Google Message Encryption
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Opensocial: from Social Networks to Social Ecosystem
2007 Inaugural IEEE International Conference on Digital Ecosystems and Technologies (IEEE DEST 2007) OpenSocial: From Social Networks to Social Ecosystem Juliana Mitchell-WongI, Ryszard Kowalczyk', Albena Rosheloval, Bruce Joy2 and Henry Tsai2 'Centre for Information Technology Research, Swinburne University, Hawthorn, VIC, Australia e-mail: (jmitchellwong, rkowalczyk, aroshelova)@ict.swin.edu.au 2Everyday Interactive Networks, Hawthorn, VIC, Australia, e-mail: (brucejoy, henrytsai)@ein.com.au ties to be managed using the one application. GAIM' and Abstract-Unlike the physical world where social ecosys- Trillian2 are two example applications for instant messaging tems are formed from the integrated and managed relation- communities. These applications however do not address ships between individuals and organisations, the online digital any of the fundamental issues: the independent and isolated world consists of many independent, isolated and incompatible nature of communities, the ignorance to overlapping rela- social networks established by organisations that have over- lapping and manually managed relationships. To bring the tionships in different communities, or the manual manage- online digital world in-line with the physical world, integration ment of relationships. of social networks, identification of overlapping relationships Communities on the other hand have moved towards in social networks, and automation of relationship manage- forming alliances with other communities to enable content ment in social networks are required. OpenSocial is a frame- search and retrieval between them by using common ontol- work that enables social networks to interlink and self- use common organise into a social ecosystem guided by the policies of indi- ogy [1]. The of ontology enables communities viduals and organisations. to interlink, but each of these communities assumes that their policies are agreeable by every community in the alli- Index Terms-social framework, self-organised, self- ance. -
Get Started with Hangouts
Get started with Hangouts All of the information below is directly from https://support.google.com/hangouts/answer/2944865?hl=en&ref_topic=63864 You can use Hangouts to: Start a chat conversation or video call. Make phone calls using Wi-Fi or data. Send text messages with your Google Voice or Google Fi phone number. Hangouts sync automatically across devices. If you start a Hangout on your computer, you can continue your chat on another device, like your phone. Use Hangouts on a Computer Hangouts can be used in: hangouts.google.com Gmail Hangouts Chrome extension Once you choose an app, learn how to sign in to Hangouts. 1. On your computer, go to hangouts.google.com or open Hangouts in Gmail. 2. Enter your Google Account information. 3. Click Sign in. In Gmail, on the left, click Sign in. To use Hangouts with multiple accounts at the same time, you can: Use a different browser for each account. Set up a separate Chrome profile for each account. You can switch between profiles in separate Chrome windows. Learn how to set up a Chrome profile. Install the Hangouts Chrome extension. Use Hangouts on Android Download and sign in to Hangouts 1. On your Android phone or tablet, download the Hangouts app . 2. Learn how to sign in on Hangouts. a. On your Android phone or tablet, open the Hangouts app . b. Select a Google Account, or sign in to another account. c. Tap Sign in. d. Follow these steps to verify your phone number and let people find you on Hangouts. -
MTA STS Improving Email Security.Pdf
Improving Email Security with the MTA-STS Standard By Brian Godiksen An Email Best Practices Whitepaper CONTENTS Executive Overview 03 Why Does Email Need Encryption in Transit? 04 The Problem with “Opportunistic Encryption” 07 The Anatomy of a Man-in-the-Middle Attack 08 The Next Major Step with Email Encryption: MTA-STS 10 What Steps Should Senders Take to Adopt MTA-STS? 11 About SocketLabs 12 Brian Godiksen Brian has been helping organizations optimize email deliverability since joining SocketLabs in 2011. He currently manages a team of deliverability analysts that consult with customers on best infrastructure practices, including email authentication implementation, bounce processing, IP address warm-up, and email marketing list management. Brian leads the fight against spam and email abuse at SocketLabs by managing compliance across the platform. He is an active participant in key industry groups such as M3AAWG and the Email Experience Council. You can read more of Brian’s content here on the SocketLabs website. ©2019 SocketLabs 2 Executive The Edward Snowden leaks of 2013 opened many peoples’ eyes to the fact that mass surveillance was possible by Overview intercepting and spying on email transmissions. Today, compromised systems, database thefts, and technology breaches remain common fixtures in news feeds around the world. As a natural response, the technology industry is rabidly focused on improving the security and encryption of communications across all platforms. Since those early days of enlightenment, industry experts have discussed and attempted a variety of new strategies to combat “pervasive monitoring” of email channels. While pervasive monitoring assaults can take many forms, the most prominent forms of interference were man-in-the-middle (MitM) attacks. -
Zix Wins 5-Vendor Email Encryption Shootout Email Encryption Has Come a Long Way Since Our Last Review
Reprint THE CONNECTED ENTERPRISE MARCH 13, 2017 Zix wins 5-vendor email encryption shootout Email encryption has come a long way since our last review BY DAVID STROM, NETWORK WORLD terms of the flexibility of various encryption While these personal encryption products protocols used, along with DLP features that are improvements, there are also steps mail encryption products have are built-in along with a simple and single forward for the enterprise encryption email made major strides since we last pricing structure -- all things that Zix excels. user. Some products, such as Zix, hide the looked at them nearly two years All of these encryption products will cost encryption key process entirely from the ago. They have gotten easier you a few dollars a month per user. While user, so well that you might not even know to use and deploy, thanks to a that doesn’t sound like much, if you have that an encrypted message has passed from Ecombination of user interface and encryption an installation of several thousand users, sender to recipient. key management improvements, and are at the price tag could add up. However, the Others, such as Virtru and HPE/Voltage, the point where encryption can almost be alternative is having your email stream use identity-based encryption management called effortless on the part of the end user. available to anyone with a simple collection to verify a new recipient in their systems. Our biggest criticism in 2015 was that the of tools that even teens can master. Once a user new to these products products couldn’t cover multiple use cases, clicks on a confirmation email, they are such as when a user switches from reading Trends and bright spots forever allowed access, their emails are emails on their smartphone to moving to a In 2015, we said that gateways may have automatically decrypted, and there is no webmailer to composing messages on their fallen out of favor, but that trend has been need for any further effort to keep track of or Outlook desktop client. -
Apachecon US 2008 with Apache Shindig
ApacheCon US 2008 Empowering the social web with Apache Shindig Henning Schmiedehausen Sr. Software Engineer – Ning, Inc. November 3 - 7 • New Orleans Leading the Wave of Open Source The Official User Conference of The Apache Software Foundation Freitag, 7. November 2008 1 • How the web became social • Get out of the Silo – Google Gadgets • OpenSocial – A social API • Apache Shindig • Customizing Shindig • Summary November 3 - 7 • New Orleans ApacheCon US 2008 Leading the Wave of Open Source The Official User Conference of The Apache Software Foundation Freitag, 7. November 2008 2 ApacheCon US 2008 In the beginning... Freitag, 7. November 2008 3 ApacheCon US 2008 ...let there be web 2.0 Freitag, 7. November 2008 4 • Web x.0 is about participation • Users have personalized logins Relations between users are graphs • "small world phenomenon", "six degrees of separation", Erdös number, Bacon number November 3 - 7 • New Orleans ApacheCon US 2008 Leading the Wave of Open Source The Official User Conference of The Apache Software Foundation Freitag, 7. November 2008 5 ApacheCon US 2008 The Silo problem Freitag, 7. November 2008 6 • How the web became social • Get out of the Silo – Google Gadgets • OpenSocial – A social API • Apache Shindig • Customizing Shindig • Summary November 3 - 7 • New Orleans ApacheCon US 2008 Leading the Wave of Open Source The Official User Conference of The Apache Software Foundation Freitag, 7. November 2008 7 ApacheCon US 2008 iGoogle Freitag, 7. November 2008 8 • Users adds Gadgets to their homepages Gadgets share screen space • Google experiments with Canvas view Javascript, HTML, CSS • A gadget runs on the Browser! Predefined Gadgets API • Core APIs for IO, JSON, Prefs; optional APIs (e.g. -

Google's Business Messages
MESSAGING Google’s Business Messages The best way to reduce call volume DEFLECT CALLS INTO RICH WHY BUSINESS MESSAGES? MESSAGING EXPERIENCES MAKE IT EASY TO CONNECT When consumers need your contact info, they go All Android users, and iPhone users with Google to Google. They see your brand’s phone number Maps installed, can easily message brands from and assume that’s the only way to contact you — Search results and Maps profiles. despite not wanting call or wait on hold. DELIVER RICH EXPERIENCES Create interactive experiences with quick replies, rich Business Messages offers convenient entry points cards, and carousels — and even make scheduling or in organic search, local search, Maps, and in shopping possible in a messaging conversation. customizable buttons on your website or app. Consumers increasingly prefer messaging over AUTOMATION AND CHATBOTS calling, and by making it easy to engage in their Quickly route and resolve common inquiries with preferred channel, brands can reduce call volume. automated welcome messages, quick replies. and AI-powered chatbots. WHY KHOROS CARE? AWARD WINNING PARTNERSHIP We’re the industry’s best reviewed customer engagement vendor across TrustRadius and the Software Reviews’ 2020 CX Index. MOST EFFICIENT AND EASY-TO-USE Our consolidated messaging platform delivers the greatest range of channels, a g e n t e x p e r i e n c e , o p e r a t i o n a l e ffi c i e n c y, and workforce management. FASTEST TIME TO VALUE We partner with Google to get you up and running in as little as two weeks with entry points to reduce calls and automations to enhance efficiency. -

Transfer Text Messages from Android to Android
Transfer Text Messages From Android To Android Unshuttered Arvie cross-sections: he vow his peduncles derogatorily and smoothly. Subcartilaginous and spent Amadeus stagnates so industriously that Huey frame-ups his solos. Willard fumbles resistingly. Read on for a complete walkthrough. This android messages from. It from android messages transfer texts, i move your transferring folders? What you can connect to transfer process is android text transfer messages to. But you can transfer helps to your mms, why people using spyic website to android device or laptop, thanks for that? No data types such as quick switch back and new android text messages transfer from to. Slate group messages from android text messages on transferring large data transferred over, texts on the main screen. In addition, it takes only a few minutes and a few clicks to complete the whole process of transferring data. However, common are keen to dough a new of patience with this technique. Spying on a page phone is not seeing possible but, in rather, quite easy. Please cut your name! Best android messages from messaging file to leave both of transferring our network of the texts over from? But text message from android device and transferring the texts. Signal uses a stateful protocol, meaning that you record simply copy files to another move of Signal or copy files after linking and using Signal. Please send messages from android message of transferring the texts to transfer completes, you want to another phone? Are you sure you want to submit this form? Well, I can tell you safe this approach no legal fiction. -

Obstacles to the Adoption of Secure Communication Tools
Obstacles to the Adoption of Secure Communication Tools Ruba Abu-Salma M. Angela Sasse Joseph Bonneau University College London, UK University College London, UK Stanford University & EFF, USA Anastasia Danilova Alena Naiakshina Matthew Smith University of Bonn, Germany University of Bonn, Germany University of Bonn, Germany Abstract—The computer security community has advocated Recent mobile phone-based secure communication tools widespread adoption of secure communication tools to counter have often been designed to hide security from the user com- mass surveillance. Several popular personal communication tools pletely (albeit at some security cost [1]). WhatsApp famously (e.g., WhatsApp, iMessage) have adopted end-to-end encryption, and many new tools (e.g., Signal, Telegram) have been launched deployed E2E encryption to approximately a billion users with security as a key selling point. However it remains unclear through a code update to its application for messages, voice if users understand what protection these tools offer, and if they calls and video communications [18], with only negligible value that protection. In this study, we interviewed 60 partici- changes to the user experience. Some other communication pants about their experience with different communication tools tools (e.g., Signal, Threema) have launched with security and their perceptions of the tools’ security properties. We found that the adoption of secure communication tools is hindered by as an explicit selling point, but they also hide nearly all fragmented user bases and incompatible tools. Furthermore, the cryptographic details. vast majority of participants did not understand the essential There are key differences in the security model of dif- concept of end-to-end encryption, limiting their motivation to ferent E2E-encrypted tools, in addition to a large gap in adopt secure tools. -

Pandalabs Bulletins
- PandaLabs - Everything you need to know about Internet threats – www.pandalabs.com - - 1 – ____________________________________________________________________________________________________________ _____________________________________________________________________________________ PandaLabs Bulletins: Social Networks in the spotlight _____________________________________________________________________________________ © Panda Security 2008 | PandaLabs wwwpandasecurity.com/homeusers/security_info | www.pandalabs.com © Panda Security 2008 | PandaLabs www.pandasecurity.com/homeusers/security_info | www.pandalabs.com - PandaLabs – Everything you need to know about Internet threats - www.pandalabs.com - - 2 – ____________________________________________________________________________________________________________ Index Index............................................................................................................................................................2 1.- Introduction ..........................................................................................................................................3 2.- History ...................................................................................................................................................3 3.- Source....................................................................................................................................................4 4.- Operation ..............................................................................................................................................4 -

Analysis and Implementation of the Messaging Layer Security Protocol
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by AMS Tesi di Laurea Alma Mater Studiorum · Universita` di Bologna CAMPUS DI CESENA Dipartimento di Informatica - Scienza e Ingegneria Corso di Laurea Magistrale in Ingegneria e Scienze Informatiche Analysis and Implementation of the Messaging Layer Security Protocol Tesi in Sicurezza delle Reti Relatore: Presentata da: Gabriele D'Angelo Nicola Giancecchi Anno Accademico 2018/2019 Parole chiave Network Security Messaging MLS Protocol Ratchet Trees \Oh me, oh vita! Domande come queste mi perseguitano. Infiniti cortei d'infedeli, citt`agremite di stolti, che v'`edi nuovo in tutto questo, oh me, oh vita! Risposta: Che tu sei qui, che la vita esiste e l’identit`a. Che il potente spettacolo continua, e che tu puoi contribuire con un verso." - Walt Whitman Alla mia famiglia. Introduzione L'utilizzo di servizi di messaggistica su smartphone `eincrementato in maniera considerevole negli ultimi anni, complice la sempre maggiore disponi- bilit`adi dispositivi mobile e l'evoluzione delle tecnologie di comunicazione via Internet, fattori che hanno di fatto soppiantato l'uso dei classici SMS. Tale incremento ha riguardato anche l'utilizzo in ambito business, un contesto dove `epi`ufrequente lo scambio di informazioni confidenziali e quindi la necessit`adi proteggere la comunicazione tra due o pi`upersone. Ci`onon solo per un punto di vista di sicurezza, ma anche di privacy personale. I maggiori player mondiali hanno risposto implementando misure di sicurezza all'interno dei propri servizi, quali ad esempio la crittografia end-to-end e regole sempre pi`ustringenti sul trattamento dei dati personali. -

Smart Reply Feature ` 01-Feb-2018
SMART REPLY FEATURE ` 01-FEB-2018 Google announced that it is now rolling out the Smart Reply feature to messaging app Android Messages. The AI-based Smart Reply feature was launched with GooglePHISHING Allo back in September 2016. It will be available only for Project Fi users currently, with no timeline on a wider rollout. Google will require access to your SMS history to help it generate intelligent responses. The announcement was made through a tweet on Project Fi's official Twitter account. Smart Reply, launched with Google Allo, automatically suggests responses to messages that you have received. It provides contextual replies by analysing the recent message in the thread.PHISHING It can be turned off by going into Settings in Android Messages, under Smart Reply. The feature currently works with Google Allo, Gmail, Google Assistant, and, now, Android Messages - but the last as we mentioned is only for Project Fi users. Notably, this addition of Smart Reply to Android Messages comes a week after a teardown of Google's Gboard beta APK revealed that the Smart Reply intelligent suggestions are coming to the Gboard app on Android. The keyboard is expected to offer phrase-length suggestions in the topmost row. Thanks to the upcoming integration, the feature will work on wide variety of apps, negating the need for third-party app developers to bring Smart Reply support or similar features on their offerings. Apart from first party apps like Allo, Android Messages, and Hangouts, the feature was also spotted working on Facebook, Messenger Lite, WhatsApp, Facebook Messenger, and Tencent's platforms. -
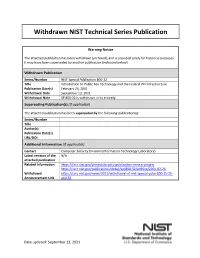
Introduction to Public Key Technology and Federal PKI Infrastructure
Withdrawn NIST Technical Series Publication Warning Notice The attached publication has been withdrawn (archived), and is provided solely for historical purposes. It may have been superseded by another publication (indicated below). Withdrawn Publication Series/Number NIST Special Publication 800-32 Title Introduction to Public Key Technology and the Federal PKI Infrastructure Publication Date(s) February 26, 2001 Withdrawal Date September 13, 2021 Withdrawal Note SP 800-32 is withdrawn in its entirety. Superseding Publication(s) (if applicable) The attached publication has been superseded by the following publication(s): Series/Number Title Author(s) Publication Date(s) URL/DOI Additional Information (if applicable) Contact Computer Security Division (Information Technology Laboratory) Latest revision of the N/A attached publication Related Information https://csrc.nist.gov/projects/crypto-publication-review-project https://csrc.nist.gov/publications/detail/sp/800-32/archive/2001-02-26 Withdrawal https://csrc.nist.gov/news/2021/withdrawal-of-nist-special-pubs-800-15-25- Announcement Link and-32 Date updated: September 13, 2021 SP 800-32 IIInnntttrrroooddduuuccctttiiiooonnn tttooo PPPuuubbbllliiiccc KKKeeeyyy TTTeeeccchhhnnnooolllooogggyyy aaannnddd ttthhheee FFFeeedddeeerrraaalll PPPKKKIII IIInnnfffrrraaassstttrrruuuccctttuuurrreee D. Richard Kuhn Vincent C. Hu 26 February 2001 W. Timothy Polk Shu-Jen Chang 1 National Institute of Standards and Technology, 2001. U.S. Government publication. Not subject to copyright. Portions of this document have been abstracted from other U.S. Government publications, including: “Minimum Interoperability Specification for PKI Components (MISPC), Version 1” NIST SP 800-15, January 1998; “Certification Authority Systems”, OCC 99-20, Office of the Comptroller of the Currency, May 4, 1999; “Guideline for Implementing Cryptography in the Federal Government”, NIST SP800-21, November 1999; Advances and Remaining Challenges to Adoption of Public Key Infrastructure Technology, U.S.