CONTENTS in THIS ISSUE Fighting Malware and Spam
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

V2I Deployment Coalition Technical Memorandum 4: Phase 1 Final Report
V2I Deployment Coalition Technical Memorandum 4: Phase 1 Final Report January 2017 V2I Deployment Coalition Technical Memorandum 4: Phase 1 Final Report Table of Contents 1. Executive Summary ......................................................................................................................... 1 2. Synthesis of the Technical Memorandum ........................................................................................ 4 3. Overall Progress Advancing V2I Deployments .................................................................................. 6 3.1. Key Outcome: Engaging a Unified Coalition with Common Messages and Discussion ............... 6 3.2. Key Outcome: Narrowing of Initial Focus for V2I Deployments ................................................. 6 3.3. Key Outcome: Definitions of Research Activities to Support V2I Deployment ........................... 7 3.4. Key Outcome: V2I Standards Context Diagram and Supporting Description .............................. 8 3.5. Key Outcome: Creation of the SPaT Challenge .......................................................................... 8 3.6. Key Outcome: Creating a Forum for Collaboration between Infrastructure Owners/Operators and Original Equipment Manufacturers (IOOs and OEMs) ........................................................ 9 4. V2I DC Workshop 2 Summary ........................................................................................................ 11 4.1. TWG 1: Deployment Initiatives .............................................................................................. -

Botection: Bot Detection by Building Markov Chain Models of Bots Network Behavior Bushra A
BOTection: Bot Detection by Building Markov Chain Models of Bots Network Behavior Bushra A. Alahmadi Enrico Mariconti Riccardo Spolaor University of Oxford, UK University College London, UK University of Oxford, UK [email protected] [email protected] [email protected] Gianluca Stringhini Ivan Martinovic Boston University, USA University of Oxford, UK [email protected] [email protected] ABSTRACT through DDoS (e.g. DDoS on Estonia [22]), email spam (e.g. Geodo), Botnets continue to be a threat to organizations, thus various ma- ClickFraud (e.g. ClickBot), and spreading malware (e.g. Zeus). 10,263 chine learning-based botnet detectors have been proposed. How- malware botnet controllers (C&C) were blocked by Spamhaus Mal- ever, the capability of such systems in detecting new or unseen ware Labs in 2018 alone, an 8% increase from the number of botnet 1 botnets is crucial to ensure its robustness against the rapid evo- C&Cs seen in 2017. Cybercriminals are actively monetizing bot- lution of botnets. Moreover, it prolongs the effectiveness of the nets to launch attacks, which are evolving significantly and require system in detecting bots, avoiding frequent and time-consuming more effective detection mechanisms capable of detecting those classifier re-training. We present BOTection, a privacy-preserving which are new or unseen. bot detection system that models the bot network flow behavior Botnets rely heavily on network communications to infect new as a Markov Chain. The Markov Chains state transitions capture victims (propagation), to communicate with the C&C server, or the bots’ network behavior using high-level flow features as states, to perform their operational task (e.g. -

2015 Threat Report Provides a Comprehensive Overview of the Cyber Threat Landscape Facing Both Companies and Individuals
THREAT REPORT 2015 AT A GLANCE 2015 HIGHLIGHTS A few of the major events in 2015 concerning security issues. 08 07/15: Hacking Team 07/15: Bugs prompt 02/15: Europol joint breached, data Ford, Range Rover, 08/15: Google patches op takes down Ramnit released online Prius, Chrysler recalls Android Stagefright botnet flaw 09/15: XcodeGhost 07/15: Android 07/15: FBI Darkode tainted apps prompts Stagefright flaw 08/15: Amazon, ENFORCEMENT bazaar shutdown ATTACKS AppStore cleanup VULNERABILITY reported SECURITYPRODUCT Chrome drop Flash ads TOP MALWARE BREACHING THE MEET THE DUKES FAMILIES WALLED GARDEN The Dukes are a well- 12 18 resourced, highly 20 Njw0rm was the most In late 2015, the Apple App prominent new malware family in 2015. Store saw a string of incidents where dedicated and organized developers had used compromised tools cyberespionage group believed to be to unwittingly create apps with malicious working for the Russian Federation since behavior. The apps were able to bypass at least 2008 to collect intelligence in Njw0rm Apple’s review procedures to gain entry support of foreign and security policy decision-making. Angler into the store, and from there into an ordinary user’s iOS device. Gamarue THE CHAIN OF THE CHAIN OF Dorkbot COMPROMISE COMPROMISE: 23 The Stages 28 The Chain of Compromise Nuclear is a user-centric model that illustrates Kilim how cyber attacks combine different Ippedo techniques and resources to compromise Dridex devices and networks. It is defined by 4 main phases: Inception, Intrusion, WormLink Infection, and Invasion. INCEPTION Redirectors wreak havoc on US, Europe (p.28) INTRUSION AnglerEK dominates Flash (p.29) INFECTION The rise of rypto-ransomware (p.31) THREATS BY REGION Europe was particularly affected by the Angler exploit kit. -

Power-Law Properties in Indonesia Internet Traffic. Why Do We Care About It
by Bisyron Wahyudi Muhammad Salahuddien Amount of malicious traffic circulating on the Internet is increasing significantly. Increasing complexity and rapid change in hosts and networks technology suggests that there will be new vulnerabilities. Attackers have interest in identifying networks and hosts to expose vulnerabilities : . Network scans . Worms . Trojans . Botnet Complicated methods of attacks make difficult to identify the real attacks : It is not simple as filtering out the traffic from some sources Security is implemented like an “add on” module for the Internet. Understanding nature behavior of malicious sources and targeted ports is important to minimize the damage by build strong specific security rules and counter measures Help the cyber security policy-making process, and to raise public awareness Questions : . Do malicious sources generate the attacks uniformly ? . Is there any pattern specific i.e. recurrence event ? . Is there any correlation between the number of some attacks over specific time ? Many systems and phenomena (events) are distributed according to a “power law” When one quantity (say y) depends on another (say x) raised to some power, we say that y is described by a power law A power law applies to a system when: . large is rare and . small is common Collection of System logs from Networked Intrusion Detection System (IDS) The NIDS contains 11 sensors installed in different core networks in Indonesian ISP (NAP) Period : January, 2012 - September, 2012 . Available fields : ▪ Event Message, Timestamp, Dest. IP, Source IP, Attacks Classification, Priority, Protocol, Dest. Port/ICMP code, Source Port/ICMP type, Sensors ID Two quantities x and y are related by a power law if y is proportional to x(-c) for a constant c y = .x(-c) If x and y are related by a power law, then the graph of log(y) versus log(x) is a straight line log(y) = -c.log(x) + log() The slope of the log-log plot is the power exponent c Destination Port Distribution . -

Hostscan 4.8.01064 Antimalware and Firewall Support Charts
HostScan 4.8.01064 Antimalware and Firewall Support Charts 10/1/19 © 2019 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 76 Contents HostScan Version 4.8.01064 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.890.0 for Windows .................................................. 5 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.890.0 for Windows ........................................................ 44 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.824.0 for macos .................................................... 65 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.824.0 for macOS ........................................................... 71 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.730.0 for Linux ...................................................... 73 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.730.0 for Linux .............................................................. 76 ©201 9 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. -

Security Survey 2014
Security Survey 2014 www.av-comparatives.org IT Security Survey 2014 Language: English Last Revision: 28th February 2014 www.av-comparatives.org - 1 - Security Survey 2014 www.av-comparatives.org Overview Use of the Internet by home and business users continues to grow in all parts of the world. How users access the Internet is changing, though. There has been increased usage of smartphones by users to access the Internet. The tablet market has taken off as well. This has resulted in a drop in desktop and laptop sales. With respect to attacks by cyber criminals, this means that their focus has evolved. This is our fourth1 annual survey of computer users worldwide. Its focus is which security products (free and paid) are employed by users, OS usage, and browser usage. We also asked respondents to rank what they are looking for in their security solution. Survey methodology Report results are based on an Internet survey run by AV-Comparatives between 17th December 2013 and 17th January 2014. A total of 5,845 computer users from around the world anonymously answered the questions on the subject of computers and security. Key Results Among respondents, the three most important aspects of a security protection product were (1) Low impact on system performance (2) Good detection rate (3) Good malware removal and cleaning capabilities. These were the only criteria with over 60% response rate. Europe, North America and Central/South America were similar in terms of which products they used, with Avast topping the list. The share of Android as the mobile OS increased from 51% to 70%, while Symbian dropped from 21% to 5%. -

Transition Analysis of Cyber Attacks Based on Long-Term Observation—
2-3 nicterReport —TransitionAnalysisofCyberAttacksBasedon Long-termObservation— NAKAZATO Junji and OHTAKA Kazuhiro In this report, we provide a statistical data concerning cyber attacks and malwares based on a long-term network monitoring on the nicter. Especially, we show a continuous observation report of Conficker, which is a pandemic malware since November 2008. In addition, we report a transition analysis of the scale of botnet activities. Keywords Incident analysis, Darknet, Network monitoring, Malware analysis 1 Introduction leverages the traffic as detected by the four black hole sensors placed on different network We have been monitoring the IP address environments as shown by Fig. 1. space that is reachable and unused on the ● Sensor I : Structure where live nets and Internet (i.e. darknets) on a large-scale to darknets coexist in a class B understand the overall impact inflicted by network infectious activities including malware. This ● Sensor II : Structure where only darknets report analyzes the darknet traffic that has exist in a class B network been monitored and accumulated over six ● Sensor III : Structure where a /24 subnet years by an incident analysis center named in a class B network is a dark- *1 the nicter[1][2] to provide changing trends of net cyber attacks and fluctuation of attacker host ● Sensor IV : Structure where live nets and activities as obtained by long-term monitor- darknets coexist in a class B ing. In particular, we focus on Conficker, a network worm that has triggered large-scale infections The traffic obtained by these four sensors since November 2008, and report its impact on is analyzed by different analysis engines[3][4] the Internet and its current activities. -

Symantec Intelligence Report: June 2011
Symantec Intelligence Symantec Intelligence Report: June 2011 Three-quarters of spam send from botnets in June, and three months on, Rustock botnet remains dormant as Cutwail becomes most active; Pharmaceutical spam in decline as new Wiki- pharmacy brand emerges Welcome to the June edition of the Symantec Intelligence report, which for the first time combines the best research and analysis from the Symantec.cloud MessageLabs Intelligence Report and the Symantec State of Spam & Phishing Report. The new integrated report, the Symantec Intelligence Report, provides the latest analysis of cyber security threats, trends and insights from the Symantec Intelligence team concerning malware, spam, and other potentially harmful business risks. The data used to compile the analysis for this combined report includes data from May and June 2011. Report highlights Spam – 72.9% in June (a decrease of 2.9 percentage points since May 2011): page 11 Phishing – One in 330.6 emails identified as phishing (a decrease of 0.05 percentage points since May 2011): page 14 Malware – One in 300.7 emails in June contained malware (a decrease of 0.12 percentage points since May 2011): page 15 Malicious Web sites – 5,415 Web sites blocked per day (an increase of 70.8% since May 2011): page 17 35.1% of all malicious domains blocked were new in June (a decrease of 1.7 percentage points since May 2011): page 17 20.3% of all Web-based malware blocked was new in June (a decrease of 4.3 percentage points since May 2011): page 17 Review of Spam-sending botnets in June 2011: page 3 Clicking to Watch Videos Leads to Pharmacy Spam: page 6 Wiki for Everything, Even for Spam: page 7 Phishers Return for Tax Returns: page 8 Fake Donations Continue to Haunt Japan: page 9 Spam Subject Line Analysis: page 12 Best Practices for Enterprises and Users: page 19 Introduction from the editor Since the shutdown of the Rustock botnet in March1, spam volumes have never quite recovered as the volume of spam in global circulation each day continues to fluctuate, as shown in figure 1, below. -
Page 1 of 375 6/16/2021 File:///C:/Users/Rtroche
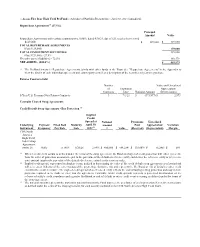
Page 1 of 375 :: Access Flex Bear High Yield ProFund :: Schedule of Portfolio Investments :: April 30, 2021 (unaudited) Repurchase Agreements(a) (27.5%) Principal Amount Value Repurchase Agreements with various counterparties, 0.00%, dated 4/30/21, due 5/3/21, total to be received $129,000. $ 129,000 $ 129,000 TOTAL REPURCHASE AGREEMENTS (Cost $129,000) 129,000 TOTAL INVESTMENT SECURITIES 129,000 (Cost $129,000) - 27.5% Net other assets (liabilities) - 72.5% 340,579 NET ASSETS - (100.0%) $ 469,579 (a) The ProFund invests in Repurchase Agreements jointly with other funds in the Trust. See "Repurchase Agreements" in the Appendix to view the details of each individual agreement and counterparty as well as a description of the securities subject to repurchase. Futures Contracts Sold Number Value and Unrealized of Expiration Appreciation/ Contracts Date Notional Amount (Depreciation) 5-Year U.S. Treasury Note Futures Contracts 3 7/1/21 $ (371,977) $ 2,973 Centrally Cleared Swap Agreements Credit Default Swap Agreements - Buy Protection (1) Implied Credit Spread at Notional Premiums Unrealized Underlying Payment Fixed Deal Maturity April 30, Amount Paid Appreciation/ Variation Instrument Frequency Pay Rate Date 2021(2) (3) Value (Received) (Depreciation) Margin CDX North America High Yield Index Swap Agreement; Series 36 Daily 5 .00% 6/20/26 2.89% $ 450,000 $ (44,254) $ (38,009) $ (6,245) $ 689 (1) When a credit event occurs as defined under the terms of the swap agreement, the Fund as a buyer of credit protection will either (i) receive from the seller of protection an amount equal to the par value of the defaulted reference entity and deliver the reference entity or (ii) receive a net amount equal to the par value of the defaulted reference entity less its recovery value. -

Aluria Security Center Avira Antivir Personaledition Classic 7
Aluria Security Center Avira AntiVir PersonalEdition Classic 7 - 8 Avira AntiVir Personal Free Antivirus ArcaVir Antivir/Internet Security 09.03.3201.9 x64 Ashampoo FireWall Ashampoo FireWall PRO 1.14 ALWIL Software Avast 4.0 Grisoft AVG 7.x Grisoft AVG 6.x Grisoft AVG 8.x Grisoft AVG 8.x x64 Avira Premium Security Suite 2006 Avira WebProtector 2.02 Avira AntiVir Personal - Free Antivirus 8.02 Avira AntiVir PersonalEdition Premium 7.06 AntiVir Windows Workstation 7.06.00.507 Kaspersky AntiViral Toolkit Pro BitDefender Free Edition BitDefender Internet Security BullGuard BullGuard AntiVirus BullGuard AntiVirus x64 CA eTrust AntiVirus 7 CA eTrust AntiVirus 7.1.0192 eTrust AntiVirus 7.1.194 CA eTrust AntiVirus 7.1 CA eTrust Suite Personal 2008 CA Licensing 1.57.1 CA Personal Firewall 9.1.0.26 CA Personal Firewall 2008 CA eTrust InoculateIT 6.0 ClamWin Antivirus ClamWin Antivirus x64 Comodo AntiSpam 2.6 Comodo AntiSpam 2.6 x64 COMODO AntiVirus 1.1 Comodo BOClean 4.25 COMODO Firewall Pro 1.0 - 3.x Comodo Internet Security 3.8.64739.471 Comodo Internet Security 3.8.64739.471 x64 Comodo Safe Surf 1.0.0.7 Comodo Safe Surf 1.0.0.7 x64 DrVirus 3.0 DrWeb for Windows 4.30 DrWeb Antivirus for Windows 4.30 Dr.Web AntiVirus 5 Dr.Web AntiVirus 5.0.0 EarthLink Protection Center PeoplePC Internet Security 1.5 PeoplePC Internet Security Pack / EarthLink Protection Center ESET NOD32 file on-access scanner ESET Smart Security 3.0 eTrust EZ Firewall 6.1.7.0 eTrust Personal Firewall 5.5.114 CA eTrust PestPatrol Anti-Spyware Corporate Edition CA eTrust PestPatrol -

Heuristic / Behavioural Protection Test 2013
Anti‐Virus Comparative ‐ Retrospective test – March 2013 www.av‐comparatives.org Anti-Virus Comparative Retrospective/Proactive test Heuristic and behavioural protection against new/unknown malicious software Language: English March 2013 Last revision: 16th August 2013 www.av-comparatives.org ‐ 1 ‐ Anti‐Virus Comparative ‐ Retrospective test – March 2013 www.av‐comparatives.org Contents 1. Introduction 3 2. Description 3 3. False-alarm test 5 4. Test Results 5 5. Summary results 6 6. Awards reached in this test 7 7. Copyright and disclaimer 8 ‐ 2 ‐ Anti‐Virus Comparative ‐ Retrospective test – March 2013 www.av‐comparatives.org 1. Introduction This test report is the second part of the March 2013 test1. The report is delivered several months later due to the large amount of work required, deeper analysis, preparation and dynamic execution of the retrospective test-set. This type of test is performed only once a year and includes a behavioural protection element, where any malware samples are executed, and the results observed. Although it is a lot of work, we usually receive good feedback from various vendors, as this type of test allows them to find bugs and areas for improvement in the behavioural routines (as this test evaluates specifically the proactive heuristic and behavioural protection components). The products used the same updates and signatures that they had on the 28th February 2013. This test shows the proactive protection capabilities that the products had at that time. We used 1,109 new, unique and very prevalent malware samples that appeared for the first time shortly after the freezing date. The size of the test-set has also been reduced to a smaller set containing only one unique sam- ple per variant, in order to enable vendors to peer-review our results in a timely manner. -

An Adaptive Multi-Layer Botnet Detection Technique Using Machine Learning Classifiers
applied sciences Article An Adaptive Multi-Layer Botnet Detection Technique Using Machine Learning Classifiers Riaz Ullah Khan 1,* , Xiaosong Zhang 1, Rajesh Kumar 1 , Abubakar Sharif 1, Noorbakhsh Amiri Golilarz 1 and Mamoun Alazab 2 1 Center of Cyber Security, School of Computer Science & Engineering, University of Electronic Science and Technology of China, Chengdu 611731, China; [email protected] (X.Z.); [email protected] (R.K.); [email protected] (A.S.); [email protected] (N.A.G.) 2 College of Engineering, IT and Environment, Charles Darwin University, Casuarina 0810, Australia; [email protected] * Correspondence: [email protected]; Tel.: +86-155-2076-3595 Received: 19 March 2019; Accepted: 24 April 2019; Published: 11 June 2019 Abstract: In recent years, the botnets have been the most common threats to network security since it exploits multiple malicious codes like a worm, Trojans, Rootkit, etc. The botnets have been used to carry phishing links, to perform attacks and provide malicious services on the internet. It is challenging to identify Peer-to-peer (P2P) botnets as compared to Internet Relay Chat (IRC), Hypertext Transfer Protocol (HTTP) and other types of botnets because P2P traffic has typical features of the centralization and distribution. To resolve the issues of P2P botnet identification, we propose an effective multi-layer traffic classification method by applying machine learning classifiers on features of network traffic. Our work presents a framework based on decision trees which effectively detects P2P botnets. A decision tree algorithm is applied for feature selection to extract the most relevant features and ignore the irrelevant features.