The Best Ways to Stop Malware and Ransomware That No One Else Will Tell You Roger A
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Windows 7 Operating Guide
Welcome to Windows 7 1 1 You told us what you wanted. We listened. This Windows® 7 Product Guide highlights the new and improved features that will help deliver the one thing you said you wanted the most: Your PC, simplified. 3 3 Contents INTRODUCTION TO WINDOWS 7 6 DESIGNING WINDOWS 7 8 Market Trends that Inspired Windows 7 9 WINDOWS 7 EDITIONS 10 Windows 7 Starter 11 Windows 7 Home Basic 11 Windows 7 Home Premium 12 Windows 7 Professional 12 Windows 7 Enterprise / Windows 7 Ultimate 13 Windows Anytime Upgrade 14 Microsoft Desktop Optimization Pack 14 Windows 7 Editions Comparison 15 GETTING STARTED WITH WINDOWS 7 16 Upgrading a PC to Windows 7 16 WHAT’S NEW IN WINDOWS 7 20 Top Features for You 20 Top Features for IT Professionals 22 Application and Device Compatibility 23 WINDOWS 7 FOR YOU 24 WINDOWS 7 FOR YOU: SIMPLIFIES EVERYDAY TASKS 28 Simple to Navigate 28 Easier to Find Things 35 Easy to Browse the Web 38 Easy to Connect PCs and Manage Devices 41 Easy to Communicate and Share 47 WINDOWS 7 FOR YOU: WORKS THE WAY YOU WANT 50 Speed, Reliability, and Responsiveness 50 More Secure 55 Compatible with You 62 Better Troubleshooting and Problem Solving 66 WINDOWS 7 FOR YOU: MAKES NEW THINGS POSSIBLE 70 Media the Way You Want It 70 Work Anywhere 81 New Ways to Engage 84 INTRODUCTION TO WINDOWS 7 6 WINDOWS 7 FOR IT PROFESSIONALS 88 DESIGNING WINDOWS 7 8 WINDOWS 7 FOR IT PROFESSIONALS: Market Trends that Inspired Windows 7 9 MAKE PEOPLE PRODUCTIVE ANYWHERE 92 WINDOWS 7 EDITIONS 10 Remove Barriers to Information 92 Windows 7 Starter 11 Access -

Pass-The-Hash Attacks
Pass-the-Hash Attacks Michael Grafnetter www.dsinternals.com Agenda . PtH Attack Anatomy . Mitigation – Proactive – Reactive . Windows 10 + Windows Server 2016 PtH History and Future . 1988 – Microsoft releases Lan Manager . 1997 – Pass-the-Hash demonstrated using a modified Samba . 2007 – Benjamin Delpy releases Mimikatz . 2008 – Pass-the-Ticket attack demonstrated . 2012 – Microsoft releases Pass-the-Hash guidance . 2013 – Windows contains built-in defenses against PtH . 2015 – Michael Grafnetter releases the DSInternals tools ;-) . 2016 – More defense mechanisms coming to Windows PtH Attack Anatomy Theft Use Compromise Lateral and Vertical Movement Metasploit Framework Metasploit Framework Mimikatz DEMO Pass-the-Hash + RDP LSASS NTLM Hashes Passing the Hash PtH Attack Premises Single Symmetric Pass-the-Hash Sign-On Cryptography Attack Surface Stealing the Hash Credentials Lifecycle / Attack Vectors Credentials Lifecycle / Attack Vectors Hashes in SAM/AD Authentication Method Hash Function Salted LM DES NO NTLM, NTLMv2 MD4 NO Kerberos (RC4) MD4 NO Kerberos (AES) PBKDF2 (4096*HMAC_SHA1) YES Digest MD5 YES Active Directory Database - Offline . Files – C:\Windows\NTDS\ntds.dit – C:\Windows\System32\config\SYSTEM . Acquire – Locally: ntdsutil IFM – Remotely: WMI (Win32_Process), psexec – Offline: VHDs, VMDKs, Backups . Extract – Windows: DSInternals PowerShell Module – Linux: NTDSXtract DEMO Extracting hashes from ntds.dit GUI Tools KRBTGT Account Proactive Measures . Encryption . RODC . Backup protection . Regular password changes Active Directory Database - Online . MS-DRSR/RPC Go to www.dsinternals.com for demo ;-) Proactive Measures . Avoid using administrative accounts . Do not run untrusted SW . Do not delegate the right to replicate directory changes . Use an application firewall / IDS ??? SAM Database . Offline – Files • C:\Windows\System32\config\SAM • C:\Windows\System32\config\SYSTEM – Tools • Windows Password Recovery . -

Administrative Guide for Windows 10 and Windows Server Fall Creators Update (1709)
Operational and Administrative Guidance Microsoft Windows 10 and Windows Server Common Criteria Evaluation for Microsoft Windows 10 and Windows Server Version 1903 (May 2019 Update) General Purpose Operating System Protection Profile © 2019 Microsoft. All rights reserved. Microsoft Windows 10 GP OS Administrative Guidance Copyright and disclaimer The information contained in this document represents the current view of Microsoft Corporation on the issues discussed as of the date of publication. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information presented after the date of publication. This document is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS OR IMPLIED, AS TO THE INFORMATION IN THIS DOCUMENT. Complying with all applicable copyright laws is the responsibility of the user. This work is licensed under the Creative Commons Attribution-NoDerivs-NonCommercial VLicense (which allows redistribution of the work). To view a copy of this license, visithttp://creativecommons.org/licenses/by-nd-nc/1.0/ or send a letter to Creative Commons, 559 Nathan Abbott Way, Stanford, California 94305, USA. Microsoft may have patents, patent applications, trademarks, copyrights, or other intellectual property rights covering subject matter in this document. Except as expressly provided in any written license agreement from Microsoft, the furnishing of this document does not give you any license to these patents, trademarks, copyrights, or other intellectual property. The example companies, organizations, products, people and events depicted herein are fictitious. No association with any real company, organization, product, person or event is intended or should be inferred. -

Guide to Hardening Windows 10 Technical Guide
NOVEMBER 2020 Guide to Hardening Windows 10 For Administrators, Developers and Office Workers TABLE OF CONTENTS Introduction .......................................................................................................................... 4 Prerequisites ............................................................................................................................ 4 User roles ................................................................................................................................. 4 EFI (BIOS) Configuration ...................................................................................................... 5 To be enabled: ......................................................................................................................... 5 To be disabled: ......................................................................................................................... 5 Windows Defender Firewall .................................................................................................. 6 Enable logging of dropped packets ............................................................................................. 6 Disable enforcement of local rules and disable notifications .......................................................... 7 Block outbound connections by default ....................................................................................... 8 Secure potentially vulnerable protocols ...................................................................................... -
Active Directory for the Security Professional
Beyond the MCSE: Active Directory for the Security Professional Sean Metcalf Trimarc TrimarcSecurity.com Black Hat USA 2016 Table of Contents Overview ....................................................................................................................................................... 4 Differing Views of Active Directory ............................................................................................................... 5 Active Directory Components ....................................................................................................................... 6 Administration .......................................................................................................................................... 6 Forest ........................................................................................................................................................ 9 Domains .................................................................................................................................................. 10 Schema .................................................................................................................................................... 10 Trusts ....................................................................................................................................................... 11 Sites, Subnets, & Replication .................................................................................................................. 13 Organizational -

Preparing for Installation Requirements | 3
Preparing for LESSON 1 Installation Requirements 70‐698 EXAM OBJECTIVE Objective 1.1 – Prepare for installation requirements. This objective may include but is not limited to: Determine hardware requirements and compatibility; choose between an upgrade and a clean installation; determine appro- priate editions according to device type; determine requirements for particular features, such as Hyper‐V, Cortana, Miracast, Virtual Smart Cards, and Secure Boot; determine and create appropriate installation media. Objective 1.2 – Install Windows. This objective may include but is not limited to: Install on bootable USB. * Other Objective 1.2 topics are covered in Lesson 2. LESSON HEADING EXAM OBJECTIVE Preparing for a Windows 10 Installation Determining Hardware Requirements and Determine hardware requirements and compatibility Compatibility Choosing Between an Upgrade and a Clean Choose between an upgrade and a clean installation Installation Determining Appropriate Editions According to Determine appropriate editions according to device Device Type type Determining Requirements for Particular Determine requirements for particular features Features Determining and Creating Appropriate Determine and create appropriate installation media Installation Media Install on bootable USB COPYRIGHTED MATERIAL KEY TERMS AppLocker Continuum DirectAccess Assigned Access 8.1 Cortana EFS BitLocker Credential Guard Enterprise Mode Internet BranchCache Current Branch for Business Explorer (EMIE) Business Store desktop PC Group Policy management clean installation -
Microsoft Windows Common Criteria Evaluation Security Target
Microsoft Common Criteria Security Target Microsoft Windows Common Criteria Evaluation Microsoft Windows 10 (Fall Creators Update) Microsoft Windows Server (Fall Creators Update) Security Target Document Information Version Number 0.05 Updated On July 14, 2018 Microsoft © 2018 Page 1 of 102 Microsoft Common Criteria Security Target Version History Version Date Summary of changes 0.01 January 27, 2018 Initial draft 0.02 February 24, 2018 Updates from security target evaluation 0.03 March 23, 2018 Updates from assurance activity evaluation 0.04 April 19, 2018 Prepared copy for publication 0.05 July 14, 2018 Editorial Updates Microsoft © 2018 Page 2 of 102 Microsoft Common Criteria Security Target This is a preliminary document and may be changed substantially prior to final commercial release of the software described herein. The information contained in this document represents the current view of Microsoft Corporation on the issues discussed as of the date of publication. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information presented after the date of publication. This document is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS OR IMPLIED, AS TO THE INFORMATION IN THIS DOCUMENT. Complying with all applicable copyright laws is the responsibility of the user. This work is licensed under the Creative Commons Attribution-NoDerivs- NonCommercial License (which allows redistribution of the work). To view a copy of this license, visit http://creativecommons.org/licenses/by-nd-nc/1.0/ or send a letter to Creative Commons, 559 Nathan Abbott Way, Stanford, California 94305, USA. -
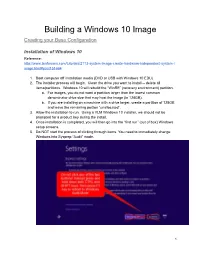
Building a Windows 10 Image Creating Your Base Configuration
Building a Windows 10 Image Creating your Base Configuration Installation of Windows 10 Reference: http://www.tenforums.com/tutorials/2113-system-image-create-hardware-independent-system-i mage.html#post151664 1. Boot computer off installation media (DVD or USB with Windows 10 EDU) 2. The installer process will begin. Clean the drive you want to install -- delete all items/partitions. Windows 10 will rebuild the “WinRE” (recovery environment) partition. a. For images, you do not want a partition larger than the lowest common denominator drive size that may host the image (ie 128GB). b. If you are installing on a machine with a drive larger, create a partition of 128GB and leave the remaining portion “unallocated”. 3. Allow the installation to run. Using a VLM Windows 10 installer, we should not be prompted for a product key during the install. 4. Once installation is completed, you will then go into the “first run” (out of box) Windows setup screens. 5. Do NOT start the process of clicking through items. You need to immediately change Windows into Sysprep “Audit” mode. 1 6. Windows reboots, and enters Audit Mode using the built-in “Administrator” account. When the desktop loads, you will notice the Sysprep box open in the middle of your screen. Close it for now by pressing the Cancel button. a. NOTE on AUDIT MODE: Throughout image construction process, remain in AUDIT Mode. When reboots are required, system will boot back up and auto-login to Administrator account. Sysprep box will be presented. Simply hit CANCEL option each time. Creation of “Base” Image In this stage, you will start setup and customization of your “template” profile. -

Windows Embedded Standard 7 Brings the Technology and Rich User Experiences of Windows 7 to Enterprise and Media Centric Devices
Now includes Windows Embedded Standard 7 Service Pack 1 Windows Embedded Standard 7 brings the technology and rich user experiences of Windows 7 to enterprise and media centric devices. Its enhanced features and familiar tools help OEMs make the journey from concept to creation quickly. Visit www.windowsembedded.com/standard. High performance embedded solutions Smart, compelling devices that offer share a high confidence platform endless possibilities Windows® Embedded Standard 7 provides OEMs with a Windows Embedded Standard 7 gives Embedded OEMs powerful, security enhanced, and flexible platform on which the ability to create exceptional user experiences based on to build innovative products. Enhanced features and tools Windows technologies. significantly reduce costs and accelerate time-to-market. RICH MEDIA EMBEDDED TOOLS Features such as Internet Explorer® 8, Windows Media Windows Embedded Standard 7 includes an easy-to-use Center, and Windows Media® Player 12 bring Web Image Build Wizard (IBW) and other embedded tools which capabilities and multimedia experiences of the desktop speed up image development and prototyping, allowing to embedded devices. The addition of Remote Desktop developers to innovate on new hardware configurations. Protocol 7.1 and RemoteFX from Service Pack 1 also enable rich media experience on remote client devices. FLEXIBLE OPTIONS Windows Embedded Standard 7 includes more than 150 COMPELLING EXPERIENCES intuitive feature packages and 500 driver sets—everything Support for 64-bit hardware and high end graphics, developers need to build fixed function devices. combined with multi-touch gestures and context aware applications, make it possible for developers to create SIMPLE INTEGRATION immersive user interfaces. IPv6 support, including a new TCP/IP stack, and added security through Network Access Protection (NAP), enable INNOVATIVE FEATURES easy integration into the enterprise network. -

Application Whitelisting
Information Security Guideline Application Whitelisting THIS PAGE INTENTIONALLY LEFT BLANK Application Whitelisting www.secmon1.com Application Whitelisting is a means to limit the number of programs running in your business environment that can potentially pose a danger to the security of your data. It restricts users from installing and accessing applications on their computer or electronic device other than those explicitly allowed by your company. In the SECMON1 blog post 'Security Overview - Information Security Essentials', we spoke about what application whitelisting is and why it is an essential security measure. In this document, we are going to describe how to implement some basic application whitelisting as well as take you step by step through some ways you can achieve this using your existing technology and resources. Finally, we will give you some interesting and important links where you can educate yourself further on the topic and discuss some other options available to you. Software Applications There are some vendor-provided application whitelisting solutions available. It is worthwhile to know that some antivirus and data loss prevention solutions include application whitelisting functionality. Below are a few of them and of course there are others. We suggest to identify what antivirus product is installed in your environment and make enquires as to whether it includes application whitelisting • Airlock Digital (Application Whitelisting) • Ivanti (Application Whitelisting) • Trend Micro (Application Whitelisting) • McAfee (Antivirus with whitelisting capability) • Carbon Black (Antivirus with Whitelisting capability) • Kaspersky (Antivirus with Whitelisting capability) • Digital Guardian (Data Loss Prevention with Whitelisting capability) Note: Application whitelisting products may conflict with anti-malware software from a different vendor. -
Enterprise Desktop Support Technician
70-685: Enterprise Desktop Support Technician Course Introduction 4m Course Introduction Chapter 01 - Identifying Cause and Resolving Desktop 2hr 30m Application Issues Identifying Cause and Resolving Desktop Application Issues Role of Enterprise Technician Troubleshooting Windows 7 Programs Troubleshooting Using a Troubleshooter Demo - Troubleshooter Problem Steps Recorder Problem Steps Recorder Output Demo - Problem Steps Recorder Software Installation Methods Installing Applications Using Group Policy to Install Software Demo - GPO Driver Installation Other Group Policy Settings Group Policy and Software Restrictions Order of Software Restriction Policies Processing Enforcement Rules AppLocker AppLocker Requirements Creating AppLocker Rules Procedure Reference Demo - AppLocker Rules AppLocker Advantages AppLocker Disadvantages Installation Permissions and Compatibility Mitigation of Compatibility Issues Application Compatibility Options Digital Signing Software Program Compatibility - Control Panel Application Compatibility Toolkit Features Application Compatibility Toolkit (ACT) Running Applications in Compatibility Mode Demo - Compatibility Toolkit Other Tools to Know About User Account Control (UAC) Demo - User Account Control Windows Installer Identifying Cause of and Resolving Desktop Application Issues Running Legacy Applications How to Update Applications Application Updates Windows Update Demo - Windows Update WSUS GPO Options - WSUS WSUS Server Administrator WSUS Options Troubleshooting Windows Update Windows Management Instrumentation -
Bypassing Windows Applocker Using a Time of Check Time of Use Vulnerability
An NCC Group Publication Bypassing Windows AppLocker using a Time of Check Time of Use vulnerability Prepared by: Ollie Whitehouse © Copyright 2013 NCC Group Contents 1 Introduction and executive summary ........................................................................................ 3 1.1 Research findings overview .................................................................................................. 3 1.2 Microsoft’s response ............................................................................................................. 3 2 An introduction to Time of Check Time of Use race conditions............................................. 3 3 Bypassing Windows AppLocker with TOCTOU ....................................................................... 4 3.1 History behind the attack hypothesis .................................................................................... 4 3.2 Research environment configuration .................................................................................... 4 3.3 Observing program loading behavior .................................................................................... 5 3.4 Validating and exploiting ....................................................................................................... 7 3.5 USB attack scenario applicability .......................................................................................... 8 4 Mitigation advice when using AppLocker ................................................................................