Oral History of Fernando Corbató
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Topic a Dataflow Model of Computation
Department of Electrical and Computer Engineering Computer Architecture and Parallel Systems Laboratory - CAPSL Topic A Dataflow Model of Computation CPEG 852 - Spring 2014 Advanced Topics in Computing Systems Guang R. Gao ACM Fellow and IEEE Fellow Endowed Distinguished Professor Electrical & Computer Engineering University of Delaware CPEG852-Spring14: Topic A - Dataflow - 1 [email protected] Outline • Parallel Program Execution Models • Dataflow Models of Computation • Dataflow Graphs and Properties • Three Dataflow Models – Static – Recursive Program Graph – Dynamic • Dataflow Architectures CPEG852-Spring14: Topic A - Dataflow - 1 2 Terminology Clarification • Parallel Model of Computation – Parallel Models for Algorithm Designers – Parallel Models for System Designers • Parallel Programming Models • Parallel Execution Models • Parallel Architecture Models CPEG852-Spring14: Topic A - Dataflow - 1 3 What is a Program Execution Model? . Application Code . Software Packages User Code . Program Libraries . Compilers . Utility Applications PXM (API) . Hardware System . Runtime Code . Operating System CPEG852-Spring14: Topic A - Dataflow - 1 4 Features a User Program Depends On . Procedures; call/return Features expressed within .Access to parameters and a Programming language variables .Use of data structures (static and dynamic) But that’s not all !! . File creation, naming and access Features expressed Outside .Object directories a (typical) programming .Communication: networks language and peripherals .Concurrency: coordination; scheduling CPEG852-Spring14: Topic A - Dataflow - 1 5 Developments in the 1960s, 1970s Highlights 1960 Other Events . Burroughs B5000 Project . Project MAC Funded at MIT Started . Rice University Computer . IBM announces System 360 . Vienna Definition Method . Tasking introduced in Algol . Common Base Language, 1970 68 and PL/I Dennis . Burroughs builds Robert . Contour Model, Johnston Barton’s DDM1 . Book on the B6700, . -
NASA Contrattbr 4Report 178229 S E M I a N N U a L R E P O
NASA Contrattbr 4Report 178229 ICASE SEMIANNUAL REPORT April 1, 1986 through September 30, 1986 Contract No. NAS1-18107 January 1987 INSTITUTE FOR COMPUTER APPLICATIONS IN SCIENCE AND ENGINEERING NASA Langley Research Center, Hampton, Virginia 23665 Operatsd by the Universities Space Research Association National Aeronautics and Space Ad minis t rat ion bnglay Research Center HamDton,Virginia23665 CONTENTS Page Introduction .............................................................. iii Research in erogress ...................................................... 1 Reports and Abstracts ..................................................... 32 ICASE Colloquia........................................................... 49 ICASE Summer Activities ................................................... 52 Other Activities .......................................................... 58 ICASE Staff ............................................................... 60 i INTRODUCTION The Institute for Computer Applications in Science and Engineering (ICASE) is operated at the Langley Research Center (LaRC) of NASA by the Universities Space Research Associat€on (USRA) under a contract with the Center. USRA is a nonpro€it consortium of major U. S. colleges and universities. The Institute conducts unclassified basic research in applied mathematics, numerical analysis, and computer science in order to extend and improve problem-solving capabilities in science and engineering, particularly in aeronautics and space. ICASE has a small permanent staff. Research -

The Computational Attitude in Music Theory
The Computational Attitude in Music Theory Eamonn Bell Submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy in the Graduate School of Arts and Sciences COLUMBIA UNIVERSITY 2019 © 2019 Eamonn Bell All rights reserved ABSTRACT The Computational Attitude in Music Theory Eamonn Bell Music studies’s turn to computation during the twentieth century has engendered particular habits of thought about music, habits that remain in operation long after the music scholar has stepped away from the computer. The computational attitude is a way of thinking about music that is learned at the computer but can be applied away from it. It may be manifest in actual computer use, or in invocations of computationalism, a theory of mind whose influence on twentieth-century music theory is palpable. It may also be manifest in more informal discussions about music, which make liberal use of computational metaphors. In Chapter 1, I describe this attitude, the stakes for considering the computer as one of its instruments, and the kinds of historical sources and methodologies we might draw on to chart its ascendance. The remainder of this dissertation considers distinct and varied cases from the mid-twentieth century in which computers or computationalist musical ideas were used to pursue new musical objects, to quantify and classify musical scores as data, and to instantiate a generally music-structuralist mode of analysis. I present an account of the decades-long effort to prepare an exhaustive and accurate catalog of the all-interval twelve-tone series (Chapter 2). This problem was first posed in the 1920s but was not solved until 1959, when the composer Hanns Jelinek collaborated with the computer engineer Heinz Zemanek to jointly develop and run a computer program. -

Operating Systems & Virtualisation Security Knowledge Area
Operating Systems & Virtualisation Security Knowledge Area Issue 1.0 Herbert Bos Vrije Universiteit Amsterdam EDITOR Andrew Martin Oxford University REVIEWERS Chris Dalton Hewlett Packard David Lie University of Toronto Gernot Heiser University of New South Wales Mathias Payer École Polytechnique Fédérale de Lausanne The Cyber Security Body Of Knowledge www.cybok.org COPYRIGHT © Crown Copyright, The National Cyber Security Centre 2019. This information is licensed under the Open Government Licence v3.0. To view this licence, visit: http://www.nationalarchives.gov.uk/doc/open-government-licence/ When you use this information under the Open Government Licence, you should include the following attribution: CyBOK © Crown Copyright, The National Cyber Security Centre 2018, li- censed under the Open Government Licence: http://www.nationalarchives.gov.uk/doc/open- government-licence/. The CyBOK project would like to understand how the CyBOK is being used and its uptake. The project would like organisations using, or intending to use, CyBOK for the purposes of education, training, course development, professional development etc. to contact it at con- [email protected] to let the project know how they are using CyBOK. Issue 1.0 is a stable public release of the Operating Systems & Virtualisation Security Knowl- edge Area. However, it should be noted that a fully-collated CyBOK document which includes all of the Knowledge Areas is anticipated to be released by the end of July 2019. This will likely include updated page layout and formatting of the individual Knowledge Areas KA Operating Systems & Virtualisation Security j October 2019 Page 1 The Cyber Security Body Of Knowledge www.cybok.org INTRODUCTION In this Knowledge Area, we introduce the principles, primitives and practices for ensuring se- curity at the operating system and hypervisor levels. -
UC Berkeley Previously Published Works
UC Berkeley UC Berkeley Previously Published Works Title Building the Second Mind, 1961-1980: From the Ascendancy of ARPA-IPTO to the Advent of Commercial Expert Systems Permalink https://escholarship.org/uc/item/7ck3q4f0 ISBN 978-0-989453-4-6 Author Skinner, Rebecca Elizabeth Publication Date 2013-12-31 eScholarship.org Powered by the California Digital Library University of California Building the Second Mind, 1961-1980: From the Ascendancy of ARPA to the Advent of Commercial Expert Systems copyright 2013 Rebecca E. Skinner ISBN 978 09894543-4-6 Forward Part I. Introduction Preface Chapter 1. Introduction: The Status Quo of AI in 1961 Part II. Twin Bolts of Lightning Chapter 2. The Integrated Circuit Chapter 3. The Advanced Research Projects Agency and the Foundation of the IPTO Chapter 4. Hardware, Systems and Applications in the 1960s Part II. The Belle Epoque of the 1960s Chapter 5. MIT: Work in AI in the Early and Mid-1960s Chapter 6. CMU: From the General Problem Solver to the Physical Symbol System and Production Systems Chapter 7. Stanford University and SRI Part III. The Challenges of 1970 Chapter 8. The Mansfield Amendment, “The Heilmeier Era”, and the Crisis in Research Funding Chapter 9. The AI Culture Wars: the War Inside AI and Academia Chapter 10. The AI Culture Wars: Popular Culture Part IV. Big Ideas and Hardware Improvements in the 1970s invert these and put the hardware chapter first Chapter 11. AI at MIT in the 1970s: The Semantic Fallout of NLR and Vision Chapter 12. Hardware, Software, and Applications in the 1970s Chapter 13. -
MTS on Wikipedia Snapshot Taken 9 January 2011
MTS on Wikipedia Snapshot taken 9 January 2011 PDF generated using the open source mwlib toolkit. See http://code.pediapress.com/ for more information. PDF generated at: Sun, 09 Jan 2011 13:08:01 UTC Contents Articles Michigan Terminal System 1 MTS system architecture 17 IBM System/360 Model 67 40 MAD programming language 46 UBC PLUS 55 Micro DBMS 57 Bruce Arden 58 Bernard Galler 59 TSS/360 60 References Article Sources and Contributors 64 Image Sources, Licenses and Contributors 65 Article Licenses License 66 Michigan Terminal System 1 Michigan Terminal System The MTS welcome screen as seen through a 3270 terminal emulator. Company / developer University of Michigan and 7 other universities in the U.S., Canada, and the UK Programmed in various languages, mostly 360/370 Assembler Working state Historic Initial release 1967 Latest stable release 6.0 / 1988 (final) Available language(s) English Available programming Assembler, FORTRAN, PL/I, PLUS, ALGOL W, Pascal, C, LISP, SNOBOL4, COBOL, PL360, languages(s) MAD/I, GOM (Good Old Mad), APL, and many more Supported platforms IBM S/360-67, IBM S/370 and successors History of IBM mainframe operating systems On early mainframe computers: • GM OS & GM-NAA I/O 1955 • BESYS 1957 • UMES 1958 • SOS 1959 • IBSYS 1960 • CTSS 1961 On S/360 and successors: • BOS/360 1965 • TOS/360 1965 • TSS/360 1967 • MTS 1967 • ORVYL 1967 • MUSIC 1972 • MUSIC/SP 1985 • DOS/360 and successors 1966 • DOS/VS 1972 • DOS/VSE 1980s • VSE/SP late 1980s • VSE/ESA 1991 • z/VSE 2005 Michigan Terminal System 2 • OS/360 and successors -

Oral History of Brian Kernighan
Oral History of Brian Kernighan Interviewed by: John R. Mashey Recorded April 24, 2017 Princeton, NJ CHM Reference number: X8185.2017 © 2017 Computer History Museum Oral History of Brian Kernighan Mashey: Well, hello, Brian. It’s great to see you again. Been a long time. So we’re here at Princeton, with Brian Kernighan, and we want to go do a whole oral history with him. So why don’t we start at the beginning. As I recall, you’re Canadian. Kernighan: That is right. I was born in Toronto long ago, and spent my early years in the city of Toronto. Moved west to a small town, what was then a small town, when I was in the middle of high school, and then went to the University of Toronto for my undergraduate degree, and then came here to Princeton for graduate school. Mashey: And what was your undergraduate work in? Kernighan: It was in one of these catch-all courses called Engineering Physics. It was for people who were kind of interested in engineering and math and science and didn’t have a clue what they wanted to actually do. Mashey: <laughs> So how did you come to be down here? Kernighan: I think it was kind of an accident. It was relatively unusual for people from Canada to wind up in the United States for graduate school at that point, but I thought I would try something different and so I applied to six or seven different schools in the United States, got accepted at some of them, and then it was a question of balancing things like, “Well, they promised that they would get you out in a certain number of years and they promised that they would give you money,” but the question is whether, either that was true or not and I don’t know. -

Turing Award • John Von Neumann Medal • NAE, NAS, AAAS Fellow
15-712: Advanced Operating Systems & Distributed Systems A Few Classics Prof. Phillip Gibbons Spring 2021, Lecture 2 Today’s Reminders / Announcements • Summaries are to be submitted via Canvas by class time • Announcements and Q&A are via Piazza (please enroll) • Office Hours: – Prof. Phil Gibbons: Fri 1-2 pm & by appointment – TA Jack Kosaian: Mon 1-2 pm – Zoom links: See canvas/Zoom 2 CS is a Fast Moving Field: Why Read/Discuss Old Papers? “Those who cannot remember the past are condemned to repeat it.” - George Santayana, The Life of Reason, Volume 1, 1905 See what breakthrough research ideas look like when first presented 3 The Rise of Worse is Better Richard Gabriel 1991 • MIT/Stanford style of design: “the right thing” – Simplicity in interface 1st, implementation 2nd – Correctness in all observable aspects required – Consistency – Completeness: cover as many important situations as is practical • Unix/C style: “worse is better” – Simplicity in implementation 1st, interface 2nd – Correctness, but simplicity trumps correctness – Consistency is nice to have – Completeness is lowest priority 4 Worse-is-better is Better for SW • Worse-is-better has better survival characteristics than the-right-thing • Unix and C are the ultimate computer viruses – Simple structures, easy to port, required few machine resources to run, provide 50-80% of what you want – Programmer conditioned to sacrifice some safety, convenience, and hassle to get good performance and modest resource use – First gain acceptance, condition users to expect less, later -

Interview with Barbara Liskov ACM Turing Award Recipient 2008 Done at MIT April 20, 2016 Interviewer Was Tom Van Vleck
B. Liskov Interview 1 Interview with Barbara Liskov ACM Turing Award Recipient 2008 Done at MIT April 20, 2016 Interviewer was Tom Van Vleck Interviewer is noted as “TVV” Dr. Liskov is noted as “BL” ?? = inaudible (with timestamp) or [ ] for phonetic [some slight changes have been made in this transcript to improve the readability, but no material changes were made to the content] TVV: Hello, I’m Tom Van Vleck, and I have the honor today to interview Professor Barbara Liskov, the 2008 ACM Turing Award winner. Today is April 20th, 2016. TVV: To start with, why don’t you tell us a little bit about your upbringing, where you lived, and how you got into the business? BL: I grew up in San Francisco. I was actually born in Los Angeles, so I’m a native Californian. When I was growing up, it was definitely not considered the thing to do for a young girl to be interested in math and science. In fact, in those days, the message that you got was that you were supposed to get married and have children and not have a job. Nevertheless, I was always encouraged by my parents to take academics seriously. My mother was a college grad as well as my father, so it was expected that I would go to college, which in those times was not that common. Maybe 20% of the high school class would go on to college and the rest would not. I was always very interested in math and science, so I took all the courses that were offered at my high school, which wasn’t a tremendous number compared to what is available today. -
Role of Operating System
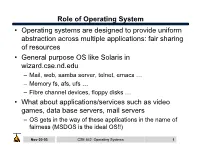
Role of Operating System • Operating systems are designed to provide uniform abstraction across multiple applications: fair sharing of resources • General purpose OS like Solaris in wizard.cse.nd.edu – Mail, web, samba server, telnet, emacs … – Memory fs, afs, ufs … – Fibre channel devices, floppy disks … • What about applications/services such as video games, data base servers, mail servers – OS gets in the way of these applications in the name of fairness (MSDOS is the ideal OS!!) Nov-20-03 CSE 542: Operating Systems 1 What is the role of OS? • Create multiple virtual machines that each user can control all to themselves – IBM 360/370 … • Monolithic kernel: Linux – One kernel provides all services. – New paradigms are harder to implement – May not be optimal for any one application • Microkernel: Mach – Microkernel provides minimal service – Application servers provide OS functionality • Nanokernel: OS is implemented as application level libraries Nov-20-03 CSE 542: Operating Systems 2 Case study: Multics • Goal: Develop a convenient, interactive, useable time shared computer system that could support many users. – Bell Labs and GE in 1965 joined an effort underway at MIT (CTSS) on Multics (Multiplexed Information and Computing Service) mainframe timesharing system. • Multics was designed to the swiss army knife of OS • Multics achieved most of the these goals, but it took a long time – One of the negative contribution was the development of simple yet powerful abstractions (UNIX) Nov-20-03 CSE 542: Operating Systems 3 Multics: Designed to be the ultimate OS • “One of the overall design goals is to create a computing system which is capable of meeting almost all of the present and near-future requirements of a large computer utility. -

Corbató Transcript Final
A. M. Turing Award Oral History Interview with Fernando J. (“Corby”) Corbató by Steve Webber Plum Island, Massachusetts April 6, 2018 Webber: Hi. My name is Steve Webber. It’s April 6th, 2018. I’m here to interview Fernando Corbató – everyone knows him as “Corby” – the ACM Turing Award winner of 1990 for his contributions to computer science. So Corby, tell me about your early life, where you went to school, where you were born, your family, your parents, anything that’s interesting for the history of computer science. Corbató: Well, my parents met at University of California, Berkeley, and they… My father got his doctorate in Spanish literature – and I was born in Oakland, California – and proceeded to… he got his first position at UCLA, which was then a new campus in Los Angeles, as a professor of Spanish literature. So I of course wasn’t very conscious of much at those ages, but I basically grew up in West Los Angeles and went to public high schools, first grammar school, then junior high, and then I began high school. Webber: What were your favorite subjects in high school? I tended to enjoy the mathematics type of subjects. As I recall, algebra was easy and enjoyable. And the… one of the results of that was that I was in high school at the time when World War II… when Pearl Harbor occurred and MIT was… rather the United States was drawn into the war. As I recall, Pearl Harbor occurred… I think it was on a Sunday, but one of the results was that it shocked the US into reacting to the war effort, and one of the results was that everything went into kind of a wartime footing. -

Notes on the History of Fork-And-Join Linus Nyman and Mikael Laakso Hanken School of Economics
Notes on the history of fork-and-join Linus Nyman and Mikael Laakso Hanken School of Economics As part of a PhD on code forking in open source software, Linus Nyman looked into the origins of how the practice came to be called forking.1 This search led back to the early history of the fork system call. Having not previously seen such a history published, this anecdote looks back at the birth of the fork system call to share what was learned, as remembered by its pioneers. The fork call allows a process (or running program) to create new processes. The original is deemed the parent process and the newly created one its child. On multiprocessor systems, these processes can run concurrently in parallel.2 Since its birth 50 years ago, the fork has remained a central element of modern computing, both with regards to software development principles and, by extension, to hardware design, which increasingly accommodates parallelism in process execution. The fork system call is imagined The year was 1962. Melvin Conway, later to become known for “Conway’s Law,”3 was troubled by what seemed an unnecessary inefficiency in computing. As Conway recalls:4 I was in the US Air Force at the time – involved with computer procurement – and I noticed that no vendor was distinguishing between “processor” and “process.” That is, when a proposal involved a multiprocessor design, each processor was committed to a single process. By late 1962, Conway had begun contemplating the idea of using a record to carry the status of a process.