Managing Linux Resources with Cgroups
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Security Assurance Requirements for Linux Application Container Deployments
NISTIR 8176 Security Assurance Requirements for Linux Application Container Deployments Ramaswamy Chandramouli This publication is available free of charge from: https://doi.org/10.6028/NIST.IR.8176 NISTIR 8176 Security Assurance Requirements for Linux Application Container Deployments Ramaswamy Chandramouli Computer Security Division Information Technology Laboratory This publication is available free of charge from: https://doi.org/10.6028/NIST.IR.8176 October 2017 U.S. Department of Commerce Wilbur L. Ross, Jr., Secretary National Institute of Standards and Technology Walter Copan, NIST Director and Under Secretary of Commerce for Standards and Technology NISTIR 8176 SECURITY ASSURANCE FOR LINUX CONTAINERS National Institute of Standards and Technology Internal Report 8176 37 pages (October 2017) This publication is available free of charge from: https://doi.org/10.6028/NIST.IR.8176 Certain commercial entities, equipment, or materials may be identified in this document in order to describe an experimental procedure or concept adequately. Such identification is not intended to imply recommendation or endorsement by NIST, nor is it intended to imply that the entities, materials, or equipment are necessarily the best available for the purpose. This p There may be references in this publication to other publications currently under development by NIST in accordance with its assigned statutory responsibilities. The information in this publication, including concepts and methodologies, may be used by federal agencies even before the completion of such companion publications. Thus, until each ublication is available free of charge from: http publication is completed, current requirements, guidelines, and procedures, where they exist, remain operative. For planning and transition purposes, federal agencies may wish to closely follow the development of these new publications by NIST. -

Systematic Evaluation of Sandboxed Software Deployment for Real-Time Software on the Example of a Self-Driving Heavy Vehicle
Systematic Evaluation of Sandboxed Software Deployment for Real-time Software on the Example of a Self-Driving Heavy Vehicle Philip Masek1, Magnus Thulin1, Hugo Andrade1, Christian Berger2, and Ola Benderius3 Abstract— Companies developing and maintaining software-only products like web shops aim for establishing persistent links to their software running in the field. Monitoring data from real usage scenarios allows for a number of improvements in the software life-cycle, such as quick identification and solution of issues, and elicitation of requirements from previously unexpected usage. While the processes of continuous integra- tion, continuous deployment, and continuous experimentation using sandboxing technologies are becoming well established in said software-only products, adopting similar practices for the automotive domain is more complex mainly due to real-time and safety constraints. In this paper, we systematically evaluate sandboxed software deployment in the context of a self-driving heavy vehicle that participated in the 2016 Grand Cooperative Driving Challenge (GCDC) in The Netherlands. We measured the system’s scheduling precision after deploying applications in four different execution environments. Our results indicate that there is no significant difference in performance and overhead when sandboxed environments are used compared to natively deployed software. Thus, recent trends in software architecting, packaging, and maintenance using microservices encapsulated in sandboxes will help to realize similar software and system Fig. 1. Volvo FH16 truck from Chalmers Resource for Vehicle Research engineering for cyber-physical systems. (Revere) laboratory that participated in the 2016 Grand Cooperative Driving Challenge in Helmond, NL. I. INTRODUCTION Companies that produce and maintain software-only prod- ucts, i.e. -

An Empirical Study of Virtualization Versus Lightweight Containers
On Exploiting Page Sharing in a Virtualized Environment - an Empirical Study of Virtualization Versus Lightweight Containers Ashish Sonone, Anand Soni, Senthil Nathan, Umesh Bellur Department of Computer Science and Engineering IIT Bombay Mumbai, India ashishsonone, anandsoni, cendhu, [email protected] Abstract—While virtualized solutions are firmly entrenched faulty application can result in the failure of all applications in cloud data centers to provide isolated execution environ- executing on that machine. On the other hand, each virtual ments, the chief overhead it suffers from is that of memory machine runs its own OS and hence, a faulty application consumption. Even pages that are common in multiple virtual machines (VMs) on the same physical machine (PM) are not cannot crash the host OS. Further, each application can shared and multiple copies exist thereby draining valuable run on any customized and optimized guest OS which is memory resources and capping the number of VMs that can be different from the host OS. For example, each guest OS can instantiated on a PM. Lightweight containers (LWCs) on the run its own I/O scheduler which is optimized for the hosted other hand does not suffer from this situation since virtually application. In addition to this, the hypervisor provides many everything is shared via Copy on Write semantics. As a result the capacity of a PM to host LWCs is far higher than hosting other features such as live migration of virtual machines, equivalent VMs. In this paper, we evaluate a solution using high availability using periodic checkpointing and storage uKSM to exploit memory page redundancy amongst multiple migration. -

Multicore Operating-System Support for Mixed Criticality∗
Multicore Operating-System Support for Mixed Criticality∗ James H. Anderson, Sanjoy K. Baruah, and Bjorn¨ B. Brandenburg The University of North Carolina at Chapel Hill Abstract Different criticality levels provide different levels of assurance against failure. In current avionics designs, Ongoing research is discussed on the development of highly-critical software is kept physically separate from operating-system support for enabling mixed-criticality less-critical software. Moreover, no currently deployed air- workloads to be supported on multicore platforms. This craft uses multicore processors to host highly-critical tasks work is motivated by avionics systems in which such work- (more precisely, if multicore processors are used, and if loads occur. In the mixed-criticality workload model that is such a processor hosts highly-critical applications, then all considered, task execution costs may be determined using but one of its cores are turned off). These design decisions more-stringent methods at high criticality levels, and less- are largely driven by certification issues. For example, cer- stringent methods at low criticality levels. The main focus tifying highly-critical components becomes easier if poten- of this research effort is devising mechanisms for providing tially adverse interactions among components executing on “temporal isolation” across criticality levels: lower levels different cores through shared hardware such as caches are should not adversely “interfere” with higher levels. simply “defined” not to occur. Unfortunately, hosting an overall workload as described here clearly wastes process- ing resources. 1 Introduction In this paper, we propose operating-system infrastruc- ture that allows applications of different criticalities to be The evolution of computational frameworks for avionics co-hosted on a multicore platform. -

Large-Scale Cluster Management at Google with Borg Abhishek Verma† Luis Pedrosa‡ Madhukar Korupolu David Oppenheimer Eric Tune John Wilkes Google Inc
Large-scale cluster management at Google with Borg Abhishek Vermay Luis Pedrosaz Madhukar Korupolu David Oppenheimer Eric Tune John Wilkes Google Inc. Abstract config file command-line Google’s Borg system is a cluster manager that runs hun- borgcfg webweb browsers tools dreds of thousands of jobs, from many thousands of differ- ent applications, across a number of clusters each with up to Cell BorgMaster tens of thousands of machines. BorgMasterBorgMaster UIUI shard shard BorgMasterBorgMaster read/UIUIUI shard shard It achieves high utilization by combining admission con- shard Scheduler persistent store trol, efficient task-packing, over-commitment, and machine scheduler (Paxos) link shard linklink shard shard sharing with process-level performance isolation. It supports linklink shard shard high-availability applications with runtime features that min- imize fault-recovery time, and scheduling policies that re- duce the probability of correlated failures. Borg simplifies life for its users by offering a declarative job specification Borglet Borglet Borglet Borglet language, name service integration, real-time job monitor- ing, and tools to analyze and simulate system behavior. We present a summary of the Borg system architecture and features, important design decisions, a quantitative anal- Figure 1: The high-level architecture of Borg. Only a tiny fraction ysis of some of its policy decisions, and a qualitative ex- of the thousands of worker nodes are shown. amination of lessons learned from a decade of operational experience with it. cluding with a set of qualitative observations we have made from operating Borg in production for more than a decade. 1. Introduction The cluster management system we internally call Borg ad- 2. -

Container and Kernel-Based Virtual Machine (KVM) Virtualization for Network Function Virtualization (NFV)
Container and Kernel-Based Virtual Machine (KVM) Virtualization for Network Function Virtualization (NFV) White Paper August 2015 Order Number: 332860-001US YouLegal Lines andmay Disclaimers not use or facilitate the use of this document in connection with any infringement or other legal analysis concerning Intel products described herein. You agree to grant Intel a non-exclusive, royalty-free license to any patent claim thereafter drafted which includes subject matter disclosed herein. No license (express or implied, by estoppel or otherwise) to any intellectual property rights is granted by this document. All information provided here is subject to change without notice. Contact your Intel representative to obtain the latest Intel product specifications and roadmaps. The products described may contain design defects or errors known as errata which may cause the product to deviate from published specifications. Current characterized errata are available on request. Copies of documents which have an order number and are referenced in this document may be obtained by calling 1-800-548-4725 or by visiting: http://www.intel.com/ design/literature.htm. Intel technologies’ features and benefits depend on system configuration and may require enabled hardware, software or service activation. Learn more at http:// www.intel.com/ or from the OEM or retailer. Results have been estimated or simulated using internal Intel analysis or architecture simulation or modeling, and provided to you for informational purposes. Any differences in your system hardware, software or configuration may affect your actual performance. For more complete information about performance and benchmark results, visit www.intel.com/benchmarks. Tests document performance of components on a particular test, in specific systems. -

Containers Demystified DOAG 2019
Containers Demystified DOAG 2019 Daniel Westermann - Jan Karremans AGENDA Intro History of containers What happened to Docker?? History k8s WHY Automation of the stuff Demo Intro …boring About me Daniel Westermann Principal Consultant Open Infrastructure Technology Leader +41 79 927 24 46 daniel.westermann[at]dbi-services.com EDB containers in Red Hat OpenShift 19.11.2019 Page 4 Who we are The Company Founded in 2010 More than 70 specialists Specialized in the Middleware Infrastructure The invisible part of IT Customers in Switzerland and all over Europe Our Offer Consulting Service Level Agreements (SLA) Trainings License Management dbi services Template - DOAG 2019 19.11.2019 Page 5 Jan Karremans @Johnnyq72 BACKGROUND 25 years of database technology 15 years of consulting 15 years of management 10 years of software development 10 years of technology sales 5 years of community advocacy 5 years of international public speaking EXPERTISE Oracle ACE Alumni EDB Postgres Advanced Server Professional Leader in the PostgreSQL community To Postgres what RedHat is to Linux EnterpriseDB Enterprise-grade Postgres The Most Complete Open Source Database Platform Freeing companies from vendor lock-in • Bruce Momjian • PostgreSQL, Global Development Group, Founding member • PostgreSQL, Core Team member • EnterpriseDB, Senior Database Architect • Mr. Postgres History of containers In the beginning • It was 1960… Bill Joy Co-founder of Sun Microsystems • Sharing 1 single computer with many users • It was then 1979… • Introducing chroot • Bill -

Containerization Introduction to Containers, Docker and Kubernetes
Containerization Introduction to Containers, Docker and Kubernetes EECS 768 Apoorv Ingle [email protected] Containers • Containers – lightweight VM or chroot on steroids • Feels like a virtual machine • Get a shell • Install packages • Run applications • Run services • But not really • Uses host kernel • Cannot boot OS • Does not need PID 1 • Process visible to host machine Containers • VM vs Containers Containers • Container Anatomy • cgroup: limit the use of resources • namespace: limit what processes can see (hence use) Containers • cgroup • Resource metering and limiting • CPU • IO • Network • etc.. • $ ls /sys/fs/cgroup Containers • Separate Hierarchies for each resource subsystem (CPU, IO, etc.) • Each process belongs to exactly 1 node • Node is a group of processes • Share resource Containers • CPU cgroup • Keeps track • user/system CPU • Usage per CPU • Can set weights • CPUset cgroup • Reserve to CPU to specific applications • Avoids context switch overheads • Useful for non uniform memory access (NUMA) Containers • Memory cgroup • Tracks pages used by each group • Pages can be shared across groups • Pages “charged” to a group • Shared pages “split the cost” • Set limits on usage Containers • Namespaces • Provides a view of the system to process • Controls what a process can see • Multiple namespaces • pid • net • mnt • uts • ipc • usr Containers • PID namespace • Processes within a PID namespace see only process in the same namespace • Each PID namespace has its own numbering staring from 1 • Namespace is killed when PID 1 goes away -
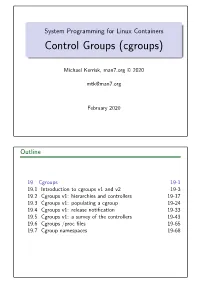
Control Groups (Cgroups)
System Programming for Linux Containers Control Groups (cgroups) Michael Kerrisk, man7.org © 2020 [email protected] February 2020 Outline 19 Cgroups 19-1 19.1 Introduction to cgroups v1 and v2 19-3 19.2 Cgroups v1: hierarchies and controllers 19-17 19.3 Cgroups v1: populating a cgroup 19-24 19.4 Cgroups v1: release notification 19-33 19.5 Cgroups v1: a survey of the controllers 19-43 19.6 Cgroups /procfiles 19-65 19.7 Cgroup namespaces 19-68 Outline 19 Cgroups 19-1 19.1 Introduction to cgroups v1 and v2 19-3 19.2 Cgroups v1: hierarchies and controllers 19-17 19.3 Cgroups v1: populating a cgroup 19-24 19.4 Cgroups v1: release notification 19-33 19.5 Cgroups v1: a survey of the controllers 19-43 19.6 Cgroups /procfiles 19-65 19.7 Cgroup namespaces 19-68 Goals Cgroups is a big topic Many controllers V1 versus V2 interfaces Our goal: understand fundamental semantics of cgroup filesystem and interfaces Useful from a programming perspective How do I build container frameworks? What else can I build with cgroups? And useful from a system engineering perspective What’s going on underneath my container’s hood? System Programming for Linux Containers ©2020, Michael Kerrisk Cgroups 19-4 §19.1 Focus We’ll focus on: General principles of operation; goals of cgroups The cgroup filesystem Interacting with the cgroup filesystem using shell commands Problems with cgroups v1, motivations for cgroups v2 Differences between cgroups v1 and v2 We’ll look briefly at some of the controllers System Programming for Linux Containers ©2020, Michael Kerrisk Cgroups 19-5 §19.1 -

A Container-Based Approach to OS Specialization for Exascale Computing
A Container-Based Approach to OS Specialization for Exascale Computing Judicael A. Zounmevo∗, Swann Perarnau∗, Kamil Iskra∗, Kazutomo Yoshii∗, Roberto Gioiosay, Brian C. Van Essenz, Maya B. Gokhalez, Edgar A. Leonz ∗Argonne National Laboratory fjzounmevo@, perarnau@mcs., iskra@mcs., [email protected] yPacific Northwest National Laboratory. [email protected] zLawrence Livermore National Laboratory. fvanessen1, maya, [email protected] Abstract—Future exascale systems will impose several con- view is essential for scalability, enabling compute nodes to flicting challenges on the operating system (OS) running on manage and optimize massive intranode thread and task par- the compute nodes of such machines. On the one hand, the allelism and adapt to new memory technologies. In addition, targeted extreme scale requires the kind of high resource usage efficiency that is best provided by lightweight OSes. At the Argo introduces the idea of “enclaves,” a set of resources same time, substantial changes in hardware are expected for dedicated to a particular service and capable of introspection exascale systems. Compute nodes are expected to host a mix of and autonomic response. Enclaves will be able to change the general-purpose and special-purpose processors or accelerators system configuration of nodes and the allocation of power tailored for serial, parallel, compute-intensive, or I/O-intensive to different nodes or to migrate data or computations from workloads. Similarly, the deeper and more complex memory hierarchy will expose multiple coherence domains and NUMA one node to another. They will be used to demonstrate nodes in addition to incorporating nonvolatile RAM. That the support of different levels of fault tolerance—a key expected workload and hardware heterogeneity and complexity concern of exascale systems—with some enclaves handling is not compatible with the simplicity that characterizes high node failures by means of global restart and other enclaves performance lightweight kernels. -

Cgroups Py: Using Linux Control Groups and Systemd to Manage CPU Time and Memory
cgroups py: Using Linux Control Groups and Systemd to Manage CPU Time and Memory Curtis Maves Jason St. John Research Computing Research Computing Purdue University Purdue University West Lafayette, Indiana, USA West Lafayette, Indiana, USA [email protected] [email protected] Abstract—cgroups provide a mechanism to limit user and individual resource. 1 Each directory in a cgroupsfs hierarchy process resource consumption on Linux systems. This paper represents a cgroup. Subdirectories of a directory represent discusses cgroups py, a Python script that runs as a systemd child cgroups of a parent cgroup. Within each directory of service that dynamically throttles users on shared resource systems, such as HPC cluster front-ends. This is done using the the cgroups tree, various files are exposed that allow for cgroups kernel API and systemd. the control of the cgroup from userspace via writes, and the Index Terms—throttling, cgroups, systemd obtainment of statistics about the cgroup via reads [1]. B. Systemd and cgroups I. INTRODUCTION systemd A frequent problem on any shared resource with many users Systemd uses a named cgroup tree (called )—that is that a few users may over consume memory and CPU time. does not impose any resource limits—to manage processes When these resources are exhausted, other users have degraded because it provides a convenient way to organize processes in access to the system. A mechanism is needed to prevent this. a hierarchical structure. At the top of the hierarchy, systemd creates three cgroups By placing throttles on physical memory consumption and [2]: CPU time for each individual user, cgroups py prevents re- source exhaustion on a shared system and ensures continued • system.slice: This contains every non-user systemd access for other users. -

Kvm – Kernel Based Virtual Machine
KVM – KERNEL BASED VIRTUAL MACHINE BACKGROUND Virtualization has begun to transform the way that enterprises are deploying and managing their infrastructure, providing the foundation for a truly agile enterprise, so that IT can deliver an infrastructure that is flexible, scalable, and most importantly economical by efficiently utilizing resources. 10 years ago virtualization was unheard of in the x86 market it was reserved for mainframe and high end UNIX systems. Over the last 3 to 4 years there has been exponential growth in the virtualization market both in terms of customer adoption and in terms of the rise of the number vendors in the virtualization space; from new hypervisor vendors to virtualization management vendors too numerous to mention. VIRTUALIZING THE X86 ARCHITECTURE The x86 architecture has proven to be the dominate platform in enterprise computing, moving from its humble beginnings in desktop systems to now, powering the large enterprise applications that run businesses across the globe. The current generation of x86 CPUs include features such as large scale multi-threading with 8 or more processing cores, support for large memory systems with NUMA and integrated memory controllers, high speed CPU interconnects and chipset for support for advanced reliability, availability and serviceability (RAS) features. These features were once reserved for mainframe and high end UNIX systems, today x86 servers with 2 or 4 sockets are replacing expensive UNIX/RISC systems while delivering better performance and 4 and 8 socket servers are challenging mainframe class systems. While the x86 platform has evolved significantly over it's lifetime it has maintained it's core architecture to provide backward compatibility.