from the keyboard • Later, you will see how these can be reassigned/redirected to other devices. 4 2 1/23/2018 Program: Convert Fahrenheit to Celsius • The celsius.c program prompts the user to enter a Fahrenheit temperature; it then prints the equivalent Celsius temperature. • Sample program output: Enter Fahrenheit temperature: 212 Celsius equivalent: 100.0 • The program will allow temperatures that aren’t integers. 5 Program: Convert Fahrenheit to Celsius ctof.c #include <stdio.h> int main(void) { float f, c; printf("Enter Fahrenheit temperature: "); scanf("%f", &f); c = (f – 32) * 5.0/9.0; printf("Celsius equivalent: %.1f\n", c); return -

After Upgrade and Reboot with Install Configuration Set to Yes, the BIG-IP
K33233632: After upgrade and reboot with Install Configuration set to Yes, the BIG-IP appears to have hung or lost all configuration and mcpd, gtmd, named and others are in a restart loop Support Solution Original Publication Date: Jan 28, 2020 Update Date: Mar 25, 2021 Details Description After you upgrade the BIG-IP system to BIG-IP 14.1.2 and later, certain daemons (e.g. mcpd, gtmd, and named) may be in a restart loop and the BIG-IP appears to have hung or lost all configuration. Additionally, the device may exhibit the following symptoms: You observe error messages similar to the following in /var/log/ltm (below is an example of an mcpd restart loop): err mcpd[8710]: 01070734:3: Configuration error: MCPProcessor::initializeDB: can't chmod for directory (/config/filestore/files_d/<directory_names>) err (Permission denied). err mcpd[8710]: 01070596:3: An unexpected failure has occurred, can't chmod for directory (/config /filestore/files_d/<directory_names>) err (Permission denied). - sys/validation/FileObject.cpp, line 612, exiting... You observe error messages similar to the following in /var/log/ltm: 01420006:3: Loading configuration process failed. You observe error messages similar to the following in /var/log/auditd/audit.log (below is an example for an mcpd restart loop): Note: The message contains denied and unlabeled_t shown in bold below. type=AVC msg=audit(day_time): avc: denied { setattr } for pid=13624 comm="mcpd" name=" external_monitor_d" dev="dm-11" ino=307 scontext=system_u:system_r:mcpd_t:s0 tcontext=system_u:object_r:unlabeled_t:s0 tclass=dir The Configuration utility displays the following: The configuration has not yet loaded. -
Install and Run External Command Line Softwares
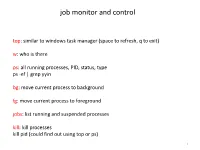
job monitor and control top: similar to windows task manager (space to refresh, q to exit) w: who is there ps: all running processes, PID, status, type ps -ef | grep yyin bg: move current process to background fg: move current process to foreground jobs: list running and suspended processes kill: kill processes kill pid (could find out using top or ps) 1 sort, cut, uniq, join, paste, sed, grep, awk, wc, diff, comm, cat All types of bioinformatics sequence analyses are essentially text processing. Unix Shell has the above commands that are very useful for processing texts and also allows the output from one command to be passed to another command as input using pipe (“|”). less cosmicRaw.txt | cut -f2,3,4,5,8,13 | awk '$5==22' | cut -f1 | sort -u | wc This makes the processing of files using Shell very convenient and very powerful: you do not need to write output to intermediate files or load all data into the memory. For example, combining different Unix commands for text processing is like passing an item through a manufacturing pipeline when you only care about the final product 2 Hands on example 1: cosmic mutation data - Go to UCSC genome browser website: http://genome.ucsc.edu/ - On the left, find the Downloads link - Click on Human - Click on Annotation database - Ctrl+f and then search “cosmic” - On “cosmic.txt.gz” right-click -> copy link address - Go to the terminal and wget the above link (middle click or Shift+Insert to paste what you copied) - Similarly, download the “cosmicRaw.txt.gz” file - Under your home, create a folder -
The AWK Programming Language
The Programming ~" ·. Language PolyAWK- The Toolbox Language· Auru:o V. AHo BRIAN W.I<ERNIGHAN PETER J. WEINBERGER TheAWK4 Programming~ Language TheAWI(. Programming~ Language ALFRED V. AHo BRIAN w. KERNIGHAN PETER J. WEINBERGER AT& T Bell Laboratories Murray Hill, New Jersey A ADDISON-WESLEY•• PUBLISHING COMPANY Reading, Massachusetts • Menlo Park, California • New York Don Mills, Ontario • Wokingham, England • Amsterdam • Bonn Sydney • Singapore • Tokyo • Madrid • Bogota Santiago • San Juan This book is in the Addison-Wesley Series in Computer Science Michael A. Harrison Consulting Editor Library of Congress Cataloging-in-Publication Data Aho, Alfred V. The AWK programming language. Includes index. I. AWK (Computer program language) I. Kernighan, Brian W. II. Weinberger, Peter J. III. Title. QA76.73.A95A35 1988 005.13'3 87-17566 ISBN 0-201-07981-X This book was typeset in Times Roman and Courier by the authors, using an Autologic APS-5 phototypesetter and a DEC VAX 8550 running the 9th Edition of the UNIX~ operating system. -~- ATs.T Copyright c 1988 by Bell Telephone Laboratories, Incorporated. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, photocopy ing, recording, or otherwise, without the prior written permission of the publisher. Printed in the United States of America. Published simultaneously in Canada. UNIX is a registered trademark of AT&T. DEFGHIJ-AL-898 PREFACE Computer users spend a lot of time doing simple, mechanical data manipula tion - changing the format of data, checking its validity, finding items with some property, adding up numbers, printing reports, and the like. -

Install Guide - UNIX Oracle CSE
Information Engineering Technology Install Guide - UNIX Oracle CSE Release 8.7.3 © Information Engineering Technology Ltd 2020 www.iet.uk Table Of Contents Introduction ............................................................................................................................................................................... 3 Architecture .................................................................................................................................................................................... 3 Communications ............................................................................................................................................................................. 3 About The Installation Guides .................................................................................................................................................... 4 Software for Download .............................................................................................................................................................. 4 Server Install – UNIX / Oracle CSE ............................................................................................................................................... 5 Pre-Requisites ................................................................................................................................................................................. 5 Who Should Perform this Installation? ..........................................................................................................................................